Chapter 10 Security
advertisement

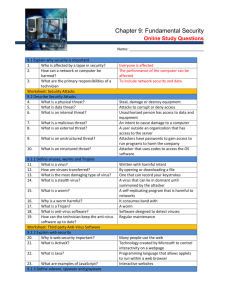
PC Support & Repair Chapter 10 Security Objectives • After completing this chapter, you will meet these objectives: ▫ ▫ ▫ ▫ Explain why security is important. Describe security threats. Identify security procedures. Identify common preventive maintenance techniques for security. ▫ Troubleshoot security. Why is Security Important? Describe Security Threats • • • • • • • • Define adware, spyware, and phishing. Define viruses, worms, Trojans, and Rootkits. Explain web security. Explain Denial of Service (DoS). Describe spam and popup windows. Explain social engineering. Explain TCP/IP attacks. Explain hardware deconstruction and recycling. Malware • Software to create malicious acts ▫ Adware, spyware, grayware, viruses, worms, Trojan horses, rootkits • Usually installed without user knowledge • Open extra windows, changes computer’s config, redirect browser, collect info, etc. Adware • Displays ads on computer ▫ Usually in pop ups ▫ Pops up faster than you can close • Comes in software you download Spyware • Similar to adware • Distributed w/out you knowing • Monitors computer activity ▫ Sends info to creator Grayware • Similar to adware • May be malicious • Sometimes installed WITH your consent ▫ Downloading software that installs a toolbar that displays ads or tracks your web history Phishing • Pretends to be legit ▫ Bank • Email, phone, or text contact ▫ Ask to verify password or account to prevent something bad from happening ▫ Through link to real-looking web page Try This… Virus • Malicious intent • Spreads by email, file transfer, IM • Attached to software, documents, or code ▫ Some can lay dormant • Executes when program runs/opens ▫ Can corrupt or delete files ▫ Some capture keystrokes Worm • Self-replicating program • Duplicates across network w/out you knowing ▫ Doesn’t need to attach to program • Ties up bandwidth of network ▫ Can’t perform normal network functions Trojan Horse • Hidden in software ▫ “Appears” to be something good • Can reproduce & spread ▫ Loss of data ▫ Infect other computers Virus, Torjan, Worm Anti-Virus Software • Can detect, disable, and remove viruses, worms, and Trojans • YOU must be sure to apply updates (virus signature files), patches, etc. • Have a security policy at company • Maintenance schedule • Make employees aware of opening email attachments • Name some AV software Rootkits • Malicious program • Gains full access to computer • Uses known vulnerability or password to get admin access • Is able to hide the files, registry edits, and folders that it uses from detection by typical virus or spyware programs ▫ Very difficult to detect because it has the rights to control and modify security programs • May have to reinstall OS to get rid of it Review- 4Q • What places ads on the desktop without you doing anything? ▫ Adware • Name two types of malware. ▫ Adware, spyware, grayware, virus, worm, Trojan, rootkit • What program is self-replicating? ▫ Worm • How do you make sure your AV software can protect you from the latest viruses? ▫ Download the latest virus updates Review- 3Q • Which attack comes by email and directs you to a web page to enter personal info? ▫ Phishing • Which software is installed on your computer w/out your knowing when you download a program and it displays product “windows” on the screen? ▫ Adware • What ties up the networks bandwidth? ▫ Worm Web Security • Certain useful web tools can be exploited ▫ ▫ ▫ ▫ ▫ ActiveX Java JavaScript Adobe Flash Microsoft Silverlight • Browsers set to “ask” you to authorize when you encounter these Web Security • Pop-up blocker • SmartScreen Filter ▫ Detects phishing sites, analyzes sites for suspicious items, checks sites & downloads a list of sites and files that are known to be malicious ▫ In IE, on by default InPrivate Browsing • Prevents the browser from storing : ▫ ▫ ▫ ▫ ▫ ▫ Usernames Passwords Cookies Browsing history Temporary Internet files Form data Spam • Unsolicited junk mail • Can include harmful links, malicious programs, or other bad content • Email/AV software can detect it ▫ ▫ ▫ ▫ No subject line Incomplete return address Computer generated e-mail Return e-mail not sent by the user Denial of Service (DoS) DoS/ DDoS • Prevents users from accessing services on network ▫ System is busy responding to the large amounts of requests; Resources get overloaded & shut down • PING OF DEATH ▫ Many, large pings • EMAIL BOMB ▫ Large amounts of bulk email overloads server • DDoS ▫ Uses infected “zombie” computers to launch attacks ▫ Zombies are all over the place; can’t trace attack DoS Other Attacks through TCP/IP • Spoofing ▫ Gains access to resources on devices by pretending to be a trusted computer ▫ Uses forged IP/MAC • Man-in-the-middle ▫ Intercepts or inserts false information in traffic between two hosts Other Attacks through TCP/IP • SYN Flood ▫ A SYN request initializes TCP communication ▫ This ties up the server by it replying to nothing Social Engineering • Person who can gain access to equipment or network by tricking people ▫ Get their username/password • Pretend technician, Look over shoulders, Look through desks, Hardware Destruction • Data wiping ▫ Used to remove sensitive data Formatting is not enough ▫ Overwrites data multiple times • Hard drive destruction ▫ Shatter platters with hammer ▫ Shred CD’s & floppies • Hard drive recycling (no sensitive data) ▫ Format & reuse or donate Review- 3Q • A visitor at your work looks over your shoulder & sees your password. They then go home & use it to access the network. What is this called? ▫ Social engineering • Which attack uses zombies all over to overwhelm/flood servers? ▫ DDoS • The IRS is replacing their computers. What should you do to the old hard drives to protect any sensitive data before you recycle the PC’s? ▫ Destroy with a hammer Review- 3Q • Which attack tricks you into entering your personal info through email and a spoofed web site? ▫ Phishing • What is the proper way to remove personal data from a hard drive that does not contain sensitive info? ▫ Data wiping • What attack gets the info before it gets to its destination? ▫ Man-in-the-middle Security Policy • Includes: ▫ An acceptable computer usage statement for the organization. ▫ The people permitted to use the computer equipment. ▫ Devices that are permitted to be installed on a network, as well as the conditions of the installation. Modems and wireless access points are examples of hardware that could expose the network to attacks. ▫ Requirements necessary for data to remain confidential on a network. ▫ Process for employees to acquire access to equipment and data. This process may require the employee to sign an agreement regarding company rules. It also lists the consequences for failure to comply. • Should describe how to address security issues Project • 10.2.1.2 • Do as a class Username & Password • Change defaults • Use a naming convention for users ▫ EX: jsmith • Don’t use other users login info 3 Levels of Passwords to Protect Data • BIOS password ▫ Prevents BIOS changes & OS access • Login password • Network password Password Requirements • Should contain a mix of upper/lower case letters, numbers, and symbols • Should expire/change after a specific period of time • Lockout rules apply after unsuccessful attempts • Rules should state: ▫ Username naming convention (jsmith) ▫ When passwords expire & when they will lockout • Standards should prevent users from writing down passwords and exposing them to public view Protect Data • Firewall ▫ Allows/denies traffic to & from network • Smart Card ▫ Plastic card with chip ▫ Stores information • Biometrics ▫ Fingerprint, eye, facial, etc. • Key fob Data Backups • Full weekly or monthly ▫ Then frequent partial • Should be stored off-site • Protect backup with password Data Encryption- EFS • EFS (Encrypting File System) in Windows ▫ Can encrypt files or folders ▫ Can only be opened by the user who encrypted them or by an administrator ▫ Right-click on file/folder, Properties, Advanced, Encrypt Data Encryption- BitLocker in Windows • Used to encrypt entire hard drive ▫ 1st- initialize TPM in BIOS ▫ 2nd- turn on BitLocker in CP Security • Windows 7 uses BitLocker on Ultimate & Enterprise ▫ Needs a TPM (Trusted Platform Module) on the motherboard to store the encrypted keys OR a flash drive to store the keys • BitLocker is 128-bit encryption • Windows 7 BitLocker can be used for flash drives too ▫ Right-click on the drive and enable BitLocker Review- Q Protection • Virus protection ▫ An antivirus program runs automatically in background & monitors for problems ▫ When virus is detected, user is warned & program attempts to quarantine or delete virus • Spyware protection ▫ Antispyware programs scan for keyloggers, which capture your keystrokes, and other malware so that it can be removed • Adware protection ▫ Anti-adware looks for programs that display ads on computer • Phishing protection ▫ Antiphishing programs block the IP addresses of known phishing websites and warn you about suspicious websites The Rogue Antivirus • The AD that says you have a virus • Looks like a Windows warning • DON’T CLICK ANYTHING! ▫ Close tab/browser/Alt+F4 Removing a Virus • Identify what’s happening • Disconnect from the network • Boot to Safe Mode & scan (or install AV) ▫ May need Safe Mode with Networking ▫ Use other tools • Delete system restore files after cleaned • Customer in a hurry? ▫ Remove HD & connect to external dock ▫ Copy data they need to another PC Signature File Updates • Get your updates for your AV software • Auto update Review- Q Wireless Security • SSID (Service Set Identifier) ▫ Name of wireless network ▫ Change & disable the broadcast • MAC address filter ▫ Only listed MAC addresses allowed/prevented • Encrypt & authenticate data ▫ WEP (weak) ▫ WPA (better) ▫ WPA2 (best) Use TKIP or AES Project • PT Lab 10.2.4.5 ▫ Configure WPA2 in the Linksys WRT300N ▫ Configure MAC Filtering in the Linksys WRT300N ▫ Configure Single Port Forwarding in the Linksys WRT300N • Wireless Lab ▫ Configure WAP ▫ Set up MAC Filtering Review • A fingerprint reader is what kind of security? ▫ Biometrics • Which wireless security should you use when you have all Cisco equipment? ▫ LEAP • Where should backups be stored? ▫ Off-site • How should a telecommuter send secure data to the company while traveling? ▫ Through a VPN Review • To secure your wireless network you should disable this & enable this… ▫ Disable the SSID broadcast ▫ Enable WPA encryption • T or F. Passwords should be text only. • T or F. You should set a password lockout rule. • What hardware/software security method on the motherboard supports storing encryption keys, digital certificates, and passwords? ▫ TPM Review • What was the 1st wireless encryption, which is also the weakest? ▫ WEP • This Cisco encryption is just as strong as WPA2. ▫ LEAP • What security method has a chip on a card? ▫ Smart Card • What wireless security method will ensure ONLY your computers are accessing the network? ▫ MAC address filtering Protecting Equipment • Physical ▫ ▫ ▫ ▫ ▫ Cable locks Locked rooms Security cages Alarms Web cams • Access ▫ Card keys ▫ Biometrics ▫ Security guards Activity Installing Patches & Service Packs • Usually to fix security holes ▫ Windows XP had a lot of them! 1. 2. 3. 4. 5. Create a restore point Check for updates Download Install Make sure it works Data Backups • Use Windows Backups, manual or scheduled • Backup & Restore in CP Troubleshooting • Complete Handout Summary • Security threats can come from inside or outside of an organization. • Viruses and worms are common threats that attack data. • Develop and maintain a security plan to protect both data and physical equipment from loss. • Keep operating systems and applications up to date and secure with patches and service packs. Review- 11 Questions PC Support & Repair Chapter 10 Security