Auditing &
Assurance
Services,
6e
Copyright © 2015 McGraw-Hill Education. All rights reserved. No reproduction or distribution without the prior written consent of McGraw-Hill Education.
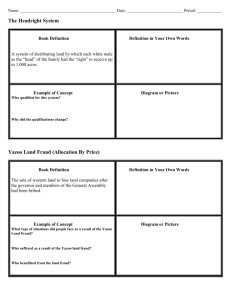
Chapter 06
Employee Fraud and the
Audit of Cash
"Rather fail with honor than succeed by fraud."
--Sophocles (496-406 BC)
6-2
Learning Objectives
1.
2.
3.
4.
5.
6.
7.
Define and explain the differences among several kinds of employee fraud
that might occur at an audit client.
Identify and explain the three conditions (i.e., the fraud triangle) that often
exist when a fraud occurs.
Describe techniques that can be used to prevent employee fraud.
Describe the control activities over the receipt and disbursement of cash.
Describe the types of substantive procedures that are conducted during the
audit of cash.
Discuss actual cash fraud cases and describe how the schemes were
uncovered.
Describe some extended procedures for detecting employee fraud schemes
involving cash.
6-3
Employee Fraud Overview
• Fraud consists of knowingly making material misrepresentations of
fact with the intent of inducing someone to believe the falsehood and
act upon it and thus, suffer a loss or damage.
• Employee fraud is the use of fraudulent means to take money or other
property from an employer. It consists of three phases: (1) the
fraudulent act, (2) the conversion of the money or property to the
fraudster's use and (3) the cover-up.
• Embezzlement is a type of fraud involving employees' or
nonemployees' wrongfully taking money or property entrusted to their
care, custody, and control, often accompanied by false accounting
entries and other forms of lying and cover-up.
• Errors are unintentional misstatements or omissions of amounts or
disclosures in financial statements.
• Direct-effect Illegal Acts are violations or government regulations by
the company, or its management or employees that produce direct and
material effects on dollar amounts in the financial statements.
6-4
Employee Fraud Red Flags
Observation of changes in a person’s habits and lifestyles may reveal
some red flags. Fraudsters may exhibit these behaviors:
•
•
•
•
•
•
•
•
•
•
•
•
•
Experience sleeplessness
Drinking too much
Take Drugs
Become irritable easily
Can’t relax
Get defensive
Can’t look people in the eye
Sweat excessively
Go to confession
Find excuses and scapegoats for mistakes
Work standing up
Work alone
Work late frequently
6-5
Characteristics of Fraudsters
• Has education beyond high school
• Is likely to be married
• Is member of a mosque, temple, or church
• Ranges in age from teens to over 60
• Is socially conforming
• Has an employment tenure from 1 to 20 years
• Has no arrest record
• Usually acts alone
Unfortunately, they look like most everybody else
6-6
The Fraud Triangle
There are three conditions that are likely
to be present when a fraud occurs.
They are:
• Motivation
• Opportunity
• Rationalization
6-7
Exhibit 6.1
Fraud Elements
6-8
Motivation
• A motive is some kind of pressure a person
experiences and believes to be unshareable with
friends and confidants
– Actual or perceived need for money (Economic motive)
– “Habitual criminal” who steals for the sake of stealing
(Psychotic motive)
– Committing fraud for personal prestige (Egocentric
motive)
– Cause is morally superior, justified in making others
victims (Ideological motive)
6-9
Opportunity
• An opportunity is an open door for solving
the unshareable problem by violating a
trust.
– Weak internal controls
– Circumvention of internal controls
– The greater the position, the greater the trust
and exposure to unprotected assets.
6-10
Rationalization
• When people do things that are contrary to their personal
beliefs – outside their normal behavior – they provide an
argument to make the action seem like it is in line with
their moral and ethical beliefs.
– Some of the most frequent rationalizations are:
•
•
•
•
•
•
•
I need it more than the other person.
I’m borrowing the money and will pay it back.
Everybody does it.
The company is big and will never miss it.
Nobody will get hurt.
I am underpaid, so this is due compensation
I need to maintain a lifestyle and image.
6-11
Fraud Prevention
• A strong control environment and tone at the top
– Can have a pervasive effect on fraud prevention
• Managing people pressures in the workplace
– Counseling services
– Anonymous hotlines
– Ethics officers
• Internal control activities and employee monitoring
– Segregation of duties and responsibilities for transaction authorization, record
keeping, custody of or access to assets, and reconciliation of actual assets to the
accounting records.
• Integrity by example and enforcement
– Accountability
– Codes of conduct
– Background checks prior to hiring
6-12
Be Aware of Exceptions
o
o
o
o
o
o
o
Missing documents.
Alterations on documents.
Photocopied documents.
Second endorsements on checks.
Unusual endorsements.
Old outstanding checks.
Unexplained adjustments to
accounts receivable and
inventory balances.
o Unusual patterns in deposits in
transit.
o General ledgers that do not
balance.
o Cash shortages and overages.
o Excessive voids and credit
memos.
o Customer complaints.
o Common names or addresses for
refunds.
o Increased past due receivables.
o Inventory shortages.
o Increased scrap.
o Duplicate payments.
o Employees that cannot be found.
o Dormant accounts that have
become active.
6-13
Cash Internal Control
Considerations
• Cash is highly liquid, easily transportable,
and not easily identifiable, and therefore is a
primary target for employee thieves.
• Some strong internal control activities:
– Dual custody of cash at all times
– Lockbox arrangement
– Fidelity bonds
6-14
Exhibit 6.2 - Cash Receipts Processing
6-15
Cash Receipts: Process activities
• Receive cash and REMITTANCE ADVICE in mail.
• Prepare REMITTANCE LISTING.
• Enter total from REMITTANCE LISTING (or
REMITTANCE ADVICE) in CASH RECEIPTS
JOURNAL.
• Prepare DEPOSIT SLIP and deposit cash receipts in bank
(INTACT and DAILY).
• Record update to SUBSIDIARY ACCOUNTS
RECEIVABLE using REMITTANCE ADVICE.
• Reconcile REMITTANCE LISTING, SUBSIDIARY
ACCOUNTS RECEIVABLE , and DEPOSIT SLIP daily
6-16
Cash Receipts and Disbursements:
Key Control Activities
• INFORMATION PROCESSING
– Voucher packet (Purchase requisition, purchase order, receiving report, invoice)
matched prior to cash disbursement authorization
– Deposits reconciled to amounts credited to accounts receivable ledger
– Bank reconciliation
• PHYSICAL CONTROLS OVER THE SECURITY OF ASSETS
–
–
–
–
–
–
Deposit cash and checks daily and intact
Lock box account
EDI transactions
Dual custody over cash
Unused checks secured
Check imprinting machine
• SEGREGATION OF DUTIES
– Separate custody, authorization, recording, execution
• PERFORMANCE REVIEWS
• RECONCILIATIONS
6-17
Exhibit 6.3 Tests of Controls for Cash
Receipts
6-18
Exhibit 6.4 Tests of Controls Over Cash
Disbursements
6-19
Audit Evidence Used to Test
Cash
•
•
•
•
•
•
Cash receipts journal
Cash disbursements journal
Bank reconciliations
Cancelled checks
Year-end bank statement
Cutoff bank statement
6-20
Exhibit 6.5
How to Read a
Cancelled Check
and Endorsement
6-21
Exhibit 6.6
Small Business
Bank Statement
6-22
Audit of Cash
The first procedure in an audit of cash is to obtain a bank reconciliation
for each cash account and audit them in the following manner:
•
Balance per bank
–
–
•
Add deposits-in-transit
–
–
•
VOUCH to cash disbursements journal
TRACE checks cleared from cutoff bank statement
Add/Subtract other Debit/Credit Memos
–
•
TRACE to cash receipts journal
VOUCH to CUTOFF BANK STATEMENT
Subtract Outstanding Checks
–
–
•
CONFIRM (STANDARD BANK CONFIRMATION) directly with bank
Agree amount to CUTOFF BANK STATEMENT
Inspect bank credit/debit memo and audit for reasonableness. Examine relevant supporting
documentation.
Balance per books
–
–
FOOT the entire reconciliation for mathematical accuracy
TRACE the amount to the trial balance
6-23
Exhibit 6.7
Bank
Reconciliation
6-24
Confirmation of Bank Balances
• Standard Bank Confirmation Inquiry
– Must be mailed under auditor’s own control.
– Used to confirm deposit balances and loan balances
– Also can be used to request information about contingent
liabilities and secured transactions.
• Electronic Confirmation Requests
– Many banks now only complete confirmation requests
electronically (e.g., confirmations.com)
– Can improve the control of both delivery and receipt of the
confirmation request
– Allowed by professional auditing standards
6-25
Exhibit 6.8
Bank
Confirmation
6-26
Check Kiting
• Is the deliberate floating of funds between two or
more bank accounts to make it appear that more
cash is present and available than is really the
case. This practice is also known as “playing the
float.”
• Advances in technology and bank scrutiny has
decreased this possibility in recent years.
• A Schedule of Interbank Transfers is generally
used by auditors to detect check kiting.
6-27
Proof of Cash
• A proof of cash would be used in situations where
controls over cash are weak.
• It essentially combines two bank reconciliations,
reconciling all transactions that occurred during the
period to the client’s Cash Receipts Journal and Cash
Disbursements Journal.
6-28
Exhibit 6.9
Illustration of Proof of Cash—First National Bank
6-29
Other Fraud Detection Procedures
for Cash
• Count the petty cash twice in one day
• Carefully examine endorsements on canceled
checks
• Audit general journal entries
• Retrieve customer checks
• Use marked coins and currency
• Measure deposit lag time
• Examine documents such as bank statements for
alteration
• Covert surveillance
6-30