IDS and IPS - Catatan Hasdi Putra

Network Intrusion Detection
Systems
MM Clements
A Adekunle
Lecture Overview
• Taxonomy of intrusion detection system
• Promiscuous & Inline Mode Protection: IDS, IPS
• IDS and IPS Deployment Considerations & example
• Cisco IDS family
• Snort
• IDS/IPS Vulnerabilities
• How to protect IDS?
• Unified Threat Management (UTM)
• Summary
Engineering and Management of Secure Computer Networks 2
Intrusion Detection
• Detection and protection from attacks against networks
• Three types of network attacks
– Reconnaissance
– Access
– Denial of service
Engineering and Management of Secure Computer Networks 3
Intrusion detection system (IDS)
• An Intrusion detection system (IDS) is software or hardware designed to monitor, analyze and respond to events occurring in a computer system or network for signs of possible incidents of violation in security policies.
– These incidents of violations can be unwanted attempts to access, manipulate or disable computer systems, mainly via a network, such as the Internet.
Engineering and Management of Secure Computer Networks 4
Classification of Intrusion Detection
• Profile or Anomaly based intrusion detection
– Monitors network traffic and compares it against an established baseline for normal use
• Bandwidth, protocols, ports and devices generally connecting to each other
– Alerts the administrator or user when traffic is detected which is anomalous, or significantly different, than the baseline.
– Example: Snort Spade plug-in
– Prone to high number of false-positives
Engineering and Management of Secure Computer Networks 5
Classification of Intrusion Detection
• Signature based intrusion detection
– Also known as Misuse Detection
• A signature based IDS will monitor packets on the network and compare them against a database of signatures or attributes from known malicious threats.
• Similar to the way most antivirus software detects malware.
– Examples: Cisco Sensors 4200 series, Snort
– Less prone to false positives
– Unable to detect zero-day threats whose signatures are not available
Engineering and Management of Secure Computer Networks 6
Signature based intrusion detection
• Signatures
– A set of patterns pertaining to typical intrusion activity that, when matched, generate an alarm
• Signature Types
– Atomic—Trigger contained in a single packet
• Example: Looking for the pattern “/etc/passwd “in the traffic
– Composite—Trigger contained in a series of multiple packets
Engineering and Management of Secure Computer Networks 7
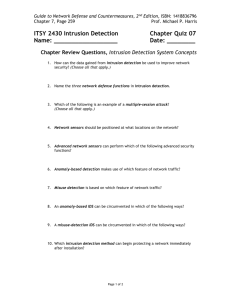
Types of Intrusion Detection Systems
• Host based intrusion detection Systems
– Software (Agents) installed on computers to monitor input and output packets from device
– It performs log analysis, file integrity checking, policy monitoring, rootkit detection, real-time alerting and active response.
– Examples:
• Cisco Security Agent (CSA) , OSSEC, Tripwire
Engineering and Management of Secure Computer Networks 8
Host-Based Intrusion Detection
Corporate network
Agent Agent
Agent Agent Agent Agent
Agent
WWW server
Firewall
Untrusted network
Agent
DNS server
Engineering and Management of Secure Computer Networks 9
Types of Intrusion Detection Systems
• Network-Based Intrusion Detection Systems
– Connected to network segments respond to network traffic.
to monitor, analyze and
– A single IDS sensor can monitor many hosts
– NIDS sensors are available in two formats
• Appliance: It consists of specialized hardware sensor and its dedicated software. The hardware consists of specialized NIC’s, processors and hard disks to efficiently capture traffic and perform analysis.
– Examples: Cisco IDS 4200 series, IBM Real Secure Network
• Software: Sensor software installed on server and placed in network to monitor network traffic.
– Examples: Snort, Bro, Untangle
Engineering and Management of Secure Computer Networks 10
Network-Based Intrusion Detection
Corporate network
Sensor
Sensor
Firewall
Untrusted network
Management
System
WWW server
DNS server
Engineering and Management of Secure Computer Networks 11
Sensor Appliance Interfaces
Untrusted
Network
Monitoring Interface
Router
Switch
Router Sensor
Protected
Network
Command and
Control Interface
Management System
Engineering and Management of Secure Computer Networks
12
Promiscuous-Mode Protection: IDS
1
A network device sends copies of packets to the sensor for analysis.
2
If the traffic matches a signature, the signature fires.
Switched Port Analyzer (SPAN )
Switch
3 2
The sensor can send an alarm to a management console and take a response action such as resetting the connection.
Management
System
Engineering and Management of Secure Computer Networks
Sensor
Target
13
Inline-Mode Protection: IPS
The sensor resides in the data forwarding path.
Sensor
An alert can be sent to the management console.
Management
System
Engineering and Management of Secure Computer Networks
Target
If a packet triggers a signature, it can be dropped before it reaches its target.
14
IDS and IPS Deployment Considerations
– Deploy an IDS sensor in areas where you cannot deploy an inline device or where you do not plan to use deny actions.
– Deploy an IPS sensor in those areas where you need and plan to use deny actions.
Engineering and Management of Secure Computer Networks 15
IDS and IPS Deployment Comparison
Inside
Attacker
Internet
Sensor on Outside:
• Sees all traffic destined for your network
• Has high probability of raising false alarms (false positives)
• Does not detect internal attacks
Engineering and Management of Secure Computer Networks
Sensor on Inside:
• Sees only traffic permitted by firewall
• Has lower probability of false alarms (false positives)
• Requires immediate response to alarms
16
Network based IDS and IPS Deployment
Corporate
Network
Management
Server
Switch
IPS Sensor
Switch
Firewall
Router
IDS
Sensor
Switch
Engineering and Management of Secure Computer Networks
WWW
Server
DNS
Server
DMZ
Untrusted
Network
17
IDS and IPS deployment example in an
Enterprise Network
Branch
Corporate
Network
NM-CIDS
Router Firewall
Untrusted
Network
Sensor
Management
Server
Engineering and Management of Secure Computer Networks
Sensor
DMZ
Agent
WWW
Server
Agent
DNS
Server
18
Cisco IDS Family
600
250
IDSM-2
IDS 4255
200
IPS 4240
80
AIP-SSM
45
NM-CIDS
10/100/1000 TX
IPS 4215
10/100 TX 10/100/1000 TX
10/100/1000 TX
1000 SX
Network Media
10/100/1000 TX
Switched/1000
Snort
• Open source, freely available software except for rules
• Installed as dedicated server on Windows and Linux,
Solaris operating systems
• Placed as network sensor in a network
• Rules are set of instructions defined to take certain action after matching some sort of signatures (atomic or composite)
• Example:
• alert tcp $HOME_NET any -> $EXTERNAL_NET any
(content:"uk.youtube.com”;msg:"someone visited YouTube"; )
Engineering and Management of Secure Computer Networks 20
Snort Modes
• Sniffer Mode
• Used to sniff traffic from network
• Traffic will be captured using libpcap or winpcap.
• Traffic will be captured directly from the sensor .
• Logger Mode
• Simple logging into a file. Two possible formats are Binary and ASCII.
• Logging into a Database (eg. MySQL)
• Can be used for creating the normal traffic profile
• Intrusion Detection / Prevention
• The rules will be used in this mode of snort to detect unwanted activity
Engineering and Management of Secure Computer Networks 21
IDS/IPS Vulnerabilities
• Cisco IPS Packet Handling DoS -
• In July 2006, a DoS vulnerability was discovered on Cisco
IPS 4200 series models which were running version 5.1
software.
• Snort Rule Matching Backtrack DoS -
• Snort versions 1.8 through 2.6 had a DoS vulnerability , found on January 11, 2007 which can exploit Snort's rule matching algorithm by using a crafted packet. This could cause the algorithm to slow down to the point where detection may become unavailable. Snort was quick to release version 2.6.1 which corrected this issue.
Engineering and Management of Secure Computer Networks 22
How to protect IDS?
• Don't run any service on your IDS sensor.
• The platform on which you are running IDS should be patched with the latest releases from your vendor.
• Configure the IDS machine so that it does not respond to ping (ICMP Echo-type) packets.
• User accounts should not be created except those that are absolutely necessary.
Engineering and Management of Secure Computer Networks 23
Unified Threat Management (UTM)
• Unified Threat Management (UTM) is a network device that have many features in one box, including:
– IDS, IPS, Firewall, Spyware, Anti Spam , Anti
Phishing
– Anti Virus, Content (www) Filter, VPN
– Example: Untangle, Watchguard
– Untangle Demo: http://www.untangle.com/video_overview/
Engineering and Management of Secure
Computer Networks
24
Summary
• Intrusion detection system (IDS) is software or hardware designed to monitor, analyze and respond to network traffic .
– Can be classified as Profile or Signature based intrusion detection.
• Signatures can be defined as Atomic or Composite.
– Can be available as Host or Network based Intrusion detection .
– IDS is used as promiscuous mode protection in DMZ
– IPS is used as Inline mode protection for securing internal network
– Cisco 4200 series IDS and IPS sensors offer rich set of features for ISD and IPS
– Snort is an open source, free IDS and can operate in sniff , logging and
Intrusion detection/prevention modes. Snort uses rules to analyze traffic.
– IDS/IPS software can be vulnerable to exploits so run patched version,
and shutdown unnecessary services.
• Unified Threat Management (UTM) is a network device that have many features in one box. E.g, Untangle, Watchguard.
Engineering and Management of Secure Computer Networks 25