1 - ADL
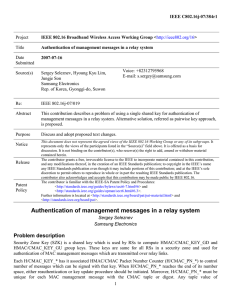
advertisement
Security Issues in Mobile WiMAX(IEEE 802.16e) Frank, A Ibikunle Covenant University, Electrical and Information Engineering Department, Ota. 2009 IEEE Mobile WiMAX Symposium Wimax ☺802.16x ☺802.16d (fixed) ☺802.16e (mobile) ☺802.16e ----3G : 韓國(WiBro), 美國, 中 國大陸(專利) ☺802.16m ---- 4G : 起步 台灣與全球 頻譜與執照 北區 南區 全區 全球 Map: http://www.wimaxmaps.org/ 和WiFi的不同 http://www.youtube.com/watch?v=chlG qhRKVjQ 基本名詞 Ớ Main roles involved in 802.16: Ớ Base Station (BS) Ớ Mobile Station (MS) / Subscriber Station (SS) Ớ Two security protocols of interest: Ớ Authentication/Authorization protocol, establishes a shared Authorization Key (AK) Ớ 3-way Traffic Encryption Key (TEK) Handshake Ớ AK used to derive various other keys Ớ Traffic Encryption Keys are used to encrypt message data between the BS and MS Ớ KEK: key encryption key Ớ MBS: Multicast and Broadcast Service 3-way TEK Handshake After authentication, BS initiates a 3-way handshake to transfer TEKs to MS TEKs generated by BS Have a specified lifetime, after which new TEK is requested by MS Structure of the 3-way handshake: Challenge: BS → MS Request: MS → BS Response: BS → MS Define Security: protection of data being transmitted over a wireless networks. CIA Confidentiality: Allowing only that the intended legitimate recipients to read encrypted messages(information). Integrity: is referred to as ensuring that another party has not altered messages after it has been sent. Authentication: This is making sure that parties sending messages or receiving messages are who they say they are, and have the right to undertake such actions. On wired networks: VPNs IPSec IDS Firewalls… Major Problem Securing wireless signal is in its mode of transmission communicated through the air. 802.16e provides 2 authentication RSA 加密演算法: 因數分解 難度和bits有關 EAP(Extensible Authentication Protocol) EAP 常用在無線網路 Data link layer Packet An authentication framework: only define message format and has many methods. Using EAP can define a way to encapsulate EAP messages. Provides some common functions and negotiation of authentication methods called EAP methods. MAC Message Authentication Code Like Digital Signature, but using symmetry key. Initial network 1. EAP-based authentication. 2. The BS and BS set up a common AK. 3. KEK is derived from the AK. (and AK is used to securely transfer further keys) 4. MAC digest and the transferred TEK is encrypted by the KEK. 5. After above, the 3-way TEK-exchange for each data connection is executed. AK – KEK - TEK Security Flaws 1. Unauthenticated messages 2. Unencrypted management communication 3. Shared keys in Multicast and Broadcast Service Unauthenticated messages Most of the management messages defined in IEEE 802.16e are integrity protected. Done by: HMAC: Hash based message authentication code CMAC: Cipher based message authentication code But some messages are not covered by any authentication mechanism. Unauthenticated messages MOB_TRF-IND: Traffic Indication message MOB_NBR-ADV: Neighbor Advertisement message FPC: Fast Power Control message MSC-REQ: Multicast Assignment Request message DBPC-REQ: Downlink Burst Profile Change Request message 6. PMC-REQ: 7. MOB_ASC-REP: Association Result Report 8. RNG-REQ: Ranging Request message 1. 2. 3. 4. 5. Unencrypted management communication In Mobile WiMAX management messages are still sent in the clear. Nearly all management information exchanged between MS and BS can be accessed by a listening adversary. Collecting management info can create detailed profiles about MSs. Including capabilities of devices, security settings, associations with base stations… Also can determine the movement and approximate position of the MS. Shared keys in Multicast and Broadcast Service Encrypted symmetrically with a shared key. Also message authentication is based on the same shared key. This alg. Contains the vulnerability that every group member can also encrypt and authenticate broadcast messages as if they originate from the real BS(be forged). Shared keys in Multicast and Broadcast Service GTEK: Group TEK MBRA: Multicast and Broadcast Rekeying Algorithm The Solutions 1. For Unauthenticated messages: 1. Easily using a HMAC or CMAC digit as well. 2. But most messages are very short, a tradeoff between the security and the effectiveness of the protocol has to be found. 3. Suggestion: use CMAC and Short HMAC to 64bits, and with all other needed parameters (i.e., packet number, key sequence number and reserved fields), both will be 104 bits in total. HMAC 詳細請看: http://en.wikipedia.org/wiki/HMAC Use SHA-1 (128bits ?) SHA: Secure Hash Algorithm CMAC 詳細請看: http://en.wikipedia.org/wiki/CMAC , too.(有點複雜......) Use AES-128 (感覺也很偉大……) AES: Advanced Encryption Standard A symmetric-key encryption standard adopted by the U.S. government. 2. For Unencrypted management communication: 1. Encrypt directly after both sides have established a common key. 2. Doesn’t introduce any overhead to the connection. 3. Possible to use a symmetric key, decryption can be processed very fast. 3. For broadcasted/multicasted messages(shared keys): 1. From outside the group. 2. Use asymmtric cryptography(but may not effective). 3. And for the MBS, see Figures as followings. Figure 1. Possible solutions to transmit GTEK in a secure way Figure 2. Avoiding key forgery by a GTEK hash chain Contributions 1. Describe different security vulnerabilities found in IEEE 802.16e. 2. Proffer possible solutions to eliminate them. Thanks Q&A