SSL Supplement - YSU Computer Science & Information Systems
advertisement
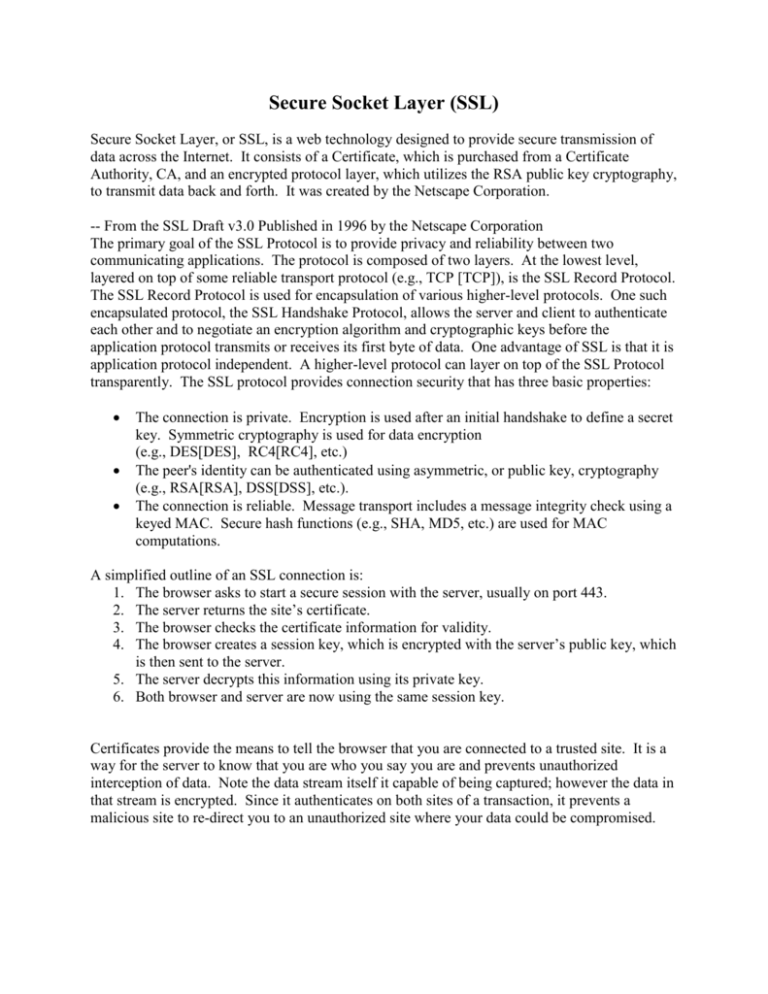
Secure Socket Layer (SSL) Secure Socket Layer, or SSL, is a web technology designed to provide secure transmission of data across the Internet. It consists of a Certificate, which is purchased from a Certificate Authority, CA, and an encrypted protocol layer, which utilizes the RSA public key cryptography, to transmit data back and forth. It was created by the Netscape Corporation. -- From the SSL Draft v3.0 Published in 1996 by the Netscape Corporation The primary goal of the SSL Protocol is to provide privacy and reliability between two communicating applications. The protocol is composed of two layers. At the lowest level, layered on top of some reliable transport protocol (e.g., TCP [TCP]), is the SSL Record Protocol. The SSL Record Protocol is used for encapsulation of various higher-level protocols. One such encapsulated protocol, the SSL Handshake Protocol, allows the server and client to authenticate each other and to negotiate an encryption algorithm and cryptographic keys before the application protocol transmits or receives its first byte of data. One advantage of SSL is that it is application protocol independent. A higher-level protocol can layer on top of the SSL Protocol transparently. The SSL protocol provides connection security that has three basic properties: The connection is private. Encryption is used after an initial handshake to define a secret key. Symmetric cryptography is used for data encryption (e.g., DES[DES], RC4[RC4], etc.) The peer's identity can be authenticated using asymmetric, or public key, cryptography (e.g., RSA[RSA], DSS[DSS], etc.). The connection is reliable. Message transport includes a message integrity check using a keyed MAC. Secure hash functions (e.g., SHA, MD5, etc.) are used for MAC computations. A simplified outline of an SSL connection is: 1. The browser asks to start a secure session with the server, usually on port 443. 2. The server returns the site’s certificate. 3. The browser checks the certificate information for validity. 4. The browser creates a session key, which is encrypted with the server’s public key, which is then sent to the server. 5. The server decrypts this information using its private key. 6. Both browser and server are now using the same session key. Certificates provide the means to tell the browser that you are connected to a trusted site. It is a way for the server to know that you are who you say you are and prevents unauthorized interception of data. Note the data stream itself it capable of being captured; however the data in that stream is encrypted. Since it authenticates on both sites of a transaction, it prevents a malicious site to re-direct you to an unauthorized site where your data could be compromised. There are two levels of encryption: 40-bit and 128-bit. With 40-bit encryption, there are billions of possible keys to decipher the coded information, and only one of them works. Someone intercepting the information would have to find the right key - a nearly impossible task. With 128-bit encryption, there are 300 billion trillion times as many keys as with 40-bit encryption. It is virtually impossible for an unauthorized party to find the right key, even if they are equipped with the best computers. Note that security features do not prevent you from viewing nonencrypted web sites or place any limitations on your use of the World Wide Web, email, or newsgroups. Secure Socket Layers provide data security, not site security. A web site that hosts an SSLenabled website could be vulnerable to Denial of Service, or other security breaches, but can still provide this layer of protection. There are many things that administrators don’t do, or do improperly that will compromise data that can’t be helped by SSL. The first is e-mail. After a user fills out a form that is behind a SSL, a system might decode the data once on the server, at this point it is no longer safe, then the script emails the information to the form’s owner. The data is now sent as insecure text. The second type of mistake is regarding data storage. The owner of a site uses a log-to-file method to store all information in case e-mail is lost or for audit purposes. With this, data is stored as a text file and is readable by administrators in the company, or if the data is not secured on a file level, it will be readable by everyone that has access to that computer. Another is a backup. Where are the backups stored, who has physical access to them.