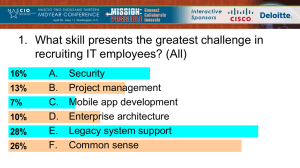
Lecture 1 - Introduction PowerPoint
advertisement

ECE509 Cyber Security : Concept, Theory, and Practice Introduction Spring 2014 • Meet Thursday 4:00pm – 6:50 pm, ECE Bldg, Room 258 • ACL lab is ECE251 • Office hours: 11:00 AM - 12:00 PM Th in ECE356p • Questions via email are encouraged alnashif@ece.arizona.edu • Web site http://acl.ece.arizona.edu/classes/ece509 Topics • Fundamentals of Cyber Security – Network Security, Risk Models and Assessments • Understand Network Attacks – – – – – Scanning / Probe DoS / DDoS attack Worm / Virus / Trojans Spam / Botnet / phishing Insider Attacks • Hardware/Software Security Technologies – Encryption / Authorization/Authentication – Access Control Matrix, Firewall, IDS/IPS, IPSec, Honeypot, etc More Topics • Network Security Monitoring (NSM) – Payload / Session / Connection Level – Active / Passive • Vulnerability Analysis – Operation System – IPv4/v6 – Wireless Network – Layer 2(ARP) – Application (Web, Database) More Topics • Defensive system design – Security architectures – Penetration testing • Labs – Network Scanning – Network Security Monitoring – Firewalls/IDS Recommended References Stallings, William; Brown, Lawrie. Computer Security: Principles and Practice (2nd Edition) Pfleeger, Charles P.; Pfleeger, Shari Lawrence. Security in Computing (4th Edition) Katz, Jonathan; Lindell, Yehuda. Introduction to Modern Cryptography Qian, Yi; Tipper, David; Krishnamurthy, Prashant; Joshi, James. Information Assurance: Dependability and Security in Networked Systems Course Grading • • • • • Homework and Assignments: Midterm Exam: Term paper + Presentation: Term project: Final Exam: 25% 10% 25% 25% 15% Note All information contained in this course information sheet, other than grading policy, may be subject to change. Important Dates • Abstracts for projects and term paper – Feb. 6, 2014 • Midterm – Mar. 13, 2014 • Term paper and presentation – Apr. 24, 2014 • Project Report – May 1, 2014 • Final Exam (24 hour take home exam) – May 1, 2014 Questions for the class Are you comfortable with C, C++, and/or Java? Questions for the class Are you familiar with IP networking? Questions for the class Are you familiar with Operating System? Linux and/or Windows? Questions for the class What is your goal of this class? Prohibited Conduct Students enrolled in academic credit bearing courses are subject to this Code. Conduct prohibited by this Code consists of all forms of academic dishonesty, including, but not limited to: 1. Cheating, fabrication, facilitating academic dishonesty, and plagiarism as set out and defined in the Student Code of Conduct, ABOR Policy 5-308-E.10, and F.1 2. Submitting an item of academic work that has previously been submitted or simultaneously submitted without fair citation of the original work or authorization by the faculty member supervising the work. 3. Violating required disciplinary and professional ethics rules contained or referenced in the student handbooks (hardcopy or online) of undergraduate or graduate programs, or professional colleges. Source: http://deanofstudents.arizona.edu/policies-and-codes/code-academic-integrity Prohibited Conduct 4. Violating discipline specific health, safety or ethical requirements to gain any unfair advantage in lab(s) or clinical assignments. 5. Failing to observe rules of academic integrity established by a faculty member for a particular course. 6. Attempting to commit an act prohibited by this Code. Any attempt to commit an act prohibited by these rules shall be subject to sanctions to the same extent as completed acts. 7. Assisting or attempting to assist another to violate this Code. Source: http://deanofstudents.arizona.edu/policies-and-codes/code-academic-integrity The Average Individual Cost due to Cyber Attack • According to 2013’s Consumer Security Risks Survey, conducted by B2B International and Kaspersky Lab, the average cost of multimedia files that a user might lose as a result of a cyber attack or other damage is estimated at $418. • According to the same survey, “over 60% of users who were victims of malware that either damaged or destroyed data admitted that they had not been able to fully restore their files.” • “in the 16-24 age group would face an average loss of $670, while those in the 25-34 group would incur an average loss of $455; users aged 45 and older would lose an average of $227.” Cyber attacks cost for US Organizations The Ponemon Institute sponsored by HP Enterprise Security Products conducted the “2013 Cost of Cyber Crime Study” that showed “the average annualized cost of cybercrime incurred by a benchmark sample of US organizations was $11.56 million, with a range of $1.3 million to $58 million. That represent a 78% increase since the initial study was conducted four years ago and an increase of 26%, or $2.6 million, over the average cost reported in 2012.” Source: http://www.infosecurity-magazine.com/view/34990/cyberattacks-cost-1-million-on-average-to-resolve/ Cyber attacks cost for US Organizations It also stated: “the time it takes to resolve a cyber-attack has increased by nearly 130% during this same period. The average time to resolve a cyber-attack is 32 days, with an average cost incurred during the resolution period of $1,035,769, or $32,469 per day – a 55% increase over last year’s estimated average cost of $591,780 for a 24-day period.” Source: http://www.infosecurity-magazine.com/view/34990/cyberattacks-cost-1-million-on-average-to-resolve/ Cyber attacks cost for US Organizations “Overall, organizations experience an average of 122 successful attacks per week, up from 102 attacks per week in 2012. Cybercrime cost varies by company size, but smaller organizations incur a significantly higher per-capita cost than larger organizations. Organizations in financial services, defense, and energy and utilities also experience substantially higher cybercrime costs than those in retail, hospitality and consumer products.” Source: http://www.infosecurity-magazine.com/view/34990/cyberattacks-cost-1-million-on-average-to-resolve/ Small Businesses • “Forty-four percent say they have been the victim of a cyberattack – that’s high, and really concerning,” says Molly Brogan, the director of communications for the NSBA. • Of the 44% of businesses that had experienced an attack, 59% say they incurred service interruptions, and 35% say information was falsely sent from their domain names. Nineteen percent say their website was taken down, and 5% say sensitive information and data was stolen. • The NSBA’s 2013 Small Business Technology Survey was conducted in August and surveyed 845 small-business owners, including both NSBA members and non-members. Source: http://smallbusiness.foxbusiness.com/technology-web/2013/09/17/cyber-attacks-cost-small-businesses-nearly-000/ Cloud Attacks • On Oct. 3, 2013, Adobe announced that their Creative Cloud customers database has been the target of a cyber attack which may have compromised the data of some 2.9 million Creative Cloud customers. Healthcare • “A top Homeland Security Department official testified Wednesday that there have been approximately 16 cyberattacks on the HealthCare.gov website and one ‘denial of service’ attack that was unsuccessful.” Source: http://investigations.nbcnews.com/_news/2013/11/13/21440068healthcaregov-targeted-about-16-times-by-cyberattacks-dhs-officialsays Source: http://hackmageddon.com/category/security/cyber-attacks-statistics/ Oct. 2013 Source: http://hackmageddon.com/category/security/cyber-attacks-statistics/ Oct. 2013 Source: http://hackmageddon.com/category/security/cyber-attacks-statistics/ Oct. 2013 Source: http://hackmageddon.com/category/security/cyber-attacks-statistics/ Oct. 2013 Why Internet Security • Internet attacks are increasing in frequency, severity and sophistication • Security has become one of the hottest jobs even with downturn of economy Why Internet Security (cont’d) • Virus and worms – Melissa, Nimda, Code Red, Code Red II, Slammer … – Cause over $28 billion in economic losses in 2003, growing to over $75 billion in economic losses by 2007. – Code Red (2001): 13 hours infected >360K machines - $2.4 billion loss – Slammer (2003): 10 minutes infected > 75K machines - $1 billion loss U.S. National Cybersecurity Martin Casado • Keith Coleman Sponsored by William J. Perry MS&E 91SI Fall 2006 Stanford University Why are we talking about cybersecurity? Case 1: Blue Security DoS • May 2006, anti-spam company “Blue Security” attacked by PharmaMaster • PharmaMaster bribed a top-tier ISP's staff member into black holing Blue Security's former IP address (194.90.8.20) at internet backbone routers. • Attack disrupts the operations of five top-tier hosting providers in the US and Canada, as well as a major DNS provider for several hours. • Blue security operation was disrupted, and they had to shutdown their service. Case 2: Slammer Worm • January 2003 Infects 90% of vulnerable computers within 10 minutes • Effect of the Worm - Interference with elections - Cancelled airline flights - 911 emergency systems affected in Seattle - 13,000 Bank of America ATMs failed • No malicious payload! • Estimated ~$1 Billion in productivity loss Case 3: WorldCom • July 2002 WorldCom declares bankruptcy • Problem WorldCom carries 13% - 50% of global internet traffic. About 40% of Internet traffic uses WorldCom’s network at some point • October 2002 Outage affecting only 20% of WorldCom users snarls traffic around the globe • Congressional Hearings Congress considers, but rejects, extension of FCC regulatory powers to prevent WorldCom shutdown Vulnerabilities are not just technical Case 4: “Titan Rain” • Successful network intrusions on U.S. military installations • Increasing in frequency since 2003 • Originating from China • Successful intrusion into… – U.S. Army Information Systems Engineering Command at Fort Huachuca, Arizona – Defense Information Systems Agency in Arlington, Virginia – Naval Ocean Systems Center in San Diego, California – United States Army Space and Strategic Defense installation in Huntsville, Alabama – more… Increasing Dependence • Communication (Email, IM, VoIP) • Commerce (business, banking, e-commerce, etc) • Control systems (public utilities, etc) • Information and entertainment • Sensitive data stored on the Internet e.g. • Biz, Edu, Gov have permanently replaced physical/manual processes with Internetbased processes • Navy command dissemination? Security Initially Not a Priority Other design priorities often trump security: Cost Speed Convenience Open Architecture Backwards Compatibility And It’s Really Hard … • Hard to retrofit security “fixes” • No metrics to measure (in)security • Internet is inherently international (no real boundaries) • Private sector owns most of the infrastructure • “Cybersecurity Gap”: a cost/incentive disconnect? – Businesses will pay to meet business imperatives – Who’s going to pay to meet national security imperatives? An Achilles Heel? This level of dependence makes the Internet a target for asymmetric attack Cyberwarfare Cyberterrorism Cyberhooliganism* and a weak spot for accidents and failures * Coined by Bruce Schneier, Counterpane The Challenge Clearly not just a technical problem. Requires consideration of economic factors, public policy, legal issues, social issues etc. That’s what this class is about. What is “cybersecurity?” Some Definitions According to the U.S. Dept of Commerce: See “information security” n. cybersecurity: n. information security: The protection of information against unauthorized disclosure, transfer, modification, or destruction, whether accidental or intentional. Some Definitions According to S. 1901 “Cybersecurity Research and Education Act of 2002”: cybersecurity: “information assurance, including scientific, technical, management, or any other relevant disciplines required to ensure computer and network security, including, but not limited to, a discipline related to the following functions: (A) Secure System and network administration and operations. (B) Systems security engineering. (C) Information assurance systems and product acquisition. (D) Cryptography. (E) Threat and vulnerability assessment, including risk management. (F) Web security. (G) Operations of computer emergency response teams. (H) Cybersecurity training, education, and management. (I) Computer forensics. (J) Defensive information operations. Some Definitions According to S. 1900 “Cyberterrorism Preparedness Act of 2002 ”: cybersecurity: “information assurance, including information security, information technology disaster recovery, and information privacy.” One way to think about it cybersecurity = security of cyberspace One way to think about it cybersecurity = security of cyberspace information systems and networks One way to think about it cybersecurity = security of information systems and networks One way to think about it cybersecurity = security of information systems and networks + with the goal of protecting operations and assets One way to think about it cybersecurity = security of information systems and networks with the goal of protecting operations and assets One way to think about it cybersecurity = security of information systems and networks with the goal of protecting operations and assets security in the face of attacks, accidents, and failures One way to think about it cybersecurity = security of information systems and networks in the face of attacks, accidents, and failures with the goal of protecting operations and assets One way to think about it cybersecurity = security of information systems and networks in the face of attacks, accidents and failures with the goal of protecting operations and assets availability, integrity, and secrecy One way to think about it cybersecurity = availability, integrity and secrecy of information systems and networks in the face of attacks, accidents, and failures with the goal of protecting operations and assets (Still a work in progress…comments?) In Context corporate cybersecurity = availability, integrity and secrecy of information systems and networks in the face of attacks, accidents and failures with the goal of protecting a corporation’s operations and assets national cybersecurity = availability, integrity and secrecy of the information systems and networks in the face of attacks, accidents and failures with the goal of protecting a nation’s operations and assets What is computer security? Why do we need? Cybersecurity Questions • How vulnerable is the United States to a cyberattack? Are we heading for an “electronic pearl harbor”? • What areas of vulnerability require the greatest attention in order to improve our national cybersecurity? • Is the Internet an appropriate platform upon which to operate infrastructure systems critical to US economic or government operation? Cybersecurity Questions • What characteristics would we want in an “Ideal Internet”? • Can the current Internet evolve into a network with significantly improved security guarantees or will another system need to created? • Does greater Internet security necessarily entail decreased online privacy? information security triad (CIA) • Confidentiality • Integrity • Availability Confidentiality • Prevent from unauthorized access • Prevent from unauthorized disclosure • Guarantee privacy Integrity • Prevent from unauthorized modifications to information Availability • Ensuring the availability of resources (System, Services, or Information) to users in a timely manner CIA in action Some of the methods used to protect the CIA of information • Identification: – Using unique naming to enforce access control and establish accountability • Authentication – Verification of the provided identification • Authorization – Define what actions the user, the system, or the process can perform on the information. Accountability Tracing back actions and events back in time to the entity (User, System, Process) that invokes them. Logs Ordered list (usually by time) of actions and events created by systems and applications to provide accountability. The term Audit trail is used when to distinguish low level actions or events. Functionality vs. Assurance Assurance • We are looking on Functionality and Assurance from security prospective • The functionality of the system provides information about what the system can perform. • The assurance of the system provides the information about what the system won’t perform. Conservative System Holistic System Functionality Privacy the state or condition of being free from being observed or disturbed by other people. New Oxford American Dictionary 3rd edition © 2010, 2012 by Oxford University Press System Resource (Asset) • Information, Services, Functionalities, or Hardware. What about Network? Threat • Threat: Set of conditions that has the potential of causing a security breach that harm the system. Types of threat: • Unauthorized Disclosure: Unauthorized access to data • Deception: Acceptance of false data • Disruption: Interruption or prevention of correct operation • Usurpation: Unauthorized control of a system or part of it. Which of the security CIA properties does each threat type affect? Unauthorized Disclosure • Exposure: Sensitive data is released to unauthorized entity • Interception: Unauthorized entity directly gain data being transferred between authorized entities. • Inference: Unauthorized entity get data indirectly • Intrusion: Unauthorized entity gain data by cheating the security enforcement entities. Deception • Masquerade: Unauthorized entity perform an malicious activity as an authorized entity. • Falsification: Providing false data • Repudiation: An entity denies the occurrence of an event. Disruption • Incapacitation: interrupt operation by disabling some functionality • Corruption: Change in system and data to interrupt the system’s operation • Obstruction: disallow system from providing services. Usurpation • Misappropriation: an unauthorized entity controls system’s resources. • Misuse: an unauthorized entity perform actions that reduce the system security. Security Policy A set of rules that regulate how the system provides security services in order to protect its services or resources. Vulnerability and Attack Vulnerability: A flaw in the system that could be exploited to violate the security policy. Attack: An exploit of a vulnerability. Adversary: the entity that is launching the attack Risk and Countermeasure Risk: The probability that a certain threat will attack and cause a particular harmful result. Countermeasure: An action that reduces the risk or the harm by eliminating or preventing from certain threats or attacks. Security Concepts’ Relations Adversary rise impose Countermeasures Threat Owners reduce Wish to abuse or damage Increase Risk to to Asset Stallings, William. Computer Security: Principles and Practice (2nd Edition) Reading • http://cryptome.org/2013/09/infosecuritycert.pdf [ Read to end of page 10]