2nd training on debugging
advertisement
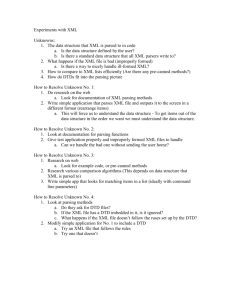
Debugging lab 2 Outline • XML • Digital signature • Laboratory of debugging – XML-security 2 Xml: eXtensible Language Markup • • • • Language to describe and transmit data Based on tags Designed to be self-descriptive W3C recommendation Xml: elements Open tag Close tag Comment <root> <child> <subchild>.....</subchild> </child> </root> <?xml version="1.0" encoding="ISO-8859-1"?> <!-- very important note --> <note> <to>Tove</to> <from>Jani</from> <heading>Reminder</heading> <body>Don't forget me this weekend!</body> </note> source: http://www.w3schools.com/ Xml: attributes Attributes <bookstore> <book category="COOKING"> <title lang="en">Everyday Italian</title> <author>Giada De Laurentiis</author> <year>2005</year> <price>30.00</price> </book> <book category="CHILDREN"> <title lang="en">Harry Potter</title> <author>J K. Rowling</author> <year>2005</year> <price>29.99</price> </book> </bookstore> source: http://www.w3schools.com/ Xml: special characters • Some characters have special meaning, so they must be handled with care <message>if salary < 1000 then</message> <message>if salary &lt; 1000 then</message> source: http://www.w3schools.com/ < > & ‘ “ &lt; &gt; &amp; &apos; &quot; Solving conflicts using prefixes <table> <tr> <td>Apples</td> <td>Bananas</td> </tr> </table> <table> <name>African Coffee Table</name> <width>80</width> <length>120</length> </table> source: http://www.w3schools.com/ Solving conflicts using prefixes <h:table xmlns:h="http://www.w3.org/TR/html4/"> <h:tr> <h:td>Apples</h:td> <h:td>Bananas</h:td> </h:tr> </h:table> <f:table xmlns:f="http://www.w3schools.com/furniture"> <f:name>African Coffee Table</f:name> <f:width>80</f:width> <f:length>120</f:length> </f:table> source: http://www.w3schools.com/ Public/private key Document 11288233f Digital signing Signature verification Main features of XML-security • Canonize (standardize) xml documents, make logically-equivalent xml parts comparable • Sign xml elements: whole document, element, element content • Verify signatures XML-Security project • Xml-security (Apache Santuario) project is aimed at providing implementation of security standards for XML. Currently the focus is on the W3C standards: – XML-Signature Syntax and Processing; and – XML Encryption Syntax and Processing. • Java implementation library includes a mature Digital Signature and Encryption implementation. It also includes the standard JSR 105 (Java XML Digital Signature) API. • Applications can use the standard JSR 105 API or the Apache Santuario API to create and validate XML Signatures. Component of an XML Signature <Signature> <SignedInfo> (CanonicalizationMethod) (SignatureMethod) ( <Reference (URI=)?> (Transforms)? (DigestMethod) (DigestValue) </Reference> )+ </SignedInfo> (SignatureValue) (KeyInfo)? (Object)* </Signature> Each resource to be signed has its own <Reference> element, identified by the URI attribute The <Transform> element specifies an ordered list of processing steps that were applied to the referenced resource’s content before it was digested. The <DigestValue> element carries the value of the digest of the referenced resource The <SignatureValue> element carries the value of the encrypted digest of the <SignedInfo> element The <KeyInfo> element indicates the key to be used to validate the signature. Possible forms for identification include certificates, key names, and key agreement algorithms and information source: http://www.xml.com/pub/a/2001/08/08/xmldsig.html Example of xml signature <Signature Id="MyFirstSignature" xmlns="http://www.w3.org/2000/09/xmldsig#"> <SignedInfo> <CanonicalizationMethod Algorithm="http://www.w3.org/TR/2001/REC-xml-c14n-20010315" /> <SignatureMethod Algorithm="http://www.w3.org/2000/09/xmldsig#dsa-sha1" /> <Reference URI="http://www.w3.org/TR/2000/REC-xhtml1-20000126/"> <Transforms> <Transform Algorithm="http://www.w3.org/TR/2001/REC-xml-c14n-20010315" /> </Transforms> <DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1" /> <DigestValue>j6lwx3rvEPO0vKtMup4NbeVu8nk=</DigestValue> </Reference> </SignedInfo> <SignatureValue>MC0CFFrVLtRlk=...</SignatureValue> <KeyInfo> <KeyValue> <DSAKeyValue> <p> ... </p> <Q> ... </Q> <G> ... </G> <Y> ... </Y> </DSAKeyValue> </KeyValue> </KeyInfo> </Signature> Source: http://www.ibm.com/developerworks/xml/library/s-xmlsec.html/index.html Laboratory • Download xml-security from http://selab.fbk.eu/swat/debugging/xmlSecurityTraining.zip • Import the project in Eclipse • Address tasks in order • Fix the bugs reported by the test cases/answer the question – – – – Record start time Fix the bug/answer the question Record stop time Fill the feedback questions • Deliver the paper sheet • Export the eclipse project and send it to studio.empirico@gmail.com 16