Web Security
advertisement

Web Security
CS598MCC Spring 2013
Yiwei Yang
• Definition
a set of procedures, practices, and
technologies for assuring the reliable,
predictable operation of web servers, web
browsers, other programs that communicate
with web servers, and the surrounding
Internet infrastructure.
• Three components
Web
Browser
Web
Server
Data in
transit
Privacy issue with web browser
• Where does information leak out?
1. Provided by users (registration form)
2. Log files
- Web logs (IP, time, requested URL, browser type,
username if authentication is used …)
proxy servers can obscure web log
- Mail logs (from, to, …)
- DNS logs (name, IP, query…)
- RADIUS logs
Privacy issue with web browser
• Where does information leak out?
3. Web bugs
<img src=“ … “width=1 height=1 border=0 />
outsourced web site monitoring
4. Cookie
- user’s actual data
- a number of codes that key into a database that
resides at the web provider
Privacy issue with web browser
• Attacks related with cookies
1.XSS(Cross-site scripting)
- Nonpersistent
- Persistent
Prevention
- Better cookie handling
- Disable the script
Privacy issue with web browser
• Attacks related with cookies
2. CSRF(Cross-Site Request Forgery)
- belongs to Deputy attack
- carried out attack from user himself
Prevention
- Better cookie handling
- Authentication for each operation
- Random number
RADIUS(Remote Authentication Dial
In User Service )
• Application layer client/server protocol on top of
UDP
• Authentication, Authorization, Accounting (AAA)
• RADIUS Server
- daemon process running on Unix or Window NT machine
• RADIUS Client
- access server(gateway) that control access to network( RAS,
NAS, VPN server)
Radius Packet format
Authentication and Authorization
1.User initiates authentication to the NAS.
2.NAS prompts for username and password.
3.User replies.
4.RADIUS client sends username and encrypted password to the
RADIUS server.
5.RADIUS server responds with Accept, Reject, or Challenge.
6.The RADIUS client acts upon services and services parameters
bundled with Accept or Reject.
Authentication and Authorization
• Client sends out access-request packet
- request authenticator is a random 16 octet string
- password is encrypted
p is divided into p1,p2,…..pn where pi is a 16-octet block
c1 = p1 XOR MD5(S || request authenticator )
c2 = p2 XOR MD5(S || c1 )
…….
cn = pn XOR MD5(S || cn-1)
- sent to port 1812 of server
Authentication and Authorization
• Server received the packet
• Drop it if no shared secret
• Otherwise authenticate the user
- access-accept( parameters used for this session including
access list to apply)
- access-reject
- access-challenge
response authenticator = MD5 (code || ID|| length|| request authenticator||
attributes || s)
• Send out the packet to client
Authentication and Authorization
• Client drop the packet if it doesn’t have
corresponding identifier or calculation on response
authenticator doesn’t match
• Otherwise the user is authenticated if received
access-accept
• What can go wrong?
Attacks on RAIDUS
• Response Authenticator Based Shared Secret
Attack
• User-Password Attribute Based Shared Secret
Attack
• User-Password Based Password Attack
• Active User-Password Compromise through
Repeated Request Authenticators
• We need to secure the traffic
Accounting
Secure Network Connection
Cryptographic protocol
• Offline encryption communication protocol
-PGP/OpenPGP, S/MIME
• Online encryption communication protocol
-SSL, IPsec, Kerberos, SET, SSH
SSL(Secure Sockets Layer)
SSL Record Protocol
Handshake Protocol: Phase 1 and 2
SSL: Handshake Round 1
{ vC || r1 || s1 || ciphers || comps }
Client
Server
{v || r2 || s1 || cipher || comp }
Client
vC
v
r1, r2
s1
ciphers
comps
cipher
comp
Server
Client’s version of SSL
Highest version of SSL that Client, Server both understand
nonces (timestamp and 28 random bytes)
Current session id (0 if new session)
Ciphers that client understands
Compression algorithms that client understand
Cipher to be used
Compression algorithm to be used
SSL: Handshake Round 2
Client
Client
Client
Client
{certificate }
{mod || exp || SigS(h(r1 || r2 || mod || exp)) }
{ctype || gca }
{er2 }
Server
Server
Server
Server
Note: if Server not to authenticate itself, only last message sent; third
step omitted if Server does not need Client certificate
kS Server’s private key
ctype
Certificate type requested (by cryptosystem)
gca Acceptable certification authorities
er2 End round 2 message
Handshake Protocols: Phases 3 and 4
SSL: Handshake Round 3
Client
{ client_cert }
Client
{ pre }PubS
Server
Server
Both Client, Server compute master secret master:
master = MD5(pre || SHA(‘A’ || pre || r1 || r2) ||
MD5(pre || SHA(‘BB’ || pre || r1 || r2) ||
MD5(pre || SHA(‘CCC’ || pre || r1 || r2)
Client
{ h(master || opad || h(msgs || master | ipad)) }
Server
msgs
Concatenation of previous messages sent/received this handshake
opad, ipad As above
SSL: Handshake Round 4
Client sends “change cipher spec” message using that protocol
Client
Server
{ h(master || opad || h(msgs || 0x434C4E54 || master || ipad )) }
Client
Server
Server sends “change cipher spec” message using that protocol
Client
Server
{ h(master || opad || h(msgs || 0x53525652 || master | ipad)) }
Client
Server
msgs
Concatenation of messages sent/received this handshake in
previous rounds (does notinclude these messages)
opad, ipad, master As above
SSL
• What does SSL provide us?
- Data integrity, Confidentiality
- Authentication(handshake)
• Limitation on SSL
- doesn’t work with connection less protocol
- doesn’t support non-repudiation
- doesn’t protect the application itself
- general-purpose data security
• Misuse of SSL
TLS(Transport Layer Security)
• SSL 3.0 served as the basis for TLS 1.0(SSL 3.1)
• Slightly different from SSL
- Message Authentication (HMAC)
- key derivation
- Finished
-Alert protocol message type
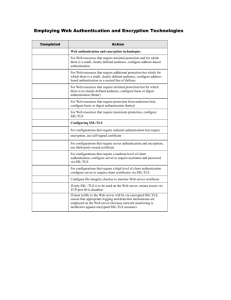
Secure Web Server
•
Based on CIA, what do we need to secure?
• Three steps to secure server
1. Host security
2. Secure web service
3. Examine interaction between OS and web service
References
• RADIUS
http://en.wikipedia.org/wiki/RADIUS
http://www.cisco.com/en/US/tech/tk59/technologies_tech_note09186a0080
0945cc.shtml
• SSL
https://wiki.engr.illinois.edu/download/attachments/202934655
/ssl-ipsec.pdf?version=1&modificationDate=1348193253000
Thank you!