Secure DNS for DMZ Clients
advertisement
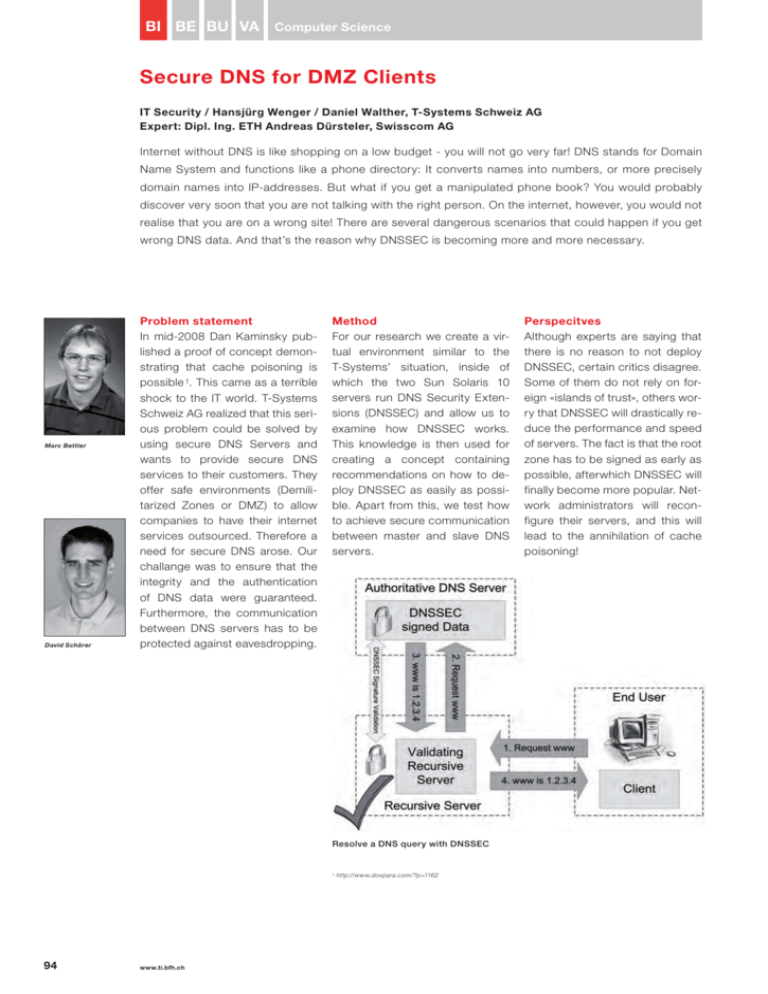
BI BE BU VA Computer Science Secure DNS for DMZ Clients IT Security / Hansjürg Wenger / Daniel Walther, T-Systems Schweiz AG Expert: Dipl. Ing. ETH Andreas Dürsteler, Swisscom AG Internet without DNS is like shopping on a low budget - you will not go very far! DNS stands for Domain Name System and functions like a phone directory: It converts names into numbers, or more precisely domain names into IP-addresses. But what if you get a manipulated phone book? You would probably discover very soon that you are not talking with the right person. On the internet, however, you would not realise that you are on a wrong site! There are several dangerous scenarios that could happen if you get wrong DNS data. And that’s the reason why DNSSEC is becoming more and more necessary. Marc Bettler David Schärer Problem statement In mid-2008 Dan Kaminsky published a proof of concept demonstrating that cache poisoning is possible 1. This came as a terrible shock to the IT world. T-Systems Schweiz AG realized that this serious problem could be solved by using secure DNS Servers and wants to provide secure DNS services to their customers. They offer safe environments (Demilitarized Zones or DMZ) to allow companies to have their internet services outsourced. Therefore a need for secure DNS arose. Our challange was to ensure that the integrity and the authentication of DNS data were guaranteed. Furthermore, the communication between DNS servers has to be protected against eavesdropping. Method For our research we create a virtual environment similar to the T-Systems’ situation, inside of which the two Sun Solaris 10 servers run DNS Security Extensions (DNSSEC) and allow us to examine how DNSSEC works. This knowledge is then used for creating a concept containing recommendations on how to deploy DNSSEC as easily as possible. Apart from this, we test how to achieve secure communication between master and slave DNS servers. Resolve a DNS query with DNSSEC 1 94 www.ti.bfh.ch http://www.doxpara.com/?p=1162 Perspecitves Although experts are saying that there is no reason to not deploy DNSSEC, certain critics disagree. Some of them do not rely on foreign «islands of trust», others worry that DNSSEC will drastically reduce the performance and speed of servers. The fact is that the root zone has to be signed as early as possible, afterwhich DNSSEC will finally become more popular. Network administrators will reconfigure their servers, and this will lead to the annihilation of cache poisoning!