Review questions

1
R EVIEW ( NETWORK D ESIGN )
1. List some of the major tasks that should be accomplished in the design phase.
The following are some of the major tasks commonly accomplished in the design phase.
First, the designer(s) will investigate the requirements for the future network.
Develop a logical network model which should include the specifications for the protocols, applications, network media, and network devices.
Develop an IP addressing and routing strategy.
The designer needs to develop a security policy.
Based on the logical network, the designer will develop a plan for the physical implementation of the network. 2
2.
What are the layers in the Cisco hierarchical network design model?
Describe the role of each layer in the hierarchical network model.
What are three roles of the hierarchical model’s core layer?
What are some of the benefits provided by the Cisco Network
Architectures?
3
The Cisco hierarchical network design model has three layers, the core layer, the distribution layer, and the access layer.
The role of each layer in the hierarchical network model is as follows:
Core Layer: connects Distribution Layer devices, provides high-speed, backbone transport
Distribution Layer: interconnects smaller LANs
Access Layer: provides connections for hosts and end devices
Three roles of core layer
Provide fast and efficient data transport
Provide maximum availability and reliability
Implement scalable routing protocols
Functionality, scalability, availability, performance, manageability, and efficiency
4
3. To determine how IP addresses should be assigned, what are the decisions a designer has to make?
The designer should make decisions on the following options.
Use either public IP addresses or private IP addresses for hosts and subnets.
Make decisions on the number of subnets and the number of hosts in each subnet.
Choose to use either classless IP addresses or classful IP addresses.
Determine whether to use a hierarchical routing infrastructure or a flat routing infrastructure.
Decide whether to use the variable length subnet mask.
Determine whether to use supernets.
Decide if a host should be assigned a static IP address or automatically assigned a dynamic IP address.
Reserve a range of static IP addresses for servers and routers.
5
4. Who should be included in creating a security policy?
The security policy is created by a team that consists of an organization’s administrators, network managers, and user representatives
6
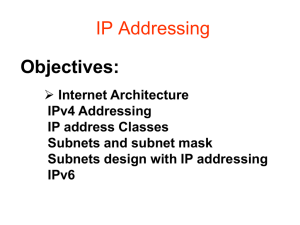
5. What are the prefix and suffix of an IP address?
In IPv4, the 32 binary bits are divided into two parts. The first part is called the prefix which is used to identify the networks. The second part is called the suffix which is used to identify the hosts in a network.
7
6. What are the improvements of
IPv6 over IPv4?
The following are some of the improvements.
IPv6 supports a large number of IP addresses.
IPv6 has a flexible header structure that can minimize header overhead.
IPv6 supports the hierarchical addressing and routing infrastructure to reduce the load on backbone routers.
IPv6 does not support broadcasting. Instead, it supports the more efficient unicast, multicast, and anycast.
IPv6 can create a high quality path between the sender and the receiver for transmitting multimedia content.
IPv6 has the built-in encryption service for data security.
8
7 . M ATCH THE PPDIOO NETWORK
LIFECYCLE PHASES WITH THEIR CORRECT
DESCRIPTIONS .
Prepare phase: 5
Plan phase: 2
Design phase: 4
Implement phase:
1
Operate phase: 6
Optimize phase: 3
1.
2.
3.
4.
5.
6.
The network is built and verified based on design requirements.
The network requirements, where the network will be installed, and who will require network services are identified.
Includes the identification and resolving of network problems, proactively.
A design is proposed based on the initial network requirements along with additional data.
The organizational requirements, development of network strategy, and proposed high-level conceptual architecture are completed.
9
Includes the maintenance of the network and day-to-day activities.
8. What are the three basic steps of the design methodology when using the PPDIOO lifecycle framework?
Identify customer requirements, characterize the existing network and sites, design the network topology and solutions
10
9. What steps are involved in identifying customer design requirements?
Identifying network applications and network services, defining organizational goals, organizational constraints, technical goals, assess technical constraints
11
10. List some common organizational constraints.
Budget, availability of personnel, policies, schedule availability
12
11. What types of redundancies can be implemented in networking?
Device redundancy, including card and port redundancy
Redundant physical connections to workstations and servers
Route redundancy
Link redundancy
13
12. A corporate network is spread over four floors. Each floor has a
Layer 2 switch and more than one
VLAN. One connection from each floor leads to the basement, where all WAN connections are terminated and all servers are located. Traffic between VLANs is essential. What type of device should be used in the basement?
14
A multilayer switch should be used as the building distribution layer in the basement to route between the VLANs, route to the
WANs, and take advantage of the intelligent network services, such as QoS and traffic filtering, which must be supported at the distribution layer.
15
13. Which of the possible routing protocols are recommended to be used at the campus core?
EIGRP or OSPF
16
14. What is Hierarchical Network
Design? What are its advantages over
Flat Networks
In networking, a hierarchical design is used to group devices into multiple networks. The networks are organized in a layered approach. The hierarchical design model has three basic layers:
Core Layer - Connects Distribution Layer devices
Distribution Layer - Interconnects the smaller local networks
Access Layer - Provides connectivity for network hosts and end devices
Advantages:
Hierarchical networks have advantages over flat network designs.
The benefit of dividing a flat network into smaller, more manageable blocks is that local traffic remains local. Only traffic that is destined for other networks is moved to a higher layer.
Layer 2 devices in a flat network provide little opportunity to control broadcasts or to filter undesirable traffic. As more devices and applications are added to a flat network, response times degrade until the network becomes unusable.
17
15. When designing firewall rule sets and Access Control Lists (ACLs, which users or system processes are granted access to objects, as well as what operations are allowed on given objects) for a client, what is the general policy concerning unauthorized traffic? Why?
When designing firewall rule sets and ACLs for a client, the general rule is to deny all traffic that is either not specifically authorized or is not in response to a permitted inquiry. This is done to ensure that only authorized traffic is permitted.
18
16. You are the network designer for
XYZ Company. You plan an IP utilities and tools to perform connectivity and reach ability tests to validate the LAN technologies and devices. What two utilities or tools could you use?
Ping and traceroute
Many others; netstat, nslookup, arp, telnet can test connectivity and display information from the PC.
19
17. You are the network designer for
XYZ Company. Your client needs a secure way of transmitting information across a shared network.
What would you recommend they incorporate into the network design?
VPN would be beneficial in providing secure transmission of information. A
VPN is an extension of the internal private network. VPNs transmit information securely across shared or public networks, like the internet.
20
18. You are the network designer for
XYZ Company. Your client needs a
Mean Time Between Failure (MTBF) for a network is 4000 hours. The availability goal is 99.98%. Compute
Mean Time to Repair (MTTR).
MTTR = 1 hour, the network failure should be fix within 0.8 hour.
21
19. A network design customer has a goal of 99.8% uptime. How much downtime will be permitted in hours per week? How much downtime will be permitted in minutes per day?
Uptime = 167.664, downtime =
168-167.664 = 0.336 hour
Uptime = 1437.12 minutes, downtime =
24 × 60-1437.12 = 2.88minute
22
20. A packet switch has 5 users, each offering packets at a rate of 10 packets per second
The average length of the packets is
1,024 bits. The packet switch needs to transmit this data over a 56-Kbps
WAN circuit. What is the average number of packets in the queue? If the number of the user increased to
100. The packet rate per user keeps the same. WAN circuit changed to T1
(1.544-Mbps), what is the average number of packets in the queue?
23
Queue depth = utilisation/(1- utilisation)
Load = 5 x 10 x 1,024 = 51,200 bps
Utilization = 51,200/56,000 = 91.4%
Average number of packets in queue =
(0.914)/(1-0.914) = 10.63 packets
Utilization = 1024000/1544000 = 66.3%
Average number of packets in queue =
(0.663)/(1-0.663) = 2 packets
24
Scenario one
Refer to Figure, design the addressing scheme for the network.
Ensure that you include the following:
Address the network using the private network
10.0.0.0. Design the addressing scheme so that it allows for the summarization of addresses between areas. Show the summarization that you allocate, and explain your reasons for your choices.
Area 0 is using a prefix of 28 bits within the area.
Area 2 is using a prefix of 22 bits within the area.
Area 3 is using a prefix of 24 bits within the area.
Area 4 is using a prefix of 30 bits for the serial connections. It is using a 28-bit prefix for the connections to the Ethernet routers. Do not include the subnets attached to the LANs in Area 4.
25
26
Ar ea
Subnet/Pref ix
Subnet Range Reasons
0 10.0.0.0/28 10.0.0.16 to
10.0.255.224
The use of the zeros in the second octet is an easy reminder that you are in Area 0. Because Area 0 is a transit area, it will be small. The addressing within the area would be allocated the prefix of 28 bits, allowing the range of SUBNETS shown. The number of hosts on each of these subnets would be 15.
2 10.2.0.0/22 10.2.0.0 to
10.2.252.0
Again, the private addressing of 10.0.0.0 as a Class A address is so large that full use may be made of the documentation advantages of the addressing scheme. The second octet allows Area 2 to be identified. The prefix of 22 bits is used within the area. This allows
1022 hosts on each network, which is good for further VLSM and
VLANs in switched environments.
3 10.3.0.0/24 10.3.0.0 to
10.3.255.0
4 10.4.0.0/28
. . .
Ethernet:
10.4.0.16 to
10.4.255.240
10.4.100.0/3
0
Serial:
10.4.100.0 to
10.4.100.250
The second octet identifies the area. Within the area, a 24-bit prefix is used to address the LANs.
The second octet identifies the area. Within the area, a 30-bit mask is used to identify the serial links on which only two addresses are needed. The subnet 10.4.100.0 was chosen as the subnet to sub-subnet for the serial links simply to ease troubleshooting—all serial links in the company in any area would be assigned the third octet of 100. A
28-bit mask was chosen for the Ethernet connections to allow the 27 creation of many subnets.
Scenario two
Mr. Robertson, the IT director at Pearland Hospital, is responsible for managing the network. Mr. Robertson has requested your help in proposing a network solution that will meet the hospital’s requirements. The hospital is growing, and the management has released funds for network improvements.
The medical staff would like to be able to access medical systems using laptops from any of the patient rooms. Doctors and nurses should be able to access patient medical records, x-rays, prescriptions, and recent patient information. Mr. Robertson purchased new servers and placed them in the data center. The wireless LAN (WLAN) has approximately
30 laptops, and about 15 more are due in six months. The servers must have high availability.
Patient rooms are on floors 6 through 10 of the hospital building.
Doctors should be able to roam and access the network from any of the floors. A radio-frequency report mentions that a single access point located in each communication closet can reach all the rooms on each floor. The current network has ten segments that reach a single router that also serves the Internet. The router is running Routing
Information Protocol Version 1 (RIPv1). The back-end new servers are located in the same segment as those used on floor 1. Mr. Robertson mentions that users have complained of slow access to the servers. He also hands you a table with current IP addresses
28
C URRENT IP A DDRESSES
7
8
5
6
9
10
2
3
4
Floor
1
0
0
0
0
0
0
0
0
0
Servers Clients IP Network
15 40 200.100.1.0/24
43
39
42
200.100.2.0/24
200.100.3.0/24
200.100.4.0/24
17
15
14
20
18
15
200.100.5.0/24
200.100.6.0/24
200.100.7.0/24
200.100.8.0/24
200.100.9.0/24
200.100.10.0/24
29
Mr. Robertson would like a proposal to upgrade the network with fast switches and to provide faster access to the servers.
The proposal should also cover secure
WLAN access on floors 6 through 10.
Include an IP addressing scheme that reduces the number of Class C networks the hospital uses. Mr. Robertson wants to reduce the number of networks leased from the Internet service provider (ISP).
Answer questions
1.What are Pearland Hospital’s business requirements?
2.Are there any business-cost constraints?
3.What are the network’s technical requirements?
4.What are the network’s technical constraints?
5.Prepare a logical diagram of the current network.
6.Does the hospital use IP addresses effectively?
7.What would you recommend to improve the switching speed between floors?
8.Based on the number of servers and clients provided, what IP addressing scheme would you propose?
9.What routing protocols would you recommend?
10.What solution would you recommend for WLAN access and the network upgrade?
31