Chapter 05 Access Control Lists (ACL)
advertisement

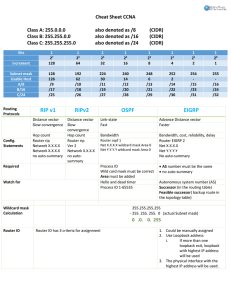
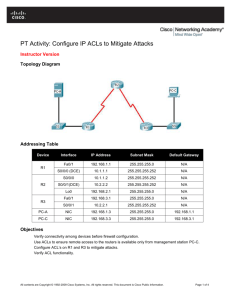
CCNA4
Access Control
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
Perrine /Brierley
Chapter 05
4/9/2020
server
172.16.4.13
Page 1
CCNA4
Access Control
172.16.2.0
Computer
Chapter 05
172.16.4.0
e0
e1
172.16.2.2
172.16.3.1
s0
172.16.3.0
s1
172.16.3.2
Computer
172.16.4.3
Server
172.16.4.2
Perrine /Brierley
4/9/2020
Page 2
CCNA4
High Level View
Chapter 05
A HIGH LEVEL VIEW of ACLs
Perrine /Brierley
4/9/2020
Page 3
CCNA4
Chapter 05
Access Control Lists
Standard
Extended
Perrine /Brierley
4/9/2020
Page 4
CCNA4
Standard Access Control Lists
Chapter 05
ACLs are instructions that are applied to a router interfaces.
The ACLs describe the kind of packets that are to be permitted or denied.
Permitted or Denial testing can be based on:
• source address
• destination address
• port number
ACLs are configured on the router Interfaces to control access to a network.
ACLs must be defined separately for each protocol; Unique for IP, Unique for
IPX; Unique for AppleTalk, etc.
Some times ACLs are called packet filters.
Perrine /Brierley
4/9/2020
Page 5
CCNA4
Standard Access Control Lists
Perrine /Brierley
4/9/2020
Chapter 05
Page 6
CCNA4
Perrine /Brierley
Extended ACLs
4/9/2020
Chapter 05
Page 7
CCNA4
Named ACLs
Perrine /Brierley
4/9/2020
Chapter 05
Page 8
CCNA4
Placing ACLs
Chapter 05
• Standard ACLs should be placed close to the destination.
• Extended ACLs should be placed close to the source.
Perrine /Brierley
4/9/2020
Page 9
CCNA4
Firewalls
Chapter 05
A firewall is an architectural structure that
exists between the user and the outside world
to protect the internal network from intruders.
Perrine /Brierley
4/9/2020
Page 10
CCNA4
Restricting Virtual Terminal Access
Perrine /Brierley
4/9/2020
Chapter 05
Page 11
CCNA4
Summary
Perrine /Brierley
4/9/2020
Chapter 05
Page 12
CCNA4
ACL - Access Control Lists
Chapter 05
Reasons to create ACLs:
• limit network traffic - hence increase network performance
• provide traffic flow - limit traffic through the network
• provide for security
• ACLs establish
•which traffic is blocked
•which traffic is not blocked
Perrine /Brierley
4/9/2020
Page 13
CCNA4
DETAIL
Chapter 05
A MORE DETAILED VIEW of ACLs
Perrine /Brierley
4/9/2020
Page 14
CCNA4
ACL - Access Control Lists
Chapter 05
Cisco IOS checks each packet for:
1.
destination address
2.
source address
3.
protocol
4.
port number
access-list 1 deny 192.169.1.0 0.0.255.255
access-list 1 deny 192.168.1.9 0.0.0.0
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
Each ACL statement is checked in a sequential order (first to last) and when
there is a match, no more statements are checked.
If the results are no matches, then the packet (by default) is discarded.
Adding addition ACL statements to the end of an existing list is just a matter of
adding the new statement. BUT, if
deleting an existing ACL statement causes the entire access list to be deleted.
Perrine /Brierley
4/9/2020
Page 15
CCNA4
ACL - Access Control Lists
Chapter 05
When a packet enters a router’s interface:
“IN” (inbound) checking is required. The packet:
1)
Is checked against the ACL list (if one exists)
2)
Here It can be interrogated to permit or deny.
3)
If denied the packet is dropped else,
4)
It is matched against the routing table and passed to an
“OUT” (outbound interface)
1)
“OUT” (outbound) checking is required.
Here It can be interrogated to permit or deny.
2) If denied the packet is dropped
3) If permitted then packet is allowed “OUT” (outbound).
The Outbound interface’s ACL is a different list from the inbound)
Perrine /Brierley
4/9/2020
Page 16
CCNA4
ACL - Access Control Lists
Chapter 05
ACL statements operate in a logical, sequential order. When a match is made
the rest of the statements are not checked.
If none the ACL statements match, then there is an implicit deny any rule.
access-list 10 { permit | deny } { test conditions }
access-list 10 { permit | deny } { test conditions }
access-list 10 { permit | deny } { test conditions }
access-list 10 { permit | deny } { test conditions }
access-list 1 deny 192.169.1.0 0.0.255.255
access-list 1 deny 192.168.1.9 0.0.0.0
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 10 deny any
access-list 1 permit any
Perrine /Brierley
4/9/2020
Page 17
CCNA4
ACL - Access Control Lists
Chapter 05
Two types of IP ACL :
• standard - has access list value of 1- 99
• extended - has access list value of 100 - 199
Must be configured in global configuration mode. Router (config) #
Steps in creating ACLs:
1) create the ACL (in config mode)
2) apply the ACL to an interface
ACLs are used to filter:
• inbound traffic, or
• outbound traffic
Perrine /Brierley
4/9/2020
Page 18
CCNA4
Where to place ACLs
Chapter 05
Standard ACLs are place as close as possible to the destination.
Extended ACLs are place as close as possible to the source.
Perrine /Brierley
4/9/2020
Page 19
CCNA4
Where to place ACLs
Chapter 05
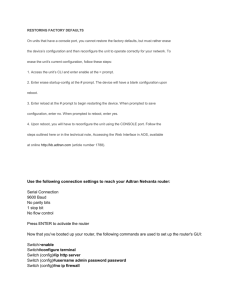
Configuring an Access List:
Router(config)# access-list <ACL number> { permit | deny } { test conditions }
Router(config)# access-list 1 permit { test conditions }
Router(config)# access-list 50 deny { test conditions }
To delete all ACL statements of an access-list
Router(config)# no access-list <ACL number>
Applying the Access List:
At an interface:
Router(config)# int E0
Router(config-if)# { protocol } access-group <ACL number> [IN | OUT]
Out is the default if not mentioned
Router(config-if)# ip access-group 1
Router(config-if)# ip access-group 50
To delete an ACL group statement (this will not delete the associated list):
Router(config)# no access-group <ACL number>
Perrine /Brierley
4/9/2020
Page 20
CCNA4
Wildcard
Chapter 05
A wildcard is matched with an IP address or protocol address.
It is a 32 bit mask divided into 4 octet, each containing 8 bits.
A 0 in the wildcard means to check the bit in the IP you are testing.
A 1 in the wildcard means ignore the bit in the IP you are testing.
NOTE!!!
Do NOT think subnet mask – that is a totally different
meaning not related to the WILDCARD
Perrine /Brierley
4/9/2020
Page 21
CCNA4
Abbreviations
Chapter 05
To permit or deny any address:
0.0.0.0
255.255.255.255
Address
Wildcard
Use the abbreviation any
Router(config)# access-list 1 permit 0.0.0.0 255.255.255.255
Router(config)# access-list 1 permit any
Router(config)# access-list 1 deny 0.0.0.0 255.255.255.255
Router(config)# access-list 1 deny any
Perrine /Brierley
4/9/2020
Page 22
CCNA4
Abbreviations
Chapter 05
To match all the bits of IP address use host:
EX: 172. 30.16. 29 0. 0. 0. 0
Router(config)# access-list 1 permit 172.30.16.29 0.0.0.0
Router(config)# access-list 1 permit host 172.30.16.29
Perrine /Brierley
4/9/2020
Page 23
CCNA4
Standard ACLs
Chapter 05
Criteria:
• block all traffic from a network
• allow all traffic from a network
• deny entire protocol suits
Standard ACLs only check the source address.
Router(config)# access-list <ACL number> { deny | permit } source [ source wildcard] [log]
Perrine /Brierley
4/9/2020
Page 24
CCNA4
Standard ACLs
Chapter 05
What does this statement accomplish?
Access-list 33 permit 172.16.0.0 0.0.255.255 log
Permits all traffic from 172.16.0.0 and sends messages to the console every
time the access list is executed.
Perrine /Brierley
4/9/2020
Page 25
CCNA4
Standard ACLs
Chapter 05
What does this statement accomplish?
Access-list 44 deny 172.16.13.7 0.0.0.0 log
Denies traffic from host 172.16.13.7 and sends message to the console every
time the access list is hit.
Perrine /Brierley
4/9/2020
Page 26
CCNA4
Standard ACLs
Chapter 05
What does this statement accomplish?
Access-list 55 deny 172.16.64.3 0.0.0.255
Denies all traffic from network 172.16.64.0
Perrine /Brierley
4/9/2020
Page 27
CCNA4
Standard ACLs
Chapter 05
The log command:
Prints messages to the console which includes the ACL number, whether
the packet was permitted or denied, the source address, and the number
of packets.
The message is generated for the first packet that matches, and then at
five-minute intervals, including the number of packets permitted or
denied in the prior five-minute interval.
Log is used for debugging only not to be left active on live networks.
Perrine /Brierley
4/9/2020
Page 28
CCNA4
Standard ACLs
Chapter 05
Example of applying the access-list:
Router(config-if)# ip access-group 33 in
Router(config-if)# ip access-group 44 out
Perrine /Brierley
4/9/2020
Page 29
CCNA4
Standard ACLs
Chapter 05
To monitor IP access list: (in EXEC mode)
show access-list
Displays all access lists & their parameters configured on the router.
(Does not show you which interface the list is set on.)
show access-list <ACL number>
Shows only the parameters for the access list <ACL number>. (Does not
show you the interface the list is set on.)
show ip access-list
Shows only the IP access lists configured on the router
show ip interface
Shows which interfaces have access lists set (containing an accessgroup).
show running-config
Shows the routers entire configuration
Perrine /Brierley
4/9/2020
Page 30
CCNA4
Standard ACLs
172.16.3.0
Chapter 05
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
R(config)# Interface e0
R(config-if)# ip access-group 1 out
R(config)# Interface e1
R(config-if)# ip access-group 1 out
R(config)# access-list 1 permit 172.16.0.0 0.0.255.255
What does it do?
Perrine /Brierley
4/9/2020
Page 31
CCNA4
Standard ACLs
Chapter 05
One Access list used by multiple Interfaces
172.16.3.0
172.16.4.0
e0
e1
s0
R(config)# Interface e0
Non-172.16.0.0
server
172.16.4.13
R(config-if)# ip access-group 1 out
R(config)# Interface e1
R(config-if)# ip access-group 1 out
R(config)# access-list 1 permit 172.16.0.0 0.0.255.255
Allows only traffic from source network 172.16.0.0 to be forwarded & and
non-172.16.0.0 traffic is blocked.
Perrine /Brierley
4/9/2020
Page 32
CCNA4
Standard ACLs
172.16.3.0
Chapter 05
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
R(config)# Interface e0
R(config-if)# ip access-group 1 out
R(config)# access-list 1 deny 172.16.4.13 0.0.0.0
R(config)# access-list 1 permit any
What does this do?
Perrine /Brierley
4/9/2020
Page 33
CCNA4
Standard ACLs
172.16.3.0
Chapter 05
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
R(config)# Interface e0
R(config-if)# ip access-group 1 out
R(config)# access-list 1 deny 172.16.4.13 0.0.0.0
R(config)# access-list 1 permit any
Denies traffic from a specific device, 172.16.4.13 & allows all other traffic thru e0 to
network 172.16.3.0.
Perrine /Brierley
4/9/2020
Page 34
CCNA4
Standard ACLs
172.16.3.0
Chapter 05
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 1 out
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
What does this do?
Perrine /Brierley
4/9/2020
Page 35
CCNA4
Standard ACLs
172.16.3.0
Chapter 05
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 1 out
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
Denies traffic from the subnet, 172.16.4.0 & allows all other traffic thru e0 to
network 172.16.3.0.
Perrine /Brierley
4/9/2020
Page 36
CCNA4
Extended ACLs
Chapter 05
Criteria:
• checks both the packet’s source & destination addresses
• check for specific protocol
• check for specific port numbers
• permit or denied applications – pings, telnets, FTP, etc.
•ACL values range between 100 – 199 (for IP)
Perrine /Brierley
4/9/2020
Page 37
CCNA4
Extended ACLs
Port Numbers (decimal)
Chapter 05
IP Protocol
20
FTP data [TCP]
21
FTP program (control) [TCP]
23
Telnet [TCP]
25
Simple Mail Transport Protocol
[TCP] (SMTP)
53
DNS [TCP, UDP]
69
TFTP [UDP]
80
HTTP [TCP]
Perrine /Brierley
4/9/2020
Page 38
CCNA4
Extended ACLs
Chapter 05
Router(config)# access-list <ACL number> { permit | deny } protocol source source-mask
destination destination-mask operator operand {established}
ACL number
100 – 199
permit | deny
Packet is allowed or blocked
protocol
IP, TCP, UDP, ICMP, GRE or IGRP
source -- Source address source-wildcard mask
destination -- Destination address destination-wildcard mask
Continued
Perrine /Brierley
4/9/2020
Page 39
CCNA4
Extended ACLs
Chapter 05
Router(config)# access-list <ACL number> { permit | deny } protocol source source-mask
destination destination-mask operator
operand {established}
operator
lt, gt, eq, neq
Operand
Port number
established
Allows TCP traffic to pass if the packet uses an established connection ( for example, has
ACK bits set ).
access-list 101 permit tcp 172.16.4.0 0.0.0.255 any eq 25
Perrine /Brierley
4/9/2020
Page 40
CCNA4
Extended ACLs
Chapter 05
Configuring an extended ACL to an interface:
Router(config-if)# ip access-group <ACL number> { in | out }
Router(config)# int E0
Router(config-if)# ip access-group 101 in
Perrine /Brierley
4/9/2020
Page 41
CCNA4
Extended ACLs
Chapter 05
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 21
access-list 101 permit ip any any
What does this do?
Perrine /Brierley
4/9/2020
Page 42
CCNA4
Extended ACLs
Chapter 05
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 21
access-list 101 permit ip any any
Blocks FTP traffic from all hosts on 172.16.4.0 to any device on 172.16.3.0 & allows
all other traffic.
Perrine /Brierley
4/9/2020
Page 43
CCNA4
Extended ACLs
Chapter 05
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 23
access-list 101 permit ip any any
What does this do?
Perrine /Brierley
4/9/2020
Page 44
CCNA4
Extended ACLs
Chapter 05
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 23
access-list 101 permit ip any any
Denies only telnet traffic from 172.16.4.0 to 172.16.3.0 network, and permits all
other traffic thru e0 to any address.
Perrine /Brierley
4/9/2020
Page 45
CCNA4
Extended/Standard ACL numbers for IP
Chapter 05
NOTE:
Standard ACL numbers: 1-99;
1300-1999
Extended ACL numbers: 100-199;
Perrine /Brierley
4/9/2020
2000-2699
Page 46
CCNA4
Standard/Extended ACL
Chapter 05
You can not add ACL statements into the body of the access-list
(ONLY at the end of the list).
Otherwise the access list must be deleted first, and then rewritten.
Therefore it is prudent to write your access-list in text format using
“notepad”, and then transfer it to your router.
Perrine /Brierley
4/9/2020
Page 47
CCNA4
Configuring Named ACLs
Chapter 05
NOTE:
• A NAMED ACL is an alphanumeric string instead of the ACL
number (1 - 199 )
• NAMED ACLs are not compatible with Cisco IOS release prior to
Release 11.2
• Named ACLs can be used for either standard & extended
•You cannot configure the same name for multiple ACLs.
•use Name ACL when you want to intuitively identify ACLs
•use Name ACL when you have more than 99 standard & 100
extended ACLs have been configured on a router for a given
protocol
Perrine /Brierley
4/9/2020
Page 48
CCNA4
Configuring Named ACLs
Chapter 05
Router(config)# ip access-list { standard | extended } name { deny | permit } { commands }
ip access-list standard internetfilter
deny 172.10.15.0 0.0.0.255
permit 128.88.0.0 0.0.255.255
permit 36.0.0.0 0.0.255.255
ip access-list extended marketing-group
permit tcp any 171.69.0.0 0.255.255.255 eq telnet
deny udp any 171.69.0.0 0.255.255.255 lt 1024
Perrine /Brierley
4/9/2020
Page 49
CCNA4
Named ACL
Chapter 05
A named ACL will allow the deletion of statements, but will only allow
for the statements to be inserted a the end of the list.
Perrine /Brierley
4/9/2020
Page 50
CCNA4
More Details
Chapter 05
access-list 1 permit 172.16.0.0 0.0.255.255
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx
Matched value
Incoming packet with address of 172.18.4.2. Will it be permitted?
Source :
10101100.00010010.00000100.00000010
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010010.xxxxxxxx. xxxxxxxx Result
Perrine /Brierley
4/9/2020
Page 51
CCNA4
Chapter 05
access-list 1 permit 172.16.0.0 0.0.255.255
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx
Match value
Incoming packet with address of 172.18.4.2. Will it be permitted?
Source :
10101100.00010010.00000100.00000010
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010010.xxxxxxxx. xxxxxxxx Result
Does the result equal the match value?
No! Hence the incoming packet will not be permitted.
Perrine /Brierley
4/9/2020
Page 52
CCNA4
Chapter 05
access-list 1 permit 172.16.0.0 0.0.255.255
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx
Match value
Incoming packet with address of 172.16.4.2. Will it be permitted?
Source :
10101100.00010000.00000100.00000010
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx Result
Does the result equal the match value?
Yes! Hence the incoming packet will be permitted.
Perrine /Brierley
4/9/2020
Page 53
CCNA4
Chapter 05
access-list 1 permit 172.16.0.0 0.0.255.254
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx0
Matched value
Incoming packet with address of 172.16.4.1. Will it be permitted?
Source :
10101100.00010000.00000100.00000001
Wildcard mask: 00000000.00000000. xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx1 Result
Incoming packet with address of 172.16.4.4. Will it be permitted?
Source :
10101100.00010000.00000100.00000100
Wildcard mask: 00000000.00000000. xxxxxxxx. xxxxxxx0
10101100.00010000. xxxxxxxx. xxxxxxx0 Result
Perrine /Brierley
4/9/2020
Page 54
CCNA4
Chapter 05
access-list 1 permit 172.16.0.0 0.0.255.254
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx0
Matched value
Incoming packet with address of 172.16.4.5. Will it be permitted?
Source :
10101100.00010000.00000100.00000101
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx1 Result
So the access list perform what operation? Permits 172.16.4.4, and denies
172.16.4.1 and 172.16.4.5
Permits all even addresses from the network 172.16.0.0
Perrine /Brierley
4/9/2020
Page 55
CCNA4
Permit/Deny BLOCKS of addresses
Chapter 05
One can permit or deny a block of addresses. However, the blocks must be
a power of 2! (Example, 2, 4, 8, 16, 32, 64, 128, etc.)
When you need to specify a range of addresses, you choose the closet
block size for your needs.
You want to block access to part of network that is in the range from
198.16.99.0 through 198.16.99.7. This is a block size of 8. Hence:
198.16.99.0 0.0.0.7
Also in this case for a block of 8, the beginning address must either start at
0, 8, 16, etc.
Perrine /Brierley
4/9/2020
Page 56
CCNA4
Permit/Deny BLOCKS of addresses
Chapter 05
One has a subnet whose addresses range from 200.17.2.128 to 200.17.2.191.
One wants to divide this network so the top half are permitted and the
bottom half is denied to any other network. What is the access lists?
The block range
is:
64
What is the access-list for the bottom?
access-list 101 deny ip 200.17.2.128 0.0.0.31 any
What is the access-list for the top?
access-list 101 permit ip 200.17.2.160 0.0.0.31 any
Perrine /Brierley
4/9/2020
Page 57
CCNA4
Permit/Deny BLOCKS of addresses
Chapter 05
What does this do?
access-list 10 deny 200.16.88.64 0.0.0.63
Denies a block of 64 address starting at 200.16.88.64
Perrine /Brierley
4/9/2020
Page 58
CCNA4
Virtual Terminal ACL
Chapter 05
You can control access via the VTY ports controlling telnet sessions
coming into the router.
You write the ACL as usual, but use access-class to apply it.
As an example:
Router(config t)# access-list 1 permit 172.16.1.0 0.0.0.255
Router(config t)# line vty 0 4
Router(config-line)# login
Router(config-line)# password cisco
Router(config-line)# access-class 1 in
Note: only numbered access lists can be applied to VTY virtual lines!
Perrine /Brierley
4/9/2020
Page 59
CCNA4
Established option
Chapter 05
The ‘establish’ option in an access-list used only with TCP datagrams.
There are cases when you want to stop host B from initiating a
connection with a host A while permitting A to initiate connections with
B.
establish
¾ M a cintos h SE
¾ M a cintos h SE
A
response
B
establish
Perrine /Brierley
4/9/2020
Page 60
CCNA4
Established option
Chapter 05
As a practical example:
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Allow host 172.16.3.13 with Internet connection, but don’t allow the
internet to initialize any sessions.
Perrine /Brierley
4/9/2020
Page 61
CCNA4
Established option
Chapter 05
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Router(config)# int e1
Router(config-if)# ip access-group 101 in
Router(config)# access-list 101 permit tcp any 172.16.3.0 0.0.255.255
established
Perrine /Brierley
4/9/2020
Page 62
CCNA4
Established option
Chapter 05
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Router(config)# int e1
Router(config-if)# ip access-group 101 in
Router(config)# access-list 101 permit tcp any host 172.16.3.13 eq www established
Perrine /Brierley
4/9/2020
Page 63
CCNA4
Established option
Chapter 05
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Note: established argument is limited to tcp which means UDP, ICMP and all
other IP protocols will not match, and will be denied, unless specifically
allowed. Hence
Router(config)# int e1
Router(config-if)# ip access-group 101 in
Router(config)# access-list 101 permit tcp any 172.16.3.0 0.0.0.255 eq www established
Router(config)# access-list 101 permit icmp any any
Router(config)# access-list 101 permit udp any any eq 53
Perrine /Brierley
4/9/2020
Page 64
CCNA4
Where to Place ACLs?
Chapter 05
ACL Rules:
Standard ACL
Place the ACL as near the destination as possible.
Extended ACL
Put the ACL as close as possible to the source
Perrine /Brierley
4/9/2020
Page 65
CCNA4
Chapter 05
Access Lists
Standard
Extended
End of Session
Perrine /Brierley
4/9/2020
Page 66