Securing Windows with Group Policy
advertisement
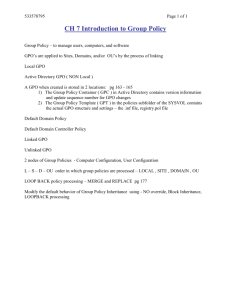
Securing Windows With Group Policy Josh Rickard • BS in Computer Information Systems • Central Methodist University – 1 year • University of Missouri – 4 years • Currently a Security Analyst-Specialist – QualysGuard, Kasperksy, incident response Josh Rickard • Microsoft Deployment Toolkit & SCCM • Group Policy • Digital forensics • Incident response • PowerShell tool making! Josh Rickard • GIAC Certified Windows Security Administrator - GCWN • GIAC Certified Forensic Analyst – GCFA • QualysGuard Certified Specialist – QGCS-VM • Apple Certified Associate – Mac Integration FIRST STEP TOWARDS SECURING WINDOWS START WITH MALWARERESISTANT OPERATING SYSTEMS AND SOFTWARE NEXT STEPS PATCH MANAGEMENT Questions • Who uses Active Directory in their environment? • Who uses Group Policy in their environment? – Daily? – Weekly? – Monthly? – Year or more? Questions • Who has/uses two separate accounts? – Mundane (email@emailaddress.com) – Admin (unique account) USE TWO SEPARATE ACCOUNTS Two Group Policy Questions • Where are you? (Domain, OU, Site) • What are you? (User or Computer) LSD OU! Local • Local Group Policy Site • Site or Forest Group Policy Domain • Domain Group Policy OU • Organizational Unit Group Policy Exceptions to the rule • • Account Policies • Kerberos Policy settings – Password Policy – Enforce user logon restrictions – Enforce password history – Maximum lifetime for service ticket – Maximum & Minimum password age – Maximum lifetime for user ticket – Minimum password length – Maximum lifetime for user ticket renewal – Passwords must meet complexity requirements – Maximum tolerance for computer clock synchronization – Store password using reversible encryption for all users in the domain (NOOOOOOOOOO!!!!!!) – Network Access: Allow anonymous SID/NAME translation – Network Security: Force Logoff when Logon Hours expire Account Lockout Policy settings • – Account lockout duration – Account lockout threshold – Reset account lockout counter after Local Policies Computer Configuration • Computer configuration almost always wins • Used to apply configuration changes specific to machines • Think, HKLM • Exception: Loopback Processing Mode User Configuration • Really only useful if user & computer objects in same OU • Used to apply configuration changes specific to users • Think, HKCU or HKU Policies • No tattoo – If GPO is out of scope, it will be removed • Overwrite current application settings • Policies are recognized by applications – i.e. grayed out settings Preferences • Tattoo's – If GPO goes out of scope, settings remain • Item Level Targeting – We will talk about this later Block Inheritance • Block GPOs higher in the LSD OU order • Keep in mind that Kerberos, password, & lockout policies will still be enforced for everyone in that domain. Enforced (a.k.a., “No Override”) • Enforce parent container GPO to all sub-containers • This will “override” any “Block Inheritance” GPO settings • Except: Loopback Mode GPOs Loopback Processing Mode • User configurations for computer objects • Replace – This will replace current user settings applied to that OU • Merge – This will merge both the user & computer GPO • *NOTE: User GPO will win. WMI Filtering • Filter/configure GPO “scope” • Filter based on specific users/computers/groups/etc. Item Level Targeting • GPO Preferences • Target a specific machine attribute (other than WMI Filtering) Active Directory Permissions • Enable “Advanced Features” • Delegate control – Always take a “least privilege” approach • Delegate full control over an OU only Morale of the Story • We need to ask ourselves, where is the computer/user account located in AD? Now the fun stuff! We need to ask ourselves, where is the computer/user account located in AD? Auto-Play & Auto-Run • Disable the action taken when a thumb drive or portable hard drive is plugged into a computer Windows Firewall with Advanced Security • Manage Network Profiles – Domain – Home – Public • Manage applications/services that should be allowed/denied Manage Group Memberships • • GPO Restricted Groups – Manage global groups in AD – Centrally manage all high-target groups – “Rebuilds” the group completely every time GP is refreshed GPO Preferences – Best for managing local groups on domain machines – Create custom local groups – Assign Customized rights and privileges – Assign customized permission as well Manage User Rights • Allow/Deny Log On Locally – Why does someone need to log on locally to a server/computer? • Allow/Deny Access to Computer From the Network – Limit this to either specific user or just admins/IT Pro’s • Allow/Deny Log On Remote Desktop Services – Normal users do not need RDP Manage High Target Accounts • Restrict Logon Hours and Workstations – Enterprise, Schema, and Domain Admins should be restricted as tightly as possible. • Remote Desktop logon • Remote Control logon • Etc. • Why would Domain/Enterprise/Schema Admins be RDPing? – Answer: They wouldn’t! AppLocker • Requirements: – Application Identity Service must be running (Automatic) • Three different conditions can be use – Hash Condition Rules – Path Condition Rules – Publisher Condition Rules AppLocker – Hash Condition • Every file has a unique hash value • Positive – Unique hash for every executable – Secure! • Negative – Every update has a new hash AppLocker – Path Condition • Positive – Select an entire suite of products – You can use wildcards (*) • Negative – You must know all paths the application uses • C:\ProgramData • C:\Users\username\AppData\Local\*\*.zip\* AppLocker – Publisher Condition • Positive – Select an entire path to allow a suite of applications – You can use wildcards (*) • Negative – Only works for applications that are digitally signed Additional Security Measures • Require screensavers with passwords • Use LAPS – do not keep the same local admin password on all machines – If possible, disable the ability to logon with a local account – If you set passwords using GP, then they are stored unencrypted in \\domain.com\SYSVOL • Hashed does not mean encrypted. Additional Security Measures • Disable Guest Account – Option: Network Access: Sharing and Security Model for Local Accounts • Automatically demotes any remote user who authenticates to guest status – If you disable the guest account and this setting is enabled, then no one will be able to long using a local account (good thing!) Additional Security Measures • Display a Logon Banner with Legal Notice This system is for use of authorized users only and is not public. Individuals using this computer system without authority or in excess of their authority are subject to having all of their activities on this system monitored and recorded, including their keystrokes and mouseclicks. Anyone using this system expressly consents to such monitoring and is advised that if this monitoring reveals possible evidence of criminal activity, this evidence may be provided to law enforcement officials with the intent to prosecute. Block Unsigned Scripts • PowerShell • WSH • VBScript • Jscript • Perl • Python • This does NOT protect you from advanced users & Malware • PowerShell is not a security mechanism Advanced Protection • DEP – Data Execution Prevention – Prevents execution of code in memory that are not marked as executable • ASLR – Address Space Layout Randomization – Random address spaces make exploits more difficult. No way to hard code memory locations • EMET – Enhanced Mitigation Experience Toolkit Scheduled Tasks for GPO Scripts • Schedule tasks to run under the identity with the least privilege – Local Services – Network Services – Local System (if needed) • Do NOT use passwords in scripts 7 Deadly Sins (for Malware) • Act As Part of the Operating System • Create a Token Object • Debug Programs • Load and Unload Device Drivers • Restore Files and Directories • Take Ownership • Impersonate a Client After Authentication Impersonate A Client Privilege • Primary Security Access Token (SAT) – Basically, impersonate a user’s SAT for other running processes • Used by network services to impersonate clients • Token stealing – Steal SATs for network authentication Debug Programs Privilege • Grants read/write access to user & kernel-mode memory • Malware uses it for: • – New thread injected into any process – Passwords, hashes, encryption keys and other data can be read out of kernel space memory without DLL injection. Pass-The-Hash Attacks – Once malware has your password hash they can: • Extract password hashes of local accounts • Extract password hashes of interactive users with AD accounts • Plus others Disable IPv6 – Until You Need It • Why Disable IPv6? – We want to shrink our attack surface • Why Not Disable IPv6? – Microsoft DirectAccess requires it (kind of) – Microsoft doesn’t test their patches on systems with IPv6 disabled Group Policy is basically a large enterprise scale registry editor! JUST REMEMBER Contact Info • Name: Josh Rickard • E-Mail: rickardj@Missouri.edu • Blog: http://MSAdministrator.com • Twitter: @MS_dministrator