USTAT A Real-time Intrusion Detection System for UNIX By: Koral Ilgun
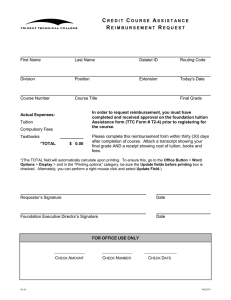
advertisement
USTAT A Real-time Intrusion Detection System for UNIX By: Koral Ilgun Jul-16 Overview: Introduction to USTAT - State Transition Analysis Tool for Unix Key issues System components Implementation issues Evaluation of USTAT Jul-16 Introduction to USTAT Misuse detector A penetration is (viewed as) a sequence of signature actions and a corresponding sequence of state changes that lead the computer from some initial state to a target compromised state Basic Properties of USTAT Real-time expert system intrusion detection tool Rule-based analysis Only for known penetrations Targets abusive insiders Jul-16 Comparison between USTAT and other intrusion detection systems Statistical anomaly detection Rule-based misuse detection Jul-16 threshold detection profile-based it is an expert system Most current intrusion detection tools employ both the anomaly detection and (rule-based) misuse detection components State Transition Analysis Jul-16 View a penetration as a (known) sequence of actions S1, S2, …,Sn that lead from an initial (limited authorized) access state, S1 to a final compromised state, Sn State Transition Analysis (cont) State really represents some attribute of the system – not the whole system state State is generic, e.g. “user is now root” Penetration sequence represented by finite state machine Jul-16 node is a state arc is an action (or transition) Examples: % ln target -x % -x User creates link euid(user) = not root User executes file euid(user) = root File ‘target’ is root’s setuid shell script that contains the #!/bin/sh mechanism Jul-16 Examples (cont): Jul-16 1. Attacker creates hard link starting with dash to root’s setuid shell script that contains the #!/bin/sh mechanism 2. Attacker executes “-x” Insight: Creating hard link ==> new directory entry is created with target’s original privileges and ownership information Target can be accessed via any link to it Executing shell script containing #!/bin/sh invokes a sub-shell Sub-shell becomes interactive (because of the “-”) Attacker is thus executing a setuid file owned by root, so shell has effective ID of root Examples (cont): Two actions/transitions: make hardlink execute “-x” Three states: Initial state: euid = user (not root) Intermediate state: hardlink established Final compromise state: not euid = user I.e. a user (non-root) running an interactive shell with an effective user id of root Jul-16 Features of USTAT Preempts attacks: USTAT monitors state transitions Note that they can span multiple sessions It foresees impending compromise -- at least one transition away Recognizes cooperative attacks Note that USTAT is not tied to users or processes It reflects state of the system So, it can detect state resulting from actions by multiple users Jul-16 USTAT input Audit records of the form, <subject, action, object> Subject is <real userID, effective userID, groupID> Action is <action, time, processID> Object is <object name, permissions, owner, group owner, inode #, device #, file systemID, target> All information can be obtained directly from Unix audit records Jul-16 USTAT input (cont) Unix audits 239 event types Only 28 are useful to USTAT They are mapped down to 10 USTAT action types Filters out all failed command events early, i.e. all the events with a return value of -1 Jul-16 USTAT simplifications (cont) All (audited) actions mapped to a small set: read write create execute exit delete modify-owner rename modify-permission hardlink Files are categorized: E.g. all files that should not be accessed via regular utilities (because they hold sensitive data) are mapped to “Fileset1” 5 “filesets” Jul-16 USTAT monitoring Monitors for all known penetrations simultaneously Finite state machine for each known penetration Maintains state tables Row represents instance of not yet completed penetration Column represents states in penetration scenario Cell holds detailed info, e.g. userID, actual file names, etc Jul-16 USTAT INITIAL state table One row for each known penetration, I.e. each possible penetration is in its initial state Initial action/transition for each is anticipated Inference Engine accepts audit input For each row, it asks: does this audit event match the “next transition” anticipated for this row such that the next state is satisfied If so, duplicate the row and mark “details” for the now satisfied state Jul-16 Decision Engine Informs sys admin about results of the inference engine Is compromise about to occur? Has compromise occurred? Play an active role in preempting the attack! However, note that USTAT input comes from the OS (Unix) audit log Jul-16 Strength and weakness of USTAT Strength: Weakness - Cannot cope with the following attacks: Jul-16 Flexibility Real-time -- preempts attack before system is damaged Detects cooperative attacks Manipulation of components outside the system’s execution domain, e.g., wiretapping Denial of service attacks Failures Evaluation of USTAT Jul-16 Massive amount of data that was collected by the audit daemon limited extensive testing Limiting factor is the transfer rate of the disk that is extensively used by USTAT and the audit daemon USTAT functionality costs 13% of machine Papers do not indicate number of penetrations that can be described as state transition diagram NSTAT – USTAT for Distributed Systems Jul-16 Similar “state-based” approach Input: audit data from multiple hosts Objective: detect coordinate attack Central server processes input Time – how to deal with skewed clocks? Vulnerability of NSTAT server Compare! Tripwire -- Integrity of file data GrIDs -- graph nodes (or accumulated groups of nodes) with arcs depicting message traffic USTAT -- monitor for known penetrations, tracking state changes that progress toward compromise Jul-16