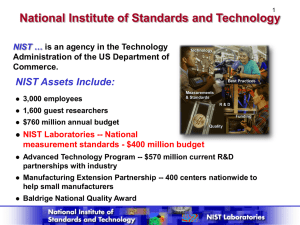
HUMAN FACTORS IN IT SECURITY UNIT 10 AUDIT AND FORENSICS Audit Frameworks ■ SANS ■ COBIT ■ NIST ■ ITIL ■ Compliance Frameworks SANS Top 20 1. Inventory of Devices 2. Inventory of Software 3. Secure Configurations-workstations 4. Vulnerability Assessment and Remediation 5. Malware Defenses SANS Top 20 6. Application Software Security 7. Wireless Access Control 8. Data Recovery Capability 9. Security Skills Assessment/Training 10. Secure Configurations for Network Devices SANS Top 20 11. Limitation and Control of Network Ports 12. Controlled Use of Administrative Privileges 13. Boundary Defense 14. Maintenance, Monitoring, and Analysis of Logs 15. Controlled Access Based on the Need to Know SANS Top 20 16. Account Monitoring and Control 17. Data Protection 18. Incident Response and Management 19. Secure Network Engineering 20. Penetration Tests and Red Team Exercises What is COBIT? ■ A set of best practices for Information Technology management ■ Developed by (ISACA) ■ Framework helping IT professionals and enterprise leaders fulfill their IT Governance responsibilities while delivering value to the business. ■ COBIT 5 is an end-to-end business view of the governance of enterprise IT that reflects the central role of IT in creating value for enterprises. What’s In COBIT ■ Framework - Organize IT governance objectives and good practices by IT domains and processes, and links them to business requirements ■ Process Descriptions - A reference process model and common language for everyone in an organization. The processes map to responsibility areas of plan, build, run and monitor. ■ Control Objectives - Provide a complete set of high-level requirements to be considered by management for effective control of each IT process. ■ Management Guidelines - Help assign responsibility, agree on objectives, measure performance, and illustrate interrelationship with other processes ■ Maturity Models - Assess maturity and capability per process and helps to address gaps. Benefits ■ Maintain high-quality information to support business decisions ■ Achieve strategic goals and realize business benefits through the effective and innovative use of IT ■ Achieve operational excellence through reliable, efficient application of technology ■ Maintain IT-related risk at an acceptable level ■ Optimize the cost of IT services and technology ■ Support compliance with relevant laws, regulations, contractual agreements and policies US Cert Overview: What is Forensics ■ The discipline that combines elements of law and computer science to collect and analyze data from computer systems, networks, wireless communications, and storage devices in a way that is admissible as evidence in a court of law ■ Defense in Depth ■ New Discipline, there is little consistency…. (2008) ■ Persistent Data – stored ■ Volatile Data – lost when computer is turned off US Cert Overview: Legal Aspects ■ You must have authorization – Management – Policy monitor and collect ■ New Rulings on admissibility ■ Avoid Lawsuit ■ Regulatory Audit US Cert Overview: Legal Aspects ■ 4th Amendment-unreasonable search and seizure ■ 5th Amendment-protection against self incrimination ■ Wire Tap Act ■ Pen Registers and Trap and Trace Devices statute ■ Stored wired and Electronic Communications Act ■ US Federal Rules of Evidence –hearsay, authentication, reliability and best evidence NIST 800-86: Executive Summary ■ Forensics – Application of science to the law ■ Digital Forensics – Application of science to the identification, collection, examination and analysis of data while preserving the integrity of the information ■ Development of Policies and Procedures NIST 800-86: Policies, Procedures and Guidelines 1. Organizations should ensure that their policies contain clear statements addressing all major forensic considerations 2. Organizations should create and maintain procedures and guidelines for performing forensic tasks 3. Organizations should ensure that their policies and procedures support the use of forensic tools. 4. Organizations should ensure that their IT professionals are prepared to participate in forensic activities NIST 800-86: The Need for Forensics “ ….most often thought of in the context of criminal investigations…also useful for many other types of tasks” 1. Operational Troubleshooting 2. Log Monitoring 3. Data Acquisition 4. Regulatory Compliance NIST 800-86: Digital Forensic Staffing Types 1. Investigators 2. IT Professionals 3. Incident Handlers Internal vs External 1. Cost 2. Response Time 3. Data Sensitivity NIST 800-86: Digital Forensic Techniques Supporting Forensics in the Information Systems Life Cycle ■ Perform Regular Backups ■ Enable Auditing on workstations, servers and network devices ■ Forward Audit records to secure centralized log servers ■ Configure mission critical applications to perform auditing ■ Maintain standard configurations of OS’s and file hashes – ■ Use file integrity checking software on particularly important assets Maintain baselines of network and system configurations SANS Critical Controls: Critical Control 14 Maintenance, Monitoring an Analysis of Audit Logs “Sometimes logging records are the only evidence of a successful attack” “Many organizations only keep audit records for compliance purposes” Quick Wins 2 synchronized time sources Validate Audit logs / Adequate Storage Log Retention Policy Verbose Logging By-weekly reports NIST 800-86: Digital Forensic Process Collection: identifying, labeling, recording, and acquiring data from the possible sources of relevant data, while following procedures that preserve the integrity of the data. Examination: forensically processing collected data using a combination of automated and manual methods, and assessing and extracting data of particular interest, while preserving the integrity of the data Analysis: analyzing the results of the examination, using legally justifiable methods and techniques, to derive useful information that addresses the questions that were the impetus for performing the collection and examination. Reporting: reporting the results of the analysis, which may include describing the actions used, explaining how tools and procedures were selected, determining what other actions need to be performed (e.g., forensic examination of additional data sources, securing identified vulnerabilities, improving existing security controls), and providing recommendations for improvement to policies, procedures, tools, and other aspects of the forensic process NIST 800-86: Digital Forensic Process NIST 800-86: Data Collection ■ Primary Sources ■ Information may also be recorded by other organizations ■ Sometimes it is not feasible to collect data from a primary source NIST 800-86: Data Collection Four major categories of data source 1. Files 2. OS 3. Network Traffic 4. Applications NIST 800-86: Data Collection: Acquiring the Data 1. Develop a plan Multiple potential data sources Likely Value Volatility Amount of Effort required 2. Acquire the data Forensic Tools 3. Verify the integrity of the data Using tools to compute the message digest/hash NIST 800-86: Incident Response Considerations ■ Response should consider in advance the impact that various containment strategies may have on the organization to operate effectively ■ Criminal – Collected hardware may be unavailable for an extended period of time ■ Incident – Secure the perimeter around a computer NIST 800-86: Data Collection: Examination ■ Involves assessing and extracting the relevant pieces of information from the collected data ■ An acquired hard drive may contain thousands of data files – (and interesting deleted files) ■ Yesterday’s firewall log might hold millions of records – Only 5 or 10 may be of value ■ Tools ■ Search NIST 800-86: Data Collection: Analysis ■ The foundation of forensics is using a methodical approach to reach appropriate conclusions based on the available data or determine that no conclusion can yet be drawn. ■ Should include identifying people, places, items, and events and determining how these elements are related ■ Tools can facilitate this process by automatically gathering and correlating the data NIST 800-86: Data Collection: Reporting Many factors affect reporting ■ Alternate Explanations – Maybe multiple plausible explanations – Methodical approach ■ Audience Considerations – Law enforcement – Detailed collection information – System Admins – Logs – Management – High level overview, Business outcomes ■ Actionable Information – List of contacts – Prevent future events NIST 800-86: Using Data from Data Files ■ Analysts should have a reasonably comprehensive understanding before beginning ■ Media (HD/USB/CD/DVD.. SD Card/Tape ■ File systems – Partitioning, directory structure, file allocation tables ■ Copying files from media (Logical Backup/Bit Stream Imaging) ■ Data File Integrity – Write blockers ■ File Attributes (Modification Time/Access Time/Creation Time) ■ Locating and Extracting ■ Analyzing NIST 800-86: Using Data from Operating Systems ■ An OS is a program that runs on a computer and provides a software platform on which other programs run ■ Volatile vs Non–Volatile ■ Config Files, Users and Groups , Password files, Scheduled Jobs ■ Logs! (System Event/Audit/Application /Events/Command History ■ Applications ■ Swap Files/Dump Files /Hibernation Files ■ Memory – Volatile ■ Network information – Volatile? ■ Prioritization? NIST 800-86: Using Data from Network Traffic ■ Network Traffic refers to computer network communications that are carried between hosts 4 Layer TCP/IP Stack Sources firewall/routers Packet sniffers, protocol analyzers Packet sniffers are designed to monitor network traffic and capture packets Protocol analyzers can re-assemble streams from packets IDS Intrusion detection systems analyze network traffic to identify suspicious activity Remote Access Security information event management (SIEM) NIST 800-86: Using Data from Applications ■ From a forensic perspective, applications bring together files, OSs, and network ■ Application and supporting files ■ Type of Application (Web/Email/File share/Office) ■ Concealment Tools – Encryption – Steganographic tools – Clean up tools ■ Collection HUMAN FACTORS IN IT SECURITY UNIT 10 AUDIT AND FORENSICS