UA Roadshows—
One Policy:
ISE and TrustSec
Nov 8, 2012
Bob Sayle
Principal Systems Engineer
© 2012 Cisco and/or its affiliates. All rights reserved.
Need for Contextual Access Policy
BYOD with Cisco ISE
Security Group Access and TrustSec
Cisco Access Device
ISE Under the Hood
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
2
© 2012 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
3
The Burden Falls on IT
• How do we simplify the security in the
BYOD process?
• How do we control and segment
the device and users?
• How do we provide consistent
policy across the network?
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
4
Getting BYOD Devices On-Net Without Wasting Their Time
BYOD On-Boarding
Zero-touch portal automates identity, profiling & provisioning to a users’ identity to get them
Zero
touch registration
& provisioning
of employee/guest devices
quickly
& securely
on-net while saving
IT time.
Allowing Users To Safely Go Where They Are Allowed To Go -- From Anywhere
Unified
Policy-based Management
Visibility & contextual control across the network while blocking untrusted access --
control,
guest
lifecycle mgmt
userPolicy-based
authentication, governance
device profiling,, contextual
posture, location,
access
method
Applying
Network Network-wide
Policy to Users from
Entry to Destination (E2E)
Consistent
Security
Control
plane from including
access layer802.1X
thru data
centeruntrusted
that is topology
independent
Compliance
ports,
device
access denial
Policy platform for unified access, DC switches & FWs with ecosystem APIs
Technology
© 2010 Cisco and/or its affiliates. All rights reserved.
Utility
Energy
Healthcare
Higher Ed
Secondary Ed
Cisco Confidential
5
Policy Management
Solution
Unified Network
Access Control
Turnkey BYOD
Solution
1st System-wide Solution
Deep network integration
System-wide Policy
Control from One Screen
Award winning product!
’12 Cisco Pioneer Award
Over 400 Trained &
Trusted ATP Partners
* Pronounced ‘ICE’. Stands for identity services engine, but just call it Cisco ISE
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
6
Policy
Management
Identity Services Engine (ISE)
Policy
Information
User Directory
Prime Infrastructure
Profiling from Cisco Infrastructure
,
Posture from NAC/AnyConnect
Agent
Policy
Enforcement
Cisco Infrastructure: Switches, Wireless Controllers, Firewalls, Routers
Policy
Context
User Identity
© 2010 Cisco and/or its affiliates. All rights reserved.
Personal Devices
Corporate Assets
Non-User Devices
Cisco Confidential
7
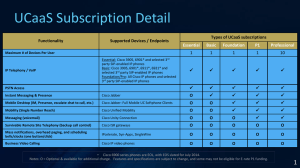
One Network
I only want to allow the “right” users and
devices on my network
Authentication
Services
I want user and devices
to receive appropriate network services
Authorization
Services
I want to allow guests into the network
and control their behavior
Guest Lifecycle
Management
One Policy
I need to allow/deny iPads in my
network (BYOD)
I want to ensure that devices on my
network are clean
I need a scalable way of enforcing
access policy across the network
Profiling and BYOD
Services
Posture
Services
TrustSec SGA
One Management
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
8
© 2012 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
9
Reduced
Burden on
IT Staff
Reduced
Burden on Help
Desk Staff
Intuitive
Management
for End Users
© 2011 Cisco and/or its affiliates. All rights reserved.
•
Device On-boarding
•
Self Registration
•
Certificate and Supplicant
Provisioning
•
Seamless intuitive end
user experience
•
Support Windows,
MAC OS X, iOS, Android
•
My Devices Portal—
register, blacklist, manage
•
Guest Sponsorship Portal
Cisco Confidential
10
MDM cannot ‘see’ non-registered devices to
enforce device security – but the network can!
Best Practice
ISE
MDM
Device Access Control
Mobile Device Security Control
Device Identity
Device Compliance
BYOD On-boarding
Mobile Application
Management
Device Access Control
Data Security Controls
© 2010 Cisco and/or its affiliates. All rights reserved.
* Mobile Device ManagerCisco Confidential
11
• User connects to
Secure SSID
• PEAP:
Username/Password
• Redirected to
Personal Asset
BYOD-Secure
Provisioning Portal
Access Point
• User registers device
Downloads Certificate
Downloads Supplicant Config
Wireless
LAN Controller
• User reconnects using
EAP-TLS
ISE
© 2010 Cisco and/or its affiliates. All rights reserved.
AD/LDAP
Cisco Confidential
12
• User connects to
Open SSID
• Redirected to
WebAuth portal
• User enters employee
or guest credentials
Personal Asset
BYOD-Secure
BYOD-Open
• Guest signs AUP and
Access Point
gets Guest access
• Employee registers device
Wireless
LAN Controller
Downloads Certificate
Downloads Supplicant Config
• Employee reconnects
using EAP-TLS
ISE
© 2010 Cisco and/or its affiliates. All rights reserved.
AD/LDAP
Cisco Confidential
13
A Retail Environment
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
14
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
15
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
16
© 2012 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
17
Any
Device
General Web
Server
User and Device Role
Registered
Device
Employee
News Portal
Manager
Portal
Corporate
Device
Employee
Time Card
Application
Credit Card
Server
Unregistered Device
Employee
Management
Credit Card Scanners
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
18
Any
Device
User and Device Role
Unregistered Device
Employee
Management
Credit Card Scanners
© 2010 Cisco and/or its affiliates. All rights reserved.
Policy Definition
General
Web
Server
Registered Device
Employee
News
Portal
Manager
Portal
Employee
Time Card
Application
Corporate
Device
Credit
Card
Server
Public SSID
Corporate SSID
Member of group “Employee”
Certificate matches endpoint
Corporate SSID
Member of group Employee and
Manager
Certificate matches endpoint
Credit_Card SSID
Member of group “Credit_Scanners”
Profiled as “iphone”
Cisco Confidential
19
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
20
SSID Access:
Corporate-wifi
Employee
Registered
AD Group:
“Management”
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
21
Profiled as an
iPhone
Certificate
Required
SSID Access:
cc-secure-wifi
AD Group:
“Credit Card Scanners”
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
22
VLAN Architecture
Scaling Concerns
Highly topology dependent
ACL Architecture
Hard to Maintain
100s-1000s of ACEs
802.1X
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
23
User and Device Role
Ingress Tag
Unregistered Device
(Unregist_Dev_SGT)
Employee
(Employee_SGT)
Management
(Management_SGT)
Credit Card Scanners
(CC_Scanner_SGT)
SGA TAG - Policy
who
what
where
when
how
Public SSID
Corporate SSID
Member of group “Employee”
Certificate matches endpoint
Cisco ISE
Corporate SSID
Member of group Employee and Manager
Certificate matches endpoint
Credit_Card SSID
Member of group “Credit_Scanners”
Profiled as “iphone”
Finance
Employee
Manager
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
24
Employee TAG
Manager TAG
Credit Card
Scanner TAG
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
25
Manager TAG
© 2010 Cisco and/or its affiliates. All rights reserved.
Credit Card
Scanner TAG
Cisco Confidential
26
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
27
© 2012 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
28
SRC\DST
Time card
Credit card
Manager
(100)
Access
No access
SGT = 100
SGACL
I registered my device
I’m a manager
Time Card (SGT=4)
Credit card
scanner (SGT=10)
Manager
SGT = 100
Cisco ISE
Security Group Based Access Control
• ISE maps tags (SGT) with user identity
• ISE Authorization policy pushes SGT to ingress NAD ( switch/WLC)
• ISE Authorization policy pushes ACL (SGACL) to egress NAD (ASA or Nexus)
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
29
Cisco
Innovation
IP Address
SGT
10.1.100.3
100
SXP
SRC\DST
Time card
Credit card
Manager
(100)
Access
No access
SGACL
I registered my device
I’m a manager
Time Card (SGT=4)
Credit card
scanner (SGT=10)
10.1.100.3
Manager
SGT = 100
Cisco ISE
Security Group Access Protocol
For transport through a non SGT core
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
30
© 2012 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
31
Cisco
Innovation
a
Identity Differentiators
Authentication Features
Monitor Mode
Cisco Catalyst Switch
• Unobstructed access
• No impact on productivity
• Gain visibility
Flexible Authentication Sequence
• Enables single configuration for most use cases
• Flexible fallback mechanism and policies
Rich and Robust 802.1X
IP Telephony Support for
Virtual Desktop Environments
• Single host mode
• Multihost mode
• Multiauth mode
Authorized
Users
802.1X
Tablets
IP Phones
MAB
Network
Device
Guests
WebAuth
• Multidomain authentication
Critical Data/Voice Authentication
• Business continuity in case of failure
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
32
• EAP Chaining ties both the machine and user credentials to the device, thus
the "owner" is using a corporate asset
Use Cases:
• Restrict use of personal laptops on a corporate network
• Corporate mandates where a corporate asset must be used and the user must
be authorized.
Machine
Credentials
Machine
Authentication
RADIUS
User
Credentials
Machine and User Credentials
Validated AD Database
User Authentication (includes both user and machine identity types )
User
Authentication
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
33
Device Sensor
Cisco
Innovation
Automated Device Classification Using Cisco Infrastructure
DEVICE PROFILING
CDP
LLDP
DHCP
MAC
Supported Platforms:
IOS 15.0(1)SE1 for Cat 3K
IOS 15.1(1)SG for Cat 4K
WLC 7.2 MR1 - DHCP data only
ISE 1.1.1
For wired and wireless networks
POLICY
Printer
ISE
Personal iPad
Access Point
Printer Policy
CDP
LLDP
DHCP
MAC
Personal
iPad Policy
CDP
LLDP
DHCP
MAC
[place on VLAN X]
[restricted access]
Access
Point
`
The Solution
Efficient Device
Classification
Leveraging
© 2010 Cisco and/or itsInfrastructure
affiliates. All rights reserved.
DEPLOYMENT SCENARIO WITH CISCO DEVICE SENSORS
COLLECTION
Switch Collects Device
Related Data and Sends
Report to ISE
CLASSIFICATION
ISE Classifies Device, Collects
Flow Information and Provides
Device Usage Report
AUTHORIZATION
ISE Executes Policy Based
on User and Device
Cisco Confidential
34
© 2012 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
35
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
36
Tying it All Together
Contextual Access Control
User
© 2010 Cisco and/or its affiliates. All rights reserved.
Device Type Location
Posture
Time
Access Method Custom
Cisco Confidential
37
What’s the Cisco
Advantage?
Fun Fact:
Cisco has 4X more
dedicated BYOD engineers
than our competitors!
Market Leader
NAC, AAA, VPN, FW – we know security
Systems Solution vs. Overlay
Deep integration vs. band aids
Commitment
Extensive engineering is funded
We are Ready
Over 400 ATP partners vigorously trained
Leader in Gartner NAC Magic Quadrant
Dec 2011
“TrustSec and ISE are consistent with our view of
identity-centric end-to-end security that is both
needed and lacking in the enterprise today.”
Forrester 2011
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
38
Removes the IT Burden
Easy BYOD
User Self Onboarding
Unified Policy
Access Control
Contextual Policy & Access
Control for Users & Guests
Consistent Security
© 2010 Cisco and/or its affiliates. All rights reserved.
Compliance: Regulatory,
Government, Corporate
Cisco Confidential
39
• ISE Information:
http://www.cisco.com/go/ise
• Cisco TrustSec:
www.cisco.com/go/trustsec
• Application Notes and How-To Guides:
http://www.cisco.com/en/US/solutions/ns340/ns414/ns742/ns744/l
anding_DesignZone_TrustSec.html
© 2010 Cisco and/or its affiliates. All rights reserved.
Cisco Confidential
40