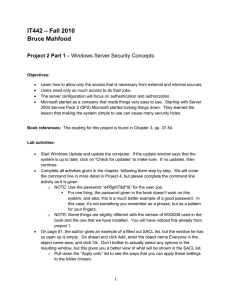
– Fall 2010 IT442 Bruce Mahfood Project 2 Part 2

IT442 – Fall 2010
Bruce Mahfood
Project 2 Part 2 – Windows Server Security Concepts
Objectives:
Learn how to allow only the access that is necessary from external and internal sources.
Users need only so much access to do their jobs.
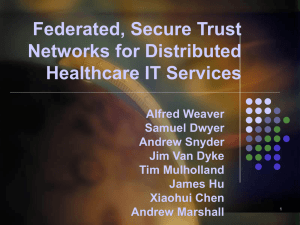
The server configuration will focus on authentication and authorization.
Microsoft started as a company that made things very easy to use. Starting with Server
2003 Service Pack 2 (SP2) Microsoft started locking things down. They learned the lesson that making the system simple to use can cause many security holes.
Book references: The reading for this project is found in Chapter 3, pp. 37-54.
Written Assignment – Part 2:
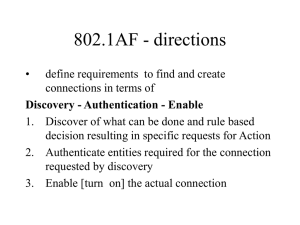
1) (25 points) Answer the following about authentication and authorization: a. What is the difference between the two practices? b. Why is it necessary to have both of these practices implemented on a serverlevel computer? c. What would happen if the server was only set to authenticate users? d. Is it possible to remove authentication and still have authorization services on a server? If so, how, and what would be the difference in how it functioned. If not so, why? e. In your own words, give a definition for biometric authentication, and say whether its use for server login would make a system more secure. If so, how? If not, why?
2) (10 points) Every time a client asks for data from a Windows 2003 / 2008 server, the server makes sure it is sending that data to an authenticated client. What does Kerberos do that makes it possible for such a client to securely receive data without sending a password over the internet for each call? Why does this ensure that the data access is secure?
3) (15 points) What is a SAM file on a Windows server? What type of file is it (which is a different question from asking what it is)? What two methods, other than the original definition of hashing, does Windows employ to make sure that SAM is a very secured file on the system?
1