Security - ECE Users Pages
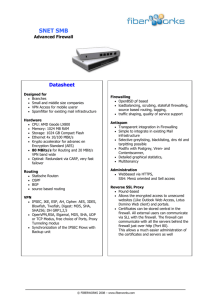
advertisement

Network Security Attacks Technical Solutions The Problem of Network Security The Internet allows an attacker to attack from anywhere in the world from their home desk. They just need to find one vulnerability: a security analyst needs to close every vulnerability. Hacking Networks Phase 1: Reconnaissance Physical Break-In Dumpster Diving Google, Newsgroups, Web sites Social Engineering Phishing: fake email Pharming: fake web pages WhoIs Database & arin.net Domain Name Server Interrogations Registrant: Microsoft Corporation One Microsoft Way Redmond, WA 98052 US Domain name: MICROSOFT.COM Administrative Contact: Administrator, Domain domains@microsoft.com One Microsoft Way Redmond, WA 98052 US +1.4258828080 Technical Contact: Hostmaster, MSN msnhst@microsoft.com One Microsoft Way Redmond, WA 98052 US +1.4258828080 Registration Service Provider: DBMS VeriSign, dbms-support@verisign.com 800-579-2848 x4 Please contact DBMS VeriSign for domain updates, DNS/Nameserver changes, and general domain support questions. Registrar of Record: TUCOWS, INC. Record last updated on 27-Aug-2006. Record expires on 03-May-2014. Record created on 02-May-1991. Domain servers in listed order: NS3.MSFT.NET 213.199.144.151 NS1.MSFT.NET 207.68.160.190 NS4.MSFT.NET 207.46.66.126 NS2.MSFT.NET 65.54.240.126 NS5.MSFT.NET 65.55.238.126 Hacking Networks Phase 2: Scanning War Driving: Can I find a wireless network? War Dialing: Can I find a modem to connect to? Network Mapping: What IP addresses exist, and what ports are open on them? Vulnerability-Scanning Tools: What versions of software are implemented on devices? Passive Attacks Eavesdropping: Listen to packets from other parties = Sniffing Traffic Analysis: Learn about network from observing traffic patterns Footprinting: Test to determine software installed on system = Network Mapping Carl Bob Jennie Hacking Networks: Phase 3: Gaining Access Network Attacks: Sniffing (Eavesdropping) IP Address Spoofing Session Hijacking Login: Ginger Password: Snap System Attacks: Buffer Overflow Password Cracking SQL Injection Web Protocol Abuse Denial of Service Trap Door Virus, Worm, Trojan horse, Bill Some Active Attacks Denial of Service: Message did not make it; or service could not run Masquerading or Spoofing: The actual sender is not the claimed sender Message Modification: The message was modified in transmission Packet Replay: A past packet is transmitted again in order to gain access or otherwise cause damage Denial of Service Joe Bill Spoofing Joe (Actually Bill) Ann Message Modification Joe Ann Packet Replay Joe Bill Bill Ann Ann Man-in-the-Middle Attack 10.1.1.1 10.1.1.3 (2) Login (1) Login (4) Password (3) Password 10.1.1.2 SQL Injection Java Original: “SELECT * FROM users_table WHERE username=” + “’” + username + “’” + “ AND password = “ + “’” + password + “’”; Inserted Password: Aa’ OR ‘’=’ Java Result: “SELECT * FROM users_table WHERE username=’anyname’ AND password = ‘Aa’ OR ‘ ‘ = ‘ ‘; Inserted Password: foo’;DELETE FROM users_table WHERE username LIKE ‘% Java Result: “SELECT * FROM users_table WHERE username=’anyname’ AND password = ‘foo’; DELETE FROM users_table WHERE username LIKE ‘%’ Inserted entry: ‘|shell(“cmd /c echo “ & char(124) & “format c:”)|’ Welcome to My System Login: Password: Password Cracking: Dictionary Attack & Brute Force Pattern Calculation Result Time to Guess (2.6x1018/month) Personal Info: interests, relatives 20 Manual 5 minutes Social Engineering 1 Manual 2 minutes 80,000 < 1 second American Dictionary 4 chars: lower case alpha 264 5x105 8 chars: lower case alpha 268 2x1011 8 chars: alpha 528 5x1013 8 chars: alphanumeric 628 2x1014 3.4 min. 8 chars alphanumeric +10 728 7x1014 12 min. 8 chars: all keyboard 958 7x1015 2 hours 12 chars: alphanumeric 6212 3x1021 96 years 12 chars: alphanumeric + 10 7212 2x1022 500 years 12 chars: all keyboard 9512 5x1023 16 5x1028 16 chars: alphanumeric 62 Draft NIST SP 800-118 Hacking Networks: Phase 4: Exploit/Maintain Access Control system: system commands, log keystrokes, pswd Backdoor Trojan Horse Useful utility actually creates a backdoor. Replaces system User-Level Rootkit executables: e.g. Login, ls, du Bots Spyware/Adware Replaces OS kernel: Kernel-Level Rootkit e.g. process or file Slave forwards/performs Spyware: Collect info: control to hide commands; spreads, keystroke logger, list email addrs, DOS collect credit card #s, attacks AdWare: insert ads, filter search results Botnets Botnets: Bots Attacker China Handler Hungary Bots: Host illegal movies, music, pornography, criminal web sites, … Forward Spam for financial gain Zombies Distributed Denial of Service Zombies Attacker Handler Victim Russia Bulgaria United States Can barrage a victim server with requests, causing the network to fail to respond to anyone Zombies Question 1. 2. 3. 4. An attack where multiple computers send connection packets to a server simultaneously to slow the firewall is known as: Spoofing DDOS Worm Rootkit Question 1. 2. 3. 4. A man in the middle attack is implementing which additional type of attack(s): Spoofing DoS Phishing Pharming Network Security Network Defense Encryption Security: Defense in Depth Border Router Perimeter firewall Internal firewall Intrusion Detection System Policies & Procedures & Audits Authentication Access Controls Bastion Host Computer fortified against attackers Applications turned off Operating system patched Security configuration tightened Attacking the Network What ways do you see of getting in? Border Router/Firewall The Internet De-Militarized Zone Commercial Network WLAN Private Network Private Network Filters The good, the bad & the ugly… Filter The Good The bad & the ugly Route Filter: Verifies sources and destination of IP addresses Packet Filter: Scans headers of packets and discards if ruleset failed (e.g., Firewall or router) Content Filter: Scans contents of packets and discards if ruleset failed (e.g., Intrusion Prevention System or firewall) Packet Filter Firewall Web Response Illegal Dest IP Address Web Request Email Response SSH Connect Request DNS Request Ping Request Illegal Source IP Address Email Response FTP request Microsoft NetBIOS Name Service Email Connect Request Telnet Request Web Response Firewall Configurations terminal host firewall A A terminal host firewall A A A Router Packet Filtering: Packet header is inspected Single packet attacks caught Very little overhead in firewall: very quick High volume filter Stateful Inspection State retained in firewall memory Most multi-packet attacks caught More fields in packet header inspected Little overhead in firewall: quick Firewall Configurations terminal host firewall A B A B terminal host firewall A B A B Circuit-Level Firewall: Packet session terminated and recreated via a Proxy Server All multi-packet attacks caught Packet header completely inspected High overhead in firewall: slow Application-Level Firewall Packet session terminated and recreated via a Proxy Server Packet header completely inspected Most or all of application inspected Highest overhead: slow & low volume Multi-Homed Firewall: Separate Zones Internet Screening Device Screened Host With Proxy Interface Router IDS Firewall Demilitarized Zone External DNS IDS Web Server E-Commerce VPN Server Protected Internal Network Zone IDS Database/File Servers The router serves as a screen for the Firewall, preventing Denial of Service attacks to the Firewall. Writing Rules Policies Corrections Network Filter Capabilities Write Rules Audit Failures Protected Network Services and Servers Workbook Service Sensitivity Roles Server Grades Confidential For Graduates: Transcripts For Current Students: Advising, Students, Faculty StudentScholastic Billing Confidential, For Current Students: Registration, Accounting, Advising Payment: Students StudentBilling Web Pages Public Students, Employees, Public Web services Path of Logical Access How would access control be improved? Border Router/ Firewall The Internet De-Militarized Zone WLAN Private Network Router/Firewall Protecting the Network Border Router: Packet Filter The Internet De-Militarized Zone Bastion Hosts WLAN Private Network Proxy server firewall Serviced Applications Workbook Applicatio Sources of ns Entry Grades University Graduates Registration Servers Graduate Scholastic Required Controls (e.g., Encryption) Confidentiality, Integrity, Authentication Grades – Current Students United States Student Scholastic Confidentiality, Integrity, Authentication Billing Payment: International Reports: Univ. Student Scholastic Confidentiality, Authentication, Integrity, Non-repudiation Web Pages International DMZ: PublicFace Network Diagram Workbook Internet Router Demilitarized Zone External DNS Email Firewall Public Web Server E-Commerce Zone 3:Student Data Zone 1: Student Labs & Files Student Scholastic Zone 2: Faculty Labs & Files Student Records Student Billing Student Billing Student History Transcripts Intrusion Detection Systems (IDS) Intrusion Prevention Systems (IPS) Router IDS Firewall Network IDS=NIDS Examines packets for attacks Can find worms, viruses, orgdefined attacks Warns administrator of attack IPS=Packets are routed through IPS Host IDS=HIDS Examines actions or resources for attacks Recognize unusual or inappropriate behavior E.g., Detect modification or deletion of special files NastyVirus IDS Intelligence Systems NIDS: ALARM!!! Attacks: NastyVirus Normal BlasterWorm Signature-Based: Specific patterns are recognized as attacks 90 80 70 60 Sales Personnel Factory 50 40 30 20 10 0 Mon. Tues. Wed. Thurs. Statistical-Based: The expected behavior of the system is understood If variations occur, they may be attacks (or maybe not) Neural Networks: Statistical-Based with self-learning (or artificial intelligence) Recognizes patterns Honeypot & Honeynet Honeypot: A system with a special software application which appears easy to break into Honeynet: A network which appears easy to break into Purpose: Catch attackers All traffic going to honeypot/net is suspicious If successfully penetrated, can launch further attacks Must be carefully monitored Firewall Honey Pot External DNS IDS Web Server E-Commerce VPN Server Bill Data Privacy Confidentiality: Unauthorized parties cannot access information (->Secret Key Encryption Authenticity: Ensuring that the actual sender is the claimed sender. (->Public Key Encryption) Integrity: Ensuring that the message was not modified in transmission. (->Hashing) Nonrepudiation: Ensuring that sender cannot deny sending a message at a later time. (->Digital Signature) Confidentiality Joe Bill Authenticity Joe (Actually Bill) Ann Ann Integrity Joe Non-Repudiation Joe Bill Ann Ann Encryption – Secret Key Examples: DES, AES plaintext Encrypt Ksecret ciphertext Decrypt Ksecret P = D(Ksecret, E(Ksecret,P)) NIST Recommended: 3DES w. CBC AES 128 Bit plaintext Public Key Encryption Examples: RSA, ECC, Quantum P = D(kPRIV, E(kPUB,P)) Joe Joe Encrypt Kpublic Encryption (e.g., RCS) Message, private key Decrypt Kprivate Authentication, Non-repudiation Decrypt Kpublic Digital Signature Encrypt Kprivate P = D(kPUB, E(kPRIV,P)) Key owner Key owner NIST Recommended: RSA 1024 bit 2011: RSA 2048 bit Remote Access Security Firewall The Internet VPN Concentrator Virtual Private Network (VPN) often implemented with IPSec Can authenticate and encrypt data through Internet (red line) Easy to use and inexpensive Difficult to troubleshoot, less reliable than dedicated lines Susceptible to malicious software and unauthorized actions Often router or firewall is the VPN endpoint Secure Hash Functions Examples: SHA1, SHA2, MD2, MD4, MD5 Ensures the message was not modified during transmission Message Message H Message H H Compare H H K Message Authentication Code Message H H K H Message H Message H E H K D One Way Hash K H Compare H NIST Recommended: SHA-1, SHA-2 2011: SHA-2 Digital Signature Electronic Signature Uses public key algorithm Verifies integrity of data Verifies identity of sender: nonrepudiation Message Encrypted K(Sender’s Private) Msg Digest Public Key Infrastructure (PKI) 7. Tom confirms Sue’s DS 5. Tom requests Sue’s DC 6. CA sends Sue’s DC Tom 4. Sue sends Tom message signed with Digital Signature Digital Certificate User: Sue Public Key: 2456 Certificate Authority (CA) 3. Send approved Digital Certificates 1. Sue registers with CA through RA Sue Register(Owner, Public Key) 2. Registration Authority (RA) verifies owners Network Access Server 1. Dial up and authenticate 2. Call back 3. Connect RADIUS or TACACS NAS: Network Access Server Handles user authentication, access control and accounting Calls back to pre-stored number based on user ID Prone to hackers, DOS, misconfigured or insecure devices RADIUS: Remote Access Dial-in User Service TACACS: Terminal Access Control Access Web Page Security SQL Filtering: Filtering of web input for SQL Injection Encryption/Authentication: Ensuring Confidentiality, Integrity, Authenticity, Nonrepudiation Web Protocol Protection: Protection of State Vulnerability Assessment Scan servers, work stations, and control devices for vulnerabilities Open services, patching, configuration weaknesses Testing controls for effectiveness Adherence to policy & standards Penetration testing Serviced Applications Workbook Applicatio Sources of ns Entry Grades – United States Current Students Required Controls (e.g., Encryption) Student Confidentiality: Encryption Scholastic Integrity: Hashing, IDS Authentication: VPN/IPsec, secure passwords Billing Student Confidentiality: Encryption, Scholastic HTTPs Authentication: VPN/IPsec Integrity, Hashing, IDS Non-repudiation: Digital Signature Payment: International Reports: Univ. Servers Summary of Network Controls Network Security Techniques Encryption: Public and Private key, Wireless WPA2 Virtual Private Network (VPN): Secure communications tunnel Secure Hashing Digital Signature Bastion Host Configuration Certificate Authority: PKI Network Protection Devices Firewall: Packet, Stateful, Circuit, Application-Level Proxy server Demilitarized Zone (DMZ) Intrusion Detection System Intrusion Prevention System Network access server (RADIUS or TACACS) Honeypot, honeynet Secure Protocols SSL: Secure web SSH: Secure telnet/rlogin or file transfer S/MIME: Secure email Secure Information Mgmt: Log mgmt Question 1. 2. 3. 4. The filter with the most extensive filtering capability is the Packet filter Application-level firewall Circuit-level firewall State Inspection Question 1. 2. 3. 4. The technique which implements nonrepudiation is: Hash Secret Key Encryption Digital Signature IDS Question 1. 2. 3. 4. Anti-virus software typically implements which type of defensive software: Neural Network Statistical-based Signature-based Packet filter Question 1. 2. 3. 4. MD5 is an example of what type of software: Public Key Encryption Secret Key Encryption Message Authentication PKI