Corporate Compliance and HIPAA Training
advertisement

Corporate Compliance
HIPAA Privacy
HIPAA Security
Training Objectives…
To Help:
– Bridge the Gap Between Ethics & Compliance
– Find Ways to Place Regulatory Theory into Practice
– Heighten Awareness of Non-Compliant Activities
Reality check…
Rules provide a set of expectations towards an expected
end…
…they serve as a roadmap for direction
The healthcare industry is full of…
RULES & REGULATIONS
But they do serve a purpose!
FEDERAL COSTS
As noted by Withrow (1999):
• Healthcare expenditure = >$1 trillion/per year
• Healthcare billing fraud = $100 billion/per year
Compliance as a buzz word
It’s really about doing the right thing.
…Liken it to an ethical responsibility.
Practice of Clinical Medicine
• Requires a strong knowledge-base of practical
issues that can result in:
–
–
–
–
–
–
Informed Consent
Truthful Communication
Confidentiality
End of Life Care
Pain Relief
Patient Rights
(HCCA,2004)
SBUH Responsibility
Organizations should find the right balance between compliance
and integrity.
“Must do ” vs. “Ought to do ”
LET US LOOK at CASE EXAMPLES
Case # 1
Mr. Cope was admitted for inpatient treatment of obesity with a
protein-sparing modified fasting regimen. He was found
repeatedly in the cafeteria, cheating on the diet. His physician
made reasonable efforts to persuade him to change his behavior.
How should the physician handle this situation?
Response
It would be ethically permissible for the physician to abandon
therapeutic goals and to discharge the patient from the
Hospital. These goals are unachievable because of the
patient’s failure to participate in the treatment program.
(Jonsen, Siegler & Winslade, 1998)
Case # 2
A resident authorizes a medical student to obtain and
document the history and condition of a patient
without supervision. The resident then tells the student
to write a progress note and leave it unsigned.
Is there a compliance implication?
Response
Medical students are not considered residents under the
Medicare guidelines. Therefore, to meet the billing
requirements under PATH, services involving medical students
are only billable when performed in the physical presence of an
attending physician, or jointly with a resident.
Case # 3
Dr. Brown supervised resident physicians during the
hours of 8am and 10am on Monday morning.
Is Dr. Brown allowed to bill Medicare for services that
he provides to these patients?
Response
Graduate Medical Education (GME) is reimbursed under
Medicare Part A. Private physician services are reimbursed
under Medicare Part B. If Dr. Brown is unable to define the
line between where his academic, teaching activities end
and where his private physician activities begin, then billing
under Medicare Part B will be considered double-dipping,
which is a fraudulent billing practice.
Case # 4
Dr. Martin has just become a part-owner of XYZ
Clinical Laboratories. She intends to refer all of
her patients to this facility.
Are there any compliance implications for this type
of activity?
Response
This situation creates a conflict that violates the Stark Law; a
federal, civil prohibition. Under Stark a physician is not allowed
to self-refer to an entity in which the physician or an immediate
family member may have a financial interest.
The federal government initially surveyed Medicare patient
clinical laboratory referrals and found that when the doctor had
a financial interest in the facility, referrals were 65% higher
than for non-Medicare patient referrals.
Conflicts of Interests
• The Ethics Law and SBUH policy prohibit situations
that can create a conflict of interest.
A Conflict of Interests Arises…
…when a person’s judgment and discretion is
or may be influenced by personal
considerations, or if the interests of SBUH
are compromised.
Examples include:
1. Accepting gifts from vendors
2. Misuse of Hospital assets
3. Activities that violate principles governing
research
What is a Gift?
According to the NYS Ethics Commission a gift may
be in the form of:
•
•
•
•
•
•
•
Money
Loan
Travel
Meal
Refreshment
Entertainment
Any Good or Service
Violations of Ethics Law…
With regard to gift taking, NYS employees are not
allowed to accept gifts valued above nominal Value
For example, coffee mug, pads, pens, key tags,
lanyards, jar grip openers, magnets business
Cards, retractable tape measures, etc.
Penalties imposed by the Ethics Commission
are up to $10,000/per incident.
ABOUT CODING AND
DOUMENTATION
Evaluation and Management/E&M codes…
• Are categorized by place of service
(i.e. Hospital, Office, ER, etc.)
• Provide definitions for new and established patients
• Begin with “99” and are 5 digits in length
• Require history, physical examination and/or medical decision
making
• Describe the “Who, What, Where, and Why”
Accurate billing = diagnosis code + procedure code
These two elements should be in harmony.
Documentation is Key…
Medicare says…
“…If it’s not documented then it didn’t
happen.”
FACT:
Documentation must always support the
billing for a claim.
EXAMPLE
A patient is admitted to a unit after complaining of pain in
his left arm.
Any tests ordered should support this condition.
Without proper documentation an order for an MRI of
the brain would be questionable.
Down the Pipeline…
Billing codes are based on the documentation
Codes that don’t match will raise a flag!
Implications
> Rejected/Denied claims
> Possible audit of the organization
Consequence
> Increased governmental scrutiny
> Fines
> Loss of revenue
> Service and staffing cuts
> Loss of privileges
> (i.e., exclusion from the Medicare Program)
The Joint Commission is…
A private agency entrusted by Medicare to certify
that healthcare organizations meet a set of
established standards. These criteria are
incorporated in:
Medicare’s Conditions of Participation
The formula:
Delivery of quality healthcare services
+
Imposition of governmental mandates
+
Cost-cutting measures by insurance carriers
+
Accrediting body rules
= Guidance for Clinical Practice
Patient Choice vs. Patient Consent
1) Patient consent:
– Patient agrees to a proposed course of treatment by
medically authorized personnel.
It is best to have consent in writing
Patient Choice vs. Patient Consent
2) Patient choice:
– Preferences are based on patient values and personal
assessment of benefits and burdens.
(HCCA, 2004)
Patient choice… What to ask?
Physicians should ask…
1.
2.
3.
What does the patient want?
What are the patient’s treatment goals?
Is the patient’s right to choose being respected?
• Physicians are challenged when patients fail to
accept or cooperate with a medical
recommendation. However…
• “Clinicians should not be expected to render
treatment that is illegal or contradictory to the
recognized standard of care” (HCCA, 2004)
Beyond the Hippocratic Oath
Professional Ethics for Residents must include
adherence to the following doctrines:
– Medical Necessity
– Physicians at Teaching Hospitals (PATH)
PATH
Teaching Physicians:
– Are required to be present during complex procedures
– Must be available to furnish all procedures for Medicare
patients
PATH Constraints
FACT:
The inherent nature of academic medical center (AMC)
operations preclude attending physicians from being present
in every situation.
Deficit Reduction/False Claims Act
• Federal and State Laws:
• Imposes penalties and fines on INDIVIDUALS and ORGRANIZATIONS that
file false or fraudulent claims for payment from Medicare, Medicaid or
other federal health programs.
• NYS False Claims can be Civil and or Criminal
• Both provide Whistleblower protections
–
–
An employer MAY NOT take retaliatory action against an employee if the employee
discloses information about the employer’s policies, practices or activities to a regulatory,
law enforcement or other similar agency or public official.
The employee’s disclosure is protected only if the employee FIRST brought up the matter
with a supervisor (departmental chain or command) and gave the employer a reasonable
opportunity to correct the alleged violation
Compliance is more than…
Adherence to regulatory requirement (i.e.):
•EMTALA
•Medicare & Medicaid Regulations
•HIPAA
•Anti-Kickback & Stark Law(s)
•Deficit Reduction/False Claims Act(s)
HIPAA & HITECH REGULATIONS
Stephanie Musso, SBUH HIPAA Privacy Officer
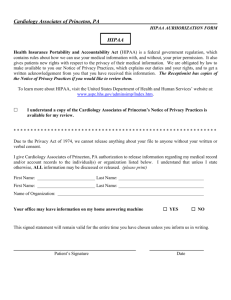
What is HIPAA?
Health Insurance Portability and Accountability Act of
1996
Focus: Title II
Addresses the privacy (4/14/03) & security (4/20/05) of
health care information
Guaranteed individuals’ rights
Establish national standards for e-health care transactions
Reduce health care fraud and abuse
What is HITECH?
• On February 17, 2009 the Federal Stimulus Bill or
American Recovery and Reinvestment Act (ARRA) was
signed into law and included provisions to address Health
Information Technology For Economic and Clinical Health
Act (HITECH).
• Purpose is to create a national health information
infrastructure and widespread adoption of electronic
health records through monetary incentives.
• Provide enhanced Privacy & Security Protections under
HIPAA including increased legal liability for noncompliance and greater enforcement.
Who must comply?
Organizations Involved in the Provision of Healthcare
Services
Individuals Involved in the Delivery of Healthcare Services
Under the HITECH Act 2009 Business Associates are now
held to the same regulatory requirements as the health
care provider they do business with.
What are the HIPAA Privacy and
Security Rules Protecting?
PHI = Protected Health Information
Any form of information that can identify, relate or be
associated with an individual obtaining healthcare services
and can be electronic, hard copy or verbal.
What Constitutes PHI?
Personal Information
Name, Address, Phone Number, Fax Number, E-mail Address. Dates:
Birth/Death, Admission/Discharge, Procedure/Surgery. Numbers:
SSN, Certificate/License Number, Automobile/Vehicle Identifiers
Medical Information
Medical Record Number, Health Plan Information, Test Results,
Clinical Notes and Procedural Information, Care Plans, Diagnoses
Technical Information
All of the above in electronic format and Biometric Identifiers (finger or
voice prints), Full-Facial Photographic Images, Device Identifiers/Serial
numbers, Web URL’s, IP addresses, Account Numbers
The information can be written, verbal or electronic
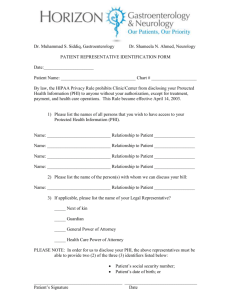
Patient Rights
Receive Notice - Inform them how their health information is being
used and shared – Joint Notice of Privacy Practices (JNPP)
Restrict - Decide whether to give permission before their information
can be used or shared for certain purposes other then treatment,
payment or operations (opt-out)
Access - Ask to see and get a copy of their health records
Amend - Ask to have corrections added to their health information
Accounting - Request a report on when and why their health
information was shared
File a Complaint - If they believe their PHI was used or shared in a way
that is not allowed under the privacy law or they were not able to
exercise a right.
How is HIPAA Enforced?
• Civil monetary penalty:
Civil penalty for inadvertent violation = fines of $100/per
incident up to $25,000/per year for each similar offense.
EXAMPLE
A hospital employee violates HIPAA by misdialing a fax
number and sending 100 patient records to Starbucks.
The hospital & the employee may have to pay a $10,000
($100 X 100) fine.
Worse Case Scenario…….
• Criminal Penalties :
Criminal penalties = large fines + jail time, and increase
with the degree of the offense.
Example:
A hospital employee steals and sells patient information
for personal profit. Criminal penalties could be as much
as $1.5 million and/or 10 years in jail.
What Must I Do?
• Maintain Confidentiality:
Find private locations to discuss patient information
Always Close doors & pull privacy curtains
Do Not discuss patient information in public places
Use, disclose & access only the Minimal Necessary
Leave generic messages on patient answering machines…
”This is Dr. Smith calling for Mr. Jones please call me at 444-XXXX at your earliest convenience”
Direct ALL media inquiries to the Public Affairs Office
Discard ALL material containing PHI in the Confidentiality Bins
(paper, whole binders, folders, scrap notes, computer disks & CD’s)
Do Not leave any materials containing PHI open to public viewing
LOG-OFF computers when you have completed your task
DO NOT leave handheld devices, PDAs or laptops unattended
Use your unique user ID and password and DO NOT share ID/Passwords
DO NOT send PHI over the internet or via e-mail including file attachments
in an e-mail outside of the UHMC – Lotus Notes Network
Do Not Snoop (neighbors, friends, relatives, immediate family members,
colleagues)
When in doubt ask the HIPAA Privacy Officer at 4-5796.
What changes can I expect under HITECH?
• Effective September 23, 2009 Breach Notification is
required for any unauthorized acquisition, access, use or
disclosure of “unsecured” PHI (PHI that is not secured through the use of
a technology or methodology specified by the Secretary of HHS > encryption or
destruction). Notice Requirements > Patient, Secretary of HHS
• Business Associates of a Covered Entity are held to the
same standards and are liable under the HITECH Act.
Business Associate Agreements must be updated to
include HITECH provisions. (SUNY effective July 1, 2009)
• Accounting of Disclosures from the electronic medical
record to now include treatment, payment and healthcare
operations for up to a 3 year period.
What changes can we expect?
Continued…
• Patient’s can get a copy of their record in an electronic
format and can request we send it to their PHR provider.
• Individually Directed Privacy Restrictions – patient pays
out-of-pocket in full for services can restrict all disclosures
• Restrictions on Marketing, Fundraising and the sale of PHI
• Preference for Limited Data Sets and De-Identified Info
• Clarification on Minimum Necessary guidance expected 8/17/10
• Enforcement and New Penalties – Increased enforcement
and oversight activities; CE’s and individual subject to
criminal provisions; State AG’s can bring civil suit in
Federal Courts on behalf of state residents; harmed
individuals can receive a % of CMP’s or settlement
Outpatient Services
• Be aware that many of our Physician Practices are
maintaining outpatient health care records
• Several Physician Practices are using some form
of electronic outpatient health care record
• These records are governed by the same
Privacy/Security Regulations defined by the HIPAA
Rule and NYS Law
• SBUH HIM department provides guidance to the
physician practices in order to ensure compliance
with HIPAA and NYS Regulations
Myth or Fact
A doctor's office can send medical records of a patient to
another doctor's office without that patient's
authorization.
Fact
Authorization is not necessary for one doctor's office to
transfer a patient's medical records to another doctor's
office for treatment purposes.
However, an ancillary service department (Radiology,
Laboratory) can not send a report to a physician who calls
in a request if they are not the ordering physician or the
patient did not request at the time of the testing the
additional physician(s) who should receive the report.
Myth or Fact
A hospital is prohibited from sharing information with the
patient’s family without the patient’s authorization.
Myth
Under the Privacy Rule, a health care provider may
“disclose to a family member, other relative, or a close
personal friend of the individual, or any other person
identified by the individual” , the medical information
directly relevant to such person’s involvement with the
patient’s care or payment related to the patient’s care.
What we should not be doing is providing information
related to the patient’s past medical history, only
information pertinent to his/her present condition.
Myth or Fact
A patient’s family member can no longer pick up
prescriptions for the patient.
Myth
Under the Regulation, a family member or other individual
may act on the patient’s behalf to pick up: prescriptions,
medical supplies, X-rays or other similar forms of
protected health information (appropriate authorization by
the patient must have been obtained – medical records).
Myth or Fact
A patient can not sue me if I violation HIPAA
Myth
HIPAA does not provide for a private right to sue.
However, under HITECT States AG can bring civil action in
federal court on behalf of the residents of his/her state
who have been or are threatened to be adversely affected
by a HIPAA violation.
Myth or Fact
The press can access information from hospitals about
accident or crime victims.
Fact
• HIPAA allows hospitals to continue to make public
(including to the press) certain patient information:
including the patient’s location in the facility and condition
in general terms - unless the patient has specifically opted
out of having such information made publicly available.
Scenario # 1
Two physicians are discussing a patient’s treatment in an
elevator filled with people. During the conversation, the
physicians mention the patient’s name.
Is this a HIPAA violation?
What steps should the physicians have taken to safeguard
the patient’s privacy?
Response
• Yes, this is a HIPAA violation
The physicians should have held this conversation
in a private location.
This is not considered an “incidental disclosure“.
This is an “inappropriate disclosure” that must be
avoided by utilizing appropriate safeguards.
These safeguards include, but are not limited to,
holding the conversation in a private location,
behind closed doors or in the absence of others
(not in public locations such as elevators,
cafeterias, hallways, etc.).
Scenario # 2
• A physician calls a patient’s home and leaves the following
message with the patient’s wife: “Please tell your husband
that I called in the prescription for his prostate infection
this morning and that he can call the pharmacy to see
when the medication will be ready for pickup.”
Did the physician do anything wrong?
Response
• Yes, this is a HIPAA violation.
The physician must remember to use only the “minimal
necessary” when disclosing patient information (PHI).
This message should have been either a simple “I have
called in a prescription for your husband to his pharmacy.
Have him call me if he has any questions” or better yet
“have your husband call my office.”
Scenario #3
• A physician, after documenting a note in a patient’s
medical record, places the chart in an unlocked chart
holder outside the patient’s room.
Is this a violation of HIPAA’s Privacy Rule?
Response
• No, this is not a HIPAA violation.
The chart must be closed and placed in the appropriate
location whether it is in a chart holder in the nurses station
or in a unlocked chart holder outside the patient’s room.
The responsibility is to ensure that PHI is not left out in the
open and easily assessable for viewing by a passerby. We
must utilize the safeguards that are in place to meet this
expectation - in this case an unlocked chart holder.
Information Security
Health Insurance Portability &
Accountability Act
HIPAA
and related
State & Federal Information Security Laws
Electronic Information Security to Ensure
Privacy, and Trust of Information
Tom Consalvo
Information Security Officer, SBUMC, HSC, and Dental School
Privacy vs. Security
• The Privacy Rule sets the standards for, among other
things, who may have access to PHI, while the Security
Rule sets the standards for ensuring that only those who
should have access to e- PHI will actually have access.
• The Security Rule applies only to e-PHI, while the Privacy
Rule applies to PHI which may be in electronic, oral, and
paper form.
• e-PHI = Electronic Protected Health Information
What is Information Security?
Information Security is the process of protecting data
from accidental or intentional misuse by persons inside
or outside of Stony Brook Hospital
State and Federal Laws as relates to
Information Security
•
•
•
•
•
•
•
•
•
•
•
NYS Cyber Security Policy, P03-002 Information Security
NYS Cyber Security P03-001, Incident Reporting Policy
SUNY Cyber Security Reporting procedure
Federal HIPAA Security regulation 45 CFR Parts 160, 162 & 164
Federal HIPAA Security Guidelines Dec 28, 2006 for Removable Devices
JCAHO Information Management (IM) section 2
NYS Information Security Breach & Notification Act, General Business Law
(Section 899-aa), Technology Law (Section 208)
New York’s Social Security Number Protection Law, General Business
Statutes, Article 26, Section 399-DD
SUNY Minimal Required Actions of a SUNY Campus Information Security
Program. Effective January 2008, Ted Phelps SUNY ISO
HIPAA 45 CFR Parts 160 and 164 Final Enforcement Rule, Feb. 2006
NYS Technology Law, Internet Security & Privacy Act
As part of the daily processes the Hospital must be
ready to be audited at any time, without notice.
HIPAA Security Standards
What is the Security Rule??
Bottom Line: We must assure that systems and
applications operate effectively and provide
appropriate confidentiality, integrity and
availability (CIA).
1. HIPAA asks that organizations to continually look at
themselves to find their vulnerabilities,
2. To continually implement measures to address their
deficiencies,
3. To apply appropriate sanctions against those who do
not comply with the rules they set, and
4. Have the appropriate technology in place to track all
changes that occur.
HIPAA Information Security
• HIPAA Information Security has three
categories
•Administrative
•Physical
•Technical controls
Note: The Federal HIPAA Security Regulation requirements are mappable to the NYS
Cyber & Information Security Law and Policies including JC and the DOH.
HIPAA Administrative Safeguards
■ Designate a Security Officer (Also required by NYS Cyber Security Law)
■ Implement work-force security policies and procedures for
appropriate access to electronic PHI; access authorization; ensure
access level is appropriate; and termination of access.
■ Train the work force in security awareness.
■ Establish procedures to address security incidents.
■ Prepare a contingency plan to permit data recovery and access in the
event of an emergency.
■ Perform periodic evaluations to ensure technical and non-technical
compliance to the code.
■ Create business associate agreements for vendors who need access
to Electronic Protected Health Information (ePHI).
HIPAA Physical Safeguards
■ Facility access controls: Implement policies and procedures
to limit unauthorized physical access to electronic
information systems or facilities.
■ Work station use: Implement policies and procedures for
proper use and physical attributes of the work station and
surroundings.
■ Workstation security: Implement physical policies and
procedures for all workstations that have access to PHI.
■ Device and media controls: Implement physical policies and
procedures that govern the receipt and removal of hardware
and electronic media in and into and out of a facility.
HIPAA Technical Safeguards
• Access controls: Implement technical policies and procedures for
electronic information systems with PHI to allow access only to
those authorized or to authorized software programs as per 164.306
(a)(4).
• Audit controls: Implement hardware, software, and /or procedural
mechanism that record and examine system activity for Electronic
PHI.
• Integrity: Implement policies and procedures to protect health
information from improper alteration or destruction.
• Person or entity authentication: Implement procedures to verify that
a person or entity seeking access to EPHI is the one claimed.
• Transmission security: Implement technical security measures to
guard against unauthorized access to electronically transmitted PHI
over a communications network.
What can be a threat to Information
Security?
•
Natural Disasters
– Hurricane
• LI has had 6 category 3 or above since 1938, last was Sandy in 2012
– Earthquake
• 4.0 in Smithtown in 1985 and 2.8 in Montauk in 1992
– Flood
– Tornado
• F-Zero (40-70 mph) in East Massapequa 2006
– Fire
• Fire In HSC Elevator By Data Center Sept 2006
•
Nonhuman
– Product failures, bugs, etc.
•
Human
– Unauthorized Access
– Data Entry Errors
– Poor Training in Application Use
The Effects of a Compromise
Business Impact
Effects of Attacks
• Loss of revenues or other
assets
• Legal liability (HIPAA)
• Tarnished name, bad press
• Degraded customer service
• Privacy violations
• Lost productivity
• Alter or destroy data
(Integrity of patient data)
• Steal passwords or data
• Damage or disable drives
• Tie up system resources
(Delay treatment)
If You Have Access
To Patient Information System
If the patient is not in your chain of care
Don’t look at their Data
Don’t be curious if you heard that some VIP is in the Hospital
If you are working on 3, don’t look up patients on 9.
Don’t be curious about why your neighbor was admitted.
If you look at patient data that has nothing to do with the
patients you treat…
You are breaking Federal and State Law.
Your New User Accounts
Once you get an account
you are given a unique user name.
Don’t give it out, and most importantly,
Never Share Your Passwords
If you give out your username and password to
someone, You are in violation of Federal and State Law.
If the audit trail comes back to your account, you can be
held liable to sanctions, up to but not limited to fines,
suspension, termination, and criminal prosecution.
Treat your passwords like your toothbrush –
Don’t share them!!!
The best way to protect yourself…
make your passwords difficult to guess
NEVER tell anyone your password.
NEVER write your password down, such as on a post-it note.
Don’t use common info about you or your family, pets, or friends names,
SS #, birthdates; anniversary, credit card number, telephone number, etc.
to create a password.
Don’t use names you have used before, variation of your user ID, or
something significant about yourself as a password.
Don’t let someone see what you are entering as your password.
If you think there is even a slight chance someone knows your password,
CHANGE IT
Remember if someone logs on as you and does something improper,
you can be held responsible.
This can’t be stressed enough…
Weak Passwords (examples):
• Cat, dog, querty hart, heat, heart, mary
• September, superman, mickeymouse, r2d2
• Aaaabbbccd, 12345678, a1b2c3d4
Strong Passwords (examples):
Wweand nadtd
IsfgaWDo6
2BoN2bTist?
3bmstfw1491
What can I use in a Password?
• Use a combination of alphanumeric
symbols consisting of at least 8 letters,
numbers, and symbols.
• Passwords are usually case sensitive so
capitalizing random letters makes it even
harder to guess.
• Alphabetic – A to Z and a to z
• Numeric – 0 to 9
• Special Characters – ~; !: @; #; $; %; ^; & ;
*; (; ); +; =; [; ]; {; }; /; ?; <; >; ,; ;; :; \; |; `; ’;
”; .
Mnemonics Made Easy
• Change them periodically. Take a phrase that is easy
for you to remember and convert it into characters.
• It could be the first line of a poem or a song lyric.
• “Water, water everywhere and not a drop to drink”
(Rhyme of the Ancient Mariner) converts to
Wweandnadtd.
• “We Three Kings from Orient Are” converts to w3KfOa
to get beyond six characters add a number.
• w3KfOa 3691 (3691 is the year 1963 backwards to extend beyond
six.)
Workstation Rules
and Storage of Important Data
You’re provided a computer that belongs to the State of New York or the
Research Foundation and as such it is auditable by Information Security
and SBUMC IT.
Only SBUMC IT may install applications and hardware.
Don’t bring in any games or software from home
Use only approved software
Don’t try to install or download any unauthorized applications.
Licensing violations can cost millions in fines
Bugs and Malware can bring down the network.
All approved applications go through an in-depth testing process.
Don’t save important files to your local hard drive, save to your network
drive (U) or request a secure share.
All requests for computer devices that allow information to be portable (ie:
CD burners, USB drives, PDA’s, laptop computers, etc) must be approved
by the ISO. NO e-PHI should be stored on these mobile devices. Use VPN
Security for USB Memory Sticks &
Storage Devices
Memory Sticks are devices which pack large amounts
of data in tiny packages, e.g., 1G, 4G, 16GB.
NEVER store e-PHI on these memory sticks.
Unless used for external presentations or education
these devices are not allowed.
Use VPN connectivity instead!
Primary Carriers of Malicious Software
• Web pages
• E-mail
• Games
• Freeware /
shareware
• Programs from
associates/home
•
•
•
•
Viruses - A virus is a small piece of software that piggybacks on
real programs in order to run destructive
E-mail viruses - An e-mail virus moves around in e-mail
messages, and usually replicates itself by automatically
mailing itself to dozens of people in the victim's e-mail address
book.
Worms - A worm is a small piece of software that uses
Computer networks and security holes to replicate itself. A
copy of the worm scans the network for another machine that
has a specific security hole. It copies itself to the new machine
using the security hole, and then starts replicating from there,
as well.
Spyware: Computer software that obtains information from a
user’s computer without the user’s knowledge or consent.
Stony Brook Information Security runs many tools
such as Internet browser reporting and filtering.
Social Networking Sites such as Facebook, You-Tube, Twitter, etc are
not permitted unless a business need is defined and approved by the
Information Security Officer.
Email Security
• Email is NOT the same as a letter sent through the normal
mail. It is the electronic equivalent of Postcards!!
• Within SBUH’s Email system messages are encrypted!
• If an e-mail is sent outside of the Stony Brook system (i.e. to
Optonline, AOL, etc…) it is sent in clear text and anyone can
intercept and read it.
• Do NOT use non-SBUH email such as Web Mail (Yahoo, AOL,
Hotmail, etc)to conduct business or send information about a
patient. If you or one of your vendors feels that this must be
done for any reason, call the Help Desk first (631-444-HELP
/444-4357)
E-Mail Security – Cont.
E-Mail Should Never Be Used for:
• Inappropriate and nonproductive material
• The misuse of company resources
• Forwarding of confidential information
REMEMBER
Never open any e-mail
if you don’t know the source.
Security Best Practices
1. Never share your login or password and if you see
someone watching you enter your password, change it.
2. Never browse and look at sensitive information that
you don’t have a need to know to perform your work
responsibilities.
3. Shut down or LOCK your computer at night.
4. Never use Cell Phone Cameras in and around patients
and patient information!
•
•
When leaving your desk log off or:
• Do a CTRL-ALT-DEL
• Then click to “LOCK COMPUTER”
This assures no one can sit down and your desk
and pretend to be you
REPORT SECURITY VIOLATIONS
Report a Security Incident if:
a. You receive an email which includes threats or material that could be
considered harassment.
b. Someone asks you for your password or asks to use your login account.
c. You suspect that someone is inappropriately using confidential data.
d. You discover unauthorized or missing hardware or software.
Compliance Officer - Privacy Officer
Security Officer - University Counsel
Compliance Hotline1-866-623-1480
The SBUH HELP DESK
is here to help!
(631) 444-HELP
If they don’t know,
they’ll assist in pointing you in the right direction.
One of the Hospital’s Most
Valuable Assets is:
The patient information that is stored
electronically!!
Patients, Families and the Community
trust us to protect it!
Good Security Begins with you!!!
You are the first line of defense in
Information Security!!
COMPLIANCE HOTLINE
•1-866-623-1480
• on-line at
• https://www.compliance-helpline.com/sbuh.jsp
• Both Allow for anonymous reporting
COMPLIANCE OFFICE
Located @ 3 Technology Drive, Suite 200
East Setauket, NY 11733-9296
Main Office # (631) 444-5776