Topic 8 Secure communication of mobile devices
advertisement
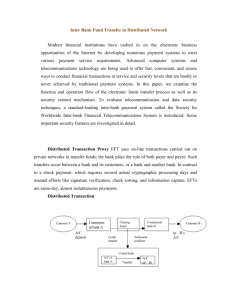
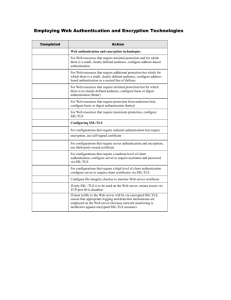
Topic 8: Secure communication in mobile devices Choice of secure communication protocols, leveraging SSL for remote authentication and using HTTPS for web traffic • The rapid growth of the mobile devices as both individual and business communication devices has created a growing demand for security and privacy in this electronic communication channel. • Both security and privacy are essential in mobile communication. • The desire for security and privacy has led to several communication security protocols and standards. • Among these are: – – – – – – Secure Socket Layer (SSL) Transport Layer Security (TLS) secure IP (IPSec); Secure HTTP (S-HTTP), secure E-mail ( PGP and S/MIME), DNDSEC, SSH, others. • We focus on three communication layers: – Application Layer: • • • • • • PGP S/MIME S-HTTP HTTPS SET KERBEROS – Transport Layer: • SSL • TLS – Network Layer: • IPSec • VPN • Secure Socket Layer (SSL) – SSL is a widely used general purpose cryptographic system used in Internet browsers and mobile communication. – It provides an encrypted end-to-end data path between a client and a server regardless of platform or OS. – Secure and authenticated services are provided through data encryption, server authentication, message integrity, and client authentication for a TCP connection through HTTP, LDAP or POP3 application layers. – It rivals S-HTTP • The SSL Handshake – Before any TCP connection between a client and a serve, both running under SSL, is established, there must be almost a process similar to a three-way handshake. This get-to-know-you process, is similarly called the SSL handshake. During the handshake, the client and server perform the following tasks: • Establish a cipher suite to use between them. • Provide mandatory server authentication through the server sending its certificate to the client to verify that the server's certificate was signed by a trusted CA. • Provide optional client authentication, if required, through the client sending its own certificate to the server to verify that the client's certificate was signed by a trusted CA. • Exchange key information using public key cryptography, after mutual authentication, that leads to the client generating a session key (usually a random number) which, with the negotiated cipher, is used in all subsequent encryption or decryption. The customer encrypts the session key using the public key of the merchant server (from the merchant’s certificate). The server recovers the session key by decrypting it using the its private key. This symmetric key which now both parties have is used in all subsequent communication. • Secure-HTTP (S-HTTP) – Secure HTTP (S-HTTP) extends the Hypertext Transfer Protocol (HTTP). – When HTTP was developed, it was developed for a Web that was simple, that did not have dynamic graphics, that did not require, at that time, hard encryption for end-to-end transactions that have since developed. – As the Web became popular for businesses users realized that current HTTP protocols needed more cryptographic and graphic improvements if it were to remain the e-commerce backbone it had become. Validation of server privilege boundary in networked applications • Server side validation offers more security over data than client side validation. – Client side validation can easily be tempered with. – Server side validation eliminates this security breach • Without strong and effective validation leaveweb application vulnerable to: – cross-site scripting attacks, – SQL injection attacks, – buffer overflows, – other types of input attack. • Consider the following guidelines when designing a validation strategy: – – – – – – Identify trust boundaries within Web application layers, and validate all data crossing these boundaries. Assume that all client-controlled data is malicious and needs to be validated. Design validation strategy to constrain, reject, and sanitize malicious input. Design to validate input for length, range, format, and type. Use client-side validation for user experience, and server-side validation for security. Use certificates and avoiding man-in-the-middle • Cryptography guarantees basic security services authorization, authentication, integrity, confidentiality, and non-repudiation in all communications and data exchanges in the new information society. These guarantees are achieved as follows: – Confidentiality - through encryption – Authentication - through digital signatures and digital certificates – Integrity - through generating a digital signature with a public key and obtain the message digest. Then hashing the message to obtain a second digest. If the digests are identical, the message is authentic and the signer’s identity is proven. – Non-repudiation - through digital signatures of a hashed message then encrypting the result with the private key of the sender, thus binding the digital signature to the message being sent – Non-replay – through encryption, hashing, and digital signature • The Key Exchange Problem in communication – Although symmetric encryption is commonly used in communication due to its historical position in the cryptography and its speed, it suffers from a serious problem of how to safely and secretly deliver a secret key from the sender to the recipient. – This problem forms the basis for the key exchange problem. The key exchange problem involves: • ensuring that keys are exchanged so that the sender and receiver can perform encryption and decryption, • ensuring that an eavesdropper or outside party (man-in-the middle) cannot break the code, • ensuring the receiver that a message was encrypted by the sender. • For the distribution of public keys, there were several solutions including: – Public announcements where any user can broadcast their public keys or send them to selected individuals – Public directory which is maintained by a trusted authority. The directory is usually dynamic to accommodate additions and deletions – Certificate Authority (CA) to distribute certificates to each communicating element. Each communicating element in a network or system communicates securely with the CA to register its public key with the CA. Since public keys are already in public arena, the registration may be done using a variety of techniques including the postal service.