DOC Version
advertisement

Final Thesis Routing overheads vs. End To End Connectivity on mobile ad hoc networks By. Christopher Totani Supervisor: Dr. Grant Wigley Declaration I declare that this thesis does not contain, without acknowledgement, any material submitted for a degree or diploma within the university. To the best of my knowledge, all material previously published or written by the author has been cited by the correct author(s). Christopher Ian Totani November 2014 Acknowledgements I would like to thank all of my friends and family for support through this experience and giving motivation to continue on. I would also like to thank my supervisor, Dr. Grant Wigley, for providing me with the opportunity to do such a thesis with the Defence Force and for providing me with great guidance upon construction of this thesis. I would finally like to thank the DSTO for providing me with the opportunity to work with them and expand my knowledge in a field I would have never been exposed to. Table of Contents Table of Figures ...................................................................................................................................... 6 1. Introduction ......................................................................................................................................... 7 1.1 Statement of Research................................................................................................................... 7 1.2 Field of Thesis............................................................................................................................... 8 1.3 Significance and Contributions ..................................................................................................... 8 2. Literature Review................................................................................................................................ 9 2.1 Network Fundamentals ................................................................................................................. 9 2.1.1 7 Layer OSI model ................................................................................................................. 9 2.1.2 What is a protocol .................................................................................................................. 9 2.1.3 Level 2 - Data Link Layer .................................................................................................... 10 2.1.4 Level 3 - Network Layer ...................................................................................................... 10 2.1.5 Network Layer protocols ..................................................................................................... 10 2.2 Concept of Ad-hoc networking and Mobile Ad Hoc Networking ............................................. 11 2.2.1 Structured Networks ............................................................................................................ 11 2.2.2 Problems with Structured Networks .................................................................................... 11 2.2.3 What is Ad-Hoc Networking and why it's desirable ............................................................ 12 2.2.4 Mobile Ad-Hoc networking (MANETs) and Routing ......................................................... 12 2.3 Introduction to Routing and Routing Protocols .......................................................................... 19 2.3.1 What is RIP (And RIPv2) .................................................................................................... 19 2.3.2 What is OSPF ....................................................................................................................... 20 2.3.3 MANET Routing Protocols ................................................................................................. 22 2.3.4 Routing Overheads............................................................................................................... 27 2.4 Conclusion of literature review ................................................................................................... 28 3. Methodology ..................................................................................................................................... 30 3.1 Question and Explanation ........................................................................................................... 30 3.1.1 Sub questions ....................................................................................................................... 30 3.2 Steps towards research and answering the question ................................................................... 31 3.2.1 Review literature and determine overheads ......................................................................... 31 3.2.2 Specify metrics of routing overheads ................................................................................... 31 3.2.3 Finalise routing protocols to be simulated ........................................................................... 31 3.2.4 Simulate routing algorithm under different scenarios .......................................................... 32 3.2.5 Map data to meaningful diagrams/tables, draw conclusions from data gathered. ............... 32 3.3 Research method to use .............................................................................................................. 32 3.4 Sampling and population ............................................................................................................ 33 3.5 Data Collection ........................................................................................................................... 34 3.6 Data Analysis .............................................................................................................................. 35 3.7 Tools ........................................................................................................................................... 36 4. Parameters for simulations ................................................................................................................ 38 4.1 Selected metrics for Routing overheads and End to End Connectivity ...................................... 38 4.1.1 Routing overhead metrics .................................................................................................... 38 4.1.2 End to End Connectivity/Performance metrics .................................................................... 40 4.2 Mobility Models.......................................................................................................................... 43 4.2.1 What are Mobility Models ................................................................................................... 43 4.3 Traffic Generated .................................................................................................................... 45 4.4 NS-2 Parameters ......................................................................................................................... 46 4.5 Bonnmotion Parameters .............................................................................................................. 49 4.6 NS-2 traffic generation simulation .............................................................................................. 49 5. Simulations ....................................................................................................................................... 52 5.1.1 Ad-Hoc On Demand Distant Vector Protocol (AODV) ..................................................... 52 5.1.3 Destination Sequenced Distance-Vector routing protocol (DSDV) .................................... 55 5.1.4 Optimised Link State Routing protocol (OLSR) ................................................................. 56 5.2 Simulation Results ...................................................................................................................... 58 5.2.1 Normalised routing load....................................................................................................... 58 5.2.2 Packet Delivery Ratio .......................................................................................................... 59 5.2.3 End to End Delay ................................................................................................................. 60 5.2.4 Throughput ........................................................................................................................... 61 5.2.5 Average Hop Count ............................................................................................................. 62 5.3 Summary of simulation results ................................................................................................... 62 6. Conclusion, Future Work .................................................................................................................. 64 6.1 Conclusion .................................................................................................................................. 64 6.2 Future Work ................................................................................................................................ 65 7. References ......................................................................................................................................... 67 Table of Figures Figure 1 Example of MANET connections (black lines) vs. direct connection (red line) .................... 14 Figure 2 Structure of the HOLSR protocol ........................................................................................... 26 Figure 3 NS-2 Parameters ..................................................................................................................... 47 Figure 4 A Route Request Packet [a] .................................................................................................... 53 Figure 5 A Route Reply Packet [a] ....................................................................................................... 53 Figure 6 A DSDV "Message" packet [a] .............................................................................................. 55 Figure 7 Normalise Routing Load Results ............................................................................................ 58 Figure 8 Packet Delivery Ratio Results ................................................................................................ 59 Figure 9 End to End Delay Results ....................................................................................................... 60 Figure 10 Throughput Results .............................................................................................................. 61 Figure 11 Average Hop Count Results ................................................................................................. 62 1. Introduction This introduction will give a synopsis on the purpose of the research on MANETS, what aspects of research this paper will address and what will be contributed within the research. 1.1 Statement of Research The research proposed will focus on Mobile Ad Hoc Networking (MANET) and Routing overheads for MANETs. MANETs are an infrastructure-less based networking paradigm, which intends to run a network purely with end user devices, rather than utilising any form of fixed infrastructure. In other words, networking is in the hands of end user devices, rather than networking devices, such as routers and switches. Routing overheads refers to the amount of networking resources dedicated towards up keeping routing. Routing overheads are of major concern with MANETs, due to limited routing resources, low bandwidth links, battery power reliance and the dynamic nature of a MANET, routing can consume these resources. Routing overheads also become of major concern when the size and distribution of the network is of significant size. Applications for MANETs are optimal when infrastructure is either impossible, too costly or impractical to use. MANETs also remove a single point of failure within the network, since it is self configuring in maintaining routing of the network. The application of MANETs intended for this research is for military use, requiring military needs to be met within the MANET. This thesis is intended towards aiding within the research of military MANETs for the Defence Science and Technology Organisation (DSTO). As network size scales up, routing overheads become larger and more of a burden. Furthermore, MANETs utilise wireless to connect between nodes, which tends to be lower in bandwidth in comparison with wired network. These concerns are what motivates with research upon utilising lower overheads with routing protocols. The core influence of routing overheads is the routing protocols themselves, since protocols hold the policies and algorithms required to function the network. The research shall evaluate several routing protocols used within MANET structures and determine which theoretically provides lower routing overheads. If possible, simulations will be done on such protocol to determine if routing overheads would be significant, with full end to end connectivity being maintained. The alternative towards utilising a MANET is a semi structured infrastructure, which contains multiple gateways, utilising smaller MANETs to gain the benefits of both infrastructure and ad hoc paradigms. However, such design will still incur costs with equipment and maintenance of the network. Furthermore, it introduces a central point of failure within each sub-network, due to dependency on the network gateway. 1.2 Field of Thesis Ad Hoc Networking, Networking, Routing Protocol, Military Networks, Mobile Ad Hoc Networking, 1.3 Significance and Contributions - Contribution for the defence force use of MANETS - Expand understanding on hierarchical MANETs within context of military use. - Expand understanding on comparisons between cylindrical and hierarchical MANETs 2. Literature Review The literature review will start from this section, building up information on networking, ad-hoc networking, mobile ad hoc networking and routing overheads. All information is based on research found on research papers, journals, conference papers, 2.1 Network Fundamentals This section will introduce the basics of networking and routing, focusing on the 7 layer OSI model, protocols, routing and popular routing protocols. A network is a group of devices connected to share data along connection lines. Data shared through a network is usually shared through wireless or through physical lines. To maintain network connections, network devices are used to maintain networking. Network devices can include router, switches, wireless gateways, network interface cards and wireless cards. Devices typically used within a network are computers, PDAs, servers, phones and networking equipment. 2.1.1 7 Layer OSI model In networking, the whole basic scheme of protocols and packets can is expressed through the Open System Connection (OSI) model. The OSI model includes the Application, Presentation, Session, Transport, Network, Data link and Physical layer. Each layer is grouped by a protocol data unit (PDU). This includes Data (Application, Presentation, Session), Segments (Transport), Datagram (Network), Frame (Data Link) and Bit (Physical). For the sakes of relevance, we shall only focus on Level 3 (Network) and level 2 (Data link) layer. 2.1.2 What is a protocol A protocol in, networking terms, is a series of methods and rules used to regulate how data is transmitted through a network. Protocols are generally expressed through packets, which are protocols which can handle data. For example, the Transmission Control Protocol (TCP) is used for sending reliable data over the internet. It regulates it by using a checksum to ensure the data contained is within the packet, to ensure the data is accurate. the User Datagram Protocol on the other hand, use in a similar fashion, but for more speedy and efficient data transfer, due to its lesser complexity. Protocols are usually used within packets, which are a unit containing overheads/relevant packet information and encapsulated data. 2.1.3 Level 2 - Data Link Layer The data link layer functions in a similar fashion from the network layer, except it is responsible with Media Access Control between nodes. Such includes error corrections and acknowledgements within the physical layer, delivery of frames within a local network. The Data link layer is typically sub layered between the Logical Link Control (LLC) layer and Media Access Control (MAC) layer. 2.1.4 Level 3 - Network Layer The network layer is used mainly for routing, normally using routers. The layer is critical towards end to end connectivity, since it maintains source and destination between hosts within a network. It also maintains segmentation of networks and subnets. 2.1.5 Network Layer protocols Due to routing occurring within the network layer, this section will focus on protocols which operate within the Network layer. Such network layer protocols are commonly used within structured, enterprise networks and are uncommon within military use. However, for the sakes of research, it is important to acknowledge such protocols and reason with their suitability/unsuitability within mobile ad-hoc networks. 2.2 Concept of Ad-hoc networking and Mobile Ad Hoc Networking The previous sections have outlined the basics of networking and purposes of the network layer protocol. This section shall expand upon an ad-hoc infrastructure and why a structured network may not be suitable within a military. 2.2.1 Structured Networks A structured networking infrastructure is a fixed, predictable network topology which uses specialised devices to maintain communications. The networks explained within the previous section are examples of structured networks. Network topologies within an structured network change less frequently in comparison with an unstructured network. Network topology changes within a structured network are usually due to faults (i.e. power outage), erroneous change of configuration and addition of new hardware. Usual topology changes can be very costly, since information of topology change must be between routing nodes. Structured networks also allow special devices to do specific networking tasks. Typically within enterprise networks, utilises the core, distribution and access layer. The core layer utilises layer 3 networking/routing and acts as the backbone for the whole network. The distribution layer utilises both layer 3 networking and layer 2 switching, depending on the size of the distribution layer. The access layer is purely for switching and brings connectivity for end devices. 2.2.2 Problems with Structured Networks The disadvantages of Structured networks for this section will focus on general, with further sections exposing why structured networks are not the best solution in the context of military ad hoc networks. One disadvantage of Structured networks is the lack of flexibility for nodes to connect to any part of the network. As outlined before, the typical core, distribution, access layer only allows access to a network through an access layer. In certain situations, it is important for access to be given through the whole network. In [2], the article shows that a military ad hoc network used allows flexibility for team radios, as end devices, to communicate freely within the network and even allows the end devices to act as repeaters within the network. One major disadvantage of structured networks is since they have central network administration which are configured by network administrators, they also require on-going maintenance/repairs to keep uptime high. Structured networks also require the usage of highly expensive routing, switching and access point devices within a network. Such networks, especially with many nodes, will require more powerful and more devices to support the infrastructure 2.2.3 What is Ad-Hoc Networking and why it's desirable Ad-hoc networking is an unstructured network, which contains end devices which self manages the whole network, typically over a wireless medium. Each node within the network acts as a link and entry point within the network, allowing participants to connect freely anywhere within the network. Ad-hoc networking also provides a natural self healing, self configurable network ecosystem which requires little maintenance. This is due to Ad-Hoc networking protocols being structured around each node being its own router and is aware of every other node. 2.2.3.1 Problems with ad hoc networking The problems with ad hoc networking is due distinct rapid nature in comparison towards structured, it is difficult to use protocols made for structured networks. For that reason, it must be taken into consideration for us to For example, the OSPF routing protocol relies upon flooding packets within the network to maintain a consistent topology. While this flooding is a very low cost within a wired network, due to the reliability of wired links, wireless links would have a higher rate of error. Since OSPF is very rapid with topology updates, we may see nodes drop out, taken off the current topology and have to be re-added to the topology. Topology changes within OSPF also rely on neighbourhood adjacencies (i.e. nearby nodes), which within an ad hoc network, can change if nodes move around a lot. More information on OSPF for Mobile Ad Hoc Networks shall be explained through the MANET section. 2.2.4 Mobile Ad-Hoc networking (MANETs) and Routing What has been introduced was the concept of ad hoc networking. This section will be dedicated towards an implementation of ad-hoc networking, known as Mobile Ad Hoc Networking (MANET). A MANET is a type of ad-hoc infrastructure, which solely uses mobile devices to structure network. 2.2.4.1 Common uses of a MANET Typically, MANETs are not used when Infrastructure services are more practical and cost effective to use. MANETs are used when infrastructure cannot be utilised, due to the environment the network must be used in. Besides the scope of the research, one prime example would be emergency services using an ad-hoc network to communicate data in the event of a disaster. Hobbyist may also utilise MANETs for educational purposes or personal uses for a Personal Area Network. MANETs may also be beneficial to be used in infrastructure- less scenarios, which may contain a simple task and not need the overheads of a structured network. One example is a vehicular ad-hoc network used within a car's safety features. Such MANET would be used for cars to establish communication to share data which may be useful in the event of a possible collision (e.g. car's speed and distance to determine automatic braking pressure). 2.2.4.2 Military usages of MANETs Military usage of MANETs is a major use, due to the self configuring properties and mobility of such network design. Combatants can use MANETs to communicate over terrain which may have restricted direct communication, since combatants in between equip with a radio link can act as a intermediate repeater to help establish connections[3]. The image below depicts what has been explained, with the black lines depicting a MANET structure and the red line depicting a direct connection between the two end nodes. The 3 nodes in between act like a repeater and passes routing through itself. It's important to note that if the two end nodes would not only have a poorer connection due to distance, but also due to noise and attenuation from the nodes interfering inbetwen. Figure 1 Example of MANET connections (black lines) vs. direct connection (red line) One news article [28] shows an example of how the US military deployed a MANET called "Force 21 Battle Command Brigade and Below". This MANET was used to keep track of fast moving combat vehicles, using GPS in conjunction to detect where vehicles were. The MANET was also used to provide info on detected landmines, directions of where vehicles must go, location of friendly forces and location of enemy forces. The MANET has also arguably helped with reducing incidents of friendly fire, due to awareness of combatants. 2.2.4.3 Advantages of MANETs MANETs provide many advantages than towards the alternative of using an infrastructure based network. MANETs do not require networking devices, such as routers and switches, to maintain a network, or a central medium to ensure full connectivity, such as a satellite network, therefore reducing costs required to structure the network. MANETs also provide a self-configuring network, which is required due to the high mobility nature of a MANET. MANETs can also provide high mobility structure less network, since the MANET is dependent on mobile devices. This allows full mobility of the network, without requiring fixed infrastructure to piece the network together. Certain military situations may require soldiers to move forward rapidly between areas. Infrastructure set up (i.e. antenna tower) within an area may not be portable enough to move rapidly. Such infrastructure may be far away, to the point where connectivity is either unreliable or no connectivity is present. Furthermore, the infrastructure could be limited due to terrain (i.e. in hilly terrain, signals could be blocked between a rugged CB radio and a antenna tower due to a hill in the way) if nodes are positioned in an awkward position. MANETs are also highly scalable, due to the low cost and low barriers to entry for a node to connect to the MANET. MANETs do not require additional equipment (e.g. Ethernet cables, wireless access points, switches) to allow access into the network. Generally, a MANET would only require a compatible wireless connection, the node is a supported device and required authentication to access the MANET. However, this scalability is not unlimited and can be hampered due to other factors. This can be hampered due to routing protocol, number of nodes (can fill routing tables), type of data commonly utilised within the network. 2.2.4.4 Disadvantages of MANETs Whilst the high mobility, scalability and cost are the major advantages within a MANET, it is not without its downfalls. One major downfall within a MANET is the reduced security in comparison with Infrastructure networks. Typically, routing within a structured network only contains wired connections, which is difficult tamper into without breaking into the system either through physical means or through the network. Within a MANET, there are many entry points into the network at every node. This can leave the network open to malicious attackers which may try to break into the network, or take down the network. [7] sees an issue with DoS attacks being implemented within a MANET and could provide serious effects upon the MANET if a DoS attack was successful. Whilst it is not within the scope of this paper, it is important to outline this major downfall when implementing a MANET. Another disadvantage of MANETs is the reduced bandwidth and speed of such structure in comparison towards an infrastructure network. The MANET is dependent upon the capacity of each nodes components and processing power. Such MANET links may not have the same bandwidth capacity as a wireless access point on an infrastructure network. Furthermore, speed could also be bottleneck through the node's processing power, since each node would have to process their own data, let alone the routing updates/requests/hops. It is why the routing protocol of the MANET must be chosen carefully that it produces less routing overheads within the MANET. A further disadvantage is an extension to the argument previously mentioned in the ad hoc networking section, which disputed the usability of common protocols used within infrastructure network. Due to its relevance to the topic, the next section shall be dedicated towards the problems with TCP and UDP within MANETs. 2.2.4.5 Problems with TCP in MANETs Most networks usage revolves around internet usage, which requires the usage of the Transmission Control Protocol (TCP). The TCP protocol is well used, due to its high accuracy of data transfer over the internet. This is due to TCP's error correction methods of requiring a retransmission of data which has been deemed erroneous. TCP is however not favoured with real time applications, such as Voice over IP (VoIP) and real time video streaming. This is because the latency caused by TCP's retransmission of erroneous data. TCP's retransmission of data has actually been proven through several papers as to why TCP may not be the best solution for usage within MANETs. [8] did testings with comparisons between TCP and UDP to look at their overheads and energy consumed respectively. [9] has done tests on TCP, UDP and ICMP ( Internet Control Message Protocol) and has compared the throughput of each protocols. The test was done over the ns-2 simulator, with the OSLR protocol as the routing protocol. [9] shows TCP fluctuating in throughput, where as UDP and ICMP, which do no retransmissions, actually kept a constant throughput. However, TCP should not be fully disregarded within the usage of MANETs. Research shows very little data on TCP transmissions over a hierarchical MANET, with flat topology MANETs used within tests. Furthermore, there are test [10] looks at the energy usage of TCP over MANETS, tracking the joules expended to do a TCP transmission over different scenarios, under different MANET routing protocols (AODV, DSDV, DSR, OLSR). The paper also looked at different TCP variants, looking at New Reno, SACK, Vegas and Westwood. The Westwood TCP model saw a great balance between error correction and computational power used. An alternative towards the TCP protocol is the UDP protocol. Such protocol will be inevitable to be used within voice and real time video use within a MANET. However, for data, TCP is commonly used within structured networks. The UDP protocol, as shown in [8], gives more throughput than TCP consistently. The UDP protocol also produces less overheads, due to its simplicity and lack of retransmission erroneous data. However, UDP is far from a perfect solution for data transfer usage within a MANET. Since UDP does not retransmit data, there are chances of inaccurate data sent to the other nodes, such as garbled text sent between two soldiers or a picture containing foreign artefacts caused by the poor retransmission. Furthermore, UDP does not support encryption through the protocol itself, since it's overhead contains no room for encryption. This can cause serious issues with attacks upon the network, or the integrity of highly confidential data. To ensure accurate data is processed through the network, a Quality of Service (QoS) framework would be implemented. QoS looks at certain metrics, such as error rate, bandwidth and throughput to ensure data is accurate and of high quality[13]. Quality of Service is usually used within services, such as Voice over IP (VoIP) and real time video transfers, since such type of applications are real time and cannot afford to have retransmission of packets through a network. QoS is generally seen as a mechanism of quality control within a network, rather than an actual protocol implementation (i.e. real time video would be transported through a UDP packet in layer 4 (Transport layer), but the application layer protocol (i.e. RSVP protocol) may implement QoS metrics. Quality of Service provides quality by priotising packets delivered through the MANET, typically allowing real time packets to traverse through the network first (i.e VoIP, real time video) than ones which are not produced in real time (i.e. HTTPS, FTP). The utlisation of QoS can be a quite critical aspect, since the routing protocol and application layer protocol needs to support QoS metrics. QoS is a significant factor within MANETs, since QoS not only could help provide accuracy with data between nodes without the usage of TCP, but QoS needs to be optimised for MANETs [25]. The limitations for QoS within in MANETs are due to the dynamic topology of a MANET, with limited resources [36]. This section is not core to research, but to outline and demonstrate through literature that MANETs do not behave or react like structured networks. This is to highlight the specialist attention MANETs need, in order to function within reason and ensure protocols to be implement will be stable within a MANET. However, a MANET routing protocol with QoS support should be considered of favorable choice, especially if MANETs will be using a range of data (especially VoIP). A support QoS would make better use of its limited bandwidth. 2.3 Introduction to Routing and Routing Protocols Routing, within the context of packet data networks, focuses with utilising the most efficient path of forwarding a packet within a network. Routing devices typically form the backbone of a wide area network (WAN), where as switches are usually utilised within Local Area Networks (LANs). Due to the complexity of many WANs with multiple LANs and the number of routers within a network, usually for purposes of redundancy, uptime and performance, it is important that the protocols used within network are suitable for the network. Routing is typically functioned within the layer 3 of a network, with the utilisation of a routing protocol. Typical routing protocols are RIP, OSPF, EIGRP and BGP. Routing does not rely on a routing protocol, since routing can be static by setting up what is known as a static route. Static routes are generally the most efficient way of routing, however have higher maintenance overheads and are typically not reserved for dynamic networks. Routing typically relies on what is known as a Routing table. A routing table is a database stored within the NVRAM of a routing device, which contains vital information for a routing infrastructure, such information includes participating networks, routing protocol, source of networks, next hop and next hop metric. Different routing protocols may have their own related tables, usually for other metrics, network topology or supporting features. Due to their relevance, the remainder of this section will focus on OSPF and RIP 2.3.1 What is RIP (And RIPv2) Routing Information Protocol (RIP) is an older routing protocol, which utilises a very basic routing algorithm. RIP only takes into consideration of hop count as a metric to determine a routing path. The hop count is the number of routers a packet must route through, before it is transported to its final destination. This hop count is limited to 15 hops, in which a 16th or more hop is considered an infinite hop. Due to the limitations of RIP, it is not a commonly used protocol for larger scale networks. A newer version, RIPv2, supports a higher hop count (96), however, lacks the extra metrics more sophisticated protocols contain to implement more efficient routing paths [1]. 2.3.2 What is OSPF The Open Shortest Path First (OSPF) protocol is a link state, non proprietary routing protocol. It utilises Shortest Path First to route to the most efficient destination. On top of that, OSPF has other mechanisms which allows the network to run more efficiently. OSPF allows the network to be divided into "areas", which allows grouping of certain routers within a network. OSPF introduces "Stub routing", which allows configuration of certain areas to have smaller, more efficient routing tables. [1] 2.3.2.1 How OSPF Works Each participating router within an OSPF network contains what is known as a Link State database (LSDB). This Link State database contains the every participating router's ID (unique identification for each router), Link State Information (maintained through Link State Advertisements(LSA)), adjacencies, neighbourhoods and neighbouring router costs[33]. Link State Advertisements (LSA) are used to maintain the LSDB and contains different types of LSA. Typical LSA's are LSA type 1 (Router LSA used for maintaining Inter area routing) and LSA type 2 (Network LSA used to maintain lists of routers)[1]. These LSA advertisements are typically flooded through the network or within the area, depending on the LSA type (LSA type 1 and two are flooded within an area only). To maintain connectivity within the network, the OSPF protocol forms adjacencies with other connected routers known as "neighbours". These neighbour adjacency help with determining with a router's presence and links within a network. If a neighbour adjacency was to be lost, the link between the two routers would be null and may cause a router to be removed from the network's topology. These adjacencies are maintained by flooding hello packets out the interfaces of the router, to keep neighbours alive and discover new links. Furthermore. OSPF contains a unique feature which the network is divided into areas. The different areas can be categorised as the backbone area (area 0, all areas connect to this), Regular Area (contains internal/external routes) and stub area (only contains internal and default routes). Every OSPF instance requires an area 0 and every area should be connected to this area. An area does not have to be directly connected to area 0 and can be connected through a virtual link, which tunnels a connection through a different area. However, it is commonly seen as bad practice and a sign of poor network design[1]. 2.3.2.2 OSPF on Ad-Hoc Networking There is research on implementing extensions for OSPF to work on ad hoc networks, since OSPF is an already established and well supported protocol. Some papers have introduced implementations on MANET Extensions for OSPF[11] [12] [34]. Some implementations are either newly developed or untested. Others have provided simulations and well documented information on the algorithm on how their version of OSPF works [27] notes the impossibility of implementing OSPF areas within an ad hoc network, due to how OSPF areas form and moving nodes. [28] argues for mobile nodes to join other areas, however this would break the fine tuning aspects of OSPF areas (e.g. allow certain areas to reduce routing tables). Furthermore, nodes would have to be preconfigured to join OSPF areas, otherwise they will not receive connectivity. However, there is compelling research done on MANET extensions for OSPF, which may seem as a plausible alternative to MANET routing protocol. This protocol is known as OSPF-MDR (OSPFMANET Designated Routers). It looks at utilising the designated router/backup designated router feature of OSPF and treating the designated routers as a default gateway (similar to how a cluster head is within a hierarchical MANET) [34]. The inter-area node is referred to as the MANET Designated Router (MDR), with a back up node known as the Backup MDR (BMDR). The MDR is responsible for flooding LSA packets, through gathering adjacencies formed, to form the topology. To help reduce overheads, MDRs can be declared as a non flooding MDR to reduce routing overheads, by reducing LSA updates[35]. It also tries to reduce routing overheads by declaring different types of adjacencies to reduce overheads with hello packet flooding. When forming adjacencies, the node differentiates neighbour relationships with adjacent nodes. This influences whether the node is routable or if even full connectivity between the nodes are plausible [35]. These neighbourhood relationships are Down, One-Way, Dependent, Selected Advertised (included in LSA) and Bidirectional [34]. Such extension shows potential, however lacks any tests within the scope of military networks. However, such protocol is a possible candidate for comparison with other MANET protocols[39]. 2.3.3 MANET Routing Protocols For this section, we shall produce the different routing protocol used within MANETs. The first part of the section will contain Flat topology MANETs, where as the rest will cover hierarchical MANETs. Please note that any references of "Flat", "Cylindrical" or "Full connectivity" will reference to Flat topology MANETS, where as "Clustered" and "Hierarchical" will refer to Hierarchical Topology MANETs. 2.3.3.1 Flat Topology MANETs Flat topology MANETs are usually referred to as standard MANETs in academia and are widely used within research purposes of MANETs, such as [9] comparing different flat topology MANETs within their energy usage. Flat topology MANETs typically contain a routing table and routing hops. They also do typical route requests, route replies and routing updates. Routing updates, however, can differ between different Flat topology MANET protocols. Typically, different routing protocols function differently by how they process routing updates. The two main types are known as Reactive and Proactive, with a combination of both seen as hybrid. Reactive MANET protocols Reactive MANET protocols are seen as protocols which every node maintains their own tables and only do routing updates sporadically [9]. Dependant on the protocol, routing tables are recalculated during an event or when a node is not found. Reactive protocols are regarded in [9] and [10] as being the most efficient protocols with little overheads. Proactive MANET protocols Proactive MANET protocols differ in that each node is required to update their own tables regularly. [9] has suggested that Proactive MANET protocols function similarly towards protocol used within infrastructure networks. Hybrid MANET protocols Hybrid MANET protocol try to bridge the best of both Reactive and MANET protocols, by being universally reactive but locally proactive. Hierarchical MANET protocols could be considered a Hybrid MANET protocol, since they tend to cluster the network and keep routing updates as local within an area. However, hierarchical MANETs tend to also different on how each nodes are considered within the structure of the route. More details will be provided within the Hierarchical Topology MANETs section. 2.3.3.2 Flat topology MANET protocol Examples This part will provide examples of a standard flat topology MANET protocol, how it functions, what is its advantages and its downfall. AODV (Ad hoc On-Demand Distance Vector) The AODV protocol is a reactive MANET protocol, which utilises Route Requests (RREQs), Route Replies (RREPs) and Route Errors (RERRs) [37] to maintain routing tables and topologies. RREQs are broadcasted through the network, when the destination IP address of a routable packet is not in the node's topology. An RREP will be sent to the requesting node if another node contains the destination IP on its routing table, or if it is the destination. To avoid infinite loops upon the network, RREQ contains a recent sequence number, which if a node receiving the RREQ has a sequence number greater than or equal to the sequence number, it will send a RREP[38]. The AODV protocol tends to have lower overheads in comparison to proactive protocols, due to the lack of flooding the network regularly for the sakes of updating routing tables. However, since routing tables are not periodically synchronized, inconsistent routes may occur if sequence numbers are further apart. Furthermore, the protocol does not optimise hop count (i.e. not bandwidth aware) to reduce the number of hops. DSR (Dynamic Source Routing) The DSR protocol is another reactive MANET protocol, which uses a source route, route cache, route discovery and route maintenance. When a node sends a packet, it sends a source route which contains the next hops to the destination route. The route cache is a list of routes which the node has learned, however if the node does not have a route, it sends out a route discovery to other nodes, which checks it's cache for a route. Route maintenance is done to see if nearby nodes are within range, if not, it removes the routes to the nearby nodes and invokes a route discovery to calculate newer routes. A simulation conducted on this protocol has shown on a small scale network of 24 mobile hosts with frequent movement of hosts, shows a 1% routing overhead in comparison to data packets transmitted[39]. This paper shows DSR to scale well with highly mobile nodes and rapid topology changes, however does show routing overheads increasing as routes become larger[39]. OLSR (Optimized Link State Routing) The OLSR protocol is a proactive MANET protocol which utilises a link state algorithm and frequent topology updates. The OLSR protocol uses hello packets and topology control to create, manage and update the network topology. Hello messages are utilised to discover up to 2 hop neighborhood information and help with election of multipoint relays. Multipoint relays function like OSPF designated routers, in which they relay routing information between nodes and control traffic flow. Multipoint relays help in reducing flooding within the network, hence reducing overheads[40]. Topology Control is used to efficiently calculate and update the topology of the network. 2.3.3.3 Hierarchical Topology MANETs The hierarchical MANET Topology differs vastly from a Cylindrical type MANET, and in some respects, a hybrid flat topology MANET. The hierarchical MANET topology is radically different from the routing topologies introduced in the previous section. Hierarchical MANETs are based on the realization of clustering, by placing specific nodes within groups [14]. Other routing protocols, such as OLSR, may have features which designates a node to do specific tasks (i.e. multipoint relay), but does not radically divide the network. Many of these protocols do not scale as efficiently as a hierarchical topology MANET, especially when the network becomes more dense, due to increased protocol overheads and increased interferences with broadcasts [15]. Furthermore, it is argued that due to the clustered structure and lower routing overheads, bandwidth is increased through the network [22]. Hierarchical MANETs try to localise routing updates, routing tables and routes as an attempt to reduce routing overheads. As mentioned, a hierarchical MANET divides the network into groups/clusters. From then, it allocates a node as a cluster head which does inter-cluster routing. The protocols to be proposed will further cluster the cluster heads and form more clusters, depending on the size of the network. 2.3.3.4 Hierarchical MANET protocols This section will brief on the different kinds of hierarchical MANET protocols found within literature. Hierarchical Optimized Link State Routing (HOLSR) The HOLSR protocol is an extension to the OLSR protocol, except it break the structure of the MANET into clusters and levels. Cluster heads would assume roles for multipoint relay; With Topology Control and hello packet flooding is reduced down to the clusters, hence reducing flooding overheads [18]. The levels of clusters are broken down to 3 levels and follow a criteria based upon several metrics. Some of these metrics include power level, node capacity, number of wireless interfaces and transmission range. A level 1 node typically is low powered, very low capacity and may only contain one wireless receiver. A level 2 node would have more wireless receivers, but may still be lacking in capacity and power. A level 3 node would be the highest capacity, most powerful and multiple wireless receivers [21]. The image below depicts of a typical HOLSR network [21]. Note the nodes upon the edges of clusters which overlap; Such nodes would contain the nodes of both clusters within routing table, thus able to locally route within each cluster. [21] Figure 2 Structure of the HOLSR protocol 2.3.4 Routing Overheads To provide scope within the research, this section shall be dedicated towards defining what routing overheads are, what routing overheads to expect (i.e. metrics) based upon what other research has defined routing overheads and why lower routing overheads may not be important. Routing overheads are the processing requirement for a node within a network to maintain connectivity. Many of these routing overheads can be seen as constraints within the network and can increase bandwidth consumption, and energy usage. The following are commonly discussed overheads, which will be used within the research of MANET overheads. 2.3.4.1 Number of Neighbours [30] suggests that the number of neighbours can have an effect on how routing overheads are shaped within a MANET. [30] argues the more neighbours contained within a nodes network, the higher it becomes an overhead due to the amount of route_request packets flooded. 2.3.4.2 Number of Hops The number of hops can have an influence upon the routing overhead of a MANET Protocol. [30] shows that as a network grows, the number of hops can influence the overhead of a route. This is mainly affected towards nodes which are further apart from each other, due to high routing path calculations. Many of the Hierarchical/clustered MANETs look at towards reducing routing tables and hops for nodes in larger scaled MANETs, since a node would have less neighbouring nodes within their cluster and only have to route to the clusterhead for intra-cluster routing. The H-LANMAR protocol could be used reduce hops within a network, however [18] has determined it's inefficiencies with its certain structure. 2.3.4.3 Route Discovery and positioning Papers such as [23] [31] argue upon that discovering routing paths and position of nodes can influence the overheads of routing. [23] uses GPS co-ordinate of nodes to help reduce routing path algorithm calculations. [31] demonstrates a modified version of the AODV protocol called the Adaptive Request Zone for Ad Hoc On-Demand Distance Vector (ARZAODV) protocol, which utilises an algorithm to determine distance and positioning of a node. 2.3.4.4 Frequency of Updates The frequency of updates refers to the amount of updates a network requires to maintain connectivity within a network. [2] lists it as a critical feature upon an ad-hoc network. 2.3.4.5 Topology changes [2] Also questions how the frequency of topology changes can affect the performance of a network. This should be seen as a major overhead within a network, since topology changes requires each node to recalculate (i.e. use resources) the topology of the network and send updates towards neighbours. 2.3.4.6 Misbehaving nodes Misbehaving nodes are nodes which do not process routing updates or route packets as expected within the network. This can be caused due to an overloaded node, a malicious node or a node presented with a fault. As shown in [7], misbehaving nodes within a MANET can cause a reduction in throughput of up to 32%. Misbehaving nodes would also require retransmission of packets, which contributes to the overhead of a network. 2.3.4.7 Packet flooding The number of packets required to flood a MANET can produce serious routing overheads within a MANET. This is due to each node required to process the packets flooded through the network. Packet flooding may be required, depending on the MANET routing protocol used within the network. Packet flooding may be required to maintain routes, such as topology updates and route requests. [32] has argued however that packet flooding may be more efficient for maintaining the network, if the MANET has a lot of moving nodes. 2.4 Conclusion of literature review In conclusion to the literature review, the concepts of networking and structured networks has been outlined on how networks work. Structured networks, whilst desirable for perfect situations, tends to be costly and high maintenance. For those reasons, the ad-hoc structure is best suited for environments which produce unpredictable situations. For military use, MANETs are ideal due to the high mobility and self configuring nature of MANETs. Routing is an important aspect of networks, since it forms the backbone of end to end connectivity for all devices. Routing protocols chosen must be suitable for the expect dynamic environment of MANETs. As found in literature, routing overheads are an important consideration, since it causes constraints with bandwidth. For that, the routing protocol for a MANET must be tested and chosen carefully to ensure routing overheads do not cause too many constraints. The question chosen for this research is What are the tradeoffs between end to end connectivity vs. routing overheads with cylindrical and hierarchal mobile ad hoc networks, within the context of urban military use?; The methodology section will clarify upon the question. 3. Methodology This section will detail through how research will be conducted to answer the thesis question, What are the tradeoffs between routing overheads and end to end connectivity, with cylindrical and hierarchal mobile ad hoc networks, within the context of urban military use? 3.1 Question and Explanation What are the tradeoffs between end to end connectivity vs. routing overheads with cylindrical and hierarchal mobile ad hoc networks, within the context of urban military use? The research conducted on Mobile Ad Hoc Networks will have a focus on routing overhead, compared against full end to end connectivity of MANETs. The research will not define which MANET structure would suit for military usage, but outline with detail on how each structure copes with full connectivity and the overheads required to maintain connectivity. Military use is the main focus upon where such MANETs will be utilised, so research must take into consideration of the type of movement, terrain, integrity and structure of military activity. End to End Connectivity is defined as connectivity between hosts (or nodes) within a network. 3.1.1 Sub questions The following sub questions are to help answer critical aspects of the full questions. Many of these sub questions are based upon DSTO's expectations of the thesis. What size should the heirarchy start? - Use figures based on military division sizes - Reccomended figure should be a balance between a smaller MANET and a cost effective - Take into consideration of next size up network (i.e. if 128 node network shows poor performance, but 64 node network does, 64 may not be optimal, just in case networks have to merge under emergency situations) What performance drops are shown when network is scaled up? - Related to first sub question - Should help provide answers whether a flat topology MANET is even feasable Any correlations between routing overheads and connectivity? - What performance metrics are affected by routing overheads? What protocol is suited for military use? - i.e. protocol should perform consistent 3.2 Steps towards research and answering the question 3.2.1 Review literature and determine overheads The literature must be reviewed in depth to identify what overheads will impact a MANET within a military setting. The overheads introduced within this proposal are examples of major overheads which may impact routing performance within a MANET. This process has already been started through the proposal, introducing concepts of MANETs, routing, routing protocols and specific MANET routing protocols. 3.2.2 Specify metrics of routing overheads A criteria must laid out and specify what routing overheads are appropriate for determining its impact upon the performance of a MANET. Critical routing overheads have been specified within the proposal, however more will be specified within the thesis. 3.2.3 Finalise routing protocols to be simulated The routing protocols displayed within the proposal are examples of many MANET routing protocols and existing structured network protocols. Due to the timeframe of research, very few protocols will be chosen for simulation. The protocols chosen for simulation will be based on past performance on previous simulations from other research, which takes into consideration of similar metrics. A cylindrical MANET protocol will be used to simulate a MANET without full end to end connectivity, such as the MANET would have a central point, acting as a default gateway. A hierarchical MANET will be assumed to have full connectivity, due to the way it arranges itself as clusters. 3.2.4 Simulate routing algorithm under different scenarios Once protocols and metrics have been finalized, routing protocols will be tested and data will be gathered from such simulations. 3.2.5 Map data to meaningful diagrams/tables, draw conclusions from data gathered. Once simulations have been finalised, data gathered will be put into meaningful graphs/tables, results explained and a conclusion will be decided to answer the question given. 3.3 Research method to use Research method to use: System (Build a system, do simulations of routing protocols) The research method to use is to build a system which could generate a functioning traffic, similar to one for use in a military scenario. A system could come under as physical devices, like ones used within military use or a virtual simulator, simulating the different MANET structures. The systems should be able to produce relevant data for determining routing overheads and end to end connectivity. The system must also produce reproducible results in which similar outcomes with the same configuration proposed within the context of this research. Utilising a virtual simulator will be the choice for this paper's research, since a virtual simulator will allow a more desirable scenario. Whilst a realistic system, using radio wave devices, would be able to produce more realistic results, it also has a few downfalls. Firstly, a sufficient sample size to produce a military MANET, especially a hierarchical, would not be feasible without a significant budget for the radio devices, enough participants for a decent sample size or terrain close to a military scenario. Other research methods are not appropriate for this research, due to either lack of literature utilising such method or impossibility of gaining relevant data. A case study is not relevant within research on routing since real life scenarios of MANET routing has not been implemented by the defence force. Furthermore, even if such MANET routing was implemented, it would be breach of confidentiality, since such military data would be confidential. Another method is utilising interviews/questionnaires. Again, such research method would require confidential data leaked. It would also assume the respondents of the questionnaire/interview would have sufficient knowledge of networking. Most qualitative research methods do not work, since Quantitive data can easily be reproduced through a simulation or mock up of the network. Network metrics tend to not be subjective and conclusions can be drawn clearer if a set of metric results were generated. 3.4 Sampling and population The sample size of the simulation may need to be compromise between what the DSTO demands and what is feasible to work within the duration of the thesis. Many papers, such as [9], [14] and [15] outline tests with flat terrain and smaller sample sizes. No papers found so far have done simulations with as many nodes as mentioned by the DSTO. This should be taken into consideration, as to whether the larger amount of nodes would be manageable within the time frame, or are there issues with the complexity of setting up such simulation. [4] and [5], whilst conducted with real devices with a small sample size, shows examples of possible terrain (e.g. hilly) which could affect the operation of wireless within the field. The simulation of nodes should take into consideration on what the population of end users of such MANETS and how they manipulate the network. The population of the network is expected to be mobile, unpredictable and usually utilising low powered. A Guideline of different sample sizes will be based upon the structure of the Australian defence force. Information will only be based on what is available on the public domain, thus not leaking any confidential information. Army - Two or more corps Corps - 30,000 Division - 10,000 - 20,000 Brigade - 2,500 - 5000 Batallion - 550 -1000 Company - 100 - 255 Platoon - 30 - 60 Section - 9 - 16 If a hierarchical MANET protocol is feasible to be simulated, then the size of a hierarchical MANET will be the size of a batallion, with lower level MANETs based on sub units. For example, utilising HOLSR's 3 tier MANET levels, a structure could be of the following... Size - Nodes per MANET - no. of MANETS Level 3 - 4 nodes - 1 MANET/Cluster head per MANET Level 2 - 64 nodes - 4 MANETS/Cluster head per MANET Level 1 - 1024 nodes - 16 MANETS / Cluster head per MANET If a hierarchal MANET protocol is not feasible then the lower levels of a heirarchy will be assumed for simulation. 3.5 Data Collection Collection of data coming from a simulation will require every event from network activity to be logged and recorded as the simulations take place. The majority of data collected from the network simulations will be objective (i.e. Quantitive) and should not require subjective explanation of results. Data will also be collected with 2 - 4 nominated routing protocols (1-2 Hierarchical and 1 - 2 cylindrical MANET protocol), depending on whether it is feasible within the time frame of the honours thesis. The RIP and OSPF protocol (including the OSPF-BDR protocol) will also be included within the simulation, to check their plausibility within a MANET. Data collection should also take into consideration of not only the different MANET structures, but also different scenarios per MANET structure. Such scenario's should include different terrains the MANETs would be placed, different combat scenarios (i.e. how the MANET reacts towards nodes moving rapidly and connecting/disconnecting, how nodes react towards large no. of nodes dropping out) and how movement of nodes affect the MANET). Scenarios can be provided by utilising different mobility models. The MANET should also simulate typical data utilised by combatants. Actual data does not have to be produced, however metrics used to measure the data will need to be collected. For example, a file transfer of classified data would need metrics such as accuracy, time taken to deliver, packet losses and average bandwidth . This may result in the utilisation of sending simple UDP broadcasts between two nodes. Alternatively, if hierarchical MANET routing protocols are without reach (i.e. not available freely on NS-2) then the thesis will focus on aspects of hierarchical routing protocol. 3.6 Data Analysis The analysis of the data produced by the simulation will require extra study upon metrics for Routing Overheads and End to end connectivity. The routing overheads section of this proposal shows an idea of how some typical routing procedures produce overheads within routing. Such information is critical when analysing data produced from simulation, to allow a clearer conclusion as to what the data produces. Furthermore, the metrics used will also be well defined with how expected results influence the conclusion of the research. The behaviour of packets within the MANET should also be looked at different levels. Layer 3 will be one of the main focuses in determining routing overheads and end to end connectivity. However, Layer 8 (Application Layer) will also be important to look at, especially with end to end connectivity. Layer 8 packets may reveal further information for how end to end connectivity is affected, since we shall be able to analyse the quality of application used within a MANET. The mobility of nodes shall also be taken into consideration on how it affect the MANETs. The mobility of nodes will be analysed on how they work within the MANET, how they influence the structure of the MANET, how certain nodes (i.e. flapping nodes) influence the routing tables. Heirarchial MANETs would need extra attention on how inter and intra cluster routing is affected by topology changes due to moving nodes, especially with higher level cluster heads moving between clusters. One aspect also of Hierarchical MANETs is to see how the network reacts to rapid changes of cluster heads, especially if past or present clusterheads had more power to maintain routing overheads (e.g. Handheld CB Radio vs. Vehicle mounted CB Radio). Another aspect to analyse is how routing tables are maintained through each MANET structure. It's important to see how frequent updates occur, how large the updates are (i.e. are the updates unicast or multicast), how significant the updates are and how large the routing tables of each node. It will also be in interest to see how routing occurs between nodes within different clusters within a hierarchical MANET. The data will also have to be checked to see if they are accurately processed through the simulation, if the simulation itself has provided an accurate depiction of the different MANET routing protocols, is wireless signal between nodes simulated properly especially within different terrains and if the metrics and data collected relevant towards military use? 3.7 Tools The various items used within the research are as needed: Software to provide network simulation, source code for the different MANET structures, source code to simulate unreliable/unpredictable radio links, software to graph the data and a machine capable of producing the simulation. The network simulation to be used within the research will either be ns-2 or OPNET. ns-2 is a free network simulation tool, which uses the TCL scripting language to program protocols within the simulator. It is a commonly used simulator within industry and was the main network simulator used within the research papers found for this proposal. The alternative is OPNET, which is the simulator which the DSTO uses for simulation. Microsoft excel will also be used to table the data and depict it in a more meaningful graphical form, such as graphs, charts, bar graphs, etc. To generate a mobility model, the java based tool BonnMotion will be utilsed[41]. This tool is able to generate many different mobility models for a simulation scenario. BonnMotion supports generating mobility models in many different platforms (including NS-2). Traffic for each scenario will be generated using NS-2's built in traffic generation tool. This tool allows the generation of both UDP and TCP traffic. Both UDP and TCP type traffic will be attempted through the simulation. Operating system used for this simulation is Lubuntu 12.04 32-bit. 32-bit operating systems tend to produce more accurate results for NS-2. NS-2 in 64 bit operating systems tend to produce errors and inaccurate results. 4. Parameters for simulations 4.1 Selected metrics for Routing overheads and End to End Connectivity This section will detail on the metrics chosen to help answer the thesis question/sub-questions. The metrics will be divided between routing overhead metrics and end to end connectivity metrics. Routing overheads will measure the amount of traffic constraints and routing load of the specific routing protocol, whilst end to end connectivity metrics will focus on the performance of the routing protocol and connectivity between nodes. 4.1.1 Routing overhead metrics Routing overhead metrics will be utilsed to calculate the efficiency of the routing protocol. There will be no comparisons between routing protocol specific metrics (i.e. number of beaconing packets, such as OLSR hello packets). This is because the algorithms of selected protocols tend to drastically differ, thus making a very difficult comparision. For example, AODV utilises Route Request (RREQ) and Route Replay (RREP) to calculate paths. AODV uses multipoint relays/elected nodes to calculate routing paths, both produce completely different metrics, thus difficult to compare. Papers typically usually look at raw routing/control packets sent through the network. This is feasable, since NS-2 labels the packets type. For example a packet of type "CBR" would indicate a data packet being traversed through the network, where as one labeled "AODV" or "HELLO" would indicate a control packet. The metrics should be an indicator of bandwidth and energy consumed by the protocol. Higher routing overheads, as mentioned in previous sections, can lead to higher bandwidth consumption, thus can affect the performance of the network. Energy consumed by the routing protocol would be a byproduct of the routing protocol utilsing more computation power or utilising more network hardware interfaces. While a lower routing overhead figure is desirable, the performance of the routing protocol should not be hampered for the sakes of lower routing overheads. A MANET can have lower routing overheads, however, may also have a very low utilisation of bandwidth, low packet delivery ratio, high average hop count and large end to end delays. Normalised Routing overhead Normalised Routing overhead (Also known as Normalised Control overhead or Control Overhead) is a ratio of routing packets sent vs. data packets sent. Normalised Routing overhead gives a metric which is compariable with the efficiency of the routing protocol in use. If a routing protocol requires lesser overheads, it would thus use less bandwidth and require less energy to buffer and process routing packets. Normalised routing overhead alone does not predict the efficiency of the routing protocol, thus should be compared with other metrics. A packet is determined as a Routing packet within NS-2 by reading what type of packet it is. Ususually, it is a keyword such as "message" (indicating DSDV), "AODV", "DSR", "OLSR" or "HELLO" (Hello packets sent for OLSR). Note: ROUTING_PACKET, could substitute for a function which takes the keyword as a parmeter and returns a boolean value if the packet is a routing packet. Pseudo code: set routingPacket to 0 set dataPacket to 0 For Each packet in packetSent If packetType Equals ROUTING_PACKET Or packetType equals HELLO Increment routingPacket Else If packetType Equals DATA_PACKET Increment dataPacket normalisedRoutingOverhead Equals routingPacket/dataPacket 4.1.2 End to End Connectivity/Performance metrics This section will detail on performance/End to End Connectivity metrics. The metrics listed are not all possible End to End/performance metrics, but available and most commonly used metrics used within other research. End to End Connectivity metrics will determine the overall performance of the simulated MANET and how well a connection is defined. Such metrics will be compared toward the routing overhead metric and look for several factors. One factor is if there is a correlation between higher (or lower overheads) and performance increases/decreases. Another factor is looking whether the routing overhead is significant with the performance of the MANET. If a routing protocol produces high overheads and produces poor end to end connectivity, the routing protocol will be deemed inefficient. Average Hop Count Average hop count is the average number of nodes a data packet must traverse before it reaches to its destination. Average hop count can be an indicator of how efficient the routing protocol produces routes between source and destination. Average hop count tends to correlate between average end to end delay. If a routing protocol produces high average hop count and high delays, then the delay of a data packet could be of the routing protocol not producing efficient enough routes. Such symptoms can magnified within high mobile situations. However, alone it is not an indicator of performance, mainly since calculation of Average hop count does not take into consideration of bandwidth, latency. Furthermore, if a routing protocols produces very little hop count, or with zero average hop counts, with a significantly larger network, this could be a possible indicator of a network with poor convergence (typically in conjunction with low packet delivery ratios, low delays and low throughput). Whilst average hop count was introduced within the literature review as a routing overhead, it is merely a small indicator. However, it does not provide enough data to assume the routing overhead of a protocol. However, it is a good performance indicator of the network produced by the routing protocol itself. Pseudo code: set packetFowarded to 0 set totalHopCount to 0 For each packet in packetSent If packet is in FORWARD_STATE For each node in Nodes If nodeId is currentNode Increment packetForwarded If packet is DATA_PACKET totalHopCount Equals totalHopCount Plus packetsForwarded set averageHopCount to 0 averageHopCount Equals totalHopCount / totalPacketsRecieved Throughput Throughput is the amount of bandwidth utilised for data packets, which is usually measured in Kbps. Generally speaking, higher values are better with values closer to the maximum amount of bandwidth most optimal. Pseudo code: throughput = ((totalPacketsRecieved /100 ) * packetSizeBytes) / numberOfNodes Average end to end delay Average end to end delay is the time taken for a packet to traverse through the network in milliseconds (ms). It looks at the time from the source of the packet to delivery toward the destination. Lower delay is optimal, since it indicates a faster converging network and can expose the efficiency of the routing protocol's routing capabilities. Pseudo code: set startTime to 0 set endTime to 0 set duration to 0 For each packet in packetSent if packet Equals DATA_PACKET And packet is SENT_PACKET startTime Equals Packet.Time Else If packet Equals DATA_PACKET and packet is RECIEVED_PACKET endTime Equals packet.time duration Equals endTime Minus startTime Packet Delivery Ratio Packet Delivery ratio looks at the number of packets sent through the network and the number of packets received, then converted to a percentage figure. Packet Delivery ratio can be affected by routing overheads, mainly due to congestion of routing control packets which may lead to less data packets sent. This can also be worsened by the MANET increasing in size, which typically requires larger routing overheads. The PDR can also be affected by the type of data being sent through the MANET. MANETs which utilise more TCP data could have a lower PDR ratio, mainly due to extra packet sent out for retransmission, hence more congestion. Higher figures are better, however should be compared with the size of the network increasing to determine where the PDR is greatly affect. Pseudo code: packetDeliveryRatio = (packetRecieved/packetSent) * 100 4.2 Mobility Models This section will focus upon the theory behind mobility models, why they are important and what purpose they produce for this simulation. The section will also give examples of mobility models which are commonly used in past simulations and what could be used in future simulations. 4.2.1 What are Mobility Models A mobility model is an algorithm which is used to generate the movement of a set of nodes within a Mobile Ad-hoc network simulation. The mobility model is an important aspect of MANET simulations, since it can provide a near realistic experience of a real life scenario without the need to specify custom mobility. Mobility models typically look at three certain parameters to define mobility (velocity, pause time and direction). Mobility models are common in determining the performance of a MANET routing protocol or research in algorithms for a MANET protocol. One of the critical aspects of MANET routing protocols is not how efficient it is, but how it is able to respond to different environments. This puts the aspect of routing overheads as less of a burden, since a protocol which may have high routing overheads may also be able to react to different scenarios than other routing protocols. This can allow one to aspect different algorithms or settings of a protocol to see what tradeoffs there are certain situations. Mobility models can also give a near emulation of terrain, with the exception of the ability to change the effects attenuation or noise between wireless signals. However mobility models can alter the placement of a node based on constraints from a terrain. For example, the manhattan model is a VANET specific movement model which co-ordinates nodes into a grid-like street fashion. Such mobility model would provide the constraints of vehicles speed in traffic, where the vehicle can be placed (i.e. the road), but cannot duplicate the wireless signal interference caused by tall buildings and rain. The rest of the section will briefly go through main different types of mobility models, which will then lead to the next section, which will provide examples of mobility models Random models Random mobility models are ones which have purely random movement with no restrictions. All parameters such as speed, destination and direction are randomly generated with no influence upon other nodes. An example is the Random Waypoint model. The Random waypoint takes into consideration or random velocity, direction and pause time of each node. Random waypoint typically produces nodes Due to its wide usage when simulating MANETS on NS-2, Random Waypoint has been chosen for simulation. Models with temporal dependency Mobility models with temporal dependency tend to produce influence upon how a node moves based on its previous performance. An example of a Model with temporal dependency is the Guass-Markov movement model. Models with spacial dependency Models with spacial dependency tend to have other nodes can affect the mobility of other nodes 4.3 Traffic Generated This section will go over details on traffic generated for simulations. Since traffic is not the core focus of the simulation, simplified traffic was generated for the simulation. Traffic does not indicate any intuitive algorithm or application layer traffic. Traffic generated will be of a Constant Bit rate (CBR) on the application level over UDP (transport layer). It is a simplistic packet which simply sends over a MANET and has no timeout clause (i.e. once sent, it will not be retransmitted if packet times out). Unlike TCP, if there is not data retransmission of the packet if data from the packet is deemed in accurate (i.e. has artifacts when presented on the application layer). FTP over TCP was attempted during trial simulations using NS2's traffic generation script. However, issues occurred with traffic occurring on simulations, which lead to no connectivity. There were known issues with NS-2 and generating TCP traffic upon this research, thus TCP will not be tested. The size of the packet will be 512 bytes, the default size of a packet when traffic is generated using NS-2's traffic generation script. 4.4 NS-2 Parameters The parameters defined in the table will be universal for all simulations, except for ones which list multiple variables. Such variables will also be defined in line with the corresponding variable listed. For example 1500 for x and y would also mean number of nodes would be set to 32 and of 16 connections. Number of Simulations per protocol = 5. Physical/Datalink Layer Channel Channel Channel/WirelessChannel Prop Propagation Propagation/TwoRayGround Netif Network Interface Phy/WirelessPhy Mac Mac Layer Mac/802_11 Ifq Interface Priority Queue Queue/DropTail/PriQueue (CMUPriQueue for DSR) ll Link Layer LL Ant Antenna Antenna/OmniAntenna Scenario x x-co-ordinate size (pixels?) 1000, 1500, 2000, 4000, 8000 y y-co-ordinate size (pixels?) 1000, 1500, 2000, 4000, 8000 ifqlen Size of interface queue 100 seed Random seed no. 0.0 nn Number of nodes 16,32, 64, 128,256 stop Time of simulation 100 (seconds) Mc Maximum Connections 8, 16, 32, 64, 128 Figure 3 NS-2 Parameters Channel - Channel This parameter sets the type of channel. For obvious reasons, this is set to WirelessChannel to denote the nodes utilise wireless channel. Prop - Propagation This parameter defines the path position of the radio signal. Two-ray ground reflection model (as defined) calculates a line of sight distance (line between transmitted and reciever) and reflected path distance, which calculates a path which bounces from transmitter, to the ground then to the reciever. Netif - Network Interface This parameter refers to the type of physical interface each nodes use. Mac - Mac Layer This parameter refers to the protocol used in layer 2/data link layer. The protocol used is 802.11a, a primitive form of wireless communication. ifq - Interface Queue This parameter determines what type if queue is used to store packets with packet buffer of each node. ll - Link Layer [46] [47] This parameter defines the built in link layer class to be invoked within the simulation. Keep in mind the simulation file is a object oriented TCL script, hence would require such to be defined. Ant - Antenna This parameter defines the type of antenna which will be simulated by all nodes. OmniAntenna would therefore define a multi-directional antenna. x - x-co-ordinate size Parameter defining the x co-ordinate boundaries of the simulation. Errors will be produced if a node attempts to enter the simulation outside of the boundary. y - y-co-ordinate size Parameter defining the y co-ordinate boundaries of the simulation. Errors will be produced if a node attempts to enter the simulation outside of the boundary. ifqlen - Interface queue size This parameter defines how many packets can be stored in the queue at a time. Seed - Random seed number Seed defines the starting point of the randomness of the simulation. Two simulations, provided they contain same parameters, same generated mobility scenario and same generated traffic file will have similar results if the seed number is the same. The same simulations with different seed will produce different results. nn - number of nodes This parameter indicates the maximum number of nodes which will be simulated. If a node is referenced exceeds the number of nodes defined, an exception will occur. stop - time of simulation This parameter indicates the duration (seconds) of the simulation mc - maximum connections This parameter indicates the maximum number of connections between two nodes which can occur during a simulation. 4.5 Bonnmotion Parameters bm -RandomWay [Mobility Model] - d [Time of Simulation] -n [Number of Nodes] -x [Width of Simulation] -y [Height of Simulation] 4.6 NS-2 traffic generation simulation Parameter: ns cbrgen.tcl - type cbr [Generates UDP traffic] -nn [Number of Nodes] -mc [Maximum connections]-seed [Random number generation] - rate 4.0 [interval between packet transmission] 4.7 Simulation constraints Due to the timeline of this research and the limitations of the NS-2 simulator, this section will outlne the different constraints brought upon. These constraints could be used by the DSTO as possibilities for future references, especially for simulations of routing protocols which were proposed within the literature review, but cannot be simulated. Within the literature review, there was possibilities of structured network protocols being utilised in substitution for a designated MANET protocols. Whilst there were factors within literature which outlined the downfalls of utilising structured routing protocols within MANETS (i.e. RIP, OSPF), these cannot be confirmed within the simulations for this research. It is quite uncommon for MANETS to be simulated with standard routing protocols, especially with NS-2. This could be achieved with other network simulation tools, such as OPNET. There is also the possibilities of programming the standard routing protocols to work under NS2,.however this would require in depth technical knowledge of each protocol to write code for the program. This is achieved by writing a C program which contains the algorithm of the protocol. The algorithm will also have to interface with the simulator itself. Producing the code and interfacing it with NS-2 would take a significant amount of time, which therefore cannot be achieved within the timeframe of this thesis. Further constraints includes the complications of using multiple simulators to compare metrics between simulators. Different simulators tend to have different outcomes upon the output of results, primarily based upon the difference within their algorithms. OSPF-MDR was a proposed candidate to simulate to provide data on how a modified structured network protocol would work within a MANET. However, it uses a completely different simulator (Quagga). Research at The Ecole Polytechnique Fed´ er´ ale de Lausanne have tested NS-2, GloMoSim and OPNET by flooding packets through the network with tweaks towards the MAC layer and comparing metric data produced. The study showed disparities with results produced, especially at the MAC layer[46]. Furthermore, Quagga is less of a simulator, but a router emulator and lacks features core to the simulations (i.e. support for Mobility Models). Further constraints are also with the availability of MANET routing protocols. NS-2 2.35 is bundled with AODV, DSR, DSDV and TORA. The OLSR algorithm is an implementation as UM-OLSR (Released under GNU General Public Licence), with no modifications done to the protocol[48]. There currently no publically available implementations of H-OLSR for NS-2. There are several papers with claims of utilising H-OLSR on NS-2, however are noted to be customised implementations[47]. This alone has changed the structure of the thesis drastically, which was originally going to compare hierarchical and non hierarchical MANET implementations. However, there is evidence within literature which suggests flat topology MANET protocols are not suitable for larger MANETs. Simulation data on flat topology MANETs can also put forward the plausibility of flat topology MANETS suitability within larger networks by simulating such larger networks. By doing so, this could rule out the usage of flat topology networks used within military MANETs. However, this will require future simulations on hierarchical MANETs to gather more technical on hierarchical MANETs. Another constraint within the simulations is varied terrain too complex to set up within the timeframe, difficult to reproduce and not common in MANET simulations. Varied terrain within the simulation could be manipulated by generating code which would change bandwidth/connection parameters within the simulation when a node is at a specific position of the simulation (i.e. hilly terrain). This would require a customised mobility model and changes to the simulation with geographical knowledge on how radio waves are attenuated/boosted in certain terrains. This would require more focus upon the MAC layer, which would push the thesis closer out of scope of the thesis. Furthermore, many simulations referenced within the literature review do not utilise anything more than flat terrain. Many either use a random positioned nodes with random movement, or use something more methodic or academic, such as a mobility model. 5. Simulations 5.1 Protocols for simulation The following protocols have been chosen for the simulations. Note that none of these protocols are heirarchy based, however will be used a substitution due to resource constraints. This section will also go into detail of how each protocol works and what are the expected outcomes for each protocol. The literature review introduced examples of such routing protocols, this section will go into more detail. 5.1.1 Ad-Hoc On Demand Distant Vector Protocol (AODV) AODV is one of the distance vector, on demand routing protocols chosen for simulations. It is one of the most commonly used protocol for research on MANETs. AODV uses route request (RREQ) and route reply (RREP) packets to generate a routing path. When a data packet is transmitted and routing path is needed (based on a route with a lower sequence number used to indicate age of route path), A RREP is sent through the MANET with a Destination IP Address and Originator IP Address (itself), with a sequence number. Nodes in between the source and destination will send a RREQ, with the source's IP address within the packet until it has reached the destination. The destination node will then send a RREP with its IP address as destination recursively to each node until it has reached the source. This is done without the destination requiring the routing tables or topology information of the router[46]. 0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 Type J R G D U Reserved RREQ ID Destination IP Address Destination Sequence Number Originator IP Address Originator Sequence Number Hop Count Figure 4 A Route Request Packet [49] 0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 Type R A Reserved Prefix Size Hop count Destination IP Address Destination Sequence Number Source IP address Time to Live Figure 5 A Route Reply Packet [49] If a route cannot be produced, mainly due to an unreachable destination, A Route Error (RERR) is produced by the node and is marked to be sent back to the source. Because the routing algorithm with discovering and updating routes is only produced when needed, AODV tends to have reduced routing overheads. This is more pronounced in low mobility situations, or where connection dropouts are very minimal. However, whenever mobility increases, so does the routing overhead and performance of AODV can be hampered. This can also cause delays in packet delivery, due to the process of AODV's on demand route discovery. 5.1.2 Dynamic Source Routing (DSR) DSR is similar to AODV in how it is a distance vector, on demand routing protocol. DSR also utilises RREQ and RREP packets to gather routing path information. The difference is DSR tends to have two paradigms, route discovery and route maintenance. Route Discovery includes the process similar to AODV in discovering routes, except each node has a "route source list". whenever a node recieves a non duplicate RREQ, but is not the destination, it adds the source address to its source route list. This creates a routing cache of routing paths in which if the node is not the destination, but recieves a route request, it can send a RREP if it has a know n path to the destination. This technique is designed to reduce routing overheads, making DSR with one of the least amount of routing overheads produced. Furthermore, this provides more possible paths, thus should help with calculation of paths with the least amount of hops. One major difference between DSR and AODV is DSR uses its route cache to store information, where as AODV utilises a routing table. Route Maintenance is the aspect of keeping routes up to date and ensuring the topology is up to date and all routes within the routing cache are routable. Route Maintenance has three condition upon the inspection of RREQ in which if few are met, a route may be considered outdated. If no conditions are met, then the route is considered impossible and a Route Error is sent back to the destination.. [50] DSR has been argued to provide better routing than AODV in larger MANETs and more consistent routing when mobility increases. However, DSR tends to have delays in propagating data packets through the network. 5.1.3 Destination Sequenced Distance-Vector routing protocol (DSDV) DSDV is drastically different in comparison towards the two other protocols chosen (AODV and DSR). Whilst a distance vector protocol, DSDV is a proactive based protocol. To recap from the literature review, a proactive protocol is one which periodically updates routing tables, rather than when a route is needed. The DSDV protocol shows similar characteristics towards the RIP algorithm, in which it uses the same Bellman-Ford Algorithm. DSDV sends out a "Message" packet containing the Destination, hop count and sequence number to help find routing paths to certain. DSDV does this periodically every 30 seconds to ensure routes are up to date, whether the topology has changed or not. Which differentiates DSDV from RIP is it uses a sequence number to version routing updates. If a sequence number of a route in the routing table is lower than one received from a message packet, then the route is considered obsolete and a new routing path is calculated. This also helps with reducing infinite looping routing paths and broadcast storms. 0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 Destination Address Hop Count Sequence Number Figure 6 A DSDV "Message" packet [51] Due to its nature of periodically updating, DSDV would tend to have higher routing overheads than DSR and AODV, especially in low mobility situations in comparison. However, DSDV has been shown to have high routing overheads in high mobility situations, even more so than OLSR, according to a previous comparison between the two protocols [52]. 5.1.4 Optimised Link State Routing protocol (OLSR) OLSR is one of two, proactive routing protocol, but is the only link state protocol chosen within simulations. OLSR floods it's link state through the network, sharing all routing information to every node. Whilst link state flooding can produce a better performing network with more accurate given to every nodes to calculate more efficient paths, it can produce higher routing overheads. To resolve this issue with higher routing overheads, OLSR uses Multipoint relays (MPR) to take topology information. A Multipoint Relay (MPR) is a designated node which takes in topology information and uses it to calculate routes. MPR's also broadcasts packets to be flooded through the network. HELLO packets are flooded sprayed out by nodes to neighbouring nodes to find and maintain node adjacencies. Hello packets also contain link status and neighborhood information of other nodes within the MANET of up to two hops. HELLO packets are also sent to MPRs to help calculate topology information, mainly due to information of neighborhood relationships. Nodes also send out Topology Control messages (usually every 2 seconds) to share information about neighborhood relationship between other nodes. Topology Control messages are also received by the MPR who also forwards to each other to help build up routing paths based on neighbourhood information from other nodes. OLSR tends to work well with TCP traffic as shown in a previous simulation of a VANET with 50 nodes [54]. Furthermore, OLSR is the only routing protocol tested which has an well researched hierarchical implementation (H-OLSR). Moreover, OLSR is the only routing protocol which supports QoS, which was deemed in previous sections as a feature which could potentially help with better utilisation of low bandwidth, especially if different types of traffic are to be sued. OLSR however tends to have higher routing overheads, especially at moderate to larger networks, mainly due to its link state routing and proactive nature. 5.2 Simulation Results This section will detail upon what simulations have produced and interpretation of such simulations. 5.2.1 Normalised routing load Normalised Routing Load Normalised Routing Load 50 45 40 35 30 25 20 15 10 5 0 AODV DSR DSDV OLSR 16 0.0794 0.0794 0.1852 0.8508 32 1.1187 0.6836 0.6491 2.897 64 1.3004 1.2064 0.7782 3.884 128 5.578 4.0186 7.6448 12.3089 256 4.4232 4.8402 7.2245 43.9886 Figure 7 Normalise Routing Load Results All protocols, show fairly low routing overheads between 16 and 64 nodes, though OLSR's routing overhead is higher than all protocols at all sample sizes. DSDV, whilst considered to be of high routing overheads, does not appear to have high routing overheads at larger network sizes. As a matter of fact, DSDV has lower routing overheads than DSR and AODV (Though, marginally) at 32 and 64 nodes. This could be due to the fact that the mobility model used within the simulation has adequate amount of movement which makes AODV and DSR having to re-calculate routes more constantly. One networks reaches at around 128 nodes, routing overheads rapidly increases, especially for OLSR, which worsens for OLSR at 256 nodes, showing that routing overheads could possibly be unsustainable for OLSR. 5.2.2 Packet Delivery Ratio Packet Delivery Ratio Packet Delivery Ratio 120.00% 100.00% 80.00% 60.00% 40.00% 20.00% 0.00% AODV DSR DSDV OLSR 16 95.62% 97.35% 69.35% 87.26% 32 42.94% 44.14% 30.74% 37.85% 64 45.35% 47.69% 34.46% 41.15% 128 18.00% 17.66% 4.15% 15.89% 256 2.61% 2.55% 2.60% 2.67% Figure 8 Packet Delivery Ratio Results Packet Delivery Ratio for AODV and DSR are nearly perfect at 16 nodes (95.62% and 97.35% respectively) with OLSR showing decent PDR at 16 nodes. DSDV however shows significantly lower PDR at 69% at 16 nodes. PDR performance drastically drops at 32 nodes but increases at 64 nodes. Note this increase is possible due to the different densities of each simulations, since at 32 nodes, the size of the MANETS were 1500 x 1500 and 2000 x 2000 at 64 nodes, meaning the possibilities of direct connections skewing results. PDR also drastically drops at 128 nodes and higher, indicating poor PDR, possibly due to the size of the network producing bigger routing overheads. This can be explained when looking at hop count, in which the MANET needs to calculate longer paths. This with mobility put into place has possibly causes longer routing paths or infinite routing paths (especially with DSDV). Routing overhead may also have influence upon the PDR figures, since both AODV and DSR have lower routing overheads in comparison with OLSR. DSDV however skews this claim, since it shows lower routing overheads at 32 and 64 nodes. 5.2.3 End to End Delay End to End Delay (ms) End to End Delay 1.8 1.6 1.4 1.2 1 0.8 0.6 0.4 0.2 0 AODV DSR DSDV OLSR 16 0.2406 0.4505 0.0193 0.0174 32 0.2002 0.2876 0.0182 0.0133 64 0.2546 1.1283 0.0143 0.0189 128 0.3779 1.5715 0.0129 0.0492 256 0.0065 0.0068 0.0066 0.0065 Figure 9 End to End Delay Results End to End delay shows both proactive protocols (DSDV and OLSR) to have less packet delay than AODV and DSR consistently. Both AODV and DSR show relatively larger packet delays, however DSR's End to End delay worsens at larger MANETs ,especially at 128 nodes. The decrease of end to end delay for DSR could be explained by the density of the network increasing, with 1500 x 1500 at 32 nodes vs 1000 x 1000 size at 16 nodes, therefore more direct connections are occurring or more efficient routes produced (More so towards more direct connections, mainly due to similar hop counts at 16 and 32 nodes). At 256 nodes, End to End delay drops dramatically, below even figures given at 16 nodes. This is a good indicator that only direct connections are occuring, basing on average hop count figures show no hops produced, low PDR and low utilisation of bandwidth (throughput). 5.2.4 Throughput Throughput Throughput (Kbps) 60 50 40 30 20 10 0 AODV DSR DSDV OLSR 16 55.232 56.416 39.904 50.176 32 20.48 21.088 14.592 18.016 64 16.992 17.864 12.84 15.384 128 5.024 4.936 1.16 4.48 256 0.69 0.676 0.686 0.704 Figure 10 Throughput Results Throughput figures shows correlations with changes in comparison with the PDR, with AODV and DSR performing better at 16 nodes, OLSR performing quite well and DSDV not so well. Throughput halves at 32 nodes with performance periodically dropping at larger sizes. MANETS at 128 and 256 nodes shows very little throughput. 5.2.5 Average Hop Count Average Hop Count Normalised Routing Load 40 35 30 25 20 15 10 5 0 AODV DSR DSDV OLSR 16 3 5 1 2 32 5 5 2 2 64 7 9 2 3 128 30 37 3 25 256 0 1 0 0 Figure 11 Average Hop Count Results Hop counts appear to be fair at 16 and 32 nodes with the reactive protocols (AODV and DSR) with slightly higher hop counts than the proactive protocols (DSR, DSDV). At 64 nodes, DSDV and OLSR remain consistent, where as AODV and DSR show slight increases. at 128 nodes AODV and DSR hop count figures rises, with DSDV's figures staying consistent. However, DSDV's figures may has less to do with efficiency of the routing protocol and more to do with lack of convergence, based on its throughput and Packet Delivery Ratio. 256 nodes shows all MANETs with little to no routing activity, since no hops are generated. 5.3 Summary of simulation results Simulations have provided both reasonable and contradictory results based on assumptions from past simulations. DSDV appears to have lower routing overheads than expected, despite being a proactive protocol, in comparison with reactive protocols. This could be due to the mobility introduced into simulations, which has caused an increase of routing overheads for the reactive protocols. Furthermore, DSR is claimed to have lower overheads than AODV, however the figures presented in simulations appear to be negligible. When looking at end to end connectivity metrics, performance of both protocols are close, with DSR (Except for End to End Delay and Average Hop Count) performing slightly better. DSDV could also possibly suffering from routing loops due to outdated routing paths. DSDV only updates routing paths every 30 seconds, in comparison to OLSR periodically sending out topology control messages every 2 seconds and DSR/AODV whenever a route is requested. With old routing paths used, this can cause packets to loop through the network, time out and be dropped. When looking at what size the lower level MANETs should be when implementing a hierarchical network, it appears that 16 nodes would perform the most adequate. Majority of protocols and performance metrics showed performance drops at 32 and 64 nodes, with major performance drops at over 100 nodes. With tradeoffs between routing overheads and end to end connectivity, it is important to look at routing overheads from how they are caused. On the basis of routing overheads caused by the increase of complexity of the network, then simulations have shown that with larger networks, and with more complex routing required, routing overheads can affect the performance of the network. However, on the basis of routing overheads as in the structure of how the protocol works, routing overheads appear to have less of an effect on performance of the routing protocol. OLSR, with the highest amount of routing overhead appears to perform more consistent through all metrics, whereas the other routing protocols perform worse on certain metrics but perform better on others. It appears performance is more so influenced through the how the routing protocol works, rather than how much work the routing protocol. Due to its known support for QoS and well known hierarchical implementation, along with consistent performance amongst all performance metrics, OLSR appears to be best suited for military MANET usage. 6. Conclusion, Future Work 6.1 Conclusion Starting from literature review, MANETS appear to be completely different from a typical structured network and require more attention on certain aspects. MANETs generally do not performance as well structured networks, but are desirable due to its self configuration and low maintenance aspects. With that in perspective, MANETs will also require special attention to what type of routing protocol to be chosen when looking at the networking aspect. Whilst already established routing protocols, such as RIP and OSPF are possible candidates, mainly due to wide support and knowledge, they do tend to fail when put on MANETs. Whilst that was not to proven through simulations due to lack of availability of such algorithms on NS-2, it was demonstrated through MANET extensions such protocols which showed the adjacency problem. When looking at MANETs, one aspect which has popped is the routing overhead, which is the amount of resources used to maintain routing. What was the main job of the router is now the job of end devices. Since end devices typically do not have the capabilities of a router, it is important for such overheads to be reduced. One major influence on routing overheads, as shown in simulations, was the size of the network, in which the complexity of the size of the topology causes more overheads and a reduction of performance. One method of reducing routing overheads is to structure the MANET in a hierarchical fashion, in which the overall MANET is divided into smaller MANETs. Whilst the theory of hierarchical MANETs producing less routing overheads and better end to end connectivity is not tested through simulations, the performance of flat topology MANETs is proven to be hampered as the network is scaled up. Simulations on flat topology MANETs showed that the protocol had little effect on routing overheads in comparison to the size. Sizes were based on different levels of military structure. The thesis also looked at aspects of simulation and how they can influence results. One aspect was the mobility model, which was explained to have a similar effect to terrain, only without discrepancies in connection due to climate. Simulations also showed that the protocol's routing overhead had little effect on the protocol of the MANET. 6.2 Future Work The state of the thesis is incomplete, mainly due to lack of resources and time to depict an adequate answer in regards to hierarchical MANETS. Hierarchical MANETs were not directly compared within this research, therefore for future research, Hierarchical MANETs should be simulated. This could be produced through the customization of one of the routing protocols (such as OLSR) on NS-2. However, there is an implementation of H-OLSR known to be available on OPNET which could be used to simulate to compare between a hierarchical and flat topology MANET. It is also shown for optimal performance, MANETs should have as little nodes as possible, thus requiring the Hierarchical model to support a large number of MANETS. It is current unknown as to how a node in a higher level MANET could support the number of smaller MANETS. More research, especially simulations, should look at this aspect. As for getting a better representation of a military mobility, a better mobility model could be used based on known movements of combatants. Different mobility models could be customised for different military scenarios. Minus geographical and climate constraints, a good mobility model can produce something closer to harsher terrain. Structured routing protocols are typically not suitable in their current form, unless the protocol is modified to suite typical MANET conditions. There are several key aspects which could be used to identify whether the protocol is suitable for MANETS. Adjacencies How the routing protocol produces adjacencies to work out optimal routing paths can affect the performance. Do they try to form adjacencies with every node within a network? Many structured network protocols try to do that, mainly due to expectations of limited physical ports. In wireless, than can be dangerous, especially when there are many nearby nodes within the same network. Flooding of Packets Many structured MANET protocols flood packets to maintain adjacencies and to discover/maintain routing. If too many packets are flooded, higher routing overheads will be produced. However, too little can hamper the efficiency of a routing protocol in the form of in efficient routes, delays, and poor packet delivery. Method of reducing Routing Overhead It is important to see if the protocol attempts to reduce routing overheads, since this can be critical upon the performance of the overall network. Does it attempt such reduction of overheads? If so, does it produce any performance gains, or where does the performance decrease? One aspect to look at if it divides/clusters or forms hierarchies of the network. Furthermore, a simpler network protocol does not always mean a better performing one. DSDV was one of the first implementations of a MANET protocol and is the simplest of the 4 tests, however it performed significantly poor with certain aspects of simulation. 7. References [1]Teare, D. (2012). Implementing Cisco IP Routing (ROUTE) Foundation Learning Guide. Indiapolis, IN, USA, Cisco Press. [2]Subbarao, M. W. (1999). Ad Hoc Networking Critical Features and Performance Metrics. National Institute of Standards and Technology, Wireless Communications Technology Group: 11. [3]Schechter, E. (2013). Mobile ad hoc networks end reliance on infrastructure: 1. Accessed 20/03/14. URL: http://www.c4isrnet.com/article/M5/20131113/C4ISRNET04/311130028/Mobile-ad-hoc-networksend-reliance-infrastructure [4]Plesse, T., et al. (2004). OLSR Performance Measurement in a Military Mobile Ad-hoc Network. Proceedings of the 24th International Conference on Distributed Computing Systems Workshops (ICDCSW’04) - IEEE: 6. [5]Fischer, J. o., et al. (2012 ). A measurement-based path loss model for wireless links in mobile ad-hoc networks (MANET) operating in the VHF and UHF band Topical Conference on Antennas and Propagation in Wireless Communications (APWC). Cape Town, South Africa: 349 - 352. [6]Wang, H., et al. (2007). IMPLEMENTING MOBILE AD HOC NETWORKING (MANET) OVER LEGACY TACTICAL RADIO LINKS Military Communications Conference. Orlando, FL, USA 1 - 7 [7]Marti, S., et al. (2000). Mitigating Routing Misbehavior in Mobile Ad Hoc Networks. MobiCom '00 Proceedings of the 6th annual international conference on Mobile computing and networking 11. [8]Kamal, J. M. M., et al. (2010). Lessons Learned from Real MANET Experiments and Simulation-based Evaluation of UDP and TCP Proceedings of 13th International Conference on Computer and Information Technology, Dhaka, Bangladesh. [9]Spiewla, J. K. Dynamic Routing Protocols and Energy Efficient Communication in Mobile Ad Hoc Networks. EE 4272 - Computer Networks,Michigan Technological University [10]T.S.Asha and Dr.N.J.R.Muniraj Network Connectivity based Energy Efficient Topology Control Scheme for MANET Proceedings of International Conference on Optical Imaging Sensor and Security, Coimbatore, Tamil Nadu, India. [11]James, S. (2008, 2008). "OSPF Extensions for Mobile Ad-hoc Networks." from http://www.cse.wustl.edu/~jain/cse574-08/ftp/ospf/. [12]Spagnolo, P. A. and T. R. Henderson (2006). Comparison of Proposed OSPF MANET Extensions. Military Communications Conference. MILCOM 2006. Washington, DC IEEE: 1-7. [13]Chaparro, P. A., et al. (2010). Supporting scalable video transmission in MANETs through distributed admission control mechanisms. Euromicro Conference on Parallel, Distributed and Network-based Processing. Pisa, Italy, IEEE. 18th: 238 - 245 [14]Belding-Royer, E. M. Hierarchical Routing in Ad hoc Mobile Networks, University of California: 22. [15]Lee, B., et al. (2004). "Issues in Scalable Clustered Network Architecture for Mobile Ad Hoc Networks." Hhandbook of Mobile Computing. [16]Chunhua, Z. and T. Cheng (2009). A Multi-Hop Cluster Based Routing Protocol for MANET. 1st International Conference on Information Science and Engineering (ICISE). Nanjing, China: 2465 - 2468 [17]Park, V. D. and M. S. Corson (1997). A Highly Adaptive Distributed Routing Algorithm for Mobile Wireless Networks. Proceedings of IEEE InfoCom', Kobe, Japan. [18]Wang, M., et al. (2007). Comparison of Two Hierarchical Routing Protocols for Heterogeneous MANET Defence R&D Canada -- Ottawa: 44. [19]Broch, J., et al. (1998). A Performance Comparison of Multi-Hop Wireless Ad Hoc Network Routing Protocols. Proceedings of the Fourth Annual ACM/IEEE International Conference on Mobile Computing and Networking (MobiCom’98),. ACM. Dallas, Texas, USA. [20]Shiflet, C. F., et al. (2004). Address Aggregation in Mobile Ad hoc Networks. Communications, 2004 IEEE International Conference IEEE. 6. [21]Villasenor-Gonzalez, L., et al. (2005). HOLSR: A Hierarchical Proactive Routing Mechanism for Mobile Ad Hoc Networks. IEEE Communications Magazine, IEEE: 8. [22]Sheltami, T. and H. Mouftah (2003). A Comparative Study of On-demand and Cluster-based Routing Protocols in MANETs Conference Proceedings of the Performance, Computing, and Communications Conference, Canada, IEEE International. [23]Joa-Ng, M. and I.-T. Lu (2000). A GPS-based Peer-to-Peer Hierarchical Link State Routing For Mobile Ad Hoc Networks IEEE 51st Vehicular Technology Conference Proceedings, Tokyo, Japan, IEEE. [24]SEDDIK-GHALEB, A., et al. (2009). TCP Computational Energy Cost within Wireless Mobile Ad Hoc Network Rabat, Morocco: 955-962. [25]Morgan, Y. L. and T. Kunz (2005). A Design Framework for Wireless MANET QoS Gateway Wireless Conference 2005 - Next Generation Wireless and Mobile Communications and Services (European Wireless). 11th European: 1 - 7. [26]Evans, S. C., et al. (2005). Route Based QoS and the Biased Early Drop Algorithm (BED) Second International Conference on Quality of Service in Heterogeneous Wired/Wireless Networks. Lake Vista, FL 8 - 17. [27] Holter, K., et al. (2007). Design and Implementation of Wireless OSPF for Mobile Ad Hoc Networks. University Graduate Center: 6. [28] The Associated Press (2003). Battlefield Internet Helps Forces in Iraq ABC News. [29] Peacock, B. A. (2007). CONNECTING THE EDGE: Mobile Ad-Hoc Networks (MANETs) for Network Centric Warfare. Blue Horizons Paper, Air War College: 51. [30] Naserian, M., et al. (2005). Routing Overhead Analysis for Reactive Routing Protocols in Wireless Ad Hoc Networks, IEEE. [31] Thipchaksurat, S. and P. Kirdpipat (2011). Position-based Routing Protocol by Reducing Routing Overhead with Adaptive Request Zone for Mobile Ad Hoc Networks The 8th Electrical Engineering! Electronics, Computer, Telecommunications and Information Technology (ECTI) Association of Thailand. Thailand, IEEE. 8: 389 - 392. [32] Jacquet, P. (2000). Overhead in Mobile Ad-hoc Network Protocols. L. Viennot. LE CHESNAY Cedex (France), Unit´e de recherche INRIA Rocquencourt. 1: 23. [33] Guide, C. (2014). "CCNP ROUTE 642-902 :: OSPF | CCNP Guide:." Retrieved 5/5/2014, 2014, from http://www.ccnpguide.com/ccnp-route-642-902-ospf/. [34] Ogier, R. (2008). OSPF-MDR: Extension of OSPF for Mobile Ad Hoc Networks. [35] Ogier, R. G. and (2009). Mobile Ad Hoc Network (MANET) Extension of OSPF Using Connected Dominating Set (CDS) Flooding. MANET Extension of OSPF. P. Spagnolo, IETF - RFC: 71. [36] Wu, K. QoS Support in Mobile Ad Hoc Networks. J. Harms. University of Alberta - Computing Science Department. [37] Perkins, C., et al. (2003). Ad hoc On-Demand Distance Vector (AODV) Routing. University of California, Santa Barbara, The Internet Society: 37. [38] (2007). "Ad hoc On-Demand Distance Vector Routing." Retrieved 20/5/14, 2014, from http://moment.cs.ucsb.edu/AODV/aodv.html. [39] Johnson, D. B. Dynamic Source Routing in Ad Hoc Wireless Networks. D. A. Maltz, Computer Science Department Carnegie Mellon University. [40] Jacquet, P., et al. Optimized Link State Routing Protocol for Ad Hoc Networks. Le Chesnay Cedex, France, INRIA Rocquencourt. [41] Aschenbruck, R. Ernst, E. Gerhards-Padilla, and M. Schwamborn: "BonnMotion - a Mobility Scenario Generation and Analysis Tool," in Proc. of the 3rd International ICST Conference on Simulation Tools and Techniques (SIMUTools '10), Torremolinos, Malaga, Spain, 2010. [42] F. Bai, N. Sadagopan, and A. Helmy, Important: a framework to systematically analyze the impact of mobility on performance of routing protocols for ad hoc networks, in Proceedings of IEEE Information Communications Conference (INFOCOM 2003), San Francisco, Apr. 2003 [43] Bai, F. and A. Helmy A SURVEY OF MOBILITY MODELS in Wireless Adhoc Networks University of Southern California,U.S.A Southern California. [44] Henderson, T. (2005). "Network Components in a mobilenode." from http://www.isi.edu/nsnam/ns/doc/node173.html. [45] Henderson, T. (2005). "LL(link-layer) Class" from http://www.isi.edu/nsnam/ns/doc/node155.html. [46] Sasson, D. C. Y. and A. Schiper (2002). "On the Accuracy of MANET Simulators ∗.", Distributed Systems Laboratory Ecole Polytechnique Fed´ er´ ale de Lausanne (EPFL) [47] Fasolo, E., et al. (2007). VoIP Communications in Wireless Ad-hoc Network with Gateways. 12th IEEE Symposium on Computers and Communications,. [48] Ros, F. J. (2014). "UM-OLSR." from http://masimum.inf.um.es/fjrm/development/um-olsr/. [49] Perkins, C. (2003). "RFC-3561 Ad Hoc On-Demand Distance Vector (AODV) Routing." from https://www.ietf.org/rfc/rfc3561.txt. [50] Grepet, A. C. C. and S. Maag "A Validation Model for the DSR protocol." GET / Institut National des Telecommunications. [51] Sterbenz, H. N. Y. C. E. K. C. J. P. R. J. P. G. (2011). "Destination-Sequenced Distance Vector (DSDV) Routing Protocol Implementation in ns-3." University of Kansas. [52] Kumawat, R. and V. Somani (2011). "Comparative Analysis of DSDV and OLSR Routing Protocols in MANET at Different Traffic Load." International Journal of Computer Applications® (IJCA) International Conference on Computer Communication and Networks. [53] Ade, S. A. and P.A.Tijare (2010). "Performance Comparison of AODV, DSDV, OLSR and DSR Routing Protocols in Mobile Ad Hoc Networks." International Journal of Information Technology and Knowledge Management 2(2). [54] Kumar, S., et al. (2911). "Traffic Pattern Based Performance Comparison of AODV, DSDV & OLSR MANET Routing Protocols using Freeway Mobility Model." / (IJCSIT) International Journal of Computer Science and Information Technologies 2(4): 1606 - 1611.


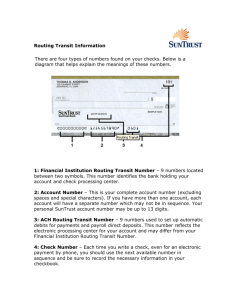

![Internetworking Technologies [Opens in New Window]](http://s3.studylib.net/store/data/007474950_1-04ba8ede092e0c026d6f82bb0c5b9cb6-300x300.png)


