Received 29 December 2004; received in revised form 24 Reporter :

Received 29 December 2004; received in revised form 24
January 2006; accepted 3 February 2006
Information Sciences, Vol. 176, No. 22, Nov. 2006, pp. 3393-3408
Reporter : Chien-Wen Huang
Date :2009.10 .24
1
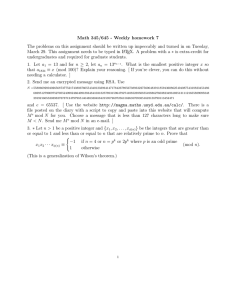
1.
2.
3.
4.
5.
Introduction
Related Work
The Proposed Methods
Hiding bitmap files
Hiding general data files
Experimental Results
Discussion and Conclusions
2
The most well-known steganographic technique-LSB.
RLE (Run-Length Encoding)
Compression standard in fax transmissions and bitmap-file coding.
Two efficient data hiding methods by run-length encoding .
BRL and GRL
3
Wu and Tsai’s steganographic method
4
Chang and Tseng’s steganographic method
5
RLE
Example1 :
AAAAABBBBAA 5A4B2A
Example2:
111000001111 315041
6
The host image is partitioned into non-overlapping consecutive two-pixel blocks by zigzag scanning.
7
Hiding bitmap files
c v i
in – namely from 0 to (k-1) c i
Thus,the definition of sign is as follows:
8
The hiding process of BRL is formulated as follows:
The extraction scheme is as follows:
9
Example:k=5, hiding secret bits:111000001111
111000001111 315041
RLE
(3,1) (5,0) (4,1)
(V
1
, C
1
) = (12, 8), (V
2
, C
2
) = (2, 3), (V
3
, C
3
) = (240, 254).
[LSB match]
1.
[LSB replace]
2.
c v
'
12-> 1 =12+1=13
( v
1
'
, c
1
'
)
( 13 , 7 ), ( v
2
'
, c
2
'
)
( 2 , 4 ), ( v
3
'
, c
3
'
)
( 241 , 253 ).
10
Hiding general data files
c
S n i v i and the value of is the sequential order of
C
N ( i )
The following mapping function f, where
C is set to be zero if n is smaller than k :
N i
( i )
11
k v v
12
Example:
( 101001 ) the pair of original pixels (43, 58).
1.
2.
( 101001 k
v
' i
)
2 mod
( n three
1 )
1'
3 s
v
' i k
mod
3 (
7
共
C v
' i
3
6
種組合
45
3.
N(1)=1,N(2)=1,N(3)=2,N(4)=2,N(5)=3
) f ( 101001 )
i
6
1
1 b i
C
N i
( i )
0
C
1
1
0
C
1
2
1
C
2
3
0
C
2
4
1
C
3
5
13
4.
C i
' mod C
3
6
13
C i
'
13 , 33 , 53
C i
'
53
13
The extraction process of (45,53) and n=6
1.
2.
v i
' c
' i
3.
S
5 s
0
:s
5
s
45 ,
53 n
6
num k
3 ( i .
e
13 ( 53
45 mod mod C
7 )
6
)
S
4
S
3
S
2
S
1
3
S
0
5
=C(5,3)=10<13
’1’ num
=13-10=3 s
0
:s
4 s
4
=C(4,2)=6>3
’0’ s
0
: s
3 s
3
=C(3,2)=3 ≦ 3 ’1’ num = 3-3 = 0 s
0
:s
2 s
2
=‘0’ ; s
0
:s
1 s
1
=‘0’, s
0
=‘1’
14
15
16
Comparison of PSNR and capacities using
Lena as the cover image.
17
Comparison of PSNR and capacities using
Baboon as the cover image.
18
No need to refer to the original image during the extraction process.
Probably be extended to embedding secret data in compressed images using VQ or JPEG techniques.
19