Percent of non-domain computers reporting infections
2.5%
2.0%
1.5%
1.0%
0.5%
0.0%
Enabled
No protection
Off
Expired
Out of date
1,800
1,600
M edium (4–6.9)
1,600
Low complexity
(highest risk)
M edium complexity
(medium risk)
1,200
1,000
High (7–10)
800
600
400
Low (0–3.9)
200
0
Industrywide vulnerability disclosures
Industrywide vulnerability disclosures
1,400
1,400
1,200
1,000
800
600
400
200
High complexity
(lowest risk)
0
2H11
1H12
2H12
1H13
2H13
1H14
2H11
1H12
2H12
1H13
2H13
1H14
14%
12.6%
Pecent of all vulnerability disclosures
12%
11.4%
11.3%
10.6%
10%
8.0%
8%
7.1%
5.9%
6%
4.6%
4%
3.1%
2.5%
2%
0%
Oracle
Debian
Red Hat
Canonical
Cisco
IBM
Microsoft
Apple
Google
Mozilla
Encounter rate (percent of all reporting computers)
3.0%
Exploit kits and
other HTM L/ JS
2.5%
2.0%
1.5%
1.0%
Java
Operating system
0.5%
0.0%
3Q13
4Q13
1Q14
2Q14
Other
Documents
Adobe Flash (SWF)
Browser
Encounter rate (percent of all reporting computers)
30%
25%
Nondomain
20%
15%
10%
Domain
5%
0%
3Q13
4Q13
1Q14
2Q14
Encounter rate (percent of all reporting computers)
9%
8%
7%
6%
5%
4%
Domain
Non-domain
3%
2%
1%
0%
Trojans
Worms &
Viruses
Adware
Exploits
Downloaders Obfuscators & Backdoors
& Droppers Injectors
Password
Stealers &
Monitoring
Tools
Other
Malware
Browser
Modifiers
Ransomware
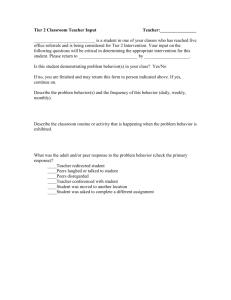
Metric
3Q13
4Q13
1Q14
2Q14
Encounter rate, Australia
16.5 %
13.5%
13.0 %
11.7 %
Worldwide encounter rate
24.0%
21.4%
21.3%
19.1%
CCM, Australia
4.3
5.7
5.2
3.6
Worldwide CCM
7.5
9.7
10.8
7.2
Percent of all reporting computers (encounter
rate)
1
2
Infection rate
25%
10
20%
8
15%
6
10%
4
5%
2
0%
0
3
Australia
4
1
Worldwide
2
3
4
Computers cleaned per 1,000 scanned (CCM)
30%
Encounter rate
12
Percent of all reporting computers (encounter rate)
8%
7%
6%
5%
4%
3%
2%
1%
0%
1
2
3
4
Series1
Series2
5
6
7
8
9
10
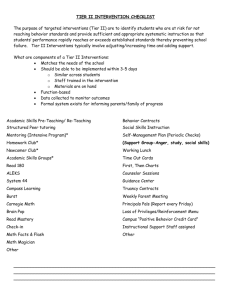
Massive Shift
In Thinking
“Not a target” or “We’re Secure”
To
Assume Breach
Typical Attack
Timeline &
Observations
Profile of an
attack
% Degradation of
Operational
Effectiveness
Recon
Escalation
Detection
Recovery
Recovery
Initiated
Penetration
Attacker Work Factor
Protect
Protect. Detect. Contain. Recover.
% Degradation of
Operational
Effectiveness
Effect of Protective
controls increasing
the work factor for the
attacker
Attacker Work Factor
Detect
Protect. Detect. Contain. Recover.
% Degradation of
Operational
Effectiveness
Effect of
detective
controls
enabling a
more rapid
response
Attacker Work Factor
Contain
Protect. Detect. Contain. Recover.
% Degradation of
Operational
Effectiveness
Effect of containment
controls reducing the
impact of an attack
Attacker Work Factor
Recover
Protect. Detect. Contain. Recover.
% Degradation of
Operational
Effectiveness
Effect of recovery
controls decreasing
the time to initiate
recovery and
improving the rate of
recovery
Attacker Work Factor
Putting it All
Together
Protect. Detect. Contain. Recover.
% Degradation of
Operational
Effectiveness
Contain
Protect
Attacker Work Factor
What’s Hot
and Relevant
•
•
•
•
Initial Exploitation - EMET
Escalation - Credential Theft
Detection – Needles in the haystack
Exec Scorecards – Top 4 ASD
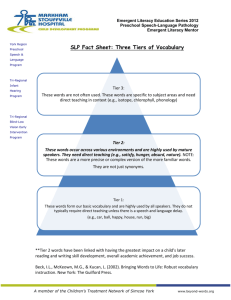
EMET
2013 0-day Vulnerabilities mitigated
2014 0-day Vulnerabilities mitigated
Vulnerability
Affected
Software/component
Security
Bulletin
EMET Mitigated
CVE-2014-1776
Internet Explorer
MS14-021
Yes
CVE-2014-1761
Microsoft Word
MS14-017
Yes
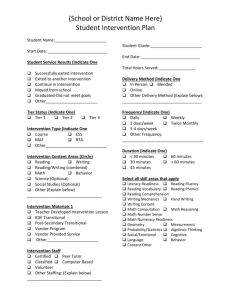
Credential
Theft
Administrative Model and Security Model
• Administrative model
• Control subjects should have over objects
• Uses normal/authorized tools
• Security model
• Control subjects actually have over objects
Control Restrictions
Tier 0
Same Tier
Control
Tier 1
Lower Tier
Control
Higher Tier
Control
Tier 2
Blocked
Only as required
by role
Tier Model Logon Restrictions
Tier 0
Same Tier
Logon
Tier 1
Higher Tier
Logon
Lower Tier
Logon
Tier 2
Blocked
Only as required
by role
Detect
Must Use On
Windows
Summary and
Take Away
• Leverage the SIR v17
• Focus on Increasing the workload of the attacker –
continue to focus refine the basics
• Do you have the right balance across Protect/ Detect/
Contain and Recover?
• Think “Agile security” – incremental improvement
• Always start any activity with “Assume breach”
scotde@microsoft.com
© 2012 Microsoft Corporation. All rights reserved. Microsoft, Windows, Internet Explorer, and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries.
The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of
Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.