Wireless Hacking Made Easy - Ernest Staats Network Security
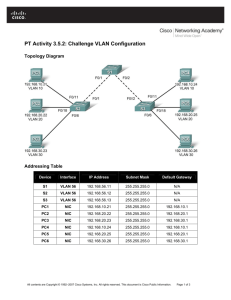
advertisement

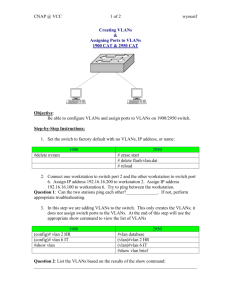
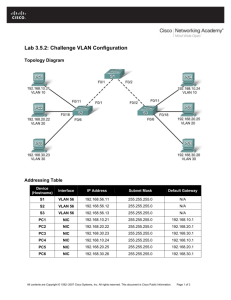
http://es-es.net/ MS Information Assurance, CISSP, CWNA, CEH, MCSE, Security+, I-Net+, Network+, Server+, CNA, A+ erstaats@es-es.net http://es-es.net In attending this session you agree that any software demonstrated comes absolutely with NO WARRANTY. Use entirely at your own risk. Ernest or Eric, & the other 3rd party vendors whose software is demonstrated as part of this session are not responsible for any subsequent loss or damage whatsoever! Legal advice– I am not a lawyer for legal advice please seek a trained lawyer in the field you have a question. ETHERNET ISSUES Network and System Access – – – – – Unauthorized Join Unauthorized Expansion of the Network VLAN Join VLAN Tagging Spoofing and Address Capture Traffic Integrity – – – – ARP Poisoning and Rogue DHCP Server Man in the Middle Session Hijacking Replay Availability of Service – Denial of Service – Switch Control Using Network as a Medium – – – – Traffic Confidentiality – Passive Eavesdropping – Active Eavesdropping RELATED ISSUES Network Scanning Break-Ins Topology Discovery Protocols Redundancy and Aggregation Protocols Other Security Related Issues – – – – – Configuration and Installation Issues Implementation Issues Issues with Legacy Technology Architectural Issues Freely available Software for Attacks and Exploits A switch learns the MAC address/port pairings and stores them in limited memory Easy to generate bogus frames and get the memory to owerflow If a MAC address is unknown the switch broadcasts it out of all its ports Makes eavesdropping possible Spanning Tree Protocol is used to define the logical topology for an Ethernet segment Any host can claim to be the STP root and direct large parts of traffic to go through itself Man in the Middle attack (MitM) STP can also be used for Denial of Service (DoS) DHCP poisoning A new host on LAN broadcasts a request for IP and router information Any host can pretend to be the DHCP server and tell that it is the router Enables a Man in the Middle attack ARP poisoning Any host on LAN can broadcast a gratuitous ARP message claiming to have any IP address (including the router) at its MAC address ARP poisoning can be used to hijack an ongoing session Frames can hop from one Virtual LAN to another with "double tagging" VLANs supposedly bring security VLAN management protocols enable all kinds of attacks Frame padding and MAC table timeouts leak information With persistance the attacker can passively wait for HTTP cookies All attacks can be (and are being) made to software Ettercap for MitM, http://ettercap.sourceforge.net/ Sniffers for eavesdropping: Wireshark, ngrep, tcpdump, snoop Packet crafting tools: packETH, Bit-Twist, Mausezahn, Hping, Nemesis, Scapy, Yersinia, THC Parasite, macof Packetsquare for capture, edit and replay Access Control and Node Authentication – – – – Physical Protection of the Network Segmentation and VLANs Access Control Lists Authentication based Access Control – IEEE 802.1X – Network Access Control Network Integrity Protection – Securing ARP – Port Security – Control and Management Plane Overload Protection (CoPP) – Control and Management Plane Logical Protection – STP BPDU and root guard – Deep Packet Inspection – Proper Configuration Traffic (Payload) Integrity and Confidentiality Protection – Traffic Encryption and Integrity Verification – IEEE 802.1AE MACsec – Replay Protection Intrusion Detection and Prevention Systems Hiding or Obfuscating Network Topology Future solutions – Automated Key Management Policies – Cryptographically generated addresses – Removing ARP broadcasts – OpenFlow or DHT/TRILL IEEE has no architectural solutions, except VLAN 802.1X adds authentication, does not protect from misuse Authenticated entities may misbehave 802.1AE MACsec adds confidentiality (encryption) Based on 802.1X authentication Not end to end, but host to switch 802.1X and MACsec require administration activities per node Software installation, identity management High cost, little flexibility Vendor solutions can make Ethernet fairly secure, but require configuration Configuring each switch with knowledge of topology Port Security, Root Guard, BPDU Guard... Effectively these are ACLs with fancy names to separate user and control (and management) planes Good administration practices Knowledge of vendor-specific quirks of the switches Ethernet architecture is flawed from security point of view It is a nice and simple LAN architecture But it is "fail open" by design ▪ If you don't know how to handle a frame, send it to everybody ▪ Trusting everybody is implicit Vendor solutions require active management Mainly to tell the switches the topology (trunk ports and leaf node ports) Potential new solutions Deduct topology information automatically (low management overhead) then use Intrusion Prevention Systems and ACLs to protect the network Get rid of ARP and broadcasts (with e.g. DHT-Trill) 1. SHARED, UNCONTROLLED MEDIA: Invisible & Airborne Threats are Hard To Control vs. Wired Network 2. SELF-DEPLOYING & TRANSIENT NETWORKS Simplicity of Self Discovery Create Security Challenges Mobile Nature of Wireless LAN Devices and Users Require In- depth Forensics capability to Address Security Breaches 3. USER INDIFFERENCE Invisible Connectivity & True Distributed Nature Gives a Faulty Sense of Security 4. EASIER TO ATTACK Lax WLAN Security is the Lowest Hanging Fruit for Hackers Dozens of Tools Readily Available to Exploit these Holes From a System management terminal, someone could: Add non-dedicated machines for administration Install new programs and new vulnerabilities Forget to update the management application when updating other LMR machines Remote into the management application from outside the LMR network Connect LMR to existing management functions Protect, Detect, Respond Physically secure the management terminals Ensure system managers are authenticated Ensure appropriate privileges for users Update patches and manage administrator terminals With the Radios, someone could: Use a radio purchased from eBay Steal an existing radio from storage Send invalid data packets from the radio and terminals Infect the radios with viruses What else could be done? Protect, Detect, Respond Ensure subscribers are authorized and authenticated Ensure that alerts are generated when unauthorized radios attempt to access the system Implement firewalls and Router Access Control Lists to ensure only valid packets are passed Close unnecessary ports and protocols Network Edge blurred – another access into your mission critical network Rogues, hackers, mis-configured devices Organized crime – hacking for profit Interfacing with other systems Access control Combination of public and private network connectivity Multiple agency access OPEN AP‟S Let‟s all play nice COOKIE SESSION IDS SSL login, and then? EDIT COOKIES Sniff and edit FERRET AND HAMSTER http://erratasec.blogspot.com/sidejacking.zip DHCP Attack Exploit attacks a client and loads creates a Admin User on device DHCP Broadcast Attack (MS06-036) http://www.milw0rm.com/sploits/07212006MS06_036_DHCP_Client.tar.gz DNS ATTACK/MANIPULATION Can offer anything to you and you believe it Sites: Banking, Hotel, Airlines, Work (Exchange, Oracle, SQL) TORNADO Web-based attack tool which exploits up to 14 browser vulnerabilities and installs malware on the user's system YOUR NOTEBOOK IS: 1. Not location-aware 2. Wants to always connect to something Office Home Hotspot Virtual Local Area Networks A logical grouping of devices or users Users can be grouped by function, department, application, regardless of physical segment location VLAN configuration is done at the switch (Layer 2) VLAN's are not security! They are obscurity, they are great for segmentation and traffic management Static VLAN Assignment - Port based membership: Membership is determined by the port on the switch on not by the host. Dynamic VLAN Assignment - Membership is determined by the host’s MAC address. Administrator has to create a database with MAC addresses and VLAN mappings • VLANS cannot communicate with each other even when they exist on the same switch • For VLANS to communicate they must pass through a router • Each VLAN is required to have at least one gateway to route packets in and out of the network Trunking allows us to cascade multiple switches using the trunk ports to interconnect them Trunk ports act as a dedicated path for each VLAN between switches The trunk port is a member of all configured VLANs These attacks are designed to allow the attacker to bypass the Layer 3 device The attack takes advantage of incorrectly configured trunk ports on network switches Basic VLAN Hopping Attack 1. Attacker fools switch into thinking that he is a switch that needs trunking 2. The attack needs a trunking favorable setting such as Auto to succeed 3. The attacker is now a member of all trunked VLANs on the switch and he send and receive data on those VLANs Double Encapsulated VLAN Hopping Attack 1. Switches perform only one level of IEEE 802.1q decapsulation 2. This allows the attacker to specify a .1q tag inside the frame, allowing the frame to go to a VLAN that the outer tag did specify. 3. This attack works even if Trunk ports are set to OFF Use dedicated VPAN for all trunk ports. Avoid using VLAN 1. Deploy port security. Set users ports to non trunking. Use ARP security options. Use BPDU guard, Root guard. Use PVLANs. Disable CDP. Disable unused ports and put them in an unused vlan. Ensure DHCP attack prevention. 26 Listed in Lab manual starting on Page 11 MiniPwner Here is a list of some of the software that comes installed: Nmap network scanner Tcpdump sniffer Netcat Hacker’s swiss army knife aircrack Wireless network analysis kismet Wireless network analysis perl Perl Scripting Language openvpn VPN Client and Server dsniff suite of sniffing and spoofing tools, including arpspoof nbtscan NetBIOS Network Scanner snort Sniffer, Packet Logger, Intrusion Detection System samba2-client Windows File Sharing Client elinks Text Based Web Browser yafc FTP Client openssh-sftp-client Secure File Transfer Client Fully loaded. Wireless, 3G/GSM, & NAC/802.1x bypass! Includes 3G, Wireless, & USB-Ethernet adapters Fully-automated NAC/802.1x/RADIUS bypass! Out-of-band SSH access over 3G/GSM cell networks! One-click Evil AP, stealth mode, & passive recon Maintains persistent, covert, encrypted SSH access to your target network Tunnels through application-aware firewalls & IPS Supports HTTP proxies, SSH-VPN, & OpenVPN Analyze risk risk = (cost of an exploit)*(likelihood it will occur) Mobile devices make this inexpensive and very possible (BeetleJuice) inside of “Flame” Demos: Bypass DLP (Safepod) ANTI FaceNif WIFI Kill • • • • • • Inherent trust. “It’s MY PHONE.” Portability is a benefit and a risk • Controls if lost • Lock/Erase? Implications of erasing personal data • PIN security – secure or easy to do 1 handed • What is resident in memory? Malware – whole new breed of malware and products Malicious apps • Increasing • How do you write secure apps? Social engineering providers – value of OOB communication Where did my app come from ? What is a trusted source? Username: root Password: toor startx Tools organized by category in the typical order of a penetration test. Main collection of tools by category Sweet and Simple ICMP: Ping Fping- quickly check an IP range. Not very reliable; many servers and firewalls can turn off ICMP replies. TCP and UDP- More than ICMP Replies Nping TCP UDP IP ranges Many others for Internal and External ▪ Applications> Backtrack> Information Gathering> Network Analysis> Identify Live Hosts Nping --tcp –p 8080 66.110.218.68 Linux: traceroute Win: tracert Seeing hops and routers in between. Zenmap The all-in-one GUI for nmap Hop and routing maps Save findings for later Extremely easy “doors” on the system where info is sent out from and received When a server app is running on a port, it listens for packets When there is nothing listening on a port, the port is closed TCP/IP Stack 65,536 TCP Ports Open – port has an application listening on it, and is accepting packets. Closed – port is accessible by nmap, but no application is listening on it. Filtered – nmap can’t figure out if the port is open or closed because the packets are being filtered. (firewall) Unfiltered – Ports are accessible, but nmap can’t figure out if it is open/closed. Any port can be configured to run any service. But major services stick to defaults Popular TCP ports/services: 80 – HTTP (web server) 23 – Telnet 443 – HTTPS (ssl-encrypted web servers) 21 – FTP 22 – SSH (shell access) 25 – SMTP (send email) 110 – POP3 (email retreival)ecure shell, replacement for Telnet) 445 – Microsoft –DS (SMB communication w/ MS Windows Services 139 – NetBIOS-SSN (communication w/ MS Windows services – 143 – IMAP (email retreival) – 53 – Domain (DNS) – 3306 – MYSQL (database) Nmap ("Network Mapper") is a great tool that we have in both the portable apps and in BT Extremely powerful. Simple use: Nmap –v –A ‘v’ for verbosity and ‘A’ for OS/version Detection Scan one target or a range Built-in profiles or make your own for personal ease. Visual Map Hop Distance Router Information Group Hosts by Service Using a quite traceroute Here are some IPs open to be scanned. Be careful! 66.110.218.68 66.110.220.87 Hackerinstitute.net 66.110.218.106 moodle.gcasda.org Just in case 192.168.2.254 192.168.2.240 Host name to IP lookup: nslookup www.es-es.net Reverse lookup: nslookup 74.208.95.36 dig [domain] any dig es-es.net any The ‘any’ switch is used to show all DNS entries. Just a few record types cribbed from: http://en.wikipedia.org/wiki/List_of_DNS_record_types Code Number Defining RFC Description A 1 RFC 1035 address record 28 RFC 3596 IPv6 address record MX 15 RFC 1035 mail exchange record CNAME 5 RFC 1035 Canonical name record PTR 12 RFC 1035 pointer record AXFR 252 RFC 1035 Full Zone Transfer AAAA http://serversniff.net/subdomains.php http://serversniff.net/nsreport.php gcasda.org http://serversniff.net/content.php?do=httprobots http://whois.domaintools.com/ Tools on Thumb Drive DNS Lookup good DIG tool(GUI) http://nscan.org/dig.html Nirsoft’s http://www.nirsoft.net/utils/whois_this_domain.html http://www.nirsoft.net/utils/ipnetinfo.html Using Wireshark and taking advantage of unencrypted traffic. Telnet Session Website logins SNMP capture Wlan0 needs to be in monitor mode List the available capture interfaces. Choose an interface… ip.src==[ip_address_of_target] Filter by protocol telnet ssh http, etc. and This is used to link multiple filters together Everything is unencrypted over telnet; every character typed is sent as an individual packet. Wireshark can follow and piece together the packet stream for us. This will allow us to see the password in clear text. Here is the unencrypted login page^ Set wireshark to filter and display HTTP only We are now looking for an interesting URL. POST requests can be full of information. Web login for the procurve 2524 Captured login packets, found encoded password hash. Hash looked base64, and used Cain to decode it: The same password from the telnet session Sniff SNMPv1 or SNMPv2c clear text You'd be a fool not to sniff traffic and look for UDP 161 just in case some SNMP traffic leaks to client or servers you control Also, try community string guessing/dictionary attacking against SNMPv1, v2c, or v3 Onesixtyone by Solar Eclipse Speedy –Sends lots of requests in parallel, not waiting for responses Doesn't stop on success –enumerates all valid community strings for a device Good for large-scale iteration through network address space dict.txt includes 49 common strings Free at www.phreedom.org/solar/onesixtyone/ Free Metasploit module: auxiliary/scanner/snmp/community Nice, flexible RHOSTS options (range, list, file, IPv6, etc.) Stops once it gets a success on a given target (maybe just Read) Includes snmp.txt file with 119 common strings If you achieve SNMP Read/Write access, you own the device We can download running or startup configuration for detailed analysis Crack the passwords for it and use them on other network devices Cisco enable passwords are typically stored using salted MD5, easily cracked using John or oclHashcat We could dump CDP, ARP cache, and routing table for target enumeration We could reconfigure the device to allow all sorts of access, such as telnet, ssh, http, or https /pentest/enumeration/snmp Onesixtyone Can dictionary attack SNMP community names With names we can enumerate. onesixtyone –c dict.txt 192.168.2.240 Both snmpcheck and snmpenum are good, but they have their pros and cons. We will use snmpcheck today. ./snmpcheck-1.8.pl -t 192.168.2.240 -c admin v2 We have the admin community from the attack with onesixtyone. Or with the –w option we can check or write access and see if we can reconfigure the switch Cell Communication has been hacked it is not secure Defcon Demos Email pop smtp sent in clear text. If you lose the device it is not stored in a secure environment. Running wireshark to sniff account at coffee shop Several mobile apps have poor security including some bank apps that store username and password on the device in clear text i.e. Citibank PayPal had the app state that if the SSL cert was bad allow it anyway Local device storage issues SSD tends to move the app around on the deice Good uses an encrypted container to store email in “secure” environment Can they get into your VM or fake the caller ID http://www.telespoof.com/freecall/agi http://www.spoofcard.com/ http://www.telespoof.com/freecall/agi www.spoofcard.com http://www.slydial.com/apps.php From the cell tower to back you is unencrypted. Rogue Apps Live malware found How will you updated Over the air or tethered What about Bring your own Device Jailbreakme.com it is so easy to jailbreak / Rooting a device Publish standards of what you will or will not support Poorly codded apps that limit password length complexity, and allow paste Running Wireshark from a mobile device Mobile Management tools available from several 3rd party Vendors : more info on es-es.net AirWatch, Good Technology, MobileIron, Sybase, and Zenprise Most offer remote wipe of Corporate APPS and email. Some have antimalware and filtering options Read the list of permissions that app requests before you install it Does that list make sense? For instance, does a game really need to be able to send premium text messages or access your contact list? Metagoofil http://www.edge-security.com/metagoofil.php Exploit DB Google Dorks http://www.exploit-db.com/google-dorks/ Online Google Hacking Tool http://www.secapps.com/a/ghdb SiteDigger http://www.mcafee.com/us/downloads/freetools/sitedigger.aspx Goolag http://goolag.org RobTex While the interface is a bit weird in my opinion, this is a great site for doing reverse DNS look-ups on IPs, grabbing Whois contacts, and finding other general information about an IP or domain name. http://www.robtex.com ServerSniff This one is sort of an odd ball. Lots of sites offer Whois info, this one goes for more exotic tools. You really have to just play with it to find all of its features. It’s sometimes hard to remember which option is where. Just some of the tools are: ICMP & TCP traceroutes, SSL Info, DNS reports and Hostnames on a shared IP. It’s nice to have them do some of the recon for you if you don’t want to use a proxy and don’t wish for your IP to show up in the target’s logs. http://serversniff.net Check if your email address has been owned http://beta.serversniff.de/compromised.php Portable apps Angry IP Scanner Wireless keyview Zenmap will do more after lunch Attack_Surface_Analyzer_BETA_x64 Wscc Google Hacking Diggity Project -- SearchDiggity.Client Google and Bing “hacking” Creepy FreeScreenRecord– HoffmanUtilitySpotlight2009_04 -- Rich Copy great copying From the portable apps we will do an angry IP scanner on our local network to see what ports are open and if we can get into them. TCPView Suffering from a slow connection? You get the feeling that something's bogging down your WiFi or Ethernet adapter? TCPView (also a part of Sysinternals and available via WSCC) is your chance to figure out which process is costing you how much bandwidth and deal with this connection hog. Simply launch TCPView and sort all processes by clicking the "Sent Packages/Bytes" or "Rcvd Packages/Bytes" header to get the top bandwidth hogs. Sign up for BrowserCheck Business Edition Ensure all browsers and plug-ins used within your organization are up-to-date with the latest security patches BrowserCheck Business Edition: Provides you with a unique URL to give to users inside your company Allows your users to scans their browsers and plug-ins for security issues Helps you track the state of browser security in your organization over time http://www.qualys.com/forms/browsercheck-businessedition/ Vulnerabilities: –OWASP (http://www.owasp.org) –SANS Top 20 (www.sans.org/top20) –National Vulnerability Database (http://nvd.nist.gov) –cgisecurity (http//www.cgisecurity.com) Guidance: –National Institute of Standards and Technology (NIST) Computer Security Resource Center (http://csrc.nist.gov/publications/nistpubs/) –Center for Internet Security (CIS) (http://www.cisecurity.org/) –Educause (http://connect.educause.edu/term_view/Cybersecurity)