Exam 2, fall 2011
advertisement

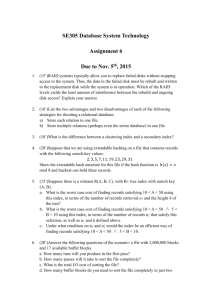
Last Name:____________________, First Initial:____ COP 4600 Operating Systems Exam 2 9 November 2011 Instructions 1. Read all instructions. Failure to follow instructions will result in loss of points. 2. This is a closed-book examination. 3. You are permitted one 8.5 by 11 inch sheet of notes (both sides OK) that you have prepared. 4. You are permitted 50 minutes to complete this examination. 5. Do not start the exam until the proctor has told you to start. 6. Answer three (3) questions, and no more. 7. Answer at least one even-numbered question and at least one odd-numbered question. 8. Leave sufficient room in the upper lefthand corner for the staple and staple your answer sheets in the room you have left. 9. Put the question number in the top center of each answer page and label each part of the question answer. 10. Include your last name and page number in the upper right hand corner of each answer page. 11. Show your work. 12. Start the answer to each question on a new page (i.e., do not put the answer to more than one question on the same page). 13. Use exactly one page of paper (both sides is OK, or two pages front side only) to hold the answer to each question, and please write legibly. 14. Assemble your answers in numerical order of the questions when you submit them. 15. Print your family name and first initial in the upper right hand corner of this page, and complete the honor statement affirmation below. Read and sign the following statement. This page MUST be attached to your examination answers and MUST be completed to obtain credit for this examination. On my honor, I have neither given nor received unauthorized aid on this examination. Signed ________________________________________ Printed Name: __________________________________ UFID: ____________-_____________ Answer 3 questions, at least one odd numbered and at least one even numbered. 1. Files and Directories a. How is opening a directory different from opening a file? Explain. b. Compare handling of multiple devices or partitions in Windows versus Unix. c. How do symbolic links differ from hard links in Unix? d. How does Unix deal with the possibility that there may be a cycle in the file system because of multiple links to the same directory? 2. Suppose that the directory containing a given file is in memory already, along with the FAT or the i-node table, but none of the file is in memory. Now suppose that a program opens the file and requests to read byte number 66,000. Assume that file blocks are 1 KB in size. a. How many disk accesses are needed to open the file and read in the desired byte if sequential file organization is used? Explain. b. Repeat (a) for a system using a FAT. c. Repeat (a) for a system using Unix-style i-nodes with 10 direct pointers. d. What advantage does the i-node approach have when the number of file blocks is very large? Justify your answer. 3. I/O a. How are major and minor device numbers used? Explain. b. What are two differences between block devices and character devices? c. What advantages does memory-mapped I/O have over I/O ports? Explain. d. Compare RAID level 1 fault tolerance with RAID level 4. e. What is the main advantage of RAID level 5 over RAID level 4? 4. Suppose that a hard disk’s heads are at cylinder 50 and requests have been queued for the following cylinders: 1, 57, 46, 104, 18, 60, 93, 32, 112. a. Give the order and the total number cylinders of seek done for FCFS. b. Repeat (a) for SSTF. c. Repeat (a) for Elevator (assume the initial direction is decreasing). d. Why is the Elevator algorithm often modified to serve requests in only one direction? e. Give two circumstances under which it does not make sense for the disk driver to perform scheduling to optimize seek time. Explain. 5. Deadlocks a. What are the four necessary conditions for deadlock? Why is each necessary? b. .Compare the basic ways of dealing with deadlock (aside from ignoring the problem). c. Describe how to determine an upper bound on resource needs based on static code analysis. d. Give an example of a situation in which allowing deadlock to happen is not acceptable. 6. Consider a system in which the exists vector is <4,4,5,4>, the max needs vectors for processes A through E are <1,2,1,2>, <0,2,3,1>, <0,1,1,2>, <3,1,1,1>, and <1,2,0,2> resp. a. If the alloc vectors for A through E are <1,0,0,1>, <0,1,1,0>, <0,0,1,1>, <1,0,1,0>, and <1,1,0,0>, respectively, is the system safe? If so, prove it, if not, show why not. b. Suppose two more items of resource type 1 are added, so exists = <6,4,5,4>. If process D requests 1 of resource 2, is it safe to allocate this? Prove or disprove. c. How is the Bankers Algorithm related to the deadlock detection algorithm?