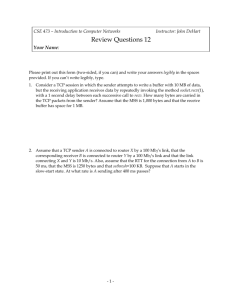
VERSION 1 1 Refer to the exhibit. The network administrator enters
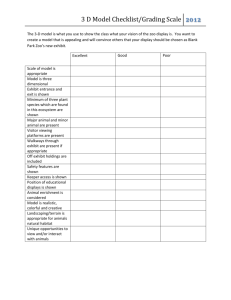
advertisement

VERSION 1 1 Refer to the exhibit. The network administrator enters these commands into the R1 router: R1# copy running-config tftp Address or name of remote host [ ]? When the router prompts for an address or remote host name, what IP address should the administrator enter at the prompt? 192.168.9.254 192.168.10.1 192.168.10.2 192.168.11.254 192.168.11.252 2 Which three statements characterize the transport layer protocols? (Choose three.) TCP uses port numbers to provide reliable transportation of IP packets. TCP and UDP port numbers are used by application layer protocols. TCP uses windowing and sequencing to provide reliable transfer of data. TCP is a connection-oriented protocol. UDP is a connectionless protocol. UDP uses windowing and acknowledgments for reliable transfer of data. 3 What is the purpose of ICMP messages? to inform routers about network topology changes to ensure the delivery of an IP packet to monitor the process of a domain name to IP address resolution to provide feedback of IP packet transmissions 4 A technician uses the ping 127.0.0.1 command. What is the technician testing? connectivity between a PC and the default gateway connectivity between two adjacent Cisco devices physical connectivity of a particular PC and the network the TCP/IP stack on a network host connectivity between two PCs on the same network 5 What will a Layer 2 switch do when the destination MAC address of a received frame is not in the MAC table? It notifies the sending host that the frame cannot be delivered. It initiates an ARP request. It forwards the frame out of all ports except for the port at which the frame was received. It broadcasts the frame out of all ports on the switch. 6 What is a characteristic of the LLC sublayer? It places information in the frame that allows multiple Layer 3 protocols to use the same network interface and media. It provides delimitation of data according to the physical signaling requirements of the medium. It defines software processes that provide services to the physical layer. It provides the logical addressing required that identifies the device. 7 On which switch interface would an administrator configure an IP address so that the switch can be managed remotely? VLAN 1 console 0 vty 0 FastEthernet0/1 8 A network engineer is measuring the transfer of bits across the company backbone for a mission critical database application. The engineer notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.) the reliability of the gigabit Ethernet infrastructure of the backbone the amount of traffic that is currently crossing the network the type of traffic that is crossing the network the sophistication of the encapsulation method applied to the data the bandwidth of the WAN connection to the Internet the latency that is created by the number of network devices that the data is crossing 9 When applied to a router, which command would help mitigate brute-force password attacks against the router? service password-encryption login block-for 60 attempts 5 within 60 banner motd $Max failed logins = 5$ exec-timeout 30 10 Which two statements correctly describe a router memory type and its contents? (Choose two.) ROM is nonvolatile and contains basic diagnostic software. FLASH is nonvolatile and contains a limited portion of the IOS. ROM is nonvolatile and stores the running IOS. RAM is volatile and stores the IP routing table. NVRAM is nonvolatile and stores other system files. 11 Which two components are necessary for a wireless client to be installed on a WLAN? (Choose two.) custom adapter wireless bridge media wireless NIC crossover cable wireless client software 12 Launch PT - Hide and Save PT Open the PT activity. Perform the tasks in the activity instructions and then fill in the blank. The Server0 message is . ” winner ” 13 A host is accessing a Web server on a remote network. Which three functions are performed by intermediary network devices during this conversation? (Choose three.) applying security settings to control the flow of data notifying other devices when errors occur regenerating data signals acting as a client or a server serving as the source or destination of the messages providing a channel over which messages travel 14 15 16 Which address on a PC does not change, even if the PC is moved to a different network? IP address logical address MAC address default gateway address 17 What will happen if the default gateway address is incorrectly configured on a host? A ping from the host to 127.0.0.1 would not be successful. The host will have to use ARP to determine the correct address of the default gateway. The host cannot communicate with other hosts in the local network. The host cannot communicate with hosts in other networks. The switch will not forward packets initiated by the host. 18 A host PC has just booted and is attempting to lease an address through DHCP. Which two messages will the client typically broadcast on the network? (Choose two.) DHCPREQUEST DHCPOFFER DHCPDISCOVER DHCPNACK DHCPACK 19 Refer to the exhibit. An administrator wants to change the name of a brand new switch, using the hostname command as shown. What prompt will display after the command is issued? Switch# My(config)# My Switch(config)# Switch(config)# MySwitch(config)# 20 After making configuration changes, a network administrator issues a copy runningconfig startup-config command in a Cisco switch. What is the result of issuing this command? The configuration changes will be removed and the original configuration will be restored. The new configuration will be stored in flash memory. The current IOS file will be replaced with the newly configured file. The new configuration will be loaded if the switch is restarted. 21 Refer to the exhibit.A TCP segment from a server has been captured by Wireshark, which is running on a host. What acknowledgement number will the host return for the TCP segment that has been received? 2921 250 2 306 21 22 Which technology provides a solution to IPv4 address depletion by allowing multiple devices to share one public IP address? ARP DNS SMB DHCP HTTP NAT 23 What is the purpose of the routing process? to encapsulate data that is used to communicate across a network to select the paths that are used to direct traffic to destination networks to convert a URL name into an IP address to provide secure Internet file transfer to forward traffic on the basis of MAC addresses 24 Three bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types? audio conference, financial transactions, web page financial transactions, audio conference, web page audio conference, web page, financial transactions financial transactions, web page, audio conference 25 A home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used? cell modem dial-up cable modem satellite DSL 26 Which connection provides a secure CLI session with encryption to a Cisco switch? a Telnet connection an SSH connection a console connection an AUX connection 27 What is the purpose of the network security accounting function? to provide challenge and response questions to require users to prove who they are to determine which resources a user can access to keep track of the actions of a user 28 Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses Telnet to connect to the switch, which password is needed to access user EXEC mode? lineconin linevtyin letmein secretin 29 Which publicly available resources describe protocols, processes, and technologies for the Internet but do not give implementation details? IEEE standards Request for Comments IRTF research papers protocol models 30 A PC is configured to obtain an IP address automatically from network 192.168.1.0/24. The network administrator issues the arp –a command and notices an entry of 192.168.1.255 ff-ff-ff-ff-ff-ff. Which statement describes this entry? This entry refers to the PC itself. This entry maps to the default gateway. This is a static map entry. This is a dynamic map entry. 31 Which subnet would include the address 192.168.1.96 as a usable host address? 192.168.1.64/26 192.168.1.32/28 192.168.1.32/27 192.168.1.64/29 32 A particular website does not appear to be responding on a Windows 7 computer. What command could the technician use to show any cached DNS entries for this web page? ipconfig /all ipconfig /displaydns arp -a nslookup 33 Which type of wireless security generates dynamic encryption keys each time a client associates with an AP? WPA PSK WEP EAP 34 A frame is transmitted from one networking device to another. Why does the receiving device check the FCS field in the frame? to compare the interface media type between the sending and receiving ends to determine the physical address of the sending device to verify that the frame destination matches the MAC address of the receiving device to check the frame for possible transmission errors to verify the network layer protocol information 35 Refer to the exhibit. Which IP addressing scheme should be changed? Site 1 Site 3 Site 4 Site 2 36 What is the effect of configuring the ipv6 unicast-routing command on a router? to assign the router to the all-nodes multicast group to permit only unicast packets on the router to enable the router as an IPv6 router to prevent the router from joining the all-routers multicast group 37 Which three IP addresses are private ? (Choose three.) 10.1.1.1 172.16.4.4 224.6.6.6 192.168.5.5 172.32.5.2 192.167.10.10 38 Refer to the exhibit. Consider the IP address configuration shown from PC1. What is a description of the default gateway address? It is the IP address of the Router1 interface that connects the company to the Internet. It is the IP address of the ISP network device located in the cloud. It is the IP address of Switch1 that connects PC1 to other devices on the same LAN. It is the IP address of the Router1 interface that connects the PC1 LAN to Router1. 39 During normal operation, from which location do most Cisco switches and routers run the IOS? flash RAM NVRAM disk drive 40 What is an important function of the physical layer of the OSI model? It encodes frames into electrical, optical, or radio wave signals. It accepts frames from the physical media. It encapsulates upper layer data into frames. It defines the media access method performed by the hardware interface. 41 Which procedure is used to reduce the effect of crosstalk in copper cables? wrapping the bundle of wires with metallic shielding avoiding sharp bends during installation requiring proper grounding connections designing a cable infrastructure to avoid crosstalk interference twisting opposing circuit wire pairs together 42 What are the three primary functions provided by Layer 2 data encapsulation? (Choose three.) placement and removal of frames from the media detection of errors through CRC calculations conversion of bits into data signals delimiting groups of bits into frames data link layer addressing error correction through a collision detection method session control using port numbers 43 What method is used to manage contention-based access on a wireless network? token passing CSMA/CD CSMA/CA priority ordering 44 What happens when part of an Internet radio transmission is not delivered to the destination? A delivery failure message is sent to the source host. The part of the radio transmission that was lost is re-sent. The transmission continues without the missing portion. The entire transmission is re-sent. 45 What is the auto-MDIX feature on a switch? the automatic configuration of full-duplex operation over a single Ethernet copper or optical cable the automatic configuration of an interface for a straight-through or a crossover Ethernet cable connection the ability to turn a switch interface on or off accordingly if an active connection is detected the automatic configuration of an interface for 10/100/1000 Mb/s operation 46 Which function is provided by TCP? detection of missing packets communication session control path determination for data packets data encapsulation 47 How does a Layer 3 switch differ from a Layer 2 switch? A Layer 3 switch learns the MAC addresses that are associated with each of its ports. However, a Layer 2 switch does not. A Layer 3 switch maintains an IP address table instead of a MAC address table. A Layer 3 switch supports VLANs, but a Layer 2 switch does not. An IP address can be assigned to a physical port of a Layer 3 switch. However, this is not supported in Layer 2 switches. 48 Which two notations are useable nibble boundaries when subnetting in IPv6? (Choose two.) /68 /62 /66 /64 /70 49 What is the purpose of having a converged network? to reduce the cost of deploying and maintaining the communication infrastructure to provide high speed connectivity to all end devices to make sure that all types of data packets will be treated equally to achieve fault tolerance and high availability of data network infrastructure devices 50 Refer to the exhibit. A ping to PC3 is issued from PC0, PC1, and PC2 in this exact order. Which MAC addresses will be contained in the S1 MAC address table that is associated with the Fa0/1 port? just the PC0 MAC address PC0, PC1, and PC2 MAC addresses just the PC2 MAC address just PC0 and PC1 MAC addresses just the PC1 MAC address 51 Which field in an IPv4 packet header will typically stay the same during its transmission? Packet Length Destination Address Flag Time-to-Live 52 What two preconfigured settings that affect security are found on most new wireless routers? (Choose two.) MAC filtering enabled default administrator password WEP encryption enabled PSK authentication required broadcast SSID 53 Which parameter does the router use to choose the path to the destination when there are multiple routes available? the higher metric value that is associated with the destination network the lower metric value that is associated with the destination network the higher gateway IP address to get to the destination network the lower gateway IP address to get to the destination network 54 Refer to the exhibit. What is the significance of the asterisk (*) in the exhibited output? An asterisk designates that the file system has at least one file that uses that file system. The asterisk designates which file system is the default file system. An asterisk indicates that the file system is bootable. The asterisk shows which file system was used to boot the system. 55 56 Fill in the blank. During data communications, a host may need to send a single message to a specific group of destination hosts simultaneously. This message is in the form of a ” multicast ” message. 57 An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes? to interrupt the ping process to restart the ping process to allow the user to complete the command to exit to a different configuration mode 58 Refer to the exhibit. Which area would most likely be an extranet for the company network that is shown? area A area D area C area B 59 60 61 In which default order will a router search for startup configuration information? setup mode, NVRAM, TFTP NVRAM, TFTP, setup mode NVRAM, RAM, TFTP TFTP, ROM, NVRAM flash, ROM, setup mode 62 Launch PT - Hide and Save PT Open the PT Activity. Perform the tasks in the activity instructions and then answer the question. Which IPv6 address is assigned to the Serial0/0/0 interface on RT2? 2001:db8:abc:1::1 2001:db8:abc:5::1 2001:db8:abc:5::2 2001:db8:abc:10::15 63 What is contained in the trailer of a data-link frame? physical address data error detection* logical address 64 VERSION 2 What layer is the first point of entry for a host into the network? Access layer Which part of the electromagnetic spectrum is commonly used to exchange data between a PDA and a computer? Infrared Your school network blocks all websites related to online gaming. What type of security policy is being applied? Acceptable use What are two examples of storage peripheral devices? Flash drive External DVD The area covered by a single AP is known as what? Basic service set When acting as a DHCP server, an integrated router can provide what three types of information to a client? Default gateway Dynamic IP address DNS server address Refer to the graphic. Assume that the exhibited output is from a host that is connected to a Linksys integrated router. What is one of the first things you should check? Link status LED on the front of the router A host sent a message that all other hosts on the switched local network received and processed. What type of domain are all these hosts a part of? Broadcast domain Refer to the exhibit. A user on host A sends an e-mail to the user on host B. Which type of message does host A send? Unicast Which type of computer uses an integrated monitor and keyboard? Laptop Refer to the exhibit. What cabling fault does the exhibit represent? Split pair What is the purpose of the ipconfig /release command? It forces a client to give up its current IP address. What is the function of the DNS server? It translates a computer or domain name to the associated IP address. Which part of a data packet is used by a router to determine the destination network? Destination IP address A network engineer wants to represent confidential data in binary format. What are the two possible values that the engineer can use? (Choose two.) 0 1 What is the purpose of spam filter software? It examines incoming e-mail messages to identify the unsolicited ones A user is unable to send e-mail. While troubleshooting this problem, the network technician first verifies the physical connectivity of cables. Which troubleshooting approach is being followed? Bottom-up Which two causes of networking problems are related to the physical layer? (Choose two.) Disconnected cables Improper operation of cooling fans What is an advantage of selecting an operating system that has a commercial license over one with a GPL license? The commercial license-based operating system provides structured support. Refer to the exhibit. What is the purpose of assigning a network name of College? It identifies the wireless LAN. Refer to the exhibit. What is the effect of setting the security mode to WEP on the Linksys integrated router? The WEP security mode encrypts network traffic during transmission between the AP and the wireless client A network technician is required to provide access to the Internet for a large company. What is needed to accomplish this task? ISP Refer to the exhibit. Assume that the command output is from a wireless DHCP client that is connected to a Linksys integrated router. What can be deduced from the output? The wireless connection is operational What is specified by the host bits in an IP address? Identity of the computer on the network What is the default subnet mask for an IP address of 64.100.19.14? 255.0.0.0 Which two transport layer protocols enable hosts to communicate and transfer data? (Choosetwo.) TCP UDP A learner wants to interact with the operating system of a computer. Which two methods can be used for this? (Choose two.) CLI GUI Which installation option enables a single physical resource to function simultaneously as multiple logical resources? Upgrade Which two statements are true about local applications? (Choose two.) They are stored on the local hard disk. They run on the computer where they are installed. For an IP address, what component decides the number of bits that is used to represent the host ID? Network number What type of cable would be required to connect a Linksys router to a wired PC? straight-through cable Refer to the exhibit. If H4 sends a message to H1 and the destination MAC address is in the MAC table for both Switch1 and Switch2, which host devices will receive the message? Only H1 Because of an increasing number of users, bandwidth per user on a WLAN has decreased to a point where users are complaining about poor performance. What can be done to improve the user experience? Reduce the number of devices using each channel. What are two best practices that are used when configuring a small home WLAN? (Choose two.) The use of pre-shared keys The disabling of SSID broadcasting Which protocol in its default configuration downloads e-mail messages to the client computer and deletes them from the server? POP3 What is the purpose of creating a DMZ during network firewall implementation? To allow for a publicly accessible zone without compromising the internal network Which of the following are the address ranges of the private IP addresses? (Choose three.) 10.0.0.0 to 10.255.255.255 172.16.0.0 to 172.31.255.255 192.168.0.0 to 192.168.255.255 What does the term “attenuation” mean in data communication? Loss of signal strength as distance increases What advantage does a peer-to-peer network have over a client-server network? It eliminates the need for centralized administration In an attempt to verify connectivity, a user issues the ping command to a device that is not on the local network. The ping is unsuccessful. What can be determined from this result? The router between the host and destination is faulty. A company has a web server that must be accessible to both external and internal clients. Which security policy best practice should be followed to maximize security of the server? Place the web server in a DMZ The help desk at a large packaging company receives a call from a user who is concerned about lost data files on the local PC. The help desk technician learns that the user clicked on an icon that appeared to be a program update, but no updates were scheduled for that program. What type of attack has likely occurred? Trojan horse Where do ISPs get the public addresses that they assign to end users? ISPs obtain address blocks from registry organizations Which transport layer protocol is used when an application requires acknowledgment that data has been delivered? TCP What type of message is sent to a specific group of hosts? Multicast A network administrator has been notified that users have experienced problems gaining access to network resources. What utility could be used to directly query a name server for information on a destination domain? Nslookup What is the function of CSMA/CA on a wireless Ethernet network? To prevent collisions Refer to the exhibit. Why would a network administrator use the network mode that is shown? To support hosts that uses different 802.11 standards When terminating UTP cabling, why is it important to untwist only a small amount of each wire pair? Minimizes crosstalk A network technician suspects that malware on a user PC is opening multiple TCP connections to a specific foreign host address. Which Windows command line utility can be used to confirm the multiple TCP connections? Netstat What are two examples of storage peripheral devices? (Choose two.) Flash drive External DVD When acting as a DHCP server, an integrated router can provide what three types of information to a client? (Choose three.) Default gateway Dynamic IP address DNS server address 2012 VERSION 1,2 y 3 Which of the following are the address ranges of the private IP addresses? (Choose three.) 10.0.0.0 to 10.255.255.255 ; 172.16.0.0 to 172.31.255.255; 192.168.0.0 to 192.168.255.255 Which two functions of the OSI model occur at layer two? (Choose two.) physical addressing ; media access control Refer to the exhibit. What function does router RT_A need to provide to allow Internet access for hosts in this network? address translation What is true regarding network layer addressing? (Choose three.) It uses a hierarchical structure.; uniquely identifies each host; A portion of the address is used to identify the network. Refer to the exhibit. Host A attempts to establish a TCP/IP session with host C. During this attempt, a frame was captured with the source MAC address 0050.7320.D632 and the destination MAC address 0030.8517.44C4. The packet inside the captured frame has an IP source address 192.168.7.5, and the destination IP address is 192.168.219.24. At which point in the network was this packet captured? Leaving Dallas Refer to the exhibit. Assume all devices are using default configurations. How many subnets are required to address the topology that is shown? 3 A technician is asked to secure the privileged EXEC mode of a switch by requiring a password. Which type of password would require this login and be considered the most secure? enable secret Refer to the exhibit. A technician is working on a network problem that requires verification of the router LAN interface. What address should be pinged from this host to confirm that the router interface is operational? 192.168.254.1 Which OSI layer does IP rely on to determine whether packets have been lost and to request retransmission? transport When connectionless protocols are implemented at the lower layers of the OSI model, what is usually used to acknowledge that the data was received and to request the retransmission of missing data? an upper-layer, connection-oriented protocol or service Refer to the exhibit. Host C is able to ping 127.0.0.1 successfully, but is unable to communicate with hosts A and B in the organization. What is the likely cause of the problem? The subnet mask on host C is improperly configured. Refer to the exhibit. Which list refers only to end devices? D,E,F,G Refer to the exhibit. Host A sends a frame with the destination MAC address as FFFF.FFFF.FFFF. What action will the switch take for this frame? It will send the frame to all hosts except host A. Which subnet mask will allow 2040 hosts per subnet on the IP network 10.0.0.0? 255.255.248.0 Refer to the exhibit. RouterB is configured properly. The Ethernet interface Fa0/0 of RouterA is configured with the use of the commands that are shown. However, a ping from the Fa0/0 interface of RouterA to the Fa0/0 interface of RouterB is unsuccessful. What action should be taken on RouterA to solve this problem? Use the no shutdown command on the FastEthernet interface Fa0/0. To send data through a network, what two flags are used to establish a session? (Choose two.) ACK; SYN Which statement is true about the TTL value of an IPv4 packet? It specifies the remaining "life" of the packet. Refer to the exhibit. Communication for hosts X and Y is restricted to the local network. What is the reason for this? The gateway addresses are broadcast addresses. What type of network is maintained if a server takes no dedicated role in the network? peer-to-peer A routing issue has occurred in your internetwork. Which of the following type of devices should be examined to isolate this error? Router Which physical component is used to access and perform the initial configuration on a new unconfigured router? Image 2, CONSOLE A user sees the command prompt: Router(config-if)# . What task can be performed at this mode? Configure individual interfaces. What is the correct order for PDU encapsulation? Frame Header, Network Header, Transport Header, Data, Frame Trailer What information can be gathered by using the command netstat? active TCP connections How can ARP be used to help document the network? It can provide a list of physical addresses on the network. What is the protocol data unit that is associated with the data link layer of the OSI reference model? Frame Which application layer protocol allows administrators to log into a server from remote locations and control a server as though logged in locally? Telnet Which statement identifies the DNS protocol? It matches a resource name with the required network address. Which password would allow a user to establish a Telnet session with a Cisco device? VTY password Which identifier is contained in the header of the Layer 2 Ethernet frame? physical source and destination addresses What happens when a node on an Ethernet network is creating a frame and it does not have the destination MAC address? The node sends out an ARP request with the destination IP address. An administrator makes changes to the default configuration of a router and saves them to NVRAM. After testing, it is discovered that the configurations did not have the desired effect and must be removed. What steps must be taken to remove the changes and return the router to the default configuration? Issue the erase startup-config command, and then reboot the router. A network administrator is tasked with connecting two workgroups that are configured to use different subnets. Which device should be selected to allow connectivity between users on the two networks? Router Which two programs can be used to accomplish terminal emulation for configuring a router from the CLI through the console port? (Choose two.) HyperTerminal; Minicom Which statement accurately describes file sharing in a peer-to-peer network? Access control is decentralized. What are two primary responsibilities of the Ethernet MAC sublayer? (Choose two.) data encapsulation; accessing the media Which router configuration mode would an administrator use to configure the router for SSH or Telnet login access? Line Refer to the exhibit. Which device should be included in the network topology to provide Layer 2 connectivity for all LAN devices, provide multiple collision domains, and also provide a connection to the rest of the network? Switch Refer to the exhibit. A technician has been asked to test connectivity from PC1 to a remote network. Which action will indicate if there is remote connectivity? C:\>ping 172.16.4.1 What purpose does a hostname serve on a router? provides device identification to users logging on remotely Which prompt is associated with the privileged exec mode? R1# A technician wishes to connect two computers to move data from one to the other before reloading the operating system. The NICs on both PCs do not support autosensing feature. Which procedure will satisfy the requirement? Interconnect the two PCs with a crossover cable. Refer to the exhibit. Interface Fa0/0 on router A is generating excessive broadcast traffic. Which LAN segments will affected by the excessive broadcasts? Only the 192.168.1.200/30 network will be affected. Two routers are connected via their serial ports in a lab environment. The routers are configured with valid IP addresses, but they cannot ping each other. The show interface serial0/0 command shows that the serial0/0 interface is up but the line protocol is down. What could be the cause of this problem? The clock rate command has not been entered on the DCE interface. Refer to the exhibit. Which layered network model is shown in the diagram? TCP/IP Refer to the exhibit. Host A is unable to reach host B on the remote network. A technician attempted to ping the local gateway and the ping was successful. To verify the host configuration, the technician issued the ipconfig command. What is the likely cause of the problem? The default gateway on host A is incorrectly configured. Which option shows how a router will route packets to a remote network? Image 4 An organization has been assigned network ID 10.10.128.0 and subnet mask 255.255.224.0. Which IP address range can be used for this organization? 10.10.128.0 to 10.10.159.255 A network administrator is configuring several switches for a network. The switches have similar configurations and only minor differences. The administrator wants to save all commands that are issued on the first switch to a text file for editing. Which transfer option should be selected in HyperTerminal? Capture Text When must a router serial interface be configured with the clock rate command? when the interface is functioning as a DCE device Due to a security violation, the router passwords must be changed. What information can be learned from the following configuration entries? (Choose two.) The entries specify four Telnet lines for remote access; Access will be permitted for Telnet using "c13c0″ as the password Which password is automatically encrypted when it is created? Enable secret Refer to the exhibit. A network technician is trying to determine the correct IP address configuration for Host A. What is a valid configuration for Host A? IP address: 192.168.100.20; Subnet Mask: 255.255.255.240; Default Gateway: 192.168.100.17 Which prompt represents the appropriate mode used for the copy running-config startup-config command ? Switch-6J# Refer to the exhibit. The tracert command is initiated from PC1 to PC4. Which device will send a response to the initial tracert packet from PC1? London Which information is used by the router to determine the path between the source and destination hosts? the network portion of the IP address Refer to the exhibit. A PC is communicating with another PC on a remote network. The two networks are connected by three routers. Which action will help to identify the path between the hosts? Use the tracert command at the host. Refer to the exhibit. The diagram represents the process of sending e-mail between clients. Which list correctly identifies the component or protocol used at each numbered stage of the diagram? MUA 2.SMTP 3.MTA 4.SMTP 5.MTA 6.MDA 7.POP 8.MUA Refer to the exhibit. The router of the company failed and was replaced. After the replacement, hosts C and D in the Education office are able to ping each other, but they are unable to access the hosts in the Accounts office. What is the likely cause of the problem? The subnet mask at the fa0/1 interface of the router is incorrectly entered. Refer to the exhibit. Host A and B are unable to communicate with each other. What is the reason for this? The gateway addresses are network addresses. Refer to the exhibit. Host B attempts to establish a TCP/IP session with host C. During this attempt, a frame was captured at the FastEthernet interface fa0/1 of the San Francisco router. The packet inside the captured frame has the source IP address 10.10.1.2, and the destination IP address is 10.31.1.20. What is the destination MAC address of the frame at the time of capture? 0060.7320.D631 Refer to the exhibit. While configuring a network, a technician wired each end of a Category 5e cable as shown. Which two statements are true about this setup? (Choose two.) The cable is suitable for connecting a switch to a router Ethernet port; The cable is suitable for connecting dissimilar types of devices. Well-known services and applications use which range of TCP/UDP port numbers? 0 to 1023 Which three IPv4 addresses represent subnet broadcast addresses? (Choose three.) 192.168.4.63 /26; 192.168.4.191 /26; 192.168.4.95 /27 Which OSI layer addressing is required to route packets between two networks? Layer 3 Refer to the exhibit. Host A is requesting a web page from the web server. Which option represents the socket to which the request is made? 10.0.0.130:80 Which statement describes the correct use of addresses to deliver an e-mail message from HostB to the e-mail service that is running on ServerA? Router B uses a Layer 3 network address to route the packet. Refer to the exhibit. Host A is configured with the correct IP address for the default gateway of the router R1 FastEthernet0/1 interface. How will a packet that is sent from host A to host B be handled by the devices on the network? R1 will forward the packet to its default gateway, the next hop router R2. R2 will forward the packet to the directly connected network 10.1.1.0/24. Which option correctly identifies the interface or interfaces used to connect the router to a CSU/DSU for WAN connectivity? Image 4 SERIAL 1; SERIAL 0 How many host addresses may be assigned when using the 128.107.0.0 network address with a subnet mask of 255.255.248.0? 2046 During the encapsulation process, what is the PDU of the internet layer? Packet Which service is used when the nslookup command is issued on a computer? DNS Refer to the exhibit. A network technician creates equal-sized subnets of network 192.168.2.0/24 using the subnet mask 255.255.255.224. If the technician wishes to calculate the number of host addresses in each subnet by using the formula that is shown in the exhibit, what value will be used for n? 5 What are the default terminal emulation software settings when configuring a Cisco device through a console port? Bits per second: 9600 Data bits: 8 Parity: None Stop bits: 1 Flow control: None In a packet-switched data network, what is used to reassemble the packets in the correct order at the destination device? Sequence number Refer to the exhibit. A network administrator tries to test the connectivity between routers R1 and R2, but the attempt to ping is unsuccessful. Based on the show ip interface brief command outputs, what could be the possible cause of the problem? Interface S0/0/0 on router R1 is configured with an incorrect IP address. Which router configuration mode will require user authentication if an administrator issues the enable secret command? Privileged executive mode Which location of router memory is cleared with the erase startupconfig command? NVRAM Which subnet mask should be used for a Class B network that is divided into subnets and will accommodate between 800 hosts and 1000 hosts? 255.255.252.0 Refer to the exhibit. The network containing router B is experiencing problems. A network associate has isolated the issue in this network to router B. What action can be preformed to correct the network issue? issue the no shutdown command on interface FastEthernet 0/1 Refer to the exhibit. A web browser running on host PC1 sends a request for a web page to the web server with an IP address 192.168.1.254/24. What sequence of steps will follow in order to establish the session before data can be exchanged? The session will be initiated using TCP. A three-way handshake must be successfully completed before the session is established. What is the effect of using the Router# copy running-config startupconfig command on a router? The contents of NVRAM will change. Which option represents a point-to-point logical topology diagram? Last image In a network design project, a network designer needs to select a device to provide collision free connections to 40 hosts on the LAN. Which device should be selected? Switch Which communication tool allows real-time collaboration? instant messaging