Security Issues in Technology
advertisement

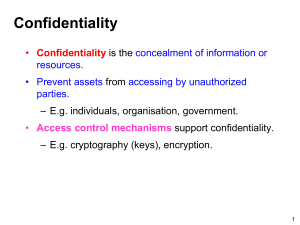
Security Myths about Business Risks in the Information Age Security is only about protecting “things” We don’t have any information anyone would want Security problems have never happened here. Firewalls provide enough security Technology will solve the security problem The “enemy” is outside Our people won’t tolerate tight security My PC is secure, so I’m secure The Internet can’t be used for secure communications The Economist and Arthur Andersen SECURITY: Deter Detect Minimize Investigate Recover Security Risks Internal External Accidental Destruction Alteration Access Intentional Threats Disaster and breakdowns Access and disclosure Alteration or destruction Improper use RISK ASSESSMENT P1 P2 L Probability of attack Probability of success Cost of Loss Expected Loss = P1 * P2 * L Minimize Threat Categories Security Policy Security is always a cost to efficiency. It must be promoted to be effective. From the top Before installing hardware Politically charged Writing a Security Policy Assess the types of risks Identify vulnerabilities Analyze user needs Write the policy Develop change procedures Plan implementation Implement Risk Areas Personnel Risk Background checks Segregation of duties Terminated employees Physical Access Risk Disaster Risk Disaster Recovery Backup/hot sites Integrity Risk Access Risk Availability Risk Infrastructure Capability Denial of service Integrity Risk Risks associated with the authorization, completeness and accuracy of transactions User interface Processing Error Processing Interfaces with other systems/databases Change Management Data Privacy Backup Access Risk Risks associated with inappropriate access to systems or data Identification, authentication and nonrepudiation What you know, what you have, what you are Encryption (algorithm and key) Secret key, private/public key smart cards, hardware tokens Digital Signature (hashing and public key; encrypt with private key, send with private key, and then decode with public key) Certification authority and digital certificates Security Protocols Firewalls and Guards Elements of Risk Asset Threat Access Administrative Controls: Limit the Threat Standards, rules, procedures and discipline to assure that personnel abide by established policies. Includes segregation of functions. Administrative Controls Security organization Audits Risk assessment Administrative standards and procedures Protecting the Assets Resource management Disaster recovery System segregation Resource Management Backup planning Job scheduling Redundant design Selective decoupling Disaster Management Redundancy and fault tolerant systems Backups and off site storage Hot and cold sites Planning and procedures Elements of Risk Asset Threat Access Vulnerabilities Servers Securing operating systems and applications Networks Access protection from snooping, attacks, spoofing Clients and modems User verification for PCAnywhere etc. Viruses Operating Systems UNIX Novell Netware Windows and Windows NT Secure Operating Systems U.S. Government Certification A1, B1, B2, B3, C1, C2 (most commercial systems), D Ease of use CERT (Computer Emergency Response Team) www.cert.org Top 12 SecurityRisks 1. Hosts run unnecessary services 3. Information leakage through network service programs 4. Misuse of trusted access 5. Misconfigured firewall access lists 7. Misconfigured web servers 10.Inadequate logging, monitoring or detecting Top 12 Security Risks 2. Unpatched, outdated or default configured software 6. Weak Passwords 8.Improperly exported file sharing services 9. Misconfigured or unpatched Windows NT servers 11.Unsecured remote access 12.Lack of comprehensive policies and standards Tools Firewalls Network partitioning and routers Encryption Testing tools Consultants Firewall functions Packet Filter: Blocks traffic based on IP address and/or port numbers. Proxy Server: Serves as a relay between two networks, breaking the connection between the two. Network Address Translation (NAT): Hides the IP addresses of client stations in an internal network by presenting one IP address to the outside world. Stateful Inspection: Tracks the transaction in order to verify that the destination of an inbound packet matches the source of a previous outbound request. Generally can examine multiple layers of the protocol stack. Firewall Operation Firewall Operation 1. A router sits between two networks 2. A programmer writes an access control list, which contains IP addresses that can be allowed onto the network. 3. A message gets sent to the router. It checks the address against the access control list. If address the is on the list, it can go through. 4. If the address isn't on the list, the message is denied access to the network. Encryption Keys and key length Public key/private key Processing problems Location Application Network Firewall Link Encryption Techniques How Public Encryption Works 1. Sue wants to send a message to Sam, so she finds his public key in a directory. 2. Sue uses the public key to encrypt the message and send it to Sam. 3. When the encrypted message arrives, Sam uses his private key to decrypt the data and read Sue's message. Encryption at the Firewall Authentication Passwords “Credit” cards Biometrics Isolation Remote location verification Biometrics: how it works Users "enroll" by having their fingerprints, irises, faces, signatures or voice prints scanned. Key features are extracted and converted to unique templates, which are stored as encrypted numerical data. Corresponding features presented by a would-be user are compared to the templates in the database. Matches will rarely be perfect, and the owners of the system can vary a sensitivity threshhold so as to minimize either the rate of false rejections, which annoy users, or false acceptances, which jeopardize security. This offers far more flexibility than the binary "Yes" or "No" answers given by password technologies. Common biometric techniques and how they rate INTRUSIVNESS EFFORT Dynamic signature Excellent verification Good Face geometry Fair Finger scan ACCURACY COST Fair Fair Excellent Good Good Fair Good Good Good Hand geometry Passive iris scan Fair Poor Good Excellent Fair Excellent Fair Poor Retina scan Voice print Poor Very good Poor Poor Very Good Fair Fair Very Good International Biometric Group, New York as reported in Computerworld, Quick Study: Biometrics, 10/12/98 Security