Model-Driven Verifying Compilation of Synchronous Distributed Applications Sagar Chaki, James Edmondson
advertisement

Model-Driven Verifying
Compilation of Synchronous
Distributed Applications
Sagar Chaki, James Edmondson
October 1, 2014
MODELS’14, Valencia, Spain
© 2014 Carnegie Mellon University
Copyright 2014 Carnegie Mellon University
This material is based upon work funded and supported by the Department of Defense under
Contract No. FA8721-05-C-0003 with Carnegie Mellon University for the operation of the Software
Engineering Institute, a federally funded research and development center.
Any opinions, findings and conclusions or recommendations expressed in this material are those of
the author(s) and do not necessarily reflect the views of the United States Department of Defense.
NO WARRANTY. THIS CARNEGIE MELLON UNIVERSITY AND SOFTWARE ENGINEERING INSTITUTE
MATERIAL IS FURNISHED ON AN “AS-IS” BASIS. CARNEGIE MELLON UNIVERSITY MAKES NO
WARRANTIES OF ANY KIND, EITHER EXPRESSED OR IMPLIED, AS TO ANY MATTER INCLUDING,
BUT NOT LIMITED TO, WARRANTY OF FITNESS FOR PURPOSE OR MERCHANTABILITY,
EXCLUSIVITY, OR RESULTS OBTAINED FROM USE OF THE MATERIAL. CARNEGIE MELLON
UNIVERSITY DOES NOT MAKE ANY WARRANTY OF ANY KIND WITH RESPECT TO FREEDOM FROM
PATENT, TRADEMARK, OR COPYRIGHT INFRINGEMENT.
This material has been approved for public release and unlimited distribution except as restricted
below.
This material may be reproduced in its entirety, without modification, and freely distributed in written
or electronic form without requesting formal permission. Permission is required for any other use.
Requests for permission should be directed to the Software Engineering Institute at
permission@sei.cmu.edu.
DM-0001691
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
2
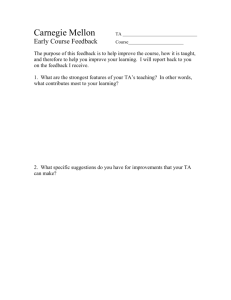
Outline
•
Motivation
•
Approach
•
Sequentialization : SEQSEM & SEQDBL
•
Examples
•
Experimental Results
•
Synchronizer Protocol : 2BSYNC
•
Tool Overview & Demo
•
Future Work
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
3
Motivation
Distributed algorithms have always been important
•
File Systems, Resource Allocation, Internet, …
Increasingly becoming safety-critical
•
Robotic, transportation, energy, medical
Prove correctness of distributed algorithm
implementations
•
•
Pseudo-code is verified manually (semantic gap)
Implementations are heavily tested (low coverage)
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
4
Approach : Verification + Code Generation
Program in Domain Specific Language
Distributed
Application
Debug Application,
Refine Specification
Safety
Specification
Verification
Failure
Success
The Verifying Compiler:
A Grand Challenge for
computing research
Code
Generation
Tony Hoare
Binary
Run on Physical
Device
Run within
simulator
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
5
Verification
Model Checking
Program in Domain Specific Language
Distributed
Application
Safety
Specification
Automatic verification technique for finite
state concurrent systems.
•
Sequentialization
•
Assume
Synchronous
Model of
Computation
Single-Threaded
C Program
Specifications are written in propositional
temporal logic. (Pnueli 77)
•
Software Model Checking
(CBMC, BLAST etc.)
Failure
Developed independently by Clarke and
Emerson and by Queille and Sifakis in
early 1980’s.
ACM Turing Award 2007
Success
Computation Tree Logic (CTL), Linear
Temporal Logic (LTL), …
Verification procedure is an intelligent
exhaustive search of the state space of
the design
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
6
Code Generation
MADARA Middleware
Program in Domain Specific Language
Distributed
Application
Safety
Specification
A database of facts: 𝐷𝐵 = 𝑉𝑎𝑟 ↦
𝑉𝑎𝑙𝑢𝑒
Node 𝑖 has a local copy: 𝐷𝐵𝑖
•
update 𝐷𝐵𝑖 arbitrarily
•
publish new variable mappings
Add synchronizer protocol
Guarantee
Synchronous
Model of
Computation
•
Immediate or delayed
•
Multiple variable mappings
transmitted atomically
Implicit “receive” thread on each node
C++/MADARA Program
Compile
(g++,clang,MSVC, etc.)
Binary
•
Receives and processes variable
updates from other nodes
•
Updates ordered via Lamport
clocks
Portable to different OSes (Windows,
Linux, Android etc.) and networking
technology (TCP/IP, UDP, DDS etc.)
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
7
Synchronous Distributed Application (SDA)
Node 𝟎 = 𝒇𝟎 ()
Shared Variables:𝑮𝑽 = 𝑮𝑽 𝟎 , 𝑮𝑽[𝟏]
Node 𝟏 = 𝒇𝟏 ()
𝑮𝑽𝟎
𝑹𝒐𝒖𝒏𝒅 𝟏
𝑮𝑽𝟏 𝟏 = 𝒇𝟏 (𝑮𝑽𝟎 )
𝑮𝑽𝟏 [𝟎] = 𝒇𝟎 𝑮𝑽𝟎
𝑮𝑽𝟏
𝑹𝒐𝒖𝒏𝒅 𝟐
𝑮𝑽𝟐 𝟏 = 𝒇𝟏 (𝑮𝑽𝟏 )
𝑮𝑽𝟐 [𝟎] = 𝒇𝟎 𝑮𝑽𝟏
𝑮𝑽𝟐
𝑮𝑽𝒊−𝟏
𝑹𝒐𝒖𝒏𝒅 𝒊
𝑮𝑽𝒊 𝟏 = 𝒇𝟏 (𝑮𝑽𝒊−𝟏 )
𝑮𝑽𝒊 [𝟎] = 𝒇𝟎 𝑮𝑽𝒊−𝟏
𝑮𝑽𝒊
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
8
SDA Verification
Program with 𝑛 nodes : 𝑃(𝑛)
•
•
•
Each node has a distinct 𝑖𝑑 ∈ 1, 𝑛
Array 𝐺𝑉 has 𝑛 elements, 𝐺𝑉[𝑖] writable only by node with id 𝑖
Each element of 𝐺𝑉 is drawn from a finite domain
In each round, node with id 𝑖𝑑 executes function 𝜌 whose body is a statement
𝑠𝑡𝑚𝑡 ≔ 𝑠𝑘𝑖𝑝 | 𝑙𝑣𝑎𝑙 = 𝑒𝑥𝑝
(𝑎𝑠𝑠𝑖𝑔𝑛𝑚𝑒𝑛𝑡)
| 𝐼𝑇𝐸 𝑒𝑥𝑝, 𝑠𝑡𝑚𝑡, 𝑠𝑡𝑚𝑡
(𝑖𝑓, 𝑡ℎ𝑒𝑛, 𝑒𝑙𝑠𝑒)
| 𝐴𝐿𝐿 𝐼𝑉, 𝑠𝑡𝑚𝑡
(𝑖𝑡𝑒𝑟𝑎𝑡𝑒 𝑜𝑣𝑒𝑟 𝑛𝑜𝑑𝑒𝑠 ∶ 𝑢𝑠𝑒 𝑡𝑜 𝑐ℎ𝑒𝑐𝑘 𝑒𝑥𝑖𝑠𝑡𝑒𝑛𝑐𝑒)
| 𝑠𝑡𝑚𝑡 +
(𝑖𝑡𝑒𝑟𝑎𝑡𝑖𝑜𝑛 𝑜𝑓 𝑠𝑡𝑎𝑡𝑒𝑚𝑒𝑛𝑡𝑠)
𝑙𝑣𝑎𝑙 ≔ 𝐺𝑉 𝑖𝑑 𝑤
(𝑙𝑣𝑎𝑙𝑢𝑒𝑠)
𝑒𝑥𝑝 ≔ ⊤ ⊥ 𝑙𝑣𝑎𝑙 𝐺𝑉 𝑖𝑣 𝑤 𝑖𝑑 𝐼𝑉 ⋄ (𝑒𝑥𝑝+ )
(𝑒𝑥𝑝𝑟𝑒𝑠𝑠𝑖𝑜𝑛𝑠)
Initial states and “ERROR” states of the program are define
•
State ≡ value assigned to all variables
Verification ≡ decide if there is an execution of the program that starts in an initial
state and ends in an ERROR state
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
9
Semantic Sequentialization: SEQSEM
Node 𝟎 = 𝒇𝟎 ()
Shared Variables:𝑮𝑽 = 𝑮𝑽 𝟎 , 𝑮𝑽[𝟏]
𝑨𝒔𝒔𝒖𝒎𝒆 𝒏 𝒏𝒐𝒅𝒆𝒔
𝑼𝒔𝒆 𝒏 𝒄𝒐𝒑𝒊𝒆𝒔 𝒐𝒇 𝑮𝑽
𝑶 𝒏𝟐
𝒗𝒂𝒓𝒊𝒂𝒃𝒍𝒆𝒔 ⇒
𝑺𝒕𝒂𝒕𝒆 𝑬𝒙𝒑𝒍𝒐𝒔𝒊𝒐𝒏
𝑹𝒐𝒖𝒏𝒅 𝟏
Node 𝟏 = 𝒇𝟏 ()
𝑮𝑽𝟎
𝑮𝑽𝟏
𝑮𝑽𝒏−𝟏
𝑮𝑽𝟎 𝟎 =
𝒇𝟎 𝑮𝑽𝟎
𝑮𝑽𝟏 𝟏 =
𝒇𝟏 (𝑮𝑽𝟏 )
𝑮𝑽𝒏−𝟏 𝒏 − 𝟏 =
𝒇𝒏−𝟏 (𝑮𝑽𝒏−𝟏 )
𝑮𝑽𝟎 𝒊 =
𝑮𝑽𝒊 𝒊 ,
𝒊≠𝟎
𝑮𝑽𝟏 𝒊 =
𝑮𝑽𝒊 𝒊 ,
𝒊≠𝟏
𝑮𝑽𝒏−𝟏 𝒊 =
𝑮𝑽𝒊 𝒊 ,
𝒊≠𝒏−𝟏
𝑮𝑽𝟎
𝑮𝑽𝟏
𝑮𝑽𝒏−𝟏
𝑶𝒑𝒆𝒓𝒂𝒕𝒊𝒐𝒏𝒔 𝒉𝒂𝒗𝒆 𝒊𝒏𝒅𝒆𝒑𝒆𝒏𝒅𝒆𝒏𝒄𝒆 ⇒ 𝒓𝒆𝒐𝒓𝒅𝒆𝒓𝒆𝒅 𝒔𝒆𝒒𝒖𝒆𝒏𝒕𝒊𝒂𝒍𝒍𝒚.
Sagar Chaki, October 1, 2014
𝑹𝒐𝒖𝒏𝒅𝒔 𝒂𝒓𝒆 𝒓𝒆𝒑𝒆𝒂𝒕𝒆𝒅 𝒊𝒏 𝒂 𝒍𝒐𝒐𝒑.
Model-Driven Verifying Compilation
© 2014 Carnegie Mellon University
10
Double Buffering Sequentialization: SEQDBL
Node 𝟎 = 𝒇𝟎 ()
Shared Variables:𝑮𝑽 = 𝑮𝑽 𝟎 , 𝑮𝑽[𝟏]
𝑼𝒔𝒆 𝟐 𝒄𝒐𝒑𝒊𝒆𝒔 𝒐𝒇 𝑮𝑽
𝑼𝒔𝒆 𝒆𝒂𝒄𝒉 𝒄𝒐𝒑𝒚 𝒂𝒔 𝒊𝒏𝒑𝒖𝒕
𝒊𝒏 𝒂𝒍𝒕𝒆𝒓𝒏𝒂𝒕𝒆 𝒓𝒐𝒖𝒏𝒅𝒔
𝑹𝒐𝒖𝒏𝒅 𝟏
𝑮𝑽𝟎
𝑮𝑽𝟏 𝟎 =
𝒇𝟎 𝑮𝑽𝟎
𝑶 𝒏
𝒗𝒂𝒓𝒊𝒂𝒃𝒍𝒆𝒔
𝑹𝒐𝒖𝒏𝒅 𝟐
Node 𝟏 = 𝒇𝟏 ()
𝑮𝑽𝟏 𝟏 =
𝒇𝟏 (𝑮𝑽𝟎 )
𝑮𝑽𝟏 𝒏 − 𝟏 =
𝒇𝒏−𝟏 (𝑮𝑽𝟎 )
𝑮𝑽𝟏
𝑮𝑽𝟎 𝟎 =
𝒇𝟎 𝑮𝑽𝟏
𝑮𝑽𝟎 𝟏 =
𝒇𝟏 (𝑮𝑽𝟏 )
𝑮𝑽𝟎 𝒏 − 𝟏 =
𝒇𝒏−𝟏 (𝑮𝑽𝟏 )
𝑮𝑽𝟎
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
11
Example: 2D Synchronous Collision Avoidance
(3,3)
Y
(0,3)
Reserve
Reserve
(0,0)
Reserve
(3,0)
X
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
12
Example: 2D Synchronous Collision Avoidance
(3,3)
Y
(0,3)
Reserve
Reserve
Reserve
(0,0)
(3,0)
X
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
13
Example: 2D Synchronous Collision Avoidance
(0,3)
(3,3)
Y
Reservation
Contention
Resolved based
on Node ID. No
collision
possible if no
over-booking.
Potential
Collision
(0,0)
(3,0)
X
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
14
2D Collision Avoidance Protocol
If time to move to
next coordinate
REQUEST
NEXT
If no other node is
locking the next
coordinate
WAITING
Reached the next
coordinate
MOVE
Moving to the
next coordinate
If no other node
“with higher id” is
trying to lock the
next coordinate
𝑶𝒕𝒉𝒆𝒓 𝑬𝒙𝒂𝒎𝒑𝒍𝒆𝒔
3D Collision Avoidance
Model-Driven Verifying Compilation
Sagar Chaki, October
1, 2014
Mutual
Exclusion
© 2014 Carnegie Mellon University
15
Results: 3D Collision Avoidance
SEQDBL
is better
𝑻𝑺 , 𝑻𝑫 = 𝒎𝒐𝒅𝒆𝒍 𝒄𝒉𝒆𝒄𝒌𝒊𝒏𝒈 𝒕𝒊𝒎𝒆 𝒘𝒊𝒕𝒉 𝑺𝑬𝑸𝑺𝑬𝑴, 𝑺𝑬𝑸𝑫𝑩𝑳
𝑻𝑺
𝝁, 𝝈 = 𝑨𝒗𝒈, 𝑺𝒕𝑫𝒆𝒗 𝒐𝒇
𝑻𝑫
Model-Driven Verifying Compilation
Sagar
Chaki,𝒔𝒊𝒛𝒆
October 1, 2014
𝒏 = #𝒐𝒇 𝒏𝒐𝒅𝒆𝒔 𝑹 = #𝒐𝒇 𝒓𝒐𝒖𝒏𝒅𝒔
𝑮×𝑮 =
𝒈𝒓𝒊𝒅
© 2014 Carnegie Mellon University
16
Results: 2D Collision Avoidance
Depends
on the
example
𝑻𝑺 , 𝑻𝑫 = 𝒎𝒐𝒅𝒆𝒍 𝒄𝒉𝒆𝒄𝒌𝒊𝒏𝒈 𝒕𝒊𝒎𝒆 𝒘𝒊𝒕𝒉 𝑺𝑬𝑸𝑺𝑬𝑴, 𝑺𝑬𝑸𝑫𝑩𝑳
𝑻𝑺
𝝁, 𝝈 = 𝑨𝒗𝒈, 𝑺𝒕𝑫𝒆𝒗 𝒐𝒇
𝑻𝑫
Model-Driven Verifying Compilation
Sagar
Chaki,𝒔𝒊𝒛𝒆
October 1, 2014
𝒏 = #𝒐𝒇 𝒏𝒐𝒅𝒆𝒔 𝑹 = #𝒐𝒇 𝒓𝒐𝒖𝒏𝒅𝒔
𝑮×𝑮 =
𝒈𝒓𝒊𝒅
© 2014 Carnegie Mellon University
17
Results: Mutual Exclusion
SEQSEM
and
SEQDBL
similar
𝑻𝑺 , 𝑻𝑫 = 𝒎𝒐𝒅𝒆𝒍 𝒄𝒉𝒆𝒄𝒌𝒊𝒏𝒈 𝒕𝒊𝒎𝒆 𝒘𝒊𝒕𝒉 𝑺𝑬𝑸𝑺𝑬𝑴, 𝑺𝑬𝑸𝑫𝑩𝑳
𝑻𝑺
𝝁, 𝝈 = 𝑨𝒗𝒈, 𝑺𝒕𝑫𝒆𝒗 𝒐𝒇
𝑻𝑫
Model-Driven Verifying Compilation
Sagar
Chaki,𝒔𝒊𝒛𝒆
October 1, 2014
𝒏 = #𝒐𝒇 𝒏𝒐𝒅𝒆𝒔 𝑹 = #𝒐𝒇 𝒓𝒐𝒖𝒏𝒅𝒔
𝑮×𝑮 =
𝒈𝒓𝒊𝒅
© 2014 Carnegie Mellon University
18
Synchronizer Protocol: 2BSYNC
Node 𝟎 = 𝒇𝟎 ()
Shared Variables:𝑮𝑽 = 𝑮𝑽 𝟎 , 𝑮𝑽[𝟏]
𝑼𝒔𝒆 𝒃𝒂𝒓𝒓𝒊𝒆𝒓
𝒗𝒂𝒓𝒊𝒂𝒃𝒍𝒆𝒔: 𝒃𝟎 , 𝒃𝟏
𝑰𝒏𝒊𝒕𝒊𝒂𝒍𝒊𝒛𝒆𝒅 𝒕𝒐 𝟎
Atomic Send. Either
both 𝑮𝑽𝟎 [𝟎] and 𝒃𝟎 are
received, or none is
received. Can be
implemented on existing
network stack, e.g.,
TPC/IP
Node 𝟏 = 𝒇𝟏 ()
𝑮𝑽𝟎 , 𝒃𝟎
𝑮𝑽𝟏 , 𝒃𝟏
𝒃𝟎 ≔ 𝒃𝟎 + 𝟏
𝒃𝟎 !
𝑩𝒂𝒓𝒓𝟎
𝒃𝟏 ≔ 𝒃𝟏 + 𝟏
𝒃𝟏 !
𝑩𝒂𝒓𝒓𝟏
𝑮𝑽𝟎 𝟎 = 𝒇𝟎 𝑮𝑽𝟎
𝑮𝑽𝟏 𝟏 = 𝒇𝟏 (𝑮𝑽𝟏 )
𝒃𝟎 ≔ 𝒃𝟎 + 𝟏
𝑮𝑽𝟎 𝟎 , 𝒃𝟎 !
𝑩𝒂𝒓𝒓𝟎
𝑩𝒂𝒓𝒓𝟎 ≡ 𝒘𝒉𝒊𝒍𝒆 𝒃𝟏 < 𝒃𝟎 𝒔𝒌𝒊𝒑;
Implicit thread receiving messages and
updating variables
𝒃𝟏 ≔ 𝒃𝟏 + 𝟏
𝑮𝑽𝟏 𝟏 , 𝒃𝟏 !
𝑩𝒂𝒓𝒓𝟏
𝑷𝒓𝒐𝒐𝒇 𝒐𝒇 𝒄𝒐𝒓𝒓𝒆𝒄𝒕𝒏𝒆𝒔𝒔
19
𝒊𝒏 𝒑𝒂𝒑𝒆𝒓
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
Tool Overview
Project webpage (http://mcda.googlecode.com)
•
Tutorial (https://code.google.com/p/mcda/wiki/Tutorial)
Verification
•
•
daslc --nodes 3 --seq --rounds 3 --seq-dbl --out tutorial-02.c tutorial02.dasl
cbmc tutorial-02.c (takes about 10s to verify)
Code generation & simulation
•
•
•
daslc --nodes 3 --madara --vrep --out tutorial-02.cpp tutorial-02.dasl
g++ …
mcda-vrep.sh 3 outdir ./tutorial-02 …
DEMO
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
20
Future Work
Improving scalability and verifying with unbounded number of rounds
Verifying for unbounded number of nodes (parameterized verification)
•
Paper at SPIN’2014 Symposium
Asynchronous and partially synchronous network semantics
Scalable model checking
•
Abstraction, compositionality, symmetry reduction, partial order reduction
Fault-tolerance, uncertainty, …
•
Combine V&V of safety-critical and mission-critical properties
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
21
QUESTIONS?
© 2014 Carnegie Mellon University
Contact Information Slide Format
Sagar Chaki
Principal Researcher
SSD/CSC
Telephone: +1 412-268-1436
Email: chaki@sei.cmu.edu
U.S. Mail
Software Engineering Institute
Customer Relations
4500 Fifth Avenue
Pittsburgh, PA 15213-2612
USA
Web
www.sei.cmu.edu
www.sei.cmu.edu/contact.cfm
Customer Relations
Email: info@sei.cmu.edu
Telephone:
+1 412-268-5800
SEI Phone:
+1 412-268-5800
SEI Fax:
+1 412-268-6257
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
23
Synchronous Collision Avoidance Code
MOC_SYNC;
NODE uav (id)
CONST X = 4; CONST Y = 4;
{
CONST NEXT = 0;
GLOBAL bool lock [X][Y][#N];
CONST REQUEST = 1;
LOCAL int state,x,y,xp,yp,xf,yf;
CONST WAITING = 2;
void NEXT_XY () { … }
CONST MOVE = 3;
void ROUND () {
INIT
{
FORALL_NODE(id)
state.id = NEXT;
//assign x.id and y.id non-deterministically
//assume they are within the correct range
//assign lock[x.id][y.id][id] appropriately
if(state == NEXT) { …
EXTERN int
state = REQUEST;
MOVE_TO (unsigned char x,
unsigned char y);
state = MOVE;
} else if(state == MOVE) { …
void INIT () { … }
FORALL_DISTINCT_NODE_PAIR (id1,id2)
state = WAITING;
} else if(state == WAITING) { …
NODE uav (id) { … }
//nodes don’t collide initially
} else if(state == REQUEST) { …
state = NEXT;
ASSUME(x.id1 != x.id2 || y.id1 != y.id2);
}
SAFETY {
FORALL_DISTINCT_NODE_PAIR (id1,id2)
}}}
void SAFETY { … }
ASSERT(x.id1 != x.id2 || y.id1 != y.id2);
}
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
24
Synchronous Collision Avoidance Code
if(state == NEXT) {
//compute next point on route
else if(state == MOVE) {
if(x == xf && y == yf) return;
//now we have the lock on (xp,yp)
NEXT_XY();
if(MOVE_TO()) return;
state = REQUEST;
lock[x ][y][id] = 0;
} else if(state == REQUEST) {
x = xp; y = yp;
//request the lock but only if it is free
if(EXISTS_OTHER(idp,lock[xp][yp][idp] != 0)) return;
state = NEXT;
}
lock[xp][yp][id] = 1;
state = WAITING;
} else if(state == WAITING) {
//grab the lock if we are the highest
//id node to request or hold the lock
if(EXISTS_HIGHER(idp, lock[xp][yp][idp] != 0)) return;
state = MOVE;
}
Model-Driven Verifying Compilation
Sagar Chaki, October 1, 2014
© 2014 Carnegie Mellon University
25