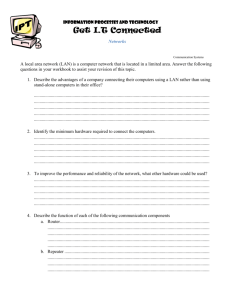
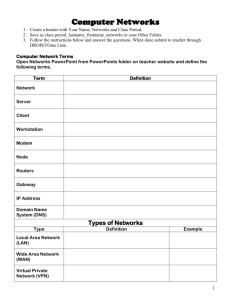
ASSIGNMENT # 1 Data Communication & Networks 15-11-2018 Submitted by: ASMA SHABIR Roll no: fa15-bscs-269 Class: 6th (b) Submitted to: DR ASIF Q No: 1 Write the difference between the following (i) Amplifier & Repeater: 1: Amplifier is used to magnify a signal, whereas repeater is used to receive and retransmit a signal with a power gain 2: Repeater has an amplifier as a part of it. 3: Sometimes, amplifiers introduce some noise to the signal, whereas repeaters contain noise eliminating parts. (ii) LAN & WAN: 1: LAN has to cowl small geographical area that’s why its data change speeds are extreme. While WAN has to cowl bigger distance which suggests knowledge has to journey prolonged distance, so there is likely to be mechanically low change tempo. 2: LAN is usually managed and managed by one particular person or a small dimension group whereas WANs have collective or distributed possession and administration for each specified area. 3: LAN has low repairs value whereas WAN setup costs are typically bigger on account of hook up with distant areas 4: It could also be very easy to trace out errors or fault in LAN that could be very onerous in case of WAN. (iii) Mesh & Star topologies: 1: The Star topology organizes the node in a star shape where the central hub is connected to all the other nodes. On the other hand, in the mesh configuration, each node is connected to the other nodes 2: Easy installation and reconfiguration is possible in the star topology. As against, the mesh topology requires more transmission media, effort and time for installation and reconfiguration. 3: Star topology is cost-effective to some extent, while the mesh is expensive. 4: The star topology has a drawback where the inoperative central hub can make the entire system inoperative. On the contrary, the mesh topology is more robust than the star topology. (iv) Physical and logical address: 1: The basic difference between Logical and physical address is that Logical address is generated by CPU in perspective of a program. On the other hand, the physical address is a location that exists in the memory unit. 2: The logical address is also called virtual address as the logical address does not exist physically in the memory unit. The physical address is a location in the memory unit that can be accessed physically. 3: The logical address is a reference used to access physical address. The user can access physical address in the memory unit using this logical address. (v) Hub and Switch: 1: Hub are network devices that operate on physical layer-1 to connect network devices for communication while switches are forward data at the data link layer (layer 2) of OSI model. 2: Hub is a passive device (without software) while switch is an active device (with software) & networking device. 3: Hub cannot learn or store MAC address while switch stores MAC addresses in a lookup table. Q No:2: What is a peer-to-peer process? Peer-to-peer process: A layer appears to be communicating directly with the same layer at the other end of the link (i.e. its peer). What is actually happening is that the data is being passed down to lower layers for transmission and is passed up again at the other end. Q No: 3: What are the advantages of layering? Advantages of layering: It prevents changes in one layer from affecting other layers. It describes what functions occur at each layer of the model that encourages industry standardization. Dividing network communication process in smaller component makes software development, design, and troubleshooting easier. Standardization of network components allows multiple-vendor development. It allows different types of network hardware and software to communicate. Dividing network in layers make network administrators life easier. They can troubleshoot issue more quickly and effectually by looking in layer that is causing issue rather than finding it entire network. It also makes learning easier. Q No 4: Is it true that the most upper layer of OSI Model can enjoy all the services provided by all lower six layers? if yes, why? ANS: The layered model allows for abstraction. In other words, the higher layers do not necessarily have to know how the lower layers are doing their jobs. In addition, the lower layers do not necessarily have to know what the upper layers are actually doing with the results of the lower layers’ labors. Q No: 5 Suppose a computer sends a packet at the network layer to another computer somewhere in the internet. The logical destination address of the packet is corrupted. What happen to the packet? How can the source computer be informed of the situation? Ans: when a packet gets sent out it has both the destination address and the source address. Once the destination successfully receives the packet it send a response back to the source address to say it was successful. (With UDP - you just send it and don’t wait for an acknowledgement that it got there OK). Therefore if the destination address or source address were incorrect, the source machine would not get a return saying all got through OK. Normally this would result in the packet being resent after a period of time. So assuming we have an incorrect address, the packet will eventually be delivered to the wrong destination (that system might send back that it received it OK - so that could be a problem - but hopefully it would ignore it - a bit like I do with letters I don’t want to receive - depends on firewall policies). Otherwise it will fail quite quickly when it can’t be routed to a host, in which case you would get an error message back. (Using the source address). Q No:6 Draw a hybrid topology with a star backbone and three ring networks Q N0:7 Let n be the number of terminal. What is the number of cables required for each type of networks: a. Mesh: A fully connected mesh network therefore has n(n-1)/2 physical channels to link n devices b. Star: In star a central hub is used and cable depend on the number of system need to b connected c. Bus: In bus network one main cable is used and n numbers of computers connected side by side as needed. d. Ring: In ring network cable=number of computers need to form a circle or a ring Q N0 8: What will happen to each of the following network of five devices if a single connection (link) is failed: a. Mesh Topology: A MESH TOPOLOGY IS ROBUST. IF ONE LINK BECOMES UNUSABLE, IT DOES NOT HALT THE ENTIRE SYSTEM. b. Star Topology: IF ONE LINK FAILS, ONLY THAT LINK IS EFFECTED, ALL OTHER REMAIN ACTIVE. c. Bus Topology : A FAULT OR BREAK IN THE BUS CABLE STOP ALL TRANSMISSION. Ring Topology: IN A SIMPLE ONE WIRE RING, A BREAK IN THE RING SUCH AS A DISABLE STATION CAN DISABLE THE ENTIRE NETWORK. BUT THIS WEAKNESS CAN BE SOLVED BY USING A DUAL RING OR A SWITCH CAPABLE OF CLOSING OFF THE BREAK. Q No: 9 Explain function and the structure of OSI model layers? The OSI (Open Systems Interconnection) Model is a conceptual model that characterizes and standardizes the communication functions of a telecommunication or computing system without regard to its underlying internal structure and technology. Its goal is the interoperability of diverse communication systems with standard protocols. In the OSI model, control is passed from one layer to the next, starting at the application layer (Layer 7) in one station, and proceeding to the bottom layer, over the channel to the next station and back up the hierarchy. The OSI model takes the task of inter-networking and divides that up into what is referred to as a vertical stack that consists of the following 7 layers. Layer 7 - Application Layer 6 - Presentation Layer 5 - Session Layer 4 - Transport Layer 3 - Network Layer 2 - Data Link Layer 1 - Physical