Review Questions
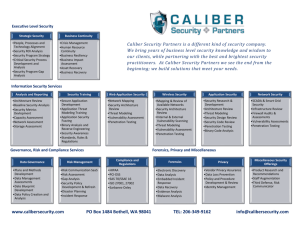
advertisement
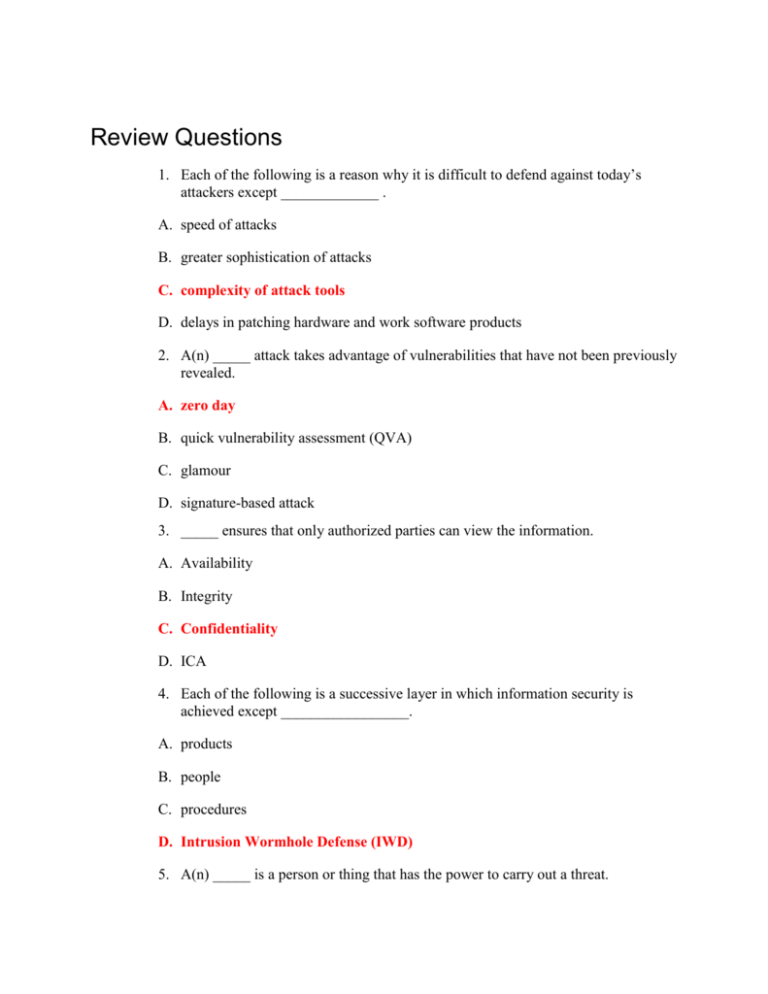
Review Questions 1. Each of the following is a reason why it is difficult to defend against today’s attackers except _____________ . A. speed of attacks B. greater sophistication of attacks C. complexity of attack tools D. delays in patching hardware and work software products 2. A(n) _____ attack takes advantage of vulnerabilities that have not been previously revealed. A. zero day B. quick vulnerability assessment (QVA) C. glamour D. signature-based attack 3. _____ ensures that only authorized parties can view the information. A. Availability B. Integrity C. Confidentiality D. ICA 4. Each of the following is a successive layer in which information security is achieved except _________________. A. products B. people C. procedures D. Intrusion Wormhole Defense (IWD) 5. A(n) _____ is a person or thing that has the power to carry out a threat. A. vulnerability B. threat agent C. exploit D. risk factor 6. Each of the following is a goal of information security except __________. A. Prevent data theft B. Decrease user productivity C. Avoid legal consequences D. Foil cyberterrorism 7. The _____ requires that enterprises must guard protected health information and implement policies and procedures to safeguard it. A. Health Insurance Portability and Accountability Act (HIPAA) B. Sarbanes-Oxley Act (Sarbox) C. Gramm-Leach-Bliley Act (GLBA) D. Hospital Protection and Insurance Association Agreement (HPIAA) 8. Utility companies, telecommunications, and financial services are considered prime targets of _____ because attackers can significantly disrupt business and personal activities by destroying a few targets. A. cyberterrorists B. kiddie scripters C. computer spies D. blue hat hackers (BHH) 9. After an attacker probed a computer or network for information she would next ________. A. modify security settings B. penetrate any defenses C. paralyze networks and devices D. circulate to other systems 10. An organization that purchased security products from different vendors in case an attacker circumvented the Brand A device, yet would have more difficulty trying to break through a Brand B device because they are different, is an example of ________. A. obscurity B. layering C. limiting D. diversity 11. _____ is a superset of information security and includes security issues that do not involve computers. A. Google reconnaissance B. Risk security (RS) C. Information assurance (IA) D. Asset restriction (AR) 12. _____ attacks come from multiple sources instead of a single source. A. Distributed B. Isolated C. Script resource malware (SRM) D. Form resource 13. _____ are a loose-knit network of attackers, identity thieves, and financial fraudsters. A. Cybercriminals B. Hackers C. Spies D. Script kiddies 14. Each of the following is a characteristic of cybercriminals except ________. A. low motivation B. less risk-averse C. better funded D. more tenacious 15. Each of the following is a characteristic of cybercrime except ________. A. targeted attacks against financial networks B. unauthorized access to information C. theft of personal information D. exclusive use of worms and viruses 16. An example of a(n) _____ is a software defect in an operating system that allows an unauthorized user to gain access to a computer without a password A. vulnerability B. threat C. threat agent D. asset exploit (AE) 17. _____ requires banks and financial institutions to alert customers of their policies and practices in disclosing customer information and to protect all electronic and paper containing personally identifiable financial information. A. California Savings and Loan Security Act (CS&LSA) B. USA Patriot Act C. Sarbanes-Oxley Act (Sarbox) D. Gramm-Leach-Bliley Act (GLBA) 18. The term _____ is commonly used in a generic sense to identify anyone who illegally breaks into a computer system. A. hacker B. cyberterrorist C. Internet Exploiter D. cyberrogue 19. An example of _____would be not revealing the type of computer, operating system, software, and network connection a computer uses. A. diversity B. limiting C. obscurity D. layering 20. The _____ is primarily responsible for assessment, management, and implementation of security. A. Chief Information Security Officer (CISO) B. security manager C. security administrator D. security technician