Chapter08
advertisement
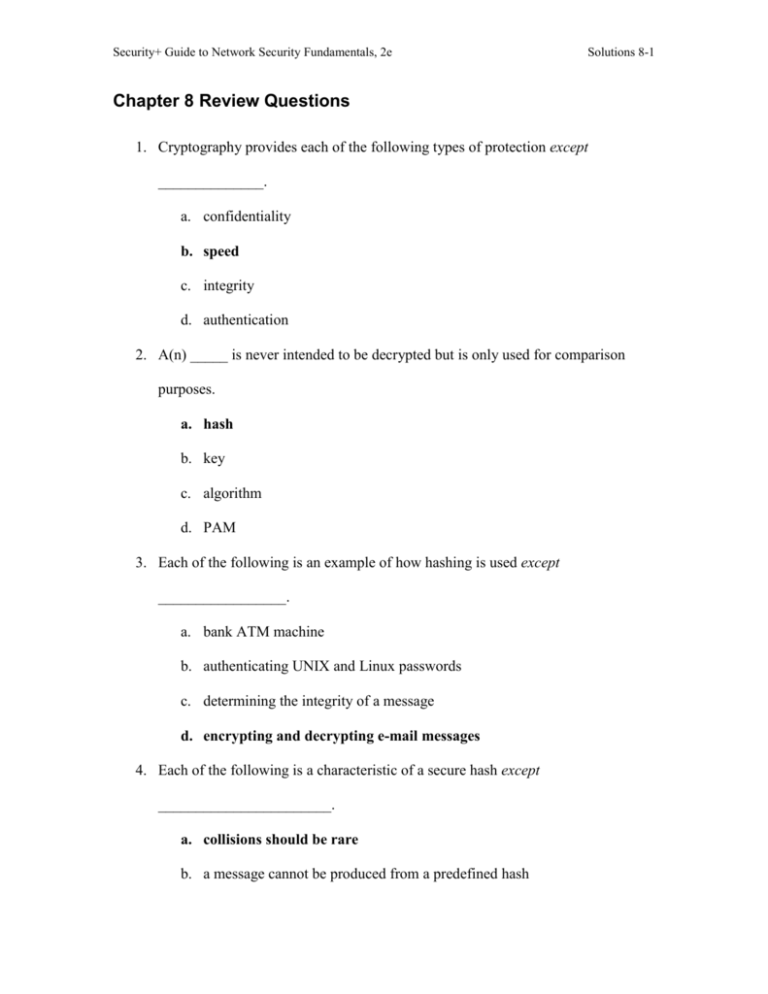
Security+ Guide to Network Security Fundamentals, 2e Solutions 8-1 Chapter 8 Review Questions 1. Cryptography provides each of the following types of protection except ______________. a. confidentiality b. speed c. integrity d. authentication 2. A(n) _____ is never intended to be decrypted but is only used for comparison purposes. a. hash b. key c. algorithm d. PAM 3. Each of the following is an example of how hashing is used except _________________. a. bank ATM machine b. authenticating UNIX and Linux passwords c. determining the integrity of a message d. encrypting and decrypting e-mail messages 4. Each of the following is a characteristic of a secure hash except _______________________. a. collisions should be rare b. a message cannot be produced from a predefined hash Security+ Guide to Network Security Fundamentals, 2e Solutions 8-2 c. the results of a hash function should not be reversed d. the hash should always be the same fixed size 5. The data added to a section of text when using the message-digest (MD) algorithm is called _________________. a. filler b. extender c. padding d. byte code 6. A cipher is an encryption or decryption algorithm tool used to create encrypted or decrypted text. True or false? 7. Most security experts recommend that the family of DES hashes be replaced with a more secure hash algorithm. True or false? 8. The Secure Hash Algorithm (SHA) creates a more secure hash 160 bits long instead of 128 bits as with other algorithms. True or false? 9. Symmetric encryption algorithms use a single key to encrypt and decrypt. True or false? 10. A stream cipher takes one character and replaces it with one character. True or false? 11. Data that has been encrypted by an encryption algorithm (a cipher) is called _____. ciphertext. 12. A(n) _____ cipher maps a single plaintext character to multiple ciphertext characters. homoalphabetic substitution 13. A(n) _____ cipher rearranges the letters without changing them. transposition Security+ Guide to Network Security Fundamentals, 2e Solutions 8-3 14. A(n) _____ cipher manipulates an entire block of plaintext at one time. block 15. The _____was specifically designed to replace the weaker Data Encryption Standard (DES). Triple Data Encryption Standard (3DES) 16. Explain the problems with key management and how it affects symmetric cryptography. The primary weakness of symmetric encryption algorithms is keeping the single key secure. Known as key management, it poses a number of significant challenges. If a user wants to send an encrypted message to another using symmetric encryption, he must be sure that she has the key to decrypt the message. How should the first user get the key to the second user? He would not want to send it electronically through the Internet, because that would make it vulnerable to eavesdroppers. Nor can he encrypt the key and send it, because the recipient would need some way to decrypt the key. And if he can even get the get securely to the user, how can be he certain that an attacker has not seen the key on that person’s computer? Key management is a significant impediment to using symmetric encryption. 17. Describe how elliptic curve cryptosystems work. Elliptic curve cryptography was first proposed in the mid-1980s. Instead of using prime numbers as with RSA, elliptic curve cryptography uses elliptic curves. An elliptic curve is a function that is drawn on an X-Y axis as a gently curved line. By adding two points on the curve together you can arrive at a third point on the curve. The public aspect of an elliptic curve cryptosystem is that users share an elliptic curve and one point on the curve. Security+ Guide to Network Security Fundamentals, 2e Solutions 8-4 One user then chooses a secret random number and computes a public key based on a point on the curve. The other user does the same. They can now exchange messages because the shared public keys can generate a private key on elliptic curve. 18. What is a digital signature? Why is it used? The asymmetric cryptographic system can itself provide for multiple types of security functions, including authentication, integrity and non-repudiation. This is done through using a digital certificate and helps to prove that the person sending the message with a public key is actually who they claim to be, that the message was not altered, and that it cannot be denied that the message was sent. A digital signature is a shorter version of the message itself that is created by the contents of the message and the sender’s private key and is then added attached to the end of the message. Because the contents of the message are used to create the digital signature, this signature will be different for every message sent. When using a digital certificate the sender uses her own private key to create a digital signature before encrypting the entire message with the receiver’s public key. The sender begins by creating the document that is to be transmitted. Then using special software a summary of that message is created. Finally, the sender’s public key is used to encrypt the summary and this is attached to the end of the message. 19. What is the Microsoft Encrypting File System (EFS) and what are some of its features? Security+ Guide to Network Security Fundamentals, 2e Solutions 8-5 Microsoft’s Encrypting File System (EFS) is an encryption scheme for Windows 2000, Windows XP Professional, and Windows 2003 Server operating systems that use the NTFS file system. Because EFS is tightly integrated with the NTFS file system, file encryption and decryption are transparent. When users open a file, it is decrypted by EFS as data is read from disk and when they save the file, EFS encrypts the data as it is written to disk. Encrypting a file is performed by setting a file attribute and the encryption attribute can also be set for a file folder. Any file created in or added to the folder is automatically encrypted. 20. What is a pluggable authentication module (PAM)? When UNIX was originally developed the task of authenticating a user was accomplished by the user entering a password and the system then checked if the entered password corresponded to the encrypted official password that is stored in the user database /etc/passwd. Since that time a number of new ways of authenticating users have become popular, such as using new hardware devices like smart cards. Yet each time a new authentication scheme was developed it requires all the necessary programs, such as login and ftp, to be rewritten to support it. The solution was to use pluggable authentication modules (PAMs) instead. PAM provides a way to develop programs that are independent of the authentication scheme. PAM rests between the operating system and the program that needs authentication. The authentication modules are attached to the programs when needed.