it governance - Regional Training Institute,Allahabad
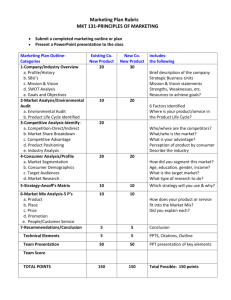
advertisement

COBIT ® By RTI, Allahabad COBIT FRAMEWORK ® OVERVIEW A framework for IT governance focusing on Alignment of IT and business objectives Responsible usage of IT resources Management of IT related risks A framework based on continuous improvement philosophy A generic framework – neither platform nor application specific COBIT FRAMEWORK ® OVERVIEW A framework for use by management, user and auditors The framework consists of 34 IT processes classified into 4 domains 7 information criteria 5 information resources 318 detailed control objectives ranging between 3 to 30 for the 34 IT processes A high level classification of IT processes Planning and organization o Strategy and tactics, and the way IT can best contribute to the achievement of the business objectives ® COBIT FRAMEWORK DOMAINS o Realization of the strategic vision through planning, communicating and managing different perspectives o Organization and technological infrastructure Acquisition and implementation o Identification, development, acquisition and implementation of IT solutions o Integration of IT solutions into business processes ® COBIT FRAMEWORK DOMAINS o Changes in existing systems Delivery and support o Actual delivery of required services including security and continuity aspects o Application controls COBIT FRAMEWORK ® DOMAINS Monitoring o Management's oversight of the organization's control process o Independent assurance provided by internal and external audit or obtained from alternative sources COBIT FRAMEWORK ® INFORMATION CRITERIA Business requirements that IT processes aim to satisfy Effectiveness o Information being relevant and pertinent to the business process o Information being delivered in a timely, correct, consistent and usable manner Efficiency o Provision of information through the optimal (most productive and economical) use of resources COBIT FRAMEWORK ® INFORMATION CRITERIA Confidentiality o Protection of sensitive information from unauthorized disclosure Integrity o Accuracy, completeness, validity in accordance with business values and expectations Availability o Information being available when required o Safeguarding of necessary resources and associated capabilities COBIT FRAMEWORK ® INFORMATION CRITERIA Compliance o Complying with laws, regulations and contractual arrangements i.e., externally imposed business criteria Reliability o Provision of appropriate information for management to operate the entity o Provision of appropriate information for management to exercise its financial and compliance reporting responsibilities COBIT FRAMEWORK ® IT RESOURCES Physical resources that IT processes aim to leverage Data o Objects in their widest sense (i.e., external and internal), structured and nonstructured, graphics, sound, etc. Application Systems o Sum of manual and programmed procedures Technology o Hardware, operating systems, database management systems, networking, multimedia, etc. Facilities ® COBIT FRAMEWORK IT RESOURCES o All the resources to house and support, information systems COBIT FRAMEWORK ® IT RESOURCES People o Staff skills, awareness and productivity to plan, organize, acquire, deliver, support and monitor information systems and services. Planning & Organization PO1 DEFINE STRATEGIC IT PLAN BUSINESS REQUIREMENT An optimum balance is maintained between IT opportunities and business requirement GENERALLY ACCEPTED STANDARD Ensure IT plan is aligned with the mission and business strategies of the organization Establish and apply a structured approach for development of IT long range plan with due consideration of o Existing system assessment Planning & Organization PO1 DEFINE STRATEGIC IT PLAN …GENERALLY ACCEPTED STANDARD o Business environment present and likely over the planning horizon o Available and emerging technologies o Legal and regulatory framework o Business process re-engineering o Outsourcing opportunities Ensure IT long range plan is regularly translated into IT short range plan Planning & Organization PO1 DEFINE STRATEGIC IT PLAN …GENERALLY ACCEPTED STANDARD Define and implement a system for communicating, monitoring, reviewing and changing the long and short range plans Planning & Organization PO2 DEFINE INFORMATION ARCHITECTURE BUSINESS REQUIREMENT Organization of information systems is optimized GENERALLY ACCEPTED STANDARD Define and implement information architecture model incorporating o Corporate data dictionary o Data syntax rules Planning & Organization PO3 DETERMINE TECHNOLOGICAL DIRECTION BUSINESS REQUIREMENT Available and emerging technologies are used to drive and achieve business goals GENERALLY ACCEPTED STANDARD Define and implement technology plan with due consideration of reliability and scalability Monitor future technology trends and factor the same in developing / maintaining technology plan Foster standardization through technology norms Planning & Organization PO4 DEFINE IT ORGANIZATION AND RELATIONSHIP BUSINESS REQUIREMENT Right IT services are delivered GENERALLY ACCEPTED STANDARD Set up a steering committee to oversee IT function Ensure due independence of IT function from user departments without harming optimal coordination Planning & Organization PO4 DEFINE IT ORGANIZATION AND RELATIONSHIP …GENERALLY ACCEPTED STANDARD Define and implement organizational structure ensuring o Clearly defined roles with due consideration of segregation of duties o Specific assignment of responsibilities for quality assurance, logical and physical security, data/system ownership etc., o Required number of competent staff Planning & Organization PO5 MANAGE IT INVESTMENTS BUSINESS REQUIREMENT Disbursement of financial resources is controlled GENERALLY ACCEPTED STANDARD Define and implement budgetary control system commensurate to the size and complexities of the organization Do periodical bench marking of costs to ensure these are in line with the industry Planning & Organization PO6 COMMUNICATE MANAGEMENT AIMS AND DIRECTIONS BUSINESS REQUIREMENT Management aims and directions are understood by all concerned GENERALLY ACCEPTED STANDARD Establish and promote a positive control culture Ensure that organizational policies are aligned with with management intent, are defined in clear and concise terms and widely communicated Planning & Organization PO6 COMMUNICATE MANAGEMENT AIMS AND DIRECTIONS …GENERALLY ACCEPTED STANDARD Define and implement procedure for review and updating of policies in response to changing business requirement Ensure allocation of adequate resources for compliance with policies Ensure and implement system for checking on compliance with policies Planning & Organization PO7 MANAGE HUMAN RESOURCES BUSINESS REQUIREMENT A motivated and competent workforce is acquired and maintained GENERALLY ACCEPTED STANDARD Ensure knowledge and skill needs are continually assessed in line with business objectives Ensure roles and responsibilities are clearly defined Planning & Organization PO7 MANAGE HUMAN RESOURCES …GENERALLY ACCEPTED STANDARD Ensure personnel policies are in place for o Recruitment o Training o Performance evaluation o Promotion o Transfer / termination Ensure policies are transparent and based on objective criteria Planning & Organization PO8 ENSURE COMPLIANCE WITH EXTERNAL REQUIREMENTS BUSINESS REQUIREMENT Legal, regulatory and contractual obligations are met GENERALLY ACCEPTED STANDARD Define and implement procedures for identification and compliance with o Safety and ergonomic standards o privacy, intellectual property, trans-border data flow and cryptographic regulations Planning & Organization PO8 ENSURE COMPLIANCE WITH EXTERNAL REQUIREMENTS …GENERALLY ACCEPTED STANDARD o Local laws and customs while trading on internet Establish formal agreements with trading partners in regard to electronic transactions Ensure compliance with insurance contract requirements Planning & Organization PO9 ASSESS RISKS BUSINESS REQUIREMENT Support decision making process through identification of complexities / threats GENERALLY ACCEPTED STANDARD Define and implement risk assessment framework incorporating o Risk assessment – identification / measurement o Risk avoidance / mitigation o Residual risk acceptance Planning & Organization PO9 ASSESS RISKS …GENERALLY ACCEPTED STANDARD Ensure sense of proportion in selection of safeguards / controls Planning & Organization PO10 MANAGE PROJECTS BUSINESS REQUIREMENT Projects are accomplished on time and within budgets GENERALLY ACCEPTED STANDARD Define and implement project management framework incorporating o Project initiation o Project approval o Master plan including quality assurance, accreditation, training etc., Planning & Organization PO10 MANAGE PROJECTS …GENERALLY ACCEPTED STANDARD o Risk management ( phase approval ) o Post implementation review Ensure user participation in all phases of project management Planning & Organization PO11 MANAGE QUALITY BUSINESS REQUIREMENT IT customers requirements are met GENERALLY ACCEPTED STANDARD Establish and promote a quality culture based on continuous improvement philosophy Define and implement quality assurance plan covering both general and project specific activities Ensure adherence to IT standards and procedures Acquisition & Implementation AI1 IDENTIFY AUTOMATED SOLUTIONS BUSINESS REQUIREMENT Effective and efficient approach is ensured to satisfy user requirements GENERALLY ACCEPTED STANDARD Define and implement a system development life cycle (SDLC) methodology requiring o Definition of user requirements o Formulation and evaluation of alternative solutions including techno-economic feasibility study Acquisition & Implementation AI1 IDENTIFY AUTOMATED SOLUTIONS …GENERALLY ACCEPTED STANDARD o Formulation and evaluation of alternate acquisition options o Procurement policy o Contract programming policy o Identification, evaluation and implementation of security controls and audit trails o Testing and acceptance Acquisition & Implementation AI2 ACQUIRE AND MAINTAIN APPLICATION SOFTWARE BUSINESS REQUIREMENT Automated solutions effectively support the business process GENERALLY ACCEPTED STANDARD Define and implement design specifications procedures requiring definition and documentation of o File requirements o Program specification Acquisition & Implementation AI2 ACQUIRE AND MAINTAIN APPLICATION SOFTWARE …GENERALLY ACCEPTED STANDARD o File requirements o Program specifications o Internal and external interfaces o Input, processing and output requirements / controls o Testing plan o User-machine interfaces o User manuals Acquisition & Implementation AI2 ACQUIRE AND MAINTAIN APPLICATION SOFTWARE …GENERALLY ACCEPTED STANDARD Design specifications should be developed in close liaison with users and should be subjected to formal approval process Major changes to existing applications should be subjected to process similar to that of new application development Design specifications should be reassessed in the event of major discrepancies Acquisition & Implementation AI3 ACQUIRE AND MAINTAIN TECHNOLOGY INFRASTRUCTURE BUSINESS REQUIREMENT Appropriate platform is provided for supporting business applications GENERALLY ACCEPTED STANDARD Define and implement hardware and software selection policy Define and implement a system for preventive maintenance of hardware Acquisition & Implementation AI3 ACQUIRE AND MAINTAIN TECHNOLOGY INFRASTRUCTURE …GENERALLY ACCEPTED STANDARD Define and implement a system for security, installation, maintenance and change of system software Define and implement a system for using, monitoring and evaluating of system utilities Acquisition & Implementation AI4 DEVELOP AND MAINTAIN PROCEDURES BUSINESS REQUIREMENT Proper use of application and technological solutions put in the place is ensured GENERALLY ACCEPTED STANDARD System development life cycle methodology should include o Operational requirement and service levels o User procedure manual Acquisition & Implementation AI4 DEVELOP AND MAINTAIN PROCEDURES …GENERALLY ACCEPTED STANDARD o Operations manual o Training material Acquisition & Implementation AI5 INSTALL AND ACCREDIT SYSTEMS BUSINESS REQUIREMENT Confirmation is obtained that the solution is fit for use GENERALLY ACCEPTED STANDARD Implementation plan should include o System conversion o Data conversion o Testing of changes Acquisition & Implementation AI5 INSTALL AND ACCREDIT SYSTEMS …GENERALLY ACCEPTED STANDARD o Parallel / pilot testing o Final acceptance testing o Security testing and accreditation o Operational test o Promotion to production Define and implement a system for post implementation review Acquisition & Implementation AI6 MANAGE CHANGES BUSINESS REQUIREMENT Likelihood of disruption, unauthorized alterations, and errors are minimized GENERALLY ACCEPTED STANDARD Define and implement change management procedure incorporating o Change request initiation o Impact assessment Acquisition & Implementation AI6 MANAGE CHANGES …GENERALLY ACCEPTED STANDARD o Tracking and monitoring of changes o Emergency change procedure o Updating of documentation o Release and distribution of change Define and implement system for monitoring access to and activities by maintenance personnel Delivery & Support DS1 DEFINE AND MANAGE SERVICE LEVELS BUSINESS REQUIREMENT Common understanding of the level of service required is established GENERALLY ACCEPTED STANDARD Define and implement a framework for users and IT to have formal service level agreements regarding availability, reliability, performance etc., of the services on offer Define and implement system for monitoring and reporting actual against target levels Delivery & Support DS1 DEFINE AND MANAGE SERVICE LEVELS …GENERALLY ACCEPTED STANDARD Define and implement system for charging for the services so as to ensure trade offs between service levels and costs Define and implement process for continuous improvements of service levels Delivery & Support DS2 MANAGE THIRD PARTY SERVICES BUSINESS REQUIREMENT Outsourced services continue to satisfy business requirements GENERALLY ACCEPTED STANDARD Ensure that business case for outsourcing is defined and documented Define and implement a framework for selection of outsource vendors based on technical competence and ability to deliver Delivery & Support DS2 MANAGE THIRD PARTY SERVICES …GENERALLY ACCEPTED STANDARD Ensure that outsourced relationship are documented in the form of formal contracts duly defining the service levels, security, continuity etc., Define and implement a system for proactive management, monitoring and reporting of outsourced relationships Delivery & Support DS3 MANAGE PERFORMANCE AND CAPACITY BUSINESS REQUIREMENT Adequate capacity is available and also optimally utilized to meet performance requirements GENERALLY ACCEPTED STANDARD Ensure that availability and performance needs are clearly identified Implement fault tolerance mechanism to ensure continued availability and performance Delivery & Support DS3 MANAGE PERFORMANCE AND CAPACITY …GENERALLY ACCEPTED STANDARD Set up preventive and predictive maintenance plans to ensure that problems get corrected before they could affect system performance Set up system for continuous monitoring, analyzing and reporting of failures/exceptions Define and implement system of workload forecasting, capacity planning and timely acquisition of required capacity Delivery & Support DS4 ENSURE CONTINUOUS SERVICE BUSINESS REQUIREMENT IT services continue to be available as required in the event of major disaster and business impact of such disaster is minimized GENERALLY ACCEPTED STANDARD Define and implement a framework for development, approval, testing and maintenance of business continuity and disaster recovery plans Delivery & Support DS4 ENSURE CONTINUOUS SERVICE …GENERALLY ACCEPTED STANDARD Identify IT resources required to support critical business processes and window of time for recovery to provide basis for continuity plan Include the following in the continuity plan o An emergency plan defining persons to be notified, evacuation procedure, action for minimizing losses etc., o Recovery plan defining location of backup facility, recovery teams, recovery ranking etc., Delivery & Support DS4 ENSURE CONTINUOUS SERVICE …GENERALLY ACCEPTED STANDARD o Test plan defining testing methodology, analysis of test results, responsibility for follow up action etc., Ensure that continuity plan is stored off-site and copies distributed to authorized persons on need to know basis Ensure off site storage of backup media, documentation and other IT resources Ensure updating of plan based on resumption experience Delivery & Support DS5 ENSURE SYSTEMS SECURITY BUSINESS REQUIREMENT Information is safeguarded against unauthorized use, disclosure or modification, damage or loss GENERALLY ACCEPTED STANDARD Define and implement an information security policy in line with business requirement Define and implement logical access control policy for access to and use IT computing resources Delivery & Support DS5 ENSURE SYSTEMS SECURITY …GENERALLY ACCEPTED STANDARD Define and implement system for user accounts management Define and implement policy for classification / reclassification of data in terms of sensitivity including guidelines for storage, sharing , archiving, deleting and disposition of classified data. Define and implement security surveillance program including reaccreditations, incident handling etc., Delivery & Support DS5 ENSURE SYSTEMS SECURITY …GENERALLY ACCEPTED STANDARD Define and implement data encryption policy for during storage and transit Define and implement system for ensure security of online transaction including counterpart trust, transaction authorization, no-repudiation etc., Define and implement virus control policy to protect information system from computer viruses Delivery & Support DS5 ENSURE SYSTEMS SECURITY …GENERALLY ACCEPTED STANDARD Define and implement a firewall policy for connection to /from internet to protect against denial of service and unauthorized access to internal resources Define and implement measures for protection of security related assets against tempering, disclosure etc., Delivery & Support DS6 IDENTIFY AND ALLOCATE COSTS BUSINESS REQUIREMENT Correct costs of IT services should be known GENERALLY ACCEPTED STANDARD Define and implement a billing and chargeback system to enable user to control use of information services and associated costs Define and implement procedures for computing, reporting, analyzing and monitoring of cost data for IT services Delivery & Support DS7 EDUCATE AND TRAIN USERS BUSINESS REQUIREMENT Users should make effective use of technology and be aware of risk and responsibilities GENERALLY ACCEPTED STANDARD Define and implement a system for identification of training needs of IT services users Define and implement procedures for training of IT users based on identified needs including security awareness and incident handling Delivery & Support DS8 ASSIST AND ADVISE CUSTOMERS BUSINESS REQUIREMENT User problems are appropriately resolved GENERALLY ACCEPTED STANDARD Define and implement a ‘help desk’ function Maintain proper records of reporting and clearance of all user problems Have an escalation procedure in place Monitor response times Delivery & Support DS8 ASSIST AND ADVISE CUSTOMERS …GENERALLY ACCEPTED STANDARD Identify trends, analyze and take appropriate actions Delivery & Support DS9 MANAGE CONFIGURATION BUSINESS REQUIREMENT IT assets are properly accounted and physical existence verified GENERALLY ACCEPTED STANDARD Define and implement system for maintenance of inventory records in respect of acquisition, disposal, transfer, status change ( including history ) etc., of all identifiable IT assets Carry out periodic physical verification Delivery & Support DS9 MANAGE CONFIGURATION …GENERALLY ACCEPTED STANDARD Define and implement policy restricting usage of personal or unlicensed software Define separate file storage area for software in development, testing and production Define and implement system for software version control. Use library management software where required Delivery & Support DS10 MANAGE PROBLEMS AND INCIDENTS BUSINESS REQUIREMENT Problems and incidents are resolved and recurrence prevented GENERALLY ACCEPTED STANDARD Define and implement procedure for recording, analyzing, resolving and reporting of non standard operational events Define and implement problem escalation procedure Delivery & Support DS10 MANAGE PROBLEMS AND INCIDENTS …GENERALLY ACCEPTED STANDARD Have an emergency change approval process in place Have a procedure for grant of emergency and temporary authorizations with automatic expiry Establish emergency processing priorities in line with criticality of operations Delivery & Support DS11 MANAGE DATA BUSINESS REQUIREMENT Integrity of data is maintained at all times GENERALLY ACCEPTED STANDARD Use well designed input forms to minimize errors and omissions Define and implement system for authorization of source documents Ensure segregation between origination and approval of source documents Delivery & Support DS11 MANAGE DATA …GENERALLY ACCEPTED STANDARD Define and implement source document retention policy Define and implement input, processing and output controls Define and implement measures to protect all sensitive information during transmission as well as storage Define and implement procedures to ensure authenticity and integrity of electronic transactions Delivery & Support DS11 MANAGE DATA …GENERALLY ACCEPTED STANDARD Define and implement system for storage, movement, physical verification and integrity testing of media Define and implement data storage and retention policy Define and implement back up and archiving procedures Delivery & Support DS12 MANAGE FACILITIES BUSINESS REQUIREMENT Physical surroundings should protect IT facilities and people from man made and natural hazards GENERALLY ACCEPTED STANDARD Define and implement physical security and access control both for on and off site IT facilities including auxiliary services Maintain low profile for all IT sites Delivery & Support DS12 MANAGE FACILITIES …GENERALLY ACCEPTED STANDARD Ensure due compliance of personnel health and safety requirements as per applicable law Ensure adequate protection against environmental factors like fire, dust, heat, humidity etc., Provide adequate back up to ensure steady uninterrupted supply in the event of power failures or fluctuations Delivery & Support DS13 MANAGE OPERATIONS BUSINESS REQUIREMENT IT operations are performed regularly and orderly GENERALLY ACCEPTED STANDARD Define and implement standard operating procedures for all routine operations like start and shut down, job scheduling, shift change, maintenance and review of operation logs Define and implement procedure for safe keeping of special forms and devices M1 MONITOR PROCESSES MONITORING BUSINESS REQUIREMENT Performance objectives set for IT processes are achieved GENERALLY ACCEPTED STANDARD Define and implement a system for measuring, reporting and reviewing of IT performance against pre defined key performance indicators Periodically assess users satisfaction level with IT to identify shortfalls / improvement targets MONITORING M2 ASSESS INTERNAL CONTROL ADEQUACY BUSINESS REQUIREMENT Internal control objectives set for IT processes are achieved GENERALLY ACCEPTED STANDARD Define and implement a system for monitoring effectiveness of internal control measures for IT processes Periodically seek assurance through self assessment or independent audit as to the adequacy of internal controls MONITORING M3 OBTAIN INDEPENDENT ASSURANCE BUSINESS REQUIREMENT Confidence and trust among organizations, customers and third party providers is increased GENERALLY ACCEPTED STANDARD Obtain independent certification / accreditation of security and internal controls of IT services both in house and outsourced, prior to use and on a routine cycle after implementation Obtain independent evaluation of effectiveness of IT services both in house and outsourced MONITORING M3 OBTAIN INDEPENDENT ASSURANCE …GENERALLY ACCEPTED STANDARD Obtain independent assurance as to IT function’s ( both in house and outsourced ) compliance of legal and regulatory requirements and contractual commitments Make sure independent assurance comes from people with due technical competence and skills Seek pro active involvement of audit in design / implementation of IT solutions MONITORING M4 PROVIDE FOR INDEPENDENT AUDIT BUSINESS REQUIREMENT Confidence level is further increased and benefits from best practices advice obtained GENERALLY ACCEPTED STANDARD Set up an audit charter defining responsibility, authority and accountability of IT audit function Ensure independence of auditors both in attitude and appearance MONITORING M4 PROVIDE FOR INDEPENDENT AUDIT …GENERALLY ACCEPTED STANDARD Ensure competence of auditors and their commitment to professional ethics and standards Define audit objectives in terms of security, effectiveness and efficiency of internal control procedures and management’s ability to follow such procedures. Audit plan should address audit objectives and comply with applicable professional standards MONITORING M4 PROVIDE FOR INDEPENDENT AUDIT …GENERALLY ACCEPTED STANDARD Auditors should obtain sufficient, reliable, relevant and useful evidence and base their findings and conclusions on the analysis and interpretation of the evidence so obtained Auditors should make a formal report and follow up on implementation of the recommendations. MANAGEMENT GUIDELINES OVERVIEW A set of tools to assess and measure an organization’s IT environment against the 34 IT processes described in COBIT® Helps in responding to questions like Whit is the right level of control for my IT to support business objectives How far should we go, is the cost justified by the benefits How do we ensure that ship is on course MANAGEMENT GUIDELINES OVERVIEW Provides a tool kit consisting of Maturity models – for benchmarking Critical success factors – for getting IT processes under control Key goal indicators – for monitoring achievement of IT goals Key performance indicators – for monitoring performance within IT process MANAGEMENT GUIDELINES MATURITY MODEL A tool for benchmarking and self assessment against the control objectives Helps in meeting following three needs a relative measure of where the organization is a manner to efficiently decide where to go a tool for measuring progress against the goal Uses grades from 0 to 5. The approach is similar to Software Engineering Institute capability maturity model ( Sei-CMM ) MANAGEMENT GUIDELINES MATURITY MODEL The 6 grades are 0 Non-Existent – management processes are not applied at all 1 Initial – processes are ad-hic and disorganized 2 Repeatable – processes follow a regular pattern 3 Defined – processes are documented and communicated 4 Managed – processes are monitored and measured 5 Optimized – best policies are followed and automated MANAGEMENT GUIDELINES MATURITY MODEL Grades are defined in terms of Understanding and awareness of risks and control issues Training and communication applied on the issues Process and practices that are implemented Techniques and automation to make processes more effective and efficient Degree of compliance to internal policy, laws and regulations Type and extent of expertise employed MANAGEMENT GUIDELINES 0 NON-EXISTENT Complete lack of any recognizable process Not even a recognition that there is an issue to be addressed MANAGEMENT GUIDELINES 1 INITIAL Organization recognizes that risk and control issues exist and need to be addressed Communication on issues is sporadic Approach is ad-hoc and tend to be applied on case to case basis MANAGEMENT GUIDELINES 2 REPEATABLE Awareness exists about the risk and control issues and the need to act Communication is informal with responsibility left to individual Use of similar processes by different individuals undertaking similar tasks emerges but heavy reliance on knowledge of individual persists Use of automated tools begin Monitoring is isolated and inconsistent MANAGEMENT GUIDELINES 3 DEFINED Risk and control issues and the needs to act are understood Communication is formal and also supported by informal training Existing processes are formalized and documented. Sharing of better internal practices begin Use of automated tools catches up Use of performance measurements, balanced score card and root cause analysis begin to emerge. Monitoring however remain inconsistent IT specialists begin to participate in business processes MANAGEMENT GUIDELINES 4 MANAGED Risk and control requirements are well understood Communication is formal and duly supported by formal training Processes are not only documented but also standardized, sound and complete. Internal best practices are applied Usage of advanced automated tools and tactical use of technology begin Use of performance measurements, balanced score card and root cause analysis are standardized All internal domain experts participate in business processes MANAGEMENT GUIDELINES 5 OPTIMIZED Risk and control requirements are understood on forward looking basis Communication and training cover external best practices and leading edge concepts External best practices are duly applied Sophisticated techniques are deployed. Technology is extensively and optimally used Performance measurements, balanced score card and root cause analysis are always applied External experts and industry leaders are consulted for guidance MANAGEMENT GUIDELINES CRITICAL SUCCESS FACTORS Most important things that contribute to the IT process achieving its goals Are deduced from Standard control model IT governance model Standard control model identifies the following CSFs Defined and documented processes Defined and documented policies Clear accountabilities MANAGEMENT GUIDELINES CRITICAL SUCCESS FACTORS Strong support/commitment of management Appropriate communication to concerned internal and external persons Consistent measurement practices IT governance model identifies the following CSFs IT to be aligned with the business IT to enable the business and maximize its benefits IT resources to be used responsibly IT related risks to be managed appropriately MANAGEMENT GUIDELINES CRITICAL SUCCESS FACTORS Management guidelines list generic CSFs in three groups as under Applicable to IT in general Applicable to most IT processes Applicable to IT governance MANAGEMENT GUIDELINES CSFs – IT IN GENERAL Definition and alignment of IT strategy and business goals Know the IT process customers and their expectations Ensure processes are scalable and are appropriately managed and leveraged Ensure availability of staff of required quality Ensure measurement of IT performance in financial terms, customer satisfaction, process effectiveness and future capability Apply continuous quality improvement MANAGEMENT GUIDELINES CSFs – MOST IT PROCESSES Ensure all stakeholders are aware of risks of IT and the opportunity offered by IT Ensure all stakeholders provide strong commitment and support to IT initiatives Ensure goals and objectives are communicated and understood across all disciplines Ensure all people know How processes implement and monitor objectives Who is accountable for process performance MANAGEMENT GUIDELINES CSFs – MOST IT PROCESSES Ensure people are goal focused and Have right information on customers and their expectations Know the consequences of their actions or inactions Establish a business culture encouraging Cross divisional co-operation Teamwork Continuous improvement MANAGEMENT GUIDELINES CSFs – MOST IT PROCESSES Ensure integration / alignment of major IT processes e.g. change, problem and configuration management MANAGEMENT GUIDELINES CSFs – IT GOVERNANCE Increase transparency Reduce complexity Promote learning Provide flexibility and scalability Avoid breakdown in internal controls and oversight Promote positive control culture Prescribe a code of conduct Promote risk assessment as a standard practice MANAGEMENT GUIDELINES CSFs – IT GOVERNANCE Encourage self assessment Ensure formal compliance on Adherence to established standards Monitoring and follow up of control deficiencies and risks Integrate IT governance with enterprise governance to provide Clear direction on It strategy Risk assessment framework Security policy MANAGEMENT GUIDELINES CSFs – IT GOVERNANCE Focus on major IT projects , change initiatives and quality effort Establish an audit committee to Oversee independent auditors Drive IT audit plan Review results of audit and 3rd part opinions MANAGEMENT GUIDELINES KEY GOAL INDICATORS A measurable indicator of achievement of IT process goals Are measured after the fact and are therefore referred as ‘LAG’ indicators Supports the financial and customer dimension of the Balanced Business Scorecard Management guidelines list the following as goals of all IT processes Availability of systems and services Absence of integrity and confidentiality risks Cost-efficiency of processes and operations MANAGEMENT GUIDELINES KEY GOAL INDICATORS Confirmation of reliability, effectiveness and compliance Management guidelines lists the following generic KGIs Achieving targeted return on investment or business value benefits Enhanced performance management Reduced IT risks Productivity improvements Integrated supply chains Standardized processes MANAGEMENT GUIDELINES KEY GOAL INDICATORS Boost of service delivery (sales) Reaching new and satisfying existing customers Creation of new service delivery channels Availability of bandwidth, computing power and IT delivery mechanisms fitting the business, and their uptime and downtime Meeting requirements and expectations of the customer of the process on budget and on time Number of customers and cost per customer served Adherence to industry standards MANAGEMENT GUIDELINES KEY PERFORMANCE INDICATORS A measurable indicator of performance of IT process enablers Are measured before the fact and are therefore referred as ‘LEAD’ indicators Helps in predicting success or failure of IT process goals Management guidelines list generic KPIs under the three groups Applicable to IT in general Applicable to most IT processes Applicable to IT governance MANAGEMENT GUIDELINES KPIs – IT IN GENERAL Reduced cycle times (i.e., responsiveness of IT production and development) Increased quality and innovation Utilization of communications bandwidth and computing power Service availability and response times Satisfaction of stakeholders (survey and number of complaints) Number of staff trained in new technology and customer service skills MANAGEMENT GUIDELINES KPIs – MOST IT PROCESSES Improved cost-efficiency of the process (cost vs. deliverables) Staff productivity (number of deliverables) and morale (survey) Amount of errors and rework MANAGEMENT GUIDELINES KPIs – IT GOVERNANCE Benchmark comparisons Number of non-compliance reporting MANAGEMENT GUIDELINES DS5 – MATURITY MODEL 0 NON-EXISTENT The organization does not recognize the need for IT security Responsibilities and accountabilities are not assigned for ensuring security Measures supporting the management of IT security are not implemented There is no IT security reporting and no response process to IT security breaches There is a complete lack of a recognizable system security administration process MANAGEMENT GUIDELINES DS5 – MATURITY MODEL 1 INITIAL The organization recognizes the need for IT security, but security awareness depends on the individual IT security is addressed on a reactive basis and not measured IT security breaches invoke "finger pointing" responses if detected, because responsibilities are unclear Responses to IT security breaches are unpredictable MANAGEMENT GUIDELINES DS5 – MATURITY MODEL 2 REPEATABLE Responsibilities and accountabilities for IT security are assigned to an IT security coordinator with no management authority Security awareness is fragmented and limited IT security information is generated, but is not analyzed Security solutions tend to respond reactively to IT security incidents and by adopting thirdparty offerings, without addressing the specific needs of the organization MANAGEMENT GUIDELINES DS5 – MATURITY MODEL …2 REPEATABLE Security policies are being developed, but inadequate skills and tools are still being used IT security reporting is incomplete, misleading or not pertinent 3 DEFINED Security awareness exists and is promoted by management Security awareness briefings have been standardized and formalized MANAGEMENT GUIDELINES DS5 – MATURITY MODEL … 3 DEFINED IT security procedures are defined and fit into a structure for security policies and procedures Responsibilities for IT security are assigned, but not consistently enforced An IT security plan exists, driving risk analysis and security solutions IT security reporting is IT focused, rather than business focused Ad hoc intrusion testing is performed MANAGEMENT GUIDELINES DS5 – MATURITY MODEL 4 MANAGED Responsibilities for IT security are clearly assigned, managed and enforced IT security risk and impact analysis is consistently performed Security policies and practices are completed with specific security baselines Security awareness briefings have become mandatory User identification, authentication and authorizations are being standardized MANAGEMENT GUIDELINES DS5 – MATURITY MODEL …4 MANAGED Security certification of staff is being established Intrusion testing is a standard and formalized process leading to improvements Cost/benefit analysis, supporting the implementation of security measures, is increasingly being utilized IT security processes are coordinated with the overall organization security function IT security reporting is linked to business objectives MANAGEMENT GUIDELINES DS5 – MATURITY MODEL 5 OPTIMIZED IT security is a joint responsibility of business and IT management and is integrated with corporate security business objectives IT security requirements are clearly defined, optimized and included in a verified security plan Security functions are integrated with applications at the design stage and end users are increasingly accountable for managing security MANAGEMENT GUIDELINES DS5 – MATURITY MODEL …5 OPTIMIZED IT security reporting provides early warning of changing and emerging risk, using automated active monitoring approaches for critical systems Incidents are promptly addressed with formalized incident response procedures supported by automated tools Periodic security assessments evaluate the effectiveness of implementation of the security plan MANAGEMENT GUIDELINES DS5 – MATURITY MODEL …5 OPTIMIZED Information on new threats and vulnerabilities is systematically collected and analyzed, and adequate mitigating controls are promptly communicated and implemented Intrusion testing, root cause analysis of security incidents and pro-active identification of risk is the basis for continuous improvements Security processes and technologies are integrated organization wide MANAGEMENT GUIDELINES DS5 – CSFs An overall security plan is developed that covers the building of awareness, establishes clear policies and standards, identifies a cost-effective and sustainable implementation, and defines monitoring and enforcement processes There is awareness that a good security plan takes time to evolve The corporate security function reports to senior management and is responsible for executing the security plan MANAGEMENT GUIDELINES DS5 – CSFs Management and staff have a common understanding of security requirements, vulnerabilities and threats, and they understand and accept their own security responsibilities Third-party evaluation of security policy and architecture is conducted periodically A "building permit" program is defined, identifying security baselines that have to be adhered to A "drivers license" program is in place for those developing, implementing and using systems, enforcing security certification of staff MANAGEMENT GUIDELINES DS5 – CSFs The security function has the means and ability to detect, record, analyze significance, report and act upon security incidents when they do occur, while minimizing the probability of occurrence by applying intrusion testing and active monitoring A centralized user management process and system provides the means to identify and assign authorizations to users in a standard and efficient manner A process is in place to authenticate users at reasonable cost, light to implement and easy to use MANAGEMENT GUIDELINES DS5 – KGIs No incidents causing public embarrassment Immediate reporting on critical incidents Alignment of access rights with organisational responsibilities Reduced number of new implementations delayed by security concerns Full compliance, or agreed and recorded deviations from minimum security requirements Reduced number of incidents involving unauthorized access, loss or corruption of information MANAGEMENT GUIDELINES DS5 – KPIs Reduced number of security-related service calls, change requests and fixes Amount of downtime caused by security incidents Reduced turnaround time for security administration requests Number of systems subject to an intrusion detection process Number of systems with active monitoring capabilities Reduced time to investigate security incidents MANAGEMENT GUIDELINES DS5 – KPIs Time lag between detection, reporting and acting upon security incidents Number of IT security awareness training days AUDIT GUIDELINES OVERVIEW A complementary tool to facilitate application of COBIT® within audit and assessment activities Support the needs of External auditors Internal auditors Evaluators Quality reviewers Technical assessors AUDIT GUIDELINES OVERVIEW Support both reactive and proactive perspectives by responding to question like Reactive o Is what I am doing all right ? And if not, how do I fix it? Proactive o What do I need so it will not need to be fixed Replaces auditor’s opinion with authoritative criteria AUDIT GUIDELINES OVERVIEW Key contents include General structure Audit process requirement Generic audit guidelines Detailed audit guidelines Opportunities and challenges AUDIT GUIDELINES OVERVIEW Disclaimers Are not intended as a tool for overall audit plan and coverage Are not intended to teach the basic of auditing Do not dwell upon the use of tools for automation of audit of IT processes Are not exhaustive nor universally applicable AUDIT GUIDELINES GENERAL STRUCTURE Audit guidelines present a 3 tier approach as under Level 1 – applicable to IT audit in general. This is supported by o COBIT® framework and control objectives o General principles of control o Audit process requirements o Generic IT audit guidelines Level 2 – applicable to specific IT process and is supported by detailed IT audit guidelines AUDIT GUIDELINES GENERAL STRUCTURE Level 3 – may apply depending upon local conditions. Audit guidelines do not offer any support for o Sector specific criteria o Industry standards o Platform specific elements o Detailed control techniques used AUDIT GUIDELINES AUDIT PROCESS REQUIREMENT Define audit scope by investigating, analyzing and defining The business processes concerned The platforms and information systems which are supporting the business process The IT roles, responsibilities and organization structure Associated business risks Identify information requirements relevant for the business process AUDIT GUIDELINES AUDIT PROCESS REQUIREMENT Identify inherent IT risks and overall level of control by identifying Recent changes and incidents in business and technology environment Results of audits, self - assessments and certification Monitoring control applied by management Select processes and platforms to audit Set audit strategy AUDIT GUIDELINES GENERIC IT AUDIT GUIDELINES Based on generally accepted audit process, the guidelines provide the following structure for IT audit process Obtaining an understanding of business related risks, and relevant control measures Evaluating the stated controls Assessing compliance Substantiating the risk of control objectives not being met AUDIT GUIDELINES OBTAINING AN UNDERSTANDING OBJECTIVE To document the underlying business activity To identify the stated control measures in place PROCEDURE Interview appropriate management and staff to gain an understanding of: o Business requirements and associated risks o Organization structure o Roles and responsibilities AUDIT GUIDELINES OBTAINING AN UNDERSTANDING …PROCEDURE o Policies and procedures o Laws and regulations o Control measure in place o Management reporting Document the process - related IT resources particularly affected by the process under review AUDIT GUIDELINES OBTAINING AN UNDERSTANDING …PROCEDURE Confirm the understanding of the process under review, the Key Performance Indicators (KPI) of the process, the control implications, e.g., by a process walk through OUTPUT Who performs the task covered by the control objective Where the task is performed When the task is performed AUDIT GUIDELINES OBTAINING AN UNDERSTANDING …OUTPUT On what inputs is the task performed What outputs are expected of the task What are the stated procedures for performing the task AUDIT GUIDELINES EVALUATING CONTROLS OBJECTIVE To assess the effectiveness of control measures in place PROCEDURE Evaluate the appropriateness of control measures by considering: o Identified criteria o Industry standard practices o Critical Success Factor (CSF) o Auditor professional judgment AUDIT GUIDELINES EVALUATING CONTROLS …PROCEDURE Conclude the degree to which the control objective is met OUTPUT Evaluated laws, regulations and organizational criteria for applicability to the procedures Evaluated stated procedures to determine if they are cost effective and provide reasonable assurance that the task is performed and the control objective is met AUDIT GUIDELINES EVALUATING CONTROLS …OUTPUT Evaluated any compensating controls used to bolster weak procedures Concluded whether the stated procedures and compensating controls together provide and effective control structure. Identified whether compliance testing is appropriate AUDIT GUIDELINES ASSESSING COMPLIANCE OBJECTIVE To ensure that the control measures established are working as prescribed, consistently and continuously To conclude on the appropriateness of the control environment PROCEDURE Obtain direct or indirect evidence to ensure that the procedures have been complied AUDIT GUIDELINES ASSESSING COMPLIANCE …PROCEDURE Perform a limited review of the adequacy of the process deliverables Determine the level of substantive testing and additional work needed to provide assurance that the IT process is adequate OUTPUT Documented the organization's adherence to the procedures AUDIT GUIDELINES ASSESSING COMPLIANCE …OUTPUT Concluded whether the stated procedures and compensating controls are being properly and consistently applied by the organization The level of substantive testing needed AUDIT GUIDELINES SUBSTANTIATING RISK OBJECTIVE To support the opinion that control objectives are not being met To ‘shock’ management into action PROCEDURE Document the control weaknesses, and resulting threats and vulnerabilities Identify and document the actual and potential impact Provide comparative information AUDIT GUIDELINES SUBSTANTIATING RISK OUTPUT Data supporting the conclusion that control objectives are not being met AUDIT GUIDELINES OPPURTUNITIES Allows for prioritizing audit activities Leads to investigation of areas that normally would not have been addressed More logical set up and sequence of interviews can be developed Investigations can be focused Ensure effective audit coverage and timely acquisition of necessary audit skills while defining the strategic audit plan AUDIT GUIDELINES CHALLENGES Initial application may be cumbersome May appear to be repetitive Formalism may at time appear unnecessary AUDIT GUIDELINES PO1 – OBTAINING UNDERSTANDING By interviewing Chief Executive Officer Chief Operations Officer Chief Financial Officer Chief Information Officer IT planning/steering committee members IT senior management and human services staff AUDIT GUIDELINES PO1 – OBTAINING UNDERSTANDING By obtaining Policies and procedures relating to the planning process Senior management steering roles and responsibilities Organization objectives and long- and shortrange plans IT objectives and long- and short-range plans Status reports and minutes of planning/steering committee meetings AUDIT GUIDELINES PO1 – EVALUATING CONTROLS By considering whether IT or business enterprise policies and procedures address a structured planning approach A methodology is in place to formulate and modify the plans and at a minimum, they cover o Organization mission and goals o IT initiatives to support the organization mission and goals o Opportunities for IT initiatives AUDIT GUIDELINES PO1 – EVALUATING CONTROLS …By considering whether o Feasibility studies of IT initiatives o Risk assessments of IT initiatives o Optimal investment of current and future IT investments o Re-engineering of IT initiatives to reflect changes in the enterprise's mission and goals o Evaluation of the alternative strategies for data applications, technology and organization AUDIT GUIDELINES PO1 – EVALUATING CONTROLS …By considering whether Organizational changes, technology evolution, regulatory requirements, business process reengineering, staffing, in- and out-sourcing, etc. are taken into account and adequately addressed in the planning process Long- and short-range IT plans exist, are current, adequately address the overall enterprise, its mission and key business functions AUDIT GUIDELINES PO1 – EVALUATING CONTROLS …By considering whether IT projects are supported by the appropriate documentation as identified in IT planning methodology Checkpoints exist to ensure that IT objectives and long- and short-range plans continue to meet organizational objectives and long- and short-range plans Review and sign-off by process owners and senior management occurs AUDIT GUIDELINES PO1 – EVALUATING CONTROLS …By considering whether The IT plan assesses the existing information systems in terms of degree of business automation, functionality, stability, complexity, costs, strengths and weaknesses The absence of long-range planning for information systems and supporting infrastructure results in systems that do not support enterprise objectives and business processes, or do not provide appropriate integrity, security and control AUDIT GUIDELINES PO1 – ASSESSING COMPLIANCE …By testing that Minutes from IT function planning/steering committee meetings reflect the planning process Planning methodology deliverables exist and are as prescribed Relevant IT initiatives are included in the IT long- and short-range plans IT initiatives support the long- and short-range plans and consider requirements for research, training, staffing, facilities, hardware and software AUDIT GUIDELINES PO1 – ASSESSING COMPLIANCE …By testing that Technical implications of IT initiatives have been identified Consideration has been given to optimizing current and future IT investments IT long- and short-range plans are consistent with the organization's long- and short-range plans and organization requirements Plans have been changed to reflect changing conditions AUDIT GUIDELINES PO1 – ASSESSING COMPLIANCE …By testing that IT long-range plans are periodically translated into short-range plans Tasks exist to implement the plans AUDIT GUIDELINES PO1 – SUBSTANTIATING RISK By performing Benchmarking of strategic IT plans against similar organizations or appropriate international standards/recognized industry best practices A detailed review of the IT plans to ensure that IT initiatives reflect the organization's mission and goals AUDIT GUIDELINES PO1 – SUBSTANTIATING RISK By performing A detailed review of the IT plans to determine if known areas of weakness within the organization are being identified for improvement as part of the IT solutions contained in the plans By identifying IT failures to meet the organization's missions and goals IT failures to match short-range plans with long-range plans AUDIT GUIDELINES PO1 – SUBSTANTIATING RISK …By identifying IT projects failures to meet short-range plans IT failures to meet cost and time guidelines Missed business opportunities Missed IT opportunities