Telnet/ssh
advertisement

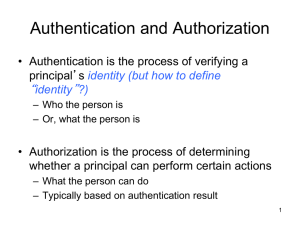
Telnet/SSH Tim Jansen, Mike Stanislawski • TELNET is short for Terminal Network • Enables the establishment of a connection to a remote system, so that the local terminal appears to be the terminal at the remote location. • Usually establishes its connection on port 23 Local log-in • Log-in is performed with a username and a password. • Keystrokes accepted at the terminal driver and passed to the operating system. • Operating system interprets the keystrokes and performs an action Remote Log-in • Terminal Driver accepts keystrokes and passes them to the TELNET client • Client transforms characters to network virtual terminal (NVT) character and delivers them to TCP/IP protocol stack • Passed online to the server’s TCP/IP stack and then to the TELNET server which deciphers the NVT characters • The decoded characters are passed to a pseudoterminal driver because the Operating System is only designed to receive characters from a terminal driver. NVT • Uses two sets of characters one for data and the other for control • Data characters are represented with the same 7 lowest-order bits as ASCII and the highest-order bit is 0. • Control characters highest-order bit is 1 Embedding • The same connection is used for sending both data and control characters. • Control characters are embedded in the data stream. • A control character is recognized by a preceding character of 11111111, this is the IAC (Interpret as control) character. Options • Options are extra features available to a user with a more sophisticated terminal. • Simple terminals use default features. • Option negotiation entails using four control characters, WILL, WONT, DO, DONT • WILL is sent as a question “Will I enable the option? • DO is sent as a request “Do enable the request” • WONT is sent to say “I won’t use this option anymore” • DONT is sent to say “Don’t use it anymore” Modes • Default Mode – used if no other modes are invoked. • Character Mode – each character is sent to the server, but the server may delay sending back the information. Creates overhead because 3 TCP segments are sent per character. • Line Mode – line editing is done by the client, and then sent as a whole line to the server. Security • TELNET is unencrypted, making it very easy to intercept. • Most implementations have no authentication to ensure communication is carried out. TELNET Today • TELNET has in the past few years been overtaken by remote login • It is still used in such ways as debugging network services. SSH • SSH is short for Secure Shell • Unlike TELNET, SSH uses a form of encryption • The encryption is public-key • SSH is also a remote login protocol • It can be used for file transfer with SFTP or SCP • Listens on standard TCP port 22 Uses of SSH • For remote login • Executing single lines on a remote host • Copying files from a local server to a remote host • As a secure alternative to FTP Transport Layer • Handles initial key exchange • Sets up encryption and compression • Also arranges for key re-exchange after an hour or 1GB is transferred. User Authentication Layer • • • • Handles client authentication Password authentication Public key authentication And others Connection Layer • Defines channel requests • Multiple channels can be hosted at once • Direct-TCP/IP handles client-to-server forwarded connections • Forwarded-TCP/IP handles server-toclient forwarded connections Security • Defends against – IP spoofing, where a remote host sends out packets which pretend to come from another, trusted host. Ssh even protects against a spoofer on the local network, who can pretend he is your router to the outside. – IP source routing, where a host can pretend that an IP packet comes from another, trusted host. DNS spoofing – DNS spoofing, where an attacker forges name server records Security cont. • Also protects against – Interception of cleartext passwords and other data by intermediate hosts – Manipulation of data by people in control of intermediate hosts • In short, SSH trusts nothing • SSH is secure assuming the option of encryption “none” is not chosen