security performance
advertisement
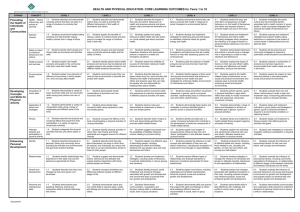
BT Security BT Security is the provider of choice for secure solutions 1 Agenda ●BT Security Performance Andy Talbot ●Process Re-engineering Andy ●People Plan Jacky West ●Behaviours Programme Keith Bezant Andy Talbot SECURITY PERFORMANCE BT Security team Scorecard P5 August 2010 Miss Thresh Target Stretch Gross Managed Costs - £m Revenue Fraud Improvement- £m debt Customer Experience – % targets hit Revenue Earning - std + custom contract revenues Transformation Delivery - % benefits Security Programme - % IAD actions/date agreed Security Risks Mgt – # satisfactory 4 Andy Talbot PROCESS RE-ENGINEERING Risk Line of Sight Driven by risk appetite – what we are prepared to lose whilst maintaining acceptable service delivery Metrics Risk Assessment Standard BT VTC risk assessment & management cycle. Key Risk Indicators How Risk Owner knows if the risk is increasing or decreasing. Vulnerability KRI Triggers KRI Consequences Etc.. Appetite A mix of lagging and leading KRIs. Can highlight environment drivers or controls inadequacy. Risk Control Strategy maintained to achieve a proportionate response to the risk (i.e. within appetite). Strategy Controls are related to the KRIs and viceversa to allow clear & defined management focus as issues arise. Existing Control Services Control KPIs & Owners Change Projects & CSFs Provided from the BTS Unified Services Catalogue. Key aspects of the controls are monitored for efficiency & effectiveness. Control KPI Project Control KPI Project Etc.. Etc.. Etc.. Controls are made up of a set of related parts that combine to achieve the risk mitigation outcome Potential De-railers Identified items beyond our control that may have a material effect on the risk and/or the ability of the controls to be effective. We may be able to lobby/influence and monitor. E.g. people’s behaviour. Programme to achieve target level of risk exposure and benefits. Failing controls and accepted audit reqs lead to corrective projects. Performance feedback loop on controls. At any time all or part of the Strategy may be implemented in controls. The remainder may be prioritised into Projects also for change projects or as candidates driven from Risk future investment. Audit may also raise Control Strategy. reqs that will accepted into change projects in line with the strategy. Our Approach to selection • Follow the BT Operate Selection Process once we have finalised the rationalisation and completed the reorganisation • Pre-deployment of people where possible into growth roles • Quality proofed selection procedure (BTO) • Commitment to train/re-skill our people as appropriate • Displaced people to move to Career Transition Centre • Underpinned by a joined up consultation and communications plan Jacky West PEOPLE PLAN People Plan Engagement Organisation Design and Transformation ● Strategic comms plan – for a Global organisation ● HR Surgeries ● SLT Meetings around the country with roundtables ● Simply Security 2 Roadshows – completed with great feedback ● Formal visibility plan for Leadership Team ● CARE Agile - ● Organisation review and integration of recent Global transfer ● OD review of overlaps into wider BT group ● Flexible resource model critical to success ● Future skills work – 7 MAs and 2 Fast Trackers - PCI 3.9 (+0.11) ● Process realignment - Bullying & Harassment – 10% (-9%) ● Phase 3 Transfers – EEI 3.76 (+0.23) B&H awareness sessions rollout - good take up started in August – extra sessions being planned Creating a High Performance Culture Performance management High Performance Culture roll out Standards set across BT Security Talent Security talent pool Group talent pool (11) Local security talent pool event 14 September Pivotal roles and succession plan Retention plans – individual Excellent Skills •Regretted leavers – especially CLAS skills •Security Professional Community •Training plan linked to Professional Community •YSC investment for SMT •Knowledge Management •Focus on re-skilling training - CLAS accreditation •New Security Job Family – phase 2 •SLT Leadership impact assessment •Development Centres •Security Academy Keith Bezant BEHAVIOURS PROGRAMME The Problem ● Security vulnerabilities caused by poor behaviour, raising the likelihood of a serious incident ▬ Personal injury ▬ Theft/damage of critical equipment ● Undermines the considerable proactive investment being made in physical security measures ● Presents a poor image to third parties, including the general public, contractors and clients What we are trying to achieve ● Ensure the Health & Safety of our staff ▬ Maintain a secure working environment ▬ Ensure equipment is not tampered with/stolen ● Improve security awareness of our staff ▬ Maintain customer service ▬ Reduce likelihood and impact of incidents ● Encourage compliance to policy ▬ Develop greater pride in the workplace, make it personal ▬ Focus on positive consequences wherever positive ▬ Use negative consequences as a last resort What we need your help with Working in partnership with security ● Help shape the behaviours programme (active member involvement) ● Reframing security in terms of personal welfare ● Help to articulate the impact/consequence of poor behaviours ● Offer ‘independent’ support to the programme ● Support the communications and awareness campaigns ● Support the positive consequences for good behaviour ● Help develop and support the negative consequences for consistent poor behaviours