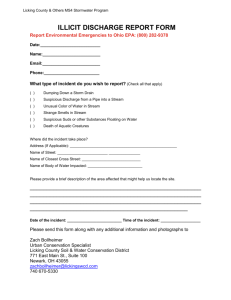
Site Specific Risk Assessment
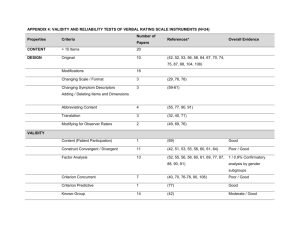
advertisement

Site Specific Threat Assessment The Site Specific Threat Assessment contains a Threat Assessment Matrix (TAM), a document that is used to assess and identify potential risks for a specific area or practice. The assessment is a twopart process, a TAM as well as a Vulnerability Assessment (VA). A TAM is mostly subjective but allows an individual to identify risks using a simple ranking system (Low, Moderate, High) which determines a total risk value for each individual risk. Description of agents: † Name of Agent or Toxin, described as † Biosafety Level agents † airborne/ (non-airborne). † Name of PI is listed as the “Principal Investigator.” and inventory control. † Name of PI maintains specimen accountability Agent-Specific Risk Assessment: Based on the agents in the University’s inventory and their intended use, the risk category associated with these agents is (Check one): Low risk includes agents that are handled in a diagnostic, nonpropagative manner (e.g., single specimen, no culture). Moderate risk includes agents that are handled in a diagnostic, propagative manner. This level includes only the amounts necessary for experiments at hand (e.g., specimen cultured for diagnostic purposes or produced only in amounts required for the research or experiments being conducted). High risk includes agents that are handled in large or highly pure quantities such as liters or grams. It would also include those agents and toxins used in restricted experiments or experiments that may increase virulence, and also includes high-risk use (e.g., centrifugation). Highest risk is a placeholder for smallpox only. Note: The agent-specific risk categories are based on the concept that all agents and toxins do not pose the same risk or require the same level of protection. 1|Page Threat Assessment: The following table lists the threats, probability of occurrence and consequences if a threat occurs. Probability and consequences are rated as low, moderate, or high. It should be noted that probability and consequences may vary due to the type of threat. Threat Man/Woman Insider with authorized access Outsider with limited access and system knowledge Anyone desiring to do harm (i.e., violent acts, anger, hatred, terrorist activity, civil disturbances, special interest groups, attack at gun point, etc.) Nature Hurricanes Severe thunderstorms Tornadoes Floods Earthquakes Incident Bomb threats Communications failure Electrical power failure Fire HAZMAT incident Biological and chemical agents Information technology hacking Probability Consequences Moderate Low Low High Moderate High Low Low Low Low Moderate High Moderate High Moderate High Low Low Low Low Moderate Low Low Low Moderate Moderate High Moderate Figure 1 As shown in the TAM in Figure 1.1, the above subjective factors (Figure1) have been reflected with their assigned values to yield “Risk Factors” which can be used to assign tasks and functions to the process. Any risks or threats with a value greater or equal to 25 will trigger the need to complete a Vulnerability Assessment (Figure 2) which will identify specific actions needed to reduce vulnerability level. Similarly, any value of 50 or greater will trigger the need for a Security Access Plan and Incident Response Plan. Both of these plans will require additional training and must be implemented properly. Note: A template for Figures 1.1 and 2.1 are available from the link below. Please note that the referenced Microsoft Excel Spreadsheet contains two sheets respective to the figures 1.1 and 2.1. Please be mindful of the included formulas which are programmed to handle any required calculations automatically. http://www.cpp.edu/~ehs/biosafety/TAM.xlsx 2|Page Vulnerability Assessment: The probability and consequences of each identified threat that were rated as low, moderate or high, in the previous section, were reviewed. Any threat with a moderate probability and consequence or higher was consider significant and chosen for Vulnerability Assessment in this section. The significant/chosen threats had the following ratings: Moderate Probability and Moderate Consequence High Probability and Moderate Consequence Moderate Probability and High Consequence High Probability and High Consequence These significant threats are listed in the following table as security weaknesses and/or deficiencies. The vulnerability and corrective measures for each of these security weaknesses and/or deficiencies were evaluated and documented in the table. The vulnerability level is rated as follows: Low level means the threats identified at the entity have little or no probability for harm Moderate level means the threats identified at the entity have some probability for harm High level means the threats identified at the entity are likely to cause harm Security Weakness/ Deficiencies (AKA Significant Threats) Vulnerabil ity Level Corrective Measures Considered High Man/Woman Insider with authorized access Develop and Implement a written Security Plan. Train personnel on the Security Plan. Require Security Risk Assessments of individuals before granting unescorted access. Maintain three lockable barriers for storage of select agents and/or toxins. Develop and implement an entry log for location. Require unauthorized personnel (Personnel without an approved security risk assessment) to be escorted by authorized personnel when entering rooms where select agents or toxins are present. Develop and implement inventory tracking and verification system. Nature Earthquakes Moderate Require secondary containment for storage of select agents and/or toxins Bracket storage cabinets to walls to prevent storage cabinets form falling over during an earthquake. Develop and implement a written Incident Response Plan. Train personnel on the Incident Response Plan. Develop and implement a written Incident Response Plan. Train personnel on the Incident Response Plan. Incident HAZMAT Incident Moderate Figure 2 Based on the above table of threats (Figure 2), vulnerability ratings and corrective measures, the overall vulnerability is low. 3|Page Graded Protection Assessment: An assessment of the area should be performed by a qualified individual such as a Police Officer and preferably someone who would be responding to the area during an actual emergency. Considerations: Based on the site-specific risk assessment, all the above corrective measures have and/or will be implemented. These measures will be documented in the Security Plan, Incident Response Plan and other plans, as necessary. Entity Security Conference: On † “Select a Date”, a security conference and survey of the Regulated Material and/or toxin storage and use area were conducted by: † PI Name, Title; † RO Name, California State Polytechnic University, Pomona, Environmental Health and Safety Department; † Inspector Name, California State Polytechnic University, Pomona, Police Department † Add any additional information or comments here: 4|Page General Observations: † Building #, Room # is located inside † Building # on the Cal Poly Pomona campus. Physical access to † Building #, Room # is possible only through the exterior lab, † Building #, Room #, which is normally kept secured through † means of access to this area (e.g. keycard, master). Access keys for † Building #, Room # are “off master,” and these keys are possessed by † PI Name and † RO Name. Authorized persons wishing to access † Building #, Room # are admitted † PI Name. The security for this lab consists of the following layers: 1 - Main access doors for † Building #, Room #, keyed to a general building master key; 2 - Internal lab door for † Building #, Room #, where agents are stored / used, keyed “off master;” 3 - Locked storage containers (refrigerators / freezers) inside † Building #, Room #; 4 – Locked internal storage containers inside each refrigerator. All agents are kept secured in these containers at all times, unless immediately being used. Access to † Building #, Room # is logged on a written sign-in sheet for all those entering the lab. This log sheet appears to be kept up to date, and contains emergency contact numbers for incidents or other occurrences relating to this room. There is also up-to-date emergency contact information posted on the entry door. Other area observations: † List any additional observations from the Inspector here. Recommendations for future security enhancements: † List all recommendations from the Inspector here. 5|Page A Threat B C Probability Consequence (Low [0], Moderate [5], High [10]) Describe any all threats. Insert additional rows as necessary. Man/Woman e.g. Low [0] Risk Factor (A)(B) e.g. High [10] Insider with Authorized Access Outsider with Limited Access or System Knowledge 5 0 10 5 50 0 Desire to do harm: violent acts, terrorist activity, civil disturbances, special interest groups, attack at gun point etc. 0 10 0 Nature e.g. Low [0] Hurricanes Severe Thunderstorms Tornadoes Floods Earthquakes e.g. High [10] 0 0 0 0 5 Incident Bomb Threats Communications Failure Electrical Power Failure Fire HAZMAT Incident Biological and Chemical Agents Information Technology Hacking e.g. Low [0] 10 5 10 5 10 0 0 0 0 50 e.g. High [10] 0 0 0 0 5 0 0 0 5 5 10 5 Criteria: Any items with a Risk Factor ≥25 must undergo a Vulnerability Assessment. Any items with a Risk Factor ≥50 require a Security Access Plan and an Incident Response Plan specific to that location. Figure 1.1 6|Page 0 0 0 0 50 0 Security Weakness Vulnerability Level Corrective Measures Considered Man/Woman Threat from Assessment (Add additional rows as necessary) Insider with Authorized Access Significant Develop and implement a written Security Plan Train personnel on security plan Maintain lockable barriers Develop entry log for restricted areas Nature Earthquakes Significant Require secondary containment for storage Bracket storage cabinets to the wall to prevent falls Develop an incident response plan Incident HAZMAT Situations Risk Factors Significant Vulnerability Level 25 Moderate 50 Significant 100 Severe Develop an incident response plan Train personnel on incident response plan Be familiar with emergency procedures Security Access Plan & Incident Response Plan Required Security Access Plan & Incident Response Plan Required Figure 2.1 7|Page Authorized Personnel Authorized personnel with access to Regulated Materials must carry a lab specific Identification card to identify themselves as Authorized Personnel. Due to the cumbersome procedures associated with this process, a viable alternative is available. All lab personnel shall be identified on a poster located in the lab and in the Security Access Plan. This identification must have their photo. † PI Name (Photo Below) † RO Name (Photo Below) † ARO Name (Photo Below) † Staff 1 (Photo Below) † Staff 2 (Photo Below) † Staff 3 (Photo Below) 8|Page Additional Information † Provide any additional information regarding Authorized Personnel here: 9|Page Certification of Annual Review of Security Plan Signature of Reviewer Date of Review 10 | P a g e