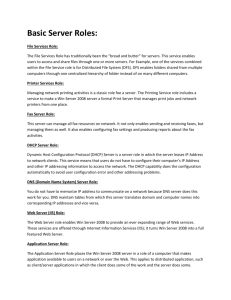
Logical Structure of an Active Directory
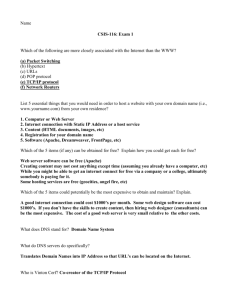
advertisement

Active Directory An active directory is a directory structure used on Microsoft Windows based computers and servers to store information and data about networks and domains. It is primarily used for online information and was originally created in 1996. It was first used with Windows 2000. An active directory (sometimes referred to as an AD) does a variety of functions including the ability to provide information on objects, helps organize these objects for easy retrieval and access, allows access by end users and administrators and allows the administrator to set security up for the directory. An active directory can be defined as a hierarchical structure and this structure is usually broken up into three main categories, the resources which might include hardware such as printers, services for end users such as web email servers and objects which are the main functions of the domain and network. Understanding Active Directories It is interesting to note the framework for the objects. Remember that an object can be a piece of hardware such as a printer, end user or security settings set by the administrator. These objects can hold other objects within their file structure. All objects have an ID, usually an object name (folder name). In addition to these objects being able to hold other objects, every object has its own attributes which allows it to be characterized by the information it contains. Most IT professionals call these settings or characterizations schemas. The type of schema created for a folder will ultimately determine how these objects are used. For instance, some objects with certain schemas cannot be deleted, they can only be deactivated. Others types of schemas with certain attributes can be deleted entirely. For instance, a user object can be deleted, but the administrator object cannot be deleted. When understanding active directories, it is important to know the framework that objects can be viewed at. In fact, an active directory can be viewed at either one of three levels, these levels are called forests, trees or domains. The highest structure is called the forest because you can see all objects included within the active directory. Within the Forest structure are trees, these structures usually hold one or more domains. Going further down the structure of an active directory are single domains. To put the forest, trees and domains into perspective, consider the following example. A large organization has many dozens of users and processes. The forest might be the entire network of end users and specific computers at a set location. Within this forest directory are now trees that hold information on specific objects such as domain controllers, program data and system, among others. Within these objects are even more objects which can then be controlled and categorized. How are Active Directories used? If you are a computer administrator for a large corporation or organization, you can easily update all end users computers with new software, patches and files simply by updating one object in a forest or tree. Because each object fits into a set schema and has specific attributes, a network administrator can easily clear a person on a set tree or instantly give or deny access to select users for certain applications. The Microsoft servers use trust to determine whether or not access should be allowed. Two types of trusts that Microsoft active directories incorporate are transitive trusts and one way non transitive trusts. A transitive trust is when there is a trust that goes further than two domains in a set tree, meaning two entities are able to access each other's domains and trees. A one way transitive trust is when a user is allowed access to another tree or domain; however, the other domain does not allow access to the further domains. This can be summed up as a network administrator and end user. The network administrator can access most trees in the forest including a specific end user's domain. However, the end user, while able to access his or her own domain, cannot access other trees. It is important to note that active directories are a great way to organize a large organization or corporation's computers' data and network. Without an active directory, most end users would have computers that would need to be updated individually and would not have access to a larger network where data can be processed and reports can be created. While active directories can be technical to a good extent and require considerable expertise to navigate, they are essential to storing information and data on networks. Physical Structure of Active Directory In comparison to the logical structure, which performs administrative tasks, the Active Directory physical structure checks when and where logon and replication traffic occurs. The physical structure of Active Directory contains all the physical subnets present in your network like domain controllers and replication between domain controllers. The physical structure of Active Directory: Domain Controllers: These computers run Microsoft Windows Server 2003/2000, and Active Directory. Every Domain Controller performs specific functions like replication, storage and authentication. It can support maximum one domain. It is always advised to have more than one domain controller in each domain. Active Directory Sites: These sites are collection of well-connected computers. The reason why we create site is domain controllers can communicate frequently within the site. This way it minimizes the latency within site say changes made on one domain controller to be replicated to other domain controllers. The other reason behind creating a site is to optimize bandwidth between domain controllers which are located in different locations. All IP subnets who share the common Local Area Network (LAN) connectivity without knowing the actual physical location of computers is called site. Let's take an example: A site has subnets 192.168.5. A and 192.168.50.A, where 192.168.5.A computer is located in Texas and 192.168.50.A computer is located in London. In this case physical location of both the computer is not known to user. Because of proper bandwidth between these two, they are able to work and configure computers within the same Active Directory Site. Few considerations an Administrator should examine before creating a new site are proper bandwidth, available bandwidth cost and replication traffic expected. Active Directory Partitions: Each Domain Controller contains the following active directory partitions: o The Domain Partition contains a copy of all the objects in that domain. Replication in Domain Partition is only to other domain controllers which are in the same domain. o The Schema Partition is forest wide. Every forest has one schema with consistent object class. The Schema and Configuration take part in replication, and get replicated to all domain controllers in a forest. o Application Partition which is optional carries objects which are not related to security and can be used by one or more applications. Application Partition replicates to specific domain controller in the forest. Logical Structure of an Active Directory Active Directory fulfills all the needs of an organization by designing a directory structure. It provides flexibility in designing the business structure according to current and future needs for an organization, so it should be examined prior to installing active directory. In Active Directory, resources are organized in a logical structure, and this grouping of resources logically enables a resource to be found by its name rather than by its physical location. Benefits of AD Logical Structure Logical Structure provides more network security by means of providing access to resources to only specified groups (OU). Logical structure simplified the network management by administration, configuration and control of the network. The relationship between the logical structure of domains and forests simplifies resource sharing across an organization. As logical structure provides simplified network management, it reduces the load on network resources and lower the total cost of ownership. Components of AD Logical Structure The logical structure components have relationship with each other so it manage to control access to stored data and finds how the data will be managed between different domains in a forest. Objects: like a user, computer , group, printer etc… Organizational Units – like any folder but in control of Active Directory Domains – Logical boundaries for objects Trees – Logical boundary for multiple domains Forests – Logical boundary for multiple trees Overall, one physical machine running as a Microsoft Domain controller can control all these logical divisions with the help of 'A Operation Master' dedicated to perform specific tasks. Tree and Forest in Active Directory The Domain is the core unit of logical structure in Active Directory. All objects which shares a common directory database, trust relationship with other domain and security policies is known as Domain. Each domain stores information only about the objects that belong to that domain. All security polices and settings, such as administrative rights, security policies, and Access Control Lists (ACLs), do not cross from one domain to another, thus a domain administrator has full rights to set policies only within domain they belong to. Domains provide administrative boundaries for objects; manage security for shared resources and a unit of replication for objects. A Tree Trees are collections of one or more domains that allow global resource sharing. A tree may consist of a single domain or multiple domains in a contiguous namespace. Adding a domain to a tree becomes a child of the tree root domain. Domain will be called as parent domain to which child domain is attached. A child domain can also have its multiple child domains. Child domain uses the name followed by parent domain name and gets a unique Domain Name System (DNS). For example, if tech.com is the root domain, you can create one or more Child domains to tech.com such as north.tech.com and or south.tech.com. These "children" may also have child domains created under them, such as sales.north.tech.com. The domains in a tree have twoway, Kerberos transitive trust relationships. A Kerberos transitive trust simply means that if Domain A trusts Domain B and Domain B trusts Domain C, then Domain A trusts Domain C. Therefore, a domain joining a tree immediately has trust relationships established with every domain in the tree. A Forest A forest is a collection of multiple trees that share a common global catalog, directory schema, logical structure, and directory configuration. Forest has automatic two-way transitive trust relationships. The very first domain you create in the forest is called the forest root domain. Forests allow organizations to group their divisions which use different naming scheme, and may need to operate independently. But as an organization they want to communicate with the entire organization via transitive trusts, and share the same schema and configuration container. Global Catalog in Active Directory Domains and Forests can also share resources available in active directory. These resources are searched by Global Catalog across domains and forests and this search is transparent to user. For example, if you make a search for all of the printers in a forest, this search goes to global catalog server for its query and then global catalog returns the results. Without a global catalog server this query needs to go to every domain in the forest of its result. It is important to have a global catalog on at least one domain controller because many applications use port 3268 for searching. For example, if you do not have any global catalog servers in your network, the Search command on the Start menu of Windows 2000/2003 cannot locate objects in Active Directory. The global catalog is a domain controller that contains attributes for every object in the Active Directory. By default, only the members of the Schema Admins group have rights to change which attributes stored in the global catalog, according to organization's requirements. The global catalog contains: The commonly used attributes need in queries, such as a user's first and last name, and logon name. All the information or records which are important to determine the location of any object in the directory. A default subset of attributes for each object type. All the access related permissions for every object and attribute that is stored in the global catalog. Say, without permission you can't access or view the objects. If you are searching for an object where you do not have the appropriate permissions to view, the object will not appear in the search results. These access permissions ensure that users can find only objects to which they have been assigned access. A global catalog server is a domain controller that contains full and writable replica of its domain directory, and a partial, read-only replica of all other domain directory partitions in the forest. Let's take an example of a user object; by default user objects have lot of attributes such as first name, last name, address, phone number, and many more. The Global Catalog will store only the main attributes of user objects in search operations like a user's first name and last name, or login name. This partial attributes of that user object which is stored would be enough to allow a search for that object to be able to locate the full replica of the object in active directory. If a search comes to locate objects, then first it goes to local global catalog and reduces network traffic over the WAN. Domain Controllers always contain the full attribute list for objects belonging to their domain. If the Domain Controller is also a GC, it will also contain a partial replica of objects from all other domains in the forest. It is always recommended to have a global catalog server for every active directory site in an enterprise network. Active Directory Operations Masters When a change is made to a domain, the change is replicated across all of the domain controllers in the domain. Some changes, such as those made to the schema, are replicated across all of the domains in the forest. This replication is called multimaster replication. But few changes are practically not possible to perform with multimaster replication, so a domain controller known as Operations Master takes such type of changes to perform. Five Operations Master Roles are given to one or more domain controllers in each forest. Operations Master Roles The operations master roles are also called as flexible single master operations (FSMO) roles. Forest-Wide Roles: Unique to a forest Schema Master: Controls all modifications and updates to the schema. The schema contains the master list of objects classes and attributes that are used to create all Active Directory objects, such as users, computers and printers. One needs to have access to update the schema of a forest. There is only one schema master in the entire forest. Domain Naming Master: Controls the additions or removal of domains in the forest. When you add a new domain to the forest, only the domain controller that holds the domain naming master role can add the new domain. There can be only one domain naming master in the entire forest. The role of domain naming master can be hold by any Windows Server 2000/2003. Domain naming master should be configured as a global catalog server. There is only one schema master and one domain-naming master in the entire forest. Domain-Wide Roles: Unique to each domain in a forest Primary Domain Controller (PDC) Emulator: If your networks has one or more Windows NT, there it act as Windows NT PDC to support any backup domain controller (BDCs) running Windows NT within a mixed mode domain. This type of domain has domain controllers that run Windows NT. The PDC Emulator role is maintained in the first domain controller that you create in a domain. By default, for time synchronization throughout the domain for all domain controllers, PDC emulator master is also responsible. Using "net time" one can synchronize the time of PDC Emulator with external server. Syntax is: net time ServerName/setsntp:TimeSource After executing this statement, all computers in the entire forest run within seconds of each other. PDC emulator role supports two authentication protocols: Kerberos V5 protocol and NTLM protocol Relative Identifier Master: When you create a new user, computer or object, the domain controller creates a new security principal for that object and assigns that object a unique security identifier (SID). This SID consists of domain ID and a relative identifier (RID). The RID master allocates blocks of RIDs to each domain controller in the domain. Domain controller use these allocated block of RIDs to assigns a RID to objects. Using Movetree.exe you can move an object between domains. But before this you need to initiate the move on the Relative Identifier (RID) master domain which contains the object. Infrastructure Master: Infrastructure master updates objects references when objects are moved from one domain to another. The object references contain GUID (Global Unique Identifier), a Security Identifier (SID), and distinguished name. The infrastructure master always replicates its data with global catalog. Global catalogs always receive the regular updates from other domain through replication; therefore global catalog data is always up to date. For regular updates it will always ask the global catalog. Then infrastructure master replicates its updated data to all domain controllers in the domain. Infrastructure master and global catalog should never be on the same domain controller because infrastructure master will not function. Understanding and Managing Operations Master Roles Understanding the Operations Master Roles Active Directory operates in a multi-master replication manner. What this means is that each domain controller in the domain holds a readable, writable replica of the Active Directory data store. In multi-master replication, any domain controller is able to change objects within Active Directory. Multi-master replication is ideal for the majority of information located in Active Directory. However, certain Active Directory functions or operations are not managed in a multi-master manner because they cannot be shared without causing some data uniformity issues. These functions are called Flexible Single Master Operations (FSMOs). There are five Operations Master (OM) roles which are automatically installed when you install the first domain controller. These five OMs are installed on the domain controller. Two of these OM roles apply to the entire Active Directory forest. The roles that apply to the forest are the Schema Master role and the Domain Naming Master role. The other three OM roles apply to each domain. The roles that apply to a domain are the Relative identifier (RID)/relative ID Master role, the Primary Domain Controller (PDC) Emulator role, and the Infrastructure Master role. When a domain controller is assigned a FSMO, that domain controller becomes a role master. The particular domain controller that is assigned these roles performs single-master replication within the Active Directory environment. Because domain controllers generally contain the same Active Directory information, when one domain controller is unavailable, the remainder of the domain controllers are able to provide access to Active Directory objects. However, if the domain controller that is lost has one of these OM roles installed, you could find that no new objects can be added to the domain. Forest-Wide Operations Master Roles Each Forest-wide OM role can exist on only one domain controller in the entire forest. What this means is that these roles have to be unique in the entire forest. The two forestwide OM roles are: Schema Master role: Because the objects that exist in the in the schema directory partition define the Active Directory structure for a forest, great control is placed on who can add objects to this partition. Since each domain controller in an Active Directory environment have a common schema, the information in the schema has to be consistent on each domain controller. It is the domain controller that is assigned the Schema Master role that controls which objects are added, changed, or removed from the schema. The domain controller with the Schema Master role is the only domain controller in the entire Active Directory forest that can perform any changes to the schema. You can use the Active Directory Schema MMC snap-in to make changes to the schema, and only if you are a member of the Schema Admins group. Any changes made to the schema would affect each domain controller within the Active Directory forest. You can transfer the Schema Master role to a different domain controller within the forest. You can also seize the role if the existing domain controller holding the role had a failure and cannot be recovered. Domain Naming Master role: As is the case with the Schema Master role, only one Domain Naming Master role is allowed in the entire forest. The domain controller that is assigned the Domain Naming Master role is responsible for tracking all the domains within the entire Active Directory forest to ensure that duplicate domain names are not created. The domain controller with the Domain Naming Master role is accessed when new domains are created for a tree or forest. This ensures that domains are not simultaneously created within the forest. The default configuration is that the first domain controller promoted in a forest, is assigned this role. You can however transfer the Domain Naming Master role to a different domain controller within te forest. Domain-Wide Operations Master Roles The three domain-wide OM roles have to unique in each domain within a forest. What this means is that there should be one of each of these roles in each domain. The three domain-wide OM roles are: Relative identifier (RID) Master role: When a security object is created within Active Directory, it is allocated a security ID. The security ID is made up of the domain security ID and a relative ID. The domain security ID is exactly the same for each security ID created in the particular domain. The relative ID on the other hand is unique to each security ID created within the domain. Because each relative ID has to be unique, the domain controller that is assigned the RID Master role is responsible for tracking and for assigning unique relative IDs to domain controllers whenever new objects are created. To ensure efficiency when assigning relative IDs to domain controllers, the domain controller assigned the RID Master role actually generates a set of 500 relative IDs to allocate to domain controllers. As the number of available relative IDs decreases, the RID Master generates more relative IDs to maintain the number of relative IDs available as 500. The default configuration is that the RID Master role and PDC Emulator role is assigned to the identical domain controller. You can however transfer the RID Master role to a different domain controller within the domain. PDC Emulator role: In domains that contain Windows NT Backup Domain Controllers (BDCs), the domain controller which is assigned the PDC Emulator role functions as the Windows NT Primary Domain Controller (PDC). The PDC Emulator role has importance when it comes to replication – BDCs only replicate from a Primary Domain Controller! Objects that are security principles can only be created and replicated by the PDC Emulator. Security principles are Users, Computers, and Groups. It is therefore the PDC Emulator that enables down-level operating systems to co-exist in Windows 2000 and Windows Server 2003 Active Directory environments. After the domain is operating in the Windows Server 2003 functional level, the domain controller assigned the PDC Emulator role continues to perform other operations for the domain. These additional functions include the following: o All password changes and account lockout requests are forwarded to the PDC Emulator. A domain controller within a domain checks first with the PDC Emulator to verify whether a bad password provided by a user was a recently changed password, and is therefore a valid password. o Group policies consist of a Group Policy Container (GPC) in Active Directory, and a Group Policy Template (GPT) in the SYSVOL folder. Because these two items can become out of sync due to multi-master replication, the Group Policy Editor is by default set to the PDC Emulator. This prevents group policy changes from being made on all domain controllers within the domain. Infrastructure Master role: The domain controller assigned the Infrastructure Master role has the following functions within the domain: o Updates the group-to-user references when the members of groups are changed. These updates are sent by the Infrastructure Master to the remainder of the domain controllers within the domain via multi-master replication. o Deletes any stale or invalid group-to-user references within the domain. To do this, the Infrastructure Master role checks with the Global Catalog for stale group-to-user references. Planning the Placement of the FSMOs A mentioned previously, all the OM roles are by default automatically assigned to the first domain controller created for the first domain in a new Active directory forest. Then, when you create either a root domain of a new tree in a forest, or a new child domain, the three domain specific OM roles are assigned to the first domain controller in that domain. In cases where a doain has only one domain controller, each domain specific OM role has to exist on that single domain controller. The two forest specific OM roles stay on the initial domain controller for the first domain created within the forest. OM roles are usually transferred to other domain controllers when you need to perform maintenance activities, or load balance the existing load of the domain controllers, or simply move the particular OM role to a better equipped domain controller. In instances where multiple domain controllers exist for a particular domain, consider the following recommendations when placing your Operations Master roles within the domain: Where you have two domain controllers that are direct replication partners and are well-connected, assign the RID Master role, PDC Emulator role and Infrastructure Master role to one domain controller. This particular domain controller would become the OM domain controller for the domain. The remaining domain controller would become the designated standby OM domain controller. It is generally recommended to assign the PDC Emulator and RID Master roles to the same domain controller. However, if the domain which you are placing FSMO roles for is large in size, consider locating the RID Master role and PDC Emulator role on two different domain controllers. Each of these domain controllers should be well-connected to the domain controller designated as the standby OM domain controller for these two roles. This strategy is usually implemented to reduce the load on the domain controller assigned the PDC Emulator. You should place the Schema Master role and the Domain Naming Master role on the same domain controller. You should refrain from assigning the Infrastructure Master role to a domain controller that contains the Global Catalog. The domain controller assigned the Infrastructure Master role should be well-connected to the Global Catalog server. The Infrastructure Master would not operate correctly if the Global Catalog is hosted on the identical domain controller. Managing Operations Master Roles Since only one or a few domain controllers are assigned the Operations Master roles, it is important that these specific domain controllers remain functioning in the Active Directory environment. There are essentially two processes involved in the management of FSMOs. These management tasks are outlined below: Because the FSMOs are automatically created when the first domain controller is installed, you might need to transfer OM roles to a more robust server. You would also need to transfer OM roles to a different server before demoting the domain controller hosting them. When a lost domain controller cannot be recovered, you would to need any seize OM roles assigned to the particular domain controller. Transferring an Operations Master role, involves moving it from one server to a different server. To transfer the Schema Master role, you need to have Schema Admins rights, and to transfer the Domain Naming Master role, you need to have Enterprise Admin rights. You can use an Active Directory console or a command-line utility to transfer OM roles. The Active Directory MMC consoles that can be utilized to transfer the different FSMOs are outlined below: Active Directory Schema MMC snap-in: For transferring the Schema Master role Active Directory Domains and Trusts console: For transferring the Domain Naming Master role Active Directory Users and Computers console: For transferring the RID Master role, PDC Emulator role, and Infrastructure Master role. When you seize an OM role, you do it without the cooperation of the existing domain controller that is assigned with the particular OM role. When an OM role is seized, it is basically reassigned to a different domain controller. Before you attempt to seize any OM roles, first try to determine what the reason is for the filure of the existing domain controller which is assigned with the particular OM role. Certain network issues which are likely to be corrected in short time fames are well worth enduring through. Before you seize OM roles, first ensure that the domain controller you are planning to shift these roles to; is indeed powerful enough to uphold these roles. In summary, you should only really seize an OM role if the existing OM cannot be recovered again. You would need to use the Ntdsutil tool command-line tool to seize OM roles. The Consequences of FSMOs Failing The following section looks at what actually happens when each FSMO role fails: A Schema Master failure is basically only evident when an Administrator attempts to change the Active Directory schema. What this means is that a Schema Master failure is invisible to your standard network users. You should only seize this role to the domain controller designated as the standby schema master if the existing Schema Master can in fact never be recovered. As is the case with a Schema Master failure, Domain Naming Master failure is only evident if an Administrator is attempting to add a domain to the forest, or remove a domain from the forest. A Domain Naming Master failure can generally not be perceived by your standard network users. You should only seize this role to the domain controller designated as its standby when the existing Domain Naming Master would never be operational again. A RID Master failure is only evident to Administrators if they are attempting to add new Active Directory objects in the particular domain where the RID Master failed. When this happens, the RID Master is unable to allocate relative IDs to the domain controllers on which the new Active Directory objects are being created. A RID Master failure cannot be detected by your conventional network users. You should also generally only seize this OM role when the existing domain controller assigned with the RID Master role would never recover from the failure. An Infrastructure Master failure is also not visible to your standard network users. The failure only impacts Administrators that are attempting to move user accounts, or rename them. Consider moving the role to the designated standby domain controller if the existing domain controller assigned with the Infrastructure Master is to be unavailable for a reasonably extended period of time, and the changes that need to be made are pertinent. Unlike the OM role failures previously described that are not evident to your standard network users, a PDC Emulator failure does impact network users. It is important to immediately seize this role to its designated standby domain controller if the domain contains any Windows NT backup domain controllers. You can always return this role to its previous domain controller when it is recovered and online again. How to view the existing Schema Master role assignment 1. Open a command prompt, and enter regsvr32 schmmgmt.dll to register the schmmgmt.dll on the computer. 2. Click Start, Run, and enter mmc in the Run dialog box. Click OK. 3. From the File menu, select Add/Remove Snap-in and then select Add. 4. In the list of available snap-ins, double-click Active Directory Schema. 5. Click Close. Click OK. 6. Open the Active Directory Schema snap-in. 7. In the console tree, right-click Active Directory Schema and select Operations Masters from the shortcut menu. 8. The Change Schema Master dialog box opens. 9. You can view the name of the existing Schema Master in the Current Schema Master (Online) box. 10. Click Close. How to view the existing Domain Naming Master role assignment 1. Open the Active Directory Domains And Trusts console from the Administrative Tools menu. 2. In the console tree, right-click Active Directory Domains And Trusts and select Operations Masters from the shortcut menu. 3. The Change Operations Master dialog box opens. 4. You can view the name of the existing Domain Naming Master in the Domain Naming Operations Master box. 5. Click Close. How to view the existing RID Master role, PDC Emulator, and Infrastructure Master role assignments 1. Open the Active Directory Users And Computers console from the Administrative Tools menu. 2. In the console tree, right-click Active Directory Users And Computers and click All Tasks, and then Operations Masters from the shortcut menu. 3. The Operations Masters dialog box contains the following tabs: o RID tab: The name of the existing RID Master is displayed in the Operations Master box of this tab. o PDC tab: In the Operations Master box of the PDC tab, you can view the name of the existing PDC Emulator. o Infrastructure tab: The existing Infrastructure Master's name is displayed in the Operations Master box. 4. Click Close. How to transfer the Schema Master role to another domain controller Before you can transfer the Schema Master role to another domain controller, ensure that you have the required Schema Admins rights, and that both domain controllers you are planning to work with are available. Before you can use the Active Directory Schema MMC snap-in, you first have to add it to a MMC. To add the Active Directory Schema snap-in to a MMC, 1. Open a command prompt, and enter regsvr32 schmmgmt.dll to register the schmmgmt.dll on the computer. 2. Click Start, Run, and enter mmc in the Run dialog box. Click OK. 3. From the File menu, select Add/Remove Snap-in and then select Add. 4. In the list of available snap-ins, double-click Active Directory Schema. 5. Click Close. Click OK To transfer the Schema Master role, 1. Open the Active Directory Schema snap-in. 2. Right-click Active Directory Schema in the console tree, and select Change Domain Controller from the shortcut menu. 3. The options available when the Change Domain Controller dialog box opens are o Any DC: If this option is selected, Active Directory will select a new domain controller for the Schema Master role. o Specify Name: If this option is enabled, you have to enter the name of the new location for the Schema Master Role. 4. Click OK 5. Right-click Active Directory Schema in the console tree again, and choose Operations Master from the shortcut menu. 6. When the Change Schema Master dialog box opens, click Change. 7. Click OK when a message appears prompting for verification of the OM role transfer you want to perform. 8. Click OK to exit the Change Schema Master dialog box. How to transfer the Domain Naming Master role to another domain controller You have to be a member of the Enterprise Admin group to transfer the Domain Naming Master role to another domain controller. 1. Open the Active Directory Domains And Trusts console from the Administrative Tools menu. 2. In the console tree, right-click Active Directory Domains And Trusts and select Connect To Domain Controller from the shortcut menu. 3. The Connect To Domain Controller dialog box opens. This is where you specify the name of the new domain controller that should be assigned the Domain Naming Master role. 4. Click OK 5. In the console tree, right-click Active Directory Domains And Trusts and select Operations Masters from the shortcut menu. 6. When the Change Operations Master dialog box opens, click Change 7. Click Close How to transfer the RID Master role, PDC Emulator role, or Infrastructure Master role to another domain controller 1. Open the Active Directory Users And Computers console from the Administrative Tools menu. 2. In the console tree, right-click Active Directory Users And Computers and click Connect To Doman from the shortcut menu. 3. When the Connect To Domain dialog box opens, enter the domain name that you want to work with. 4. Click OK 5. In the console tree, right-click Active Directory Users And Computers and click Connect To Domain Controller from the shortcut menu. 6. When the Connect To Domain Controller dialog box opens, specify the new domain controller for the OM role that you are transferring. 7. Click OK 8. In the console tree, right-click Active Directory Users And Computers and click All Tasks, and then click Operations Masters from the shortcut menu. 9. The Operations Masters dialog box opens. On one of the following tabs, o RID tab: Click Change to change the location of the RID Master o PDC tab: Click Change to change the location of the PDC Emulator o Infrastructure tab: Click Change to change the location of the Infrastructure Master. 10. Click Yes to verify that you want to transfer the particular OM role to a different domain controller. 11. Click OK. Click Close. How to seize an Operations Master role When you seize an OM role, you need to perform the following tasks: Verify that the new domain controller for the role is completely updated with changes performed on the existing domain controller of the particular role. You can use the Replication Diagnostics command-line utility for this verification. Repadmin.exe is included with the Windows Support Tools on the Windows Server 2003 CD-ROM. You would not use the Ntdsutil tool to seize the particular OM role. The Ntdsutil tool first attempts to transfer the role before it actually proceeds to seize the role. However, if you need to seize the PDC Emulator or Infrastructure FSMOs, you can use the Active Directory Users and Computers console. The Ntdsutil tool has to though be used to seize the other FSMOs – Schema Master role, Domain Naming Master role, and RID Master role. You can however also use the Ntdsutil tool to seize the PDC Emulator role or Infrastructure Master role. To seize the PDC Emulator or Infrastructure FSMOs using the Active Directory Users and Computers console, 1. Open the Active Directory Users and Computers console 2. In the console tree, right-click the domain object, and choose Connect to Domain Controller from the shortcut menu. 3. Enter the name of the other domain controller. Click OK 4. To perform the seizure of the role, right-click the domain object and choose Operations Masters from the shortcut menu. 5. Click either the PDC tab, or the Infrastructure tab 6. You will notice that the particular OM role is indicated as being offline. 7. Click Change. 8. Click OK to verify that you want to transfer the OM role. 9. Click Yes when prompted to verify that you want to perform a forced transfer. To seize any OM roles using the Ntdsutil tool, 1. 2. 3. 4. 5. 6. 7. 8. 9. Click Start, Command Prompt. Enter the following at the command prompt: ntdsutil. Press Enter Enter the following at the ntdsutil prompt: roles. Press Enter Enter the following at the fsmo maintenance prompt: connections. Press Enter Enter the following at the server connections prompt: connect to server, and the fully qualified domain name (FQDN). Press Enter Enter the following at the server connections prompt: quit. Press Enter. Enter one of the following at the fsmo maintenance prompt: o seize schema master. Press Enter o seize domain naming master. Press Enter o seize RID master. Press Enter o seize PDC. Press Enter o seize infrastructure master. Press Enter Enter quit at the fsmo maintenance prompt. Press Enter Enter quit at the ntdsutil prompt. How to perorm a metadata cleanup The class objects and attribute objects of the schema are referred to as metadata. A metadata cleanup is usually performed when you are unable to restore a failed domain controller. The cleanup removes any references to the failed domain controller in Active Directory. To perform the metadata cleanup, 1. 2. 3. 4. From the command prompt, enter ntdsutil and press Enter. Enter the following at the ntdsutil prompt: metadata cleanup. Press Enter Enter the following at the metadata cleanup prompt: connections. Press Enter Enter the following at the server connections prompt: connect to server, followed by the server name. Press Enter 5. Enter quit, and press Enter 6. Enter the following at the metadata cleanup prompt: select operation target. Press Enter 7. Enter list domains. Press Enter 8. Enter select domain, followed by the number of the domain that holds the server that you want to remove. Press Enter 9. Enter list sites. Press Enter 10. Enter select site, followed by the number of the site that holds the server that you want to remove. Press Enter 11. Enter list servers in site. Press Enter 12. Enter select server, followed by the number of the server that you want to remove. Press Enter. 13. Enter quit and press Enter to return to the metadata cleanup prompt. 14. Enter remove selected server, and press Enter. 15. When a message box appears prompting you to verify whether the server should be removed, click Yes 16. Quit from Ntdsutil. Understanding Server Roles Server Roles Overview A network or network infrastructure is the grouping of hardware devices and software components which are needed to connect devices within the organization, and to connect the organization to other organizations and the Internet. The network infrastructure's physical hardware and logical components are needed to provide a number of features for the network, including connectivity, routing and switching capabilities, network security, and access control. The network or network infrastructure has to exist before a number of servers needed to support applications which are needed by your users can be deployed into your networking environment. Therefore, when planning your network design and deciding on the computers for your network, you must know what functions the computer will be performing. Understanding these functions will put you in a good position to determine the hardware and software components needed for your computers. Windows Server 2003 itself provides a number of features and tools when you install it on a computer. You though have to implement additional features and functionality on a server to provide the services and capabilities required by the organization and its users. In fact, until these additional features and functionality make certain services available, the computer cannot be used as required by users. Computers required on your network can be broadly grouped according to the following roles: Server roles: Servers can be configured to perform a number of roles. The applications that the server is running specify the role of the particular server. Server's typically need services and additional features installed to perform its specific role. When compared to workstations, servers have more disk space and memory, and faster processors. The hardware required by servers is determined by the role being performed by the server. A few common server roles are listed below: o Domain controller o Database server o Backup server o File server o Print server o Infrastructure server o Web server o E-mail server Desktop workstation roles: Desktop workstations differ to servers in that desktop workstations are general purpose computers that can perform a number of different types of functions. Portable workstation roles: Portable workstations are the solution to bringing the features of a desktop computer to an off-site employee. Windows Server 2003 introduced the concept of server roles. Server roles basically group related administrative tasks, and are used to provide a specific capability or function to the network design. With Windows Server 2003, if you configure a server for a certain server role, then a number of additional services, features and tools are installed for the server. In this manner, the server is set up to provide the required services to your users. Windows Server 2003 provides a new tool for defining and managing server roles, namely, the Manage Your Server utility. The actual Wizard for applying the server roles to computers is the Configure Your Server Wizard. The Configure Your Server Wizard is included within the Manage Your Server utility and is also managed through this utility. For Windows Server 2003, there are 11 different server roles that you can configure using the Configure Your Server Wizard: File server Print server Application server Mail server Terminal server Remote access server/VPN server Domain controllers DNS server WINS server DHCP server Streaming media server Understanding the File Server Role The file server role is a widely used role when configuring servers in Windows Server 2003 based networks. This is due to the file server role storing data for network users, and providing access to files stored on the file server. The file server role is though not availble in the Windows Server 2003 Web Edition. A file stored on a file server volume can be accessed by users that have the necessary rights to access the directories wherein the files are stored. File servers provide the following functionality to users: Enables users to store files in a centralized location. " Enable a user to share files with another user. A few characteristics and features of the file server role are listed: Files and folder resources can be shared between network users. Administrators can manage the following aspects of file servers: o Access to files and folders o Disk space o Disk quotas can be implemented to control the amount of space which users can utilize. For file servers that have NTFS volumes: o NTFS security can be used to protect files from users who are not authorized to access the files and folders. o Encrypting File System (EFS) enables users to encrypt files and folders, and entire data drives on NTFS formatted volumes. EFS secures confidential corporate data from unauthorized access. o Distributed File System (Dfs) provides a single hierarchical file system that assists in organizing shared folders on multiple computers in the network. Dfs provides a single logical file system structure by concealing the underlying file share structure within a virtual folder structure. Users only see a single file structure even though there are multiple folders located on different file servers within the organization. The Offline files feature can be enabled if necessary. Offline Files make is possible for a user to mirror server files to a local laptop, and ensures that the laptop files and server files are in sync. For your laptop users, Offline Files ensures that the user can access the server based files when they are not connected to the network. Understanding the Print Server Role The print server role provides network printing capabilities for the network. Through the print server role, you can configure a server to manage printing functions on the network. Users typically connect to a network printer through a connection to a print server. The print server is the computer where the print drivers are located that manage printing between printers and client computers. With Windows NT, Windows 2000, Windows XP, and Windows Server 2003, the print servers supply clients with the necessary printer drivers. The print servers also manage communication between the printers and the client computers. The print servers manage the print queues, and can also supply audit logs on jobs printed by users. A network interface printer is a printer that connects to the network through a network card. The print server role is though not available in the Windows Server 2003 Web Edition. When deciding on a print server, ensure that the print server has sufficient disk space to store print jobs waiting in the printer queue. It is recommended to use a dedicated, fast drive for the print spooler. You should consider implementing a print server cluster if your enterprise needs exceptional reliability and performance when it comes to printing. A few characteristics of print servers are listed here: The Windows Management Instrumentation (WMI) a management application program interface (API) can be used to manage printing on the network. Print servers can also be remotely managed. Administrators can control when printing devices can be utilized. Administrators can control access to printers Priorities can be defined for print jobs. Print jobs can be paused, resumed, and deleted and viewed. Printers can be published in Active Directory so that access to printers can be controlled according to Active Directory accounts. Understanding Web servers The application server role makes Web applications and distributed applications available to users. A Web server typically contains a copy of a World Wide Web site and can also host Web based applications. When you install a Web server, users can utilize Web based applications and download files as well. When you add a Web server through the application server role, the following components are installed: Internet Information Services 6.0 The Application Server console The Distributed Transaction Coordinator (DTC) COM+, the extension of the Component Object Model (COM) Internet Information Services 6.0 (IIS 6.0) is Microsoft's integrated Web server that enables you to create and manage Web sites within your organization. Through IIS, you can create and manage Web sites, and share and distribute information over the Internet or intranet. With the introduction of Windows Server 2003, came the advent of Internet Information Services (IIS) 6. IIS 6 is included with the 32-bit version and the 64-bit versions of the Windows Server 2003 Editions. IIS 6 include support for a number of protocols and management tools which enable you to configure the server as a Web server, File Transfer Protocol (FTP) server or a Simple Mail Transport Protocol (SMTP) server. The management tools included with Windows Server 2003 allows you to manage Internet Information Services on the Windows Server 2003 product platforms. Before you can deploy IIS 6 Web servers within your enterprise, you first need to install Windows Server 2003 or upgrade to Windows Server 2003. Only after Windows Server 2003 is deployed, are you able to install IIS 6 in your environment. After Windows Server 2003 is installed, for all editions of Windows Server 2003 other than the Web Edition, you can install IIS 6 from the Configure Your Server Wizard. When you first log on after Windows Server 2003 is installed, the Manage Your Server Wizard is initiated. To start the Configure Your Server Wizard, choose the Add Or Remove A Role link. You next have to follow the prompts of the Configure Your Server Wizard to install the Application Server (IIS, ASP.NET) option. The protocols supported by IIS 6.0, the Microsoft integrated Web server, are listed here: Hypertext Transfer Protocol (HTTP) is a TCP/IP application layer protocol used to connect to websites, and to create Web content. HTTP handles the publishing of static and dynamic Web content. A HTTP session consists of a connection, a HTTP request and a HTTP response 1. Port 80 is used for HTTP connections. The client establishes a TCP connection to the server by using a TCP three way handshake. 2. After the connection is established, the client sends a HTTP GET request message to the server. 3. The server sends the client the requested Web page. 4. HTTP Keep-Alives maintains the TCP connection between the client and server if it is enabled, so that the client can request additional pages. 5. If HTTP Keep-Alives is not enabled, the TCP connection is terminated after the requested page is downloaded. File Transfer Protocol (FTP) is a TCP/IP application layer protocol used for copying files to and from remote systems through the Transmission Control Protocol (TCP). FTP makes it possible for clients to upload and download files from a FTP server over an internetwork. Through IIS, you can create and administer FTP servers. You need an FTP server and FTP client to use the protocol. A FTP session has a connection, a request, and a response. 1. The client establishes a TCP connection to the FTP server through port 21. 2. A port number over 1023 is assigned to the client. 3. The client sends a FTP command to port 21. 4. If the client needs to receive data, another connection is created with the client, to convey the data. This connection utilizes port 20. 5. The second connection remains in a TIME_WAIT state afte the data is transferred to the client. The TIME_WAIT state makes it possible for additional data to be transferred. The TIME_WAIT state ends when the connection timeout. Network News Transfer Protocol (NNTP) is a TCP/IP application layer protocol used to send network news messages to NNTP servers and NNTP clients on the Internet. NNTP is a client/server and server/server protocol. The NNTP protocol enables a NNTP host to replicate its list of newsgroups and messages with another host through newsfeeds, using a push method or a pull method. A NNTP client can establish a connection with a NNTP host to download a list of newsgroups, and read the messages contained in the newsgroups. Through NNTP, you can implement private news servers to host discussion groups, or you can implement public news servers to provide customer support and help resources to Internet users. You can specify that users need to be authenticated to both read and post items to newsgroups, or you can allow access to everybody. The NNTP service can also integrate with the Windows Indexing Service for the indexing of newsgroup content. It is also fully integrated with event and performance monitoring of Windows Server 2003. Simple Mail Transfer Protocol (SMTP) is a TCP/IP application layer protocol used for routing and transferring e-mail between SMTP hosts on the Internet. SMTP enables IIS machines to operate as SMTP hosts to forward e-mail over the Internet. IIS can be utilized instead of Sendmail. SMTP also enables IIS machines to protect mail servers such as Microsoft Exchange servers from malicious attacks by operating between these servers and Sendmail host at the ISP of the organization. SMTP can be used to forward mail from one SMTP host to another SMTP host. SMTP cannot deliver mail directly to the client. Mail clients use POP3 or IMAP to receive e-mail. Windows Server 2003 includes the POP3 service for providing clients with mailboxes, and for handling incoming e-mail. To use the SMTP as a component of IIS, you have to install the SMTP service first if you are running a Windows Server 2003 Edition other than the Windows Server 2003 Web Edition. The SMTP service is installed on the Windows Server 2003 Web Edition by default. Understanding the Mail Server Role The mail server role provides e-mail services for the network, by providing the functionality needed for users to both send and receive e-mail messages. A mail server has to exist for users to send e-mail to each other. When a mail server receives e-mail for a user, it stores the e-mail for the intended user until that particular user retrieves it from the mail server. The primary functions of mail servers are listed here: Store e-mail data. Process client requests Receive incoming e-mail from the Internet. When you configure a server for the mail server role, the following TCP/IP based protocols are installed: Simple Mail Transfer Protocol (SMTP): SMTP is a TCP/IP application layer protocol used for routing and transferring e-mail between SMTP hosts on the Internet. IIS 6 has to be installed to install both the SMTP service and the Post Office Protocol 3 (POP3) service. The SMTP service has to be installed because mail servers and clients utilize this service to send e-mail. Post Office Protocol 3 (POP3): Mail clients use the POP3 service or IMAP to receive e-mail. Windows Server 2003 includes the POP3 service for providing clients with mailboxes, and for handling incoming e-mail. The POP3 service also enables clients to retrieve e-mail from the mail server. Understanding the Terminal Server Role Terminal Services have the ability to operate as an application server that remote clients can connect to, and run sessions from. The Terminal Services server runs the applications. The data response is transmitted back to the Terminal Services client. Clients can access Terminal Services over a local areaconnection or a wide area connection. Terminal Services clients can be MS-DOS based clients, Windows for Workgroups clients, (version 3.11), Windows based terminals, and Macintosh clients. When a user connects to a Windows Server 2003 server using Remote Desktop, the resources of the server is used, and not that of the workstation. The terminal is only responsible for the keyboard, mouse and the display. Every user has its own individual Terminal Services session. Sessions are unique and do not affect one another. In this manner, a user connecting to a Windows Server 2003 server through Remote Desktop functions as a terminal on that server. Once a client establishes a connection to Terminal Services, it creates a Terminal Services session for the client. All processing is handled by the Terminal Services server. Clients use insignificant bandwidth on the underlying network when they establish a connection. Terminal Services is therefore popular in WANs where bandwidth is limited. It is also suited for mobile users who have to execute processor intensive applications over a dial-up connection. In this case, the local machine only needs to handle the console. When applications need to be installed or updated, a single instance of the application can be installed or updated on the Terminal Services server. Users will have access to the application without you needing to install or update the application on all machines. Remote Desktop Protocol (RDP) is the protocol that manages communications between a computer running Terminal Services, and a client computer running a Terminal Server client. The connection can be established using Terminal Services on a terminal server. The RDC utility can be used for complete terminal server client utilization, or it can be used for Remote Administration. Remote Desktop Connection is by default installed with Windows XP and Windows Server 2003. You can however install Remote Desktop Connection on the previous Windows Operating Systems (OSs) such as Windows 2000, Windows NT, Windows ME, Windows 98, and Windows 95. The RDC utility is backward compatible, and can therefore interact with Terminal Services in Windows XP, Windows 2000 and Windows NT 4 Terminal Server Edition. Understanding the Remote Access and VPN Server Role The Windows Server 2003 remote access and VPN server role can be used to provide remote access to clients through either of the methods: Dial-up connections: Dial-up networking makes it possible for a remote access client to establish a dial-up connection to a port on a remote access server. The configuration of the dial-up networking server determines what resources the remote user can access. Users that connect through a dial-up networking server, connect to the network much like a standard LAN user accessing network resources. Virtual private networks (VPNs): Virtual Private Networks (VPNs) provide secure and advanced connections through a non-secure network by providing data privacy. Private data is secure in a public environment. Remote access VPNs provides a common environment where many different sources such as intermediaries, clients and off-site employees can access through web browsers or email. Many companies supply their own VPN connections via the Internet. Through their ISPs, remote users running VPN client software are assured private access in a publicly shared environment. By using analog, ISDN, DSL, cable technology, dial and mobile IP; VPNs are implemented over extensive shared infrastructures. Email, database and office applications use these secure remote VPN connections. A few features and capabilities provided by the RRAS server are listed here: LAN-to-LAN routing and LAN-to-WAN routing Virtual private network (VPN) routing Network Address Translation (NAT) routing: NAT, defined in RFC 1631 translates private addresses to Internet IP addresses that can be routed on the Iternet Routing features, including o IP multicasting o Packet filtering o Demand-dial routing o DHCP relay Assign DHCP addresses to RRAS clients Remote Access Policies (RAPs): RAPs are used to grant remote access permissions. Layer Two Tunneling Protocol (L2TP) combines Layer 2 Forwarding (L2F) of Cisco with Point-to-Point Tunneling Protocol (PPTP) of Microsoft. L2TP is a Data-link protocol that can be used to establish Virtual Private Networks (VPNs). Internet Authentication Service (IAS), a Remote Authentication Dial-In User Service (RADIUS) server, provides remote authentication, authorization and accounting for users that are connecting to the network through a network access server (NAS) such as Windows Routing and Remote Access. Understanding the Domain Controllers Role A domain controller is a server that stores a write copy of Active Directory, and maintains the Active Directory data store. Active Directory was designed to provide a centralized repository of information, or data store that could securely manage the resources of an organization. The Active Directory directory services ensure that network resources are available to, and can be accessed by users, applications and programs. Active Directory also makes it possible for administrators to log on to a one network computer, and then manage Active Directory objects on a different computer within the domain. A domain controller is a computer running Windows 2000 or Windows Server 2003 that contains a replica of the domain directory. Domain controllers in Active Directory maintain the Active Directory data store and security policy of the domain. Domain controllers therefore also provide security for the domain by authenticating user logon attempts. The main functions of the domain controller role within Active Directory are listed here: Each domain controller in a domain stores and maintains a replica of the Active Directory data store for the particular domain. Domain controllers in Active Directory utilize multimaster replication. What this means is that no single domain controller is the master domain controller. All domain controllers are considered peers. Domain controllers also automatically replicate directory information for objects stored in the domain between one another. Updates that are considered important are replicated immediately to the remainder of the domain controllers within the domain. Implementing multiple domain controllers within the domain provides fault tolerance for the domain. In Active Directory, domain controllers can detect collisions. Collisions take place when an attribute modified on one particular domain, is changed on a different domain controller prior to the change on the initial domain controller being fully propagated. Certain master roles can be assigned to domain controllers within a domain and forest. Domain controllers that are assigned special master roles are called Operations Masters. These domain controllers host a master copy of specific data in Active Directory. They also copy data to the remainder of the domain controllers. There are five different types of master roles that can be defined for domain controllers. Two types of master roles, forestwide master roles, are assigned to one domain controller in a forest. The other three master roles, domainwide master roles, are applied to a domain controller in every domain. The different types of master roles which can be configured on domain controllers are listed here: The Schema Master is a forestwide master role applied to a domain controller that manages all changes in the Active Directory schema. The Domain Naming Master is a forestwide master role applied to a domain controller that manages changes to the forest, such as adding and removing a domain. The domain controller serving this role also manages changes to the omain namespace. The Relative ID (RID) Master is a domainwide master role applied to a domain controller that creates unique ID numbers for domain controllers and manages the allocation of these numbers. The PDC Emulator is a domainwide master role applied to a domain controller that operates like a Windows NT primary domain controller. This role is typically necessary when there are computers in your environment running pre-Windows 2000 and XP operating systems. The Infrastructure Master is a domainwide master role applied to a domain controller that manages changes made to group memberships. A Global Catalog (GC) server(s) can also be installed on a domain controller. The global catalog is a central information store on the Active Directory objects in a forest and domain, and is used to improve performance when searching for objects in Active Directory. The first domain controller installed in a domain is designated as the global catalog server by default. The global catalog server stores a full replica of all objects in its host domain, and a partial replica of objects for the remainder of the domains in the forest. The partial replica contains those objects which are frequently searched for. It is generally recommended to configure a global catalog server for each site in a domain. The functions of the global catalog server are summarized below: Global catalog servers are crucial for Active Directory's UPN functionality because they resolve user principal names (UPNs) when the domain controller handling the authentication request is unable to authenticate the user account because the user account actually exists in another domain. Here, the GC server assists in locating the user account so that the authenticating domain controller can proceed with the logon request for the user. The global catalog server deals with all search requests of users searching for information in Active Directory. It can find all Active Directory data irrespective of the domain in which the data is held. The GC server deals with requests for the entire forest. The global catalog server also makes it possible for users to provide Universal Group membership information to the domain controller for network logon requests. Understanding the DNS Server Role Domain Name Service (DNS) is a hierarchically distributed database that creates hierarchical names that can be resolved to IP addresses. The IP addresses are then resolved to MAC addresses. DNS provides the means for naming IP hosts, and for locating IP hosts when they are queried for by name. The DNS server role resolves IP addresses to domain names, and domain name to IP addresses. In this way, DNS provides name resolution services to establish connections for those clients that need to resolve to IP addresses. A Fully Qualified Domain Name (FQDN) is the DNS name that is used to identify a computer on the network. A DNS server is a computer running the DNS service or BIND; that provides domain name services. The DNS server manages the DNS database that is located on it. The information in the DNS database of a DNS server pertains to a portion of the DNS domain tree structure or namespace. This information is used to provide responses to client requests for name resolution. A DNS server is authoritative for the contiguous portion of the DNS namespace over which it resides. When a DNS server is queried for name resolution services it can do either of the following: Respond to the request directly by providing the requested information. Provide a pointer (referral) to another DNS server that can assist in resolving the query. Respond that the information is unavailable. Respond that the information does not exist You can configure different server roles for your DNS servers. The server role that you configure for a DNS server affects the followin operations of the server: The way in which the DNS server stores DNS data. The way in which the DNS server maintains data. Whether the DNS data in the database file can be directly edited. The different DNS server roles which you can configure are listed here: Standard Primary DNS server: This DNS server owns the zones defined in its DNS database, and can make changes to its zones. A standard primary DNS server obtains zone data from the local DNS database. The primary DNS server is authoritative for the zone data that it contains. When a change needs to be made to the resource records of the zone, it has to be done on the primary DNS server so that is can be included in the local zone database. A DNS primary server is created when a new primary zone is added. Standard Secondary DNS server: This DNS server obtains a read-only copy of zones through DNS zone transfers. A secondary DNS server cannot make any changes to the information contained in its read-only copy. A secondary DNS server can however resolve queries for name resolution. Secondary DNS servers are usually implemented to provide fault tolerance, provide fast access for clients in remote locations, and to distribute the DNS server processing load evenly. If a secondary DNS server is implemented, that DNS server can continue to handle queries when the primary DNS becomes unavailable. Secondary DNS servers also assist in reducing the processing load of the primary DNS server. It is recommended to install at least one primary DNS server, and one secondary DNS server for each DNS zone. Caching-only DNS server: A caching-only DNS server only performs queries and then stores the results of these queries. All information stored on the caching-only DNS server is therefore only that data which has been cached while the server performed queries. Caching-only DNS servers only cache information when the queries have been resolved. The information stored by caching-only DNS servers is the name resolution data that it has collected through name resolution queries. Caching-only DNS servers do not host zones and are not authoritative for any DNS domain. Master DNS servers: The DNS servers from which secondary DNS servers obtain zone information in the DNS hierarchy are called master DNS servers. When a secondary DNS server is configured, you have to specify the master server from whom it will obtain zone information. Zone transfer enables a secondary DNS server to obtain zone information from its configured primary DNS server. A secondary DNS server can also transfer its zone data to other secondary DNS servers, who are beneath it in the DNS hierarchy. Here, the secondary DNS server is regarded as the master server to the other subordinate secondary DNS servers. A secondary DNS server initiates the zone transfer process from its particular master server when it is brought online. Dynamic DNS Servers: Windows 2000, Windows XP and Windows Server 2003 computers can dynamically update the resource records of a DNS server when a client's IP addressing information is added, or renewed through Dynamic Host Configuration Protocol (DHCP). Both DHCP and Dynamic DNS (DDNS) updates make this possible. When dynamic DNS updates are enabled, a client sends a message to the DNS server when changes are made to its IP addressing data. This indicates to the DNS server that the A type resource record of the client needs to be updated. Understanding the WINS Server Role The Windows Internet Name Service (WINS) server roles provide name resolution services for clients that need to resolve IP addresses to NetBIOS names, and vice versa. A WINS server is an enhanced NetBIOS name server (NBNS) designed by Microsoft to resolve NetBIOS computer names to IP addresses. WINS can resolve NetBIOS names for local hosts and remote hosts. WINS registers NetBIO computer names, and stores these client name registrations in the WINS database. The registrations are used when clients query for host name resolution and service information and to resolve a NetBIOS name to an IP address. Clients that are configured to utilize a WINS server as a NetBIOS name server (NBNS) are called WINS enabled clients. If the WINS server resolves the NetBIOS name to an IP address, no broadcast traffic is sent over the network. Broadcasts are only utilized if the WINS server is unable to resolve the NetBIOS name. A WINS enabled client can communicate with a WINS server that is located anywhere on the internetwork. Since Windows 2000 was the first Windows operating system where NetBIOS naming was no longer required, you might still need to provide support for NetBIOS naming if you have legacy applications. Remember that all Windows operating system prior to Windows 2000 require NetBIOS name support. To implement WINS, you only need one WINS server for an internetwork. However, implementing two WINS servers provides fault tolerance for name resolution. The secondary WINS server would be used for name resolution if the primary WINS server is unavailable to service WINS clients' requests. A WINS server can cope with 1,500 name registrations and roughly 4,500 name queries per minute. It is recommended to have one WINS server and a backup server for each 10,000 WINS clients. When you configure the WINS server role, the WINS server must be statically assigned with the following TCP/IP parameters: static IP address, subnet mask and default gateway. Understanding the DHCP Server Role DHCP is a service and protocol which runs on a Windows Server 2003 operating system. DHCP functions at the application layer of the TCP/IP protocol stack. One of the primary tasks of the protocol is to automatically assign IP addresses to DHCP clients. A server running the DHCP service is called a DHCP server. The DHCP protocol automates the configuration of TCP/IP clients because IP addressing occurs through the system. You can configure a server as a DHCP server so that the DHCP server can automatically assign IP addresses to DHCP clients, and with no manual intervention. IP addresses that are assigned through a DHCP server are regarded as dynamically assigned IP addresses. The DHCP server assigns IP addresses from a predetermined IP address range(s), called a scope. A DHCP scope can be defined as a set of IP addresses which the DHCP server can allocate or assign to DHCP clients. A scope contains specific configuration information for clients that have IP addresses which are within the particular scope. Scope information for each DHCP server is specific to that particular DHCP server only, and is not shared between DHCP servers. Scopes for DHCP servers are configured by administrators. The functions of the DHCP server are outlined below: Dynamically assign IP addresses to DHCP clients. Allocate the following TCP/IP configuration information to DHCP clients: o Subnet mask information o Default gateway IP addresses o Domain Name System (DNS) IP addresses o Windows Internet Naming Service (WINS) IP addresses You can increase the availability of DHCP servers by using the 80/20 Rule if you have two DHCP servers located on different subnets. The 80/20 Rule is applied as follows: Allocate 80 percent of the IP addresses to the DHCP server which resides on the local subnet. Allocate 20 percent of the IP addresses to the DHCP Server on the remote subnet. If the DHCP server that is allocated with 80 percent of the IP addresses has a failure, the remote DHCP server would resume assigning the DHCP clients with IP addresses. With Windows Server 2003 DHCP, three options are available for registering IP addresses in DNS. The options can be configured for the DHCP serve, or for each individual scope. The options which can be specified to enable/disable the DHCP service to dynamically update DNS records on behalf the client are: The DHCP server can be configured to not register any IP address of the DHCP clients when it assigns IP addresses to these clients. The DHCP server can be configured to at all times register all IP address of clients when they receive IP addresses from the DHCP server. The default option results in the DHCP server registering the IP addresses of clients with the authoritative DNS server, based on the client's request for an IP address. Understanding the Streaming Media Server Role The streaming media role provides media services so that clients can access streaming audio and video. The Windows Media Services is used to provide media services to clients. The Windows Media Services can be configured on server platforms, and on enterprise platforms. The Windows Media Services is not available in the following edition of Windows Server 2003: Windows Server 2003 Web Edition Windows Server 2003 64-bit versions. Understanding Certificate Authorities (CAs) Servers A Certificate Authority is an entity that generates and validates digital certificates. The CA adds its own signature to the public key of the client. By using the tools provided by Microsoft, you can create an internal CA structure within your organization. A digital certificate associates a public key with an owner. The certificate verifies the identity of the owner. A certificate cannot be forged because the authority that issued the certificate digitally signs the certificate. Certificates are issued for functions such as the encryption of data, code signing, Web user and Web server authentication, and for securing e-mail. Certificates in Windows XP and Windows Server 2003 are managed by the Data Protection API. When certificates are issued to a client, it is stored in the Registry and in Active Directory. You can also store certificates on smart cards. The information included in a certificate is determined by the type of certificate being used. Certificate Authorities (CAs) are servers which are configured to issue certificates to users, computers, and services. CAs also manage certificates. An organization can have multiple CAs, which are arranged in a logical manner. A CA can be a trusted third party entity such as VeriSign or Thawte, or it can be an internal entity of the organization. An example of an internal CA entity is Windows Server 2003 Certificate Services. Windows Server 2003 Certificate Services can be used to create certificates for users and computers in Active Directory domains. The functions performed by Certificate Authorities (CAs) are listed below: Accepts the request for a certificate from a user, computer, application, or service. Authenticates the identity of the user, computer or service requesting the certificate. The CA utilizes its policies, and incorporates the type of certificate being requested; to verify the identity of the requestor. Creates the certificate for the requestor. Digitally signs the certificate using its own private key. Windows Certificate Services is used to create a Certificate Authority on Windows Server 2003 servers. The first CA that is installed becomes the root CA. The common practice is to first install the root CA, and then use the root CA to validate all the other CAs within the organization. A root CA is the most trusted CA in a CA hierarchy. When a root CA issues certificates to other CAs, these CAs become subordinate CAs of the root CA. When a root CA is online, it is used to issue certificates to subordinate CAs. The root CA never usually directly issues certificates to users, computers, applications or services. A subordinate CA can also issue certificates to other subordinate CAs. These subordinate CAs are called intermediate CAs. While an intermediate CA s subordinate to the root CA, it is considered superior to those subordinate CAs to which it issued certificates. Subordinate CAs which only issue certificates to users, and not to other subordinate CAs, are called leaf CAs. The type of CAs which you can install: Enterprise root CA: This is the topmost CA in the CA hierarchy, and is the first CA installed in the enterprise. Enterprise root CAs are reliant on Active Directory. Enterprise root CAs issue certificates to subordinate CAs. Enterprise Subordinate CA: This CA also needs Active Directory, and is used to issue certificates to users and computers. Stand-alone Root CA: A stand-alone root CA is the topmost CA in the certificate chain. A stand-alone root CA is not however dependent on Active Directory, and can be removed from the network. This makes a stand-alone root CAs the solution for implementing a secure offline root CA. Stand-alone Subordinate CA: This type of CA is also not dependent on Active Directory, and is used to issue certificates to users, computers, and other CAs. Understanding the Configure Your Server Wizard The Configure Your Server Wizard is one of the main wizards used to perform administrative tasks for Windows Server 20033 computers. The Configure Your Server Wizard is used to configure server roles. Windows Server 2003 provides a new tool for defining and managing server roles, namely, the Manage Your Server utility. The actual Wizard for applying the server roles to computers is the Configure Your Server Wizard. The Configure Your Server Wizard is included within the Manage Your Server utility and is also managed through this utility. To access the Manage Your Server utility and use the Configure Your Server Wizard, 1. Click Start, click Administrative Tools, and then click Manage Your Server. The main screen of the Manage Your Server utility is made up as follows: At the top of the Manage Your Server main screen, are three buttons, labelled as follows: o Add or remove a role button; for initiating the Configure Your Server Wizard. o Read about server roles button; for accessing information on server roles. o Read about remote administration button; for accessing information on remote administration. The left end of the screen contains the server roles which are already configured for the particular server. Each listed configured server role is accompanied by buttons which can be used to view information on the existing role, or manage the existing server role. The buttons which are displayed differ between the existing server roles. You can also initiate the Configure Your Server Wizard by: 1. Clicking Start, Administrative Tools, and then clicking Configure Your Server. After the Configure Your Server Wizard is initiated, the following preliminary steps need to be performed first before any server roles can be added: Install all modems and network cards. Attach all necessary cables. Create an Internet connection if the server is to be used for Internet connectivity. Turn on all peripherals Have the Windows Server 2003 installation CD at hand. Clicking the Next button on the Preliminary Steps screen invokes the Configure Your Server Wizard to test network connections and verify the operating system, and then displays the Server Role screen. The Server Role screen contains the following columns: Server role column; indicates the server roles which can be added or removed. Configured column; indicates whether a server role is configured or not configured. If you want to navigate to the Add or Remove Programs in Control Panel, click the Add or Remove Programs link on the Server Role screen. How to add an application server role to Windows Server 2003 1. 2. 3. 4. 5. Click Start, click Administrative Tools, and then click Manage Your erver. Click the Add or remove a role button. The Configure Your Server Wizard initiates. Click Next on the Preliminary Steps page of the wizard. When the Server Role page opens, select the Application server (IIS, ASP.NET) server role, and then click Next. 6. The Application Server Options page opens. 7. Select the FrontPage Server Extensions checkbox to include Web server extensions in the configuration. 8. Select the Enable ASP.NET checkbox so that Web applications created through ASP.NET can be utilized. Click Next. 9. Verify the settings which you have selected on the Summary of Selections. Click Next. 10. The installation of the components occurs next. 11. Click Finish. How to install the Remote Access and VPN server role using the using the Configure Your Server Wizard 1. 2. 3. 4. 5. Click Start, click Administrative Tools, and then click Manage Your Server. Select the Add or remove a role option. The Configure Your Server Wizard starts. On the Preliminary Steps page, click Next. A message appears, informing you that the Configure Your Server Wizard is detecting network settings and server information. 6. When the Server Role page appears, select the Remote Access/VPN Server option and then click Next. 7. On the Summary of Selections page, click Next. 8. The Welcome to the Routing and Remote Access Server Setup Wizard page is displayed. How to add the global catalog server role on a domain controller 1. Click Start, Administrative Tools, and then click Active Directory Sites and Services. 2. In the console tree, expand Sites, and then expand the site that contains the domain controller which you want to configure as a global catalog server. 3. Expand the Servers folder, and locate and then click the domain controller that you want to designate as a global catalog server. 4. In the details, pane, right-click NTDS Settings and click Properties on the shortcut menu. 5. The NTDS Settings Properties dialog box opens. 6. The General tab is where you specify the domain controller as a global catalog server. 7. Enable the Global Catalog checkbox. 8. Click OK. How to remove the global catalog server role from a domain controller 1. Open the Active Directory Sites and Services console. 2. In the console tree, locate and click the domain controller currently configured as the global catalog server. 3. Right-click NTDS Settings and click Properties on the shortcut menu to open the NTDS Settings Properties dialog box. 4. Clear the Global Catalog checkbox. 5. Click OK How to install the DHCP server role 1. Click Start, Control Panel, and then click Add Or Remove Programs. 2. When the Add Or Remove Programs dialog box opens, click Add/Remove Windows Components. 3. This starts the Windows Components Wizard. 4. In the Components list box, select Networking Services, and then click the Details button. 5. The Networking Services dialog box opens. 6. In the Subcomponents Of Networking Services list box, check the Dynamic Host Configuration Protocol (DHCP) checkbox. 7. Click OK. Click Next. 8. When The Completing The Windows Components Wizard page is displayed, click Finish. How to implement a caching-only DNS server 1. Open Control Panel 2. Double-click Add/Remove Programs., and then click Add/Remove Windows Components. 3. The Windows Components Wizard starts. 4. Click Networking Services, and then click Details. 5. In the Networking Services dialog box, select the checkbox for Domain Name System (DNS) in the list. Click OK. Click Next. 6. When The Completing The Windows Components Wizard page is displayed, click Finish. 7. Do not add or configure any zones for the DNS server. The DNS Server service functions as a caching-only DNS server by default. This basically means no configuration is necessary to set up a caching-only DNS server. 8. You should verify that the server root hints are configured correctly. How to add the Terminal Services server role to Windows Server 2003 using Add Or Remove Programs in Control Panel 1. Click Start, Control Panel, and then click Add Or Remove Programs. 2. Click Add/Remove Windows Components to initiate the Windows Components Wizard 3. Select the Terminal Server checkbox. Click Next 4. When the Terminal Server Setup page is displayed, read the message on Terminal Server Licensing and Terminal Server mode. Click Next 5. Select the appropriate security setting. Click Next 6. After the necessary files are copied, click Finish. 7. When the System Settings Change page is displayed. Click Yes to reboot the computer. 8. Terminal Services Configuration, Terminal Services Manager, and Terminal Server Licensing are added to the Administrative Tools menu. How to install IIS 6.0 using the Configure Your Server Wizard 1. 2. 3. 4. Click Start, click Administrative Tools, and then click Manage Your Server. In the Manage Your Server main screen, click Add or remove a role. The Configure Your Server Wizard starts. The Preliminary Steps screen is a warning screen that prompts you to verify that the requirements for the installation have been met. Click Next. 5. The network connections configured on the machine are tested and verified before the Wizard displays the following screen. 6. On the Configuration Options screen, choose one of the following options: o Typical configuration for a first server: You would choose this option to install the server as a domain controller, and to install the Active Directory directory service, DNS service, and DHCP service. o Custom Configuration, This option should be selected to install IIS 6 on the server. Click Next. 7. On the Server Role screen, choose Application Server (IIS, ASP.NET) as the role which you want install on the server. From this screen, you can also select to install Terminal, Print, DNS, and DHCP services. Selecting the Application Server (IIS, ASP.NET) option, installs IIS, ASP.NET and additional components so that the server can host websites and FTP sites. Click Next. 8. On the Application Server Options screen, you can select that these optional components be installed: o FrontPage Server Extensions, for users to develop Web content and publish Web content on the IIS machine via Microsoft FrontPage or Microsoft Visual Studio. o Microsoft Data Engine, for hosting SQL databases on the IIS machine o Enable ASP.NET: This option is enabled by default. ASP.NET is the scripting framework utilized for running IIS applications. Click Next. 9. The Summary of Selections screen displays a summary of the components which you selected for installation. Verify that the correct items are listed on this screen. The Enable COM+ for remote transactions option is automatically added. Click Next. 10. The installation process now commences. You would either have to insert the Windows Server 2003 CD, or indicate the location of the installation files. The Application Selections screen is displayed, the Configuration Components window appears, and the necessary files are copied. DNS Server Roles DNS Server and DNS Server Roles Overview Before DNS , HOSTS files were used to resolve host names to IP addresses. The HOSTS files were manually maintained by administrators. The HOSTS file was located on a centrally administered server on the Internet. Because of the shortcomings of the HOSTS files, DNS was designed and introduced. From the days of Windows NT Server 4.0, DNS has been included with the operating system. DNS is a hierarchically distributed and scalable database. DNS provides name registration, name resolution and service location for Windows 2000 and Windows Server 2003 clients. A DNS zone is the contiguous portion of the DNS domain name space over which a DNS server has authority, or is authoritative. A zone is a portion of a namespace – it is not a domain. A domain is a branch of the DNS namespace. A DNS zone can contain one or more contiguous domains. A DNS server can be authoritative for multiple DNS zones. A DNS server is a computer running the DNS Server service, or BIND; that provides domain name services. The DNS server manages the DNS database that is located on it. The DNS server program, whether it is the DNS Server service or BIND; manages and maintains the DNS database located on the DNS server. The information in the DNS database of a DNS server pertains to a portion of the DNS domain tree structure or namespace. This information is used to provide responses to client requests for name resolution. When a DNS server is queried for name resolution, it can respond to the request directly by providing the requested information, provide a pointer (referral) to another DNS server that can assist in resolving the query, or respond that the information is unavailable or that is does not exist. A DNS server is authoritative for the contiguous portion of the DNS namespace over which it resides. You can configure different server roles for your DNS servers. The server role that you configure for a name server affects the following operations of the server: The way in which the DNS server stores DNS data The way in which the DNS server maintains data Whether the DNS data in the database file can be directly edited. In DNS, a standard primary DNS server is the authoritative DNS server for a DNS zone. There are a number of zones used in Windows Server 2003 DNS: Primary zone: This is only zone type that can be directly updated or edited because the data in the zone is the original source of the data for all domains in the zone. Updates made to the primary zone are made by the DNS server that is authoritative for the specific primary zone. Secondary zone: This is a read-only copy of the zone that was copied from the master server during zone transfer Active Directory-integrated zone: This is an authoritative primary zone that stores its data in Active Directory. Active Directory-integrated zones can be regarded as enhanced standard primary zones. Stub zone: Stub zones only contain those resource records necessary to identify the authoritative DNS servers for the master zone Standard secondary DNS servers are usually implemented to provide a number of features for the DNS environment, including: Provide redundancy: It is recommended to install one primary DNS server, and one secondary DNS server for each DNS zone (minimum requirement). Install the DNS servers on different subnets so that if one DNS server fails, the other DNS server can continue to resolve queries. Distribution of DNS processing load: Implementing secondary DNS servers assist in reducing the load on the primary DNS server. Provide fast access for clients in remote locations: Secondary DNS servers can also assist in preventing clients from transversing slow links for name resolution requests. In addition to two server roles just mentioned, you can als configure the DNS server as a DNS forwarder, or as a caching-only DNS server. The remainder of this Article focuses on the different DNS server roles that you can configure for your DNS servers. Understanding Standard Primary DNS Servers A standard primary DNS server is a name server that obtains zone data from the local DNS database. This makes the primary DNS server authoritative for the zone data that it contains. When a change needs to be made to the resource records of the zone, it has to be done on the primary DNS server so that is can be included in the local zone database. A DNS primary server is created when a new primary zone is added. The primary server that is created becomes the mechanism for updating the specific primary zone. When a query is sent to the standard primary DNS server for name resolution, the following events take place: 1. The request for name resolution is sent to the primary DNS server. 2. The primary DNS server compares the requested name to the information it contains in its local zone database. 3. If the primary DNS server locates a match for the queried name, the requested information is returned to the client. 4. If the DNS server cannot find a matching record in its local zone database file, the DNS server then attempts a number of name resolution methods to resolve the request on behalf of the client. 5. If all attempts for name resolution in unsuccessful, the DNS server returns an error message to the client. Understanding Standard Secondary DNS Servers This DNS server type obtains a read-only copy of zone information through DNS zone transfers. A secondary DNS server cannot make any changes to the information contained in its read-only zone copy. A secondary DNS server can however resolve queries for name resolution. Secondary DNS servers are usually implemented to provide fault tolerance, provide fast access for clients in remote locations, and to distribute the DNS server processing load evenly. If a secondary DNS server is implemented, that DNS server can continue to handle queries when the primary DNS becomes unavailable. Secondary DNS servers also assist in reducing the processing load of the primary DNS server. It is recommended to install at least one primary DNS server, and one secondary DNS server for each DNS zone. A secondary DNS server obtains its data from the primary DNS server's zone database, as a copy of that database. During zone transfer, the primary DNS server's zone database is replicated to the secondary DNS server. A secondary DNS server cannot make changes to its zone information. All changes have to be made on the primary zone, and then have to be replicated to the secondary DNS server through DNS zone transfer. DNS Notify is a mechanism that enables a primary DNS server to inform secondary DNS servers when its database has been updated. The mechanism informs the secondary DNS servers when they need to initiate a zone transfer so that the updates of the primary DNS server can be replicated to them. When a secondary DNS server receives the notification from the primary DNS server, it can start an incremental zone transfer or a full zone transfer to pull zone changes from the primary DNS server. Understanding Caching-Only DNS Servers The main characteristics of caching-only DNS servers are: Caching-only DNS servers do not host zones. They are not authoritative for any DNS domain. The information stored by caching-only DNS servers is the name resolution data that it has collected through name resolution queries. A caching-only DNS server just performs queries and then stores the results of these queries. All information stored on the caching-only DNS server is therefore only that data which has been cached while the server performed queries. Caching-only DNS servers only cache information when the queries have been resolved. when a caching-only DNS servers starts or the first time, it has no cached information. The caching-only DNS server collects information as it sends and resolves queries. One of the main advantages of implementing caching-only DNS servers is that they are excluded from the zone transfer process, and therefore do not generate network traffic from zone transfers. Understanding Master DNS Servers The servers from which secondary DNS servers obtain zone information in the DNS hierarchy are called master servers. When a secondary DNS server is configured, you have to specify the master server from whom it will obtain zone information. Zone transfer enables a secondary DNS server to obtain zone information from its configured primary DNS server, and enables these servers to continue handling queries if the primary DNS server fails. In this case, the primary DNS server is the master server of the secondary DNS server. A secondary DNS server can also transfer its zone data to other secondary DNS servers, who are beneath it in the DNS hierarchy. In this case, the secondary DNS server is regarded as the master server to the other subordinate secondary DNS servers. A secondary DNS server initiates the zone transfer process from its particular master server when it is brought online. Understanding Dynamic DNS Servers Windows 2000, Windows XP and Windows Server 2003 computers can dynamically update the resource records of a DNS server when a client's IP addressing information is added, or renewed via Dynamic Host Configuration Protocol (DHCP). Both DHCP and Dynamic DNS (DDNS) updates make this possible. When dynamic DNS updates are enabled, a client sends a message to the DNS server when changes are made to its IP addressing data. This indicates to the DNS server that the A type resource record of the client needs to be updated. How to implement a caching-only DNS server 1. Open Control Panel 2. Double-click Add/Remove Programs., and then click Add/Remove Windows Components. 3. The Windows Components Wizard starts. 4. Click Networking Services, and then click Details. 5. In the Networking Services dialog box, select the checkbox for Domain Name System (DNS) in the list. 6. Click OK. Click Next. 7. Click Finish. 8. Do not add or configure any zones for the DNS server. The DNS Server service functions as a caching-only DNS server by default. This basically means no configuration is necessary to set up a caching-only DNS server. 9. You should verify that the server root hints are configured correctly. How to add a new zone to a DNS server 1. Click Start, Administrative Tools, and then click DNS to open the DNS console. 2. In the console tree, find and select the DNS server that you want to create a new DNS zone. 3. From the Action menu, click the New Zone option. 4. On the initial page of the New Zone Wizard, click Next. 5. Select the zone type that you want to create. The options are: o Primary, to create a new standard primary zone. o Secondary, to create a copy of the primary zone. o Stub, to create a copy of zone but for only the NS record, SOA record, and the glue A record. 6. Select the default selected option – Primary zone. 7. To integrate the new zone with Active Directory, and if the DNS server is a domain controller; then you can select the Store the zone in Active Directory (available only if DNS server is a domain controller) checkbox. 8. Click Next. 9. On the Active Directory Zone Replication Scope page, accept the default setting for DNS replication: To all domain controllers in the Active Directory domain. Click Next. 10. Select the Forward lookup zone option on the following page which is displayed by the New Zone Wizard, and then click Next. 11. Enter a zone name for the new zone. Click Next. The options that you can select on the following page with regar to dynamic updates are: o Allow only secure dynamic updates (recommended for Active Directory) option: This option is only available if you are using Active Directoryintegrated zones. o Allow both non-secure and secure dynamic updates option: Select this option with caution! o Do not allow dynamic updates option: You have to manually update zone information and resource records. 12. Choose the best option for your circumstance, and then click Next. 13. Click Finish to add the new zone to your DNS server. How to enable dynamic updating on your DNS servers Active Directory- integrated zones are set up to only allow secure dynamic updates. 1. Click Start, Administrative Tools, and then click DNS to open the DNS console. 2. In the console tree, expand the DNS server node that contains the authoritative zone that you want to work with. 3. Expand the Forward Lookup Zones folder. 4. Locate the specific zone that you want to configure. 5. Right-click the zone, and then select Properties on the shortcut menu. 6. When the Zone's Properties dialog box opens, leave the General tab displayed. 7. The options available in the Dynamic updates: list box are: o None o Non-secure and secure o Secure only 8. Select the Secure only option, and then click OK. How to disable dynamic updates for a host computer or interface You can also disable dynamic updates for a host computer, for a specific interface on that computer, or for multiple interfaces on the computer. 1. Open the Registry Editor tool. 2. In the left pane, expand the HKEY_LOCAL_MACHINE key, expand System, expand CurrentControlSet, and then expand Services. 3. Locate Tcpip, and then expand this node as well. 4. Find the Parameters node. 5. To disable dynamic updates for the host computer, click the Parameters node. In the details pane, double-click the DisableDynamicUpdate entry. Change the value data of DisableDynamicUpdate to 1 to disable dynamic updates. Click OK. 6. To disable dynamic updates for a single interface, expand the Parameters node, and then expand the Interface node. Select the interface, and then double-click the DisableDynamicUpdate entry in the details pane. Change the value data of DisableDynamicUpdate to 1 to disable dynamic updates. Click OK. How to test a query on a DNS server 1. Click Start, Administrative Tools, and then click DNS to open the DNS console. 2. In the console tree, right-click the DNS server that you want to test and then select Properties on the shortcut menu. 3. When the DNS Server's Properties dialog box opens, click the Monitoring tab. 4. You can choose to perform a simple query test, a recursive query test, or you can specify that the DNS server automatically performs testing at an interval that you set. 5. In the Select A Test Type area of the Monitoring tab, select the A Simple Query Against This DNS Server checkbox. 6. Click the Test Now button. 7. The Test Results area of the tab displays the results of the test. 8. Click OK. Related Articles on DNS What is DNS? How do I flush DNS? How do I find my DNS servers? What are public DNS servers? How do I perform a DNS lookup? What is reverse DNS? What is a dynamic DNS? What are DNS root servers? Understanding DNS