Chapter 6/Cisco 3
advertisement

Year 2 - Chapter 6/Cisco 3 - Module 6
ACLs
By
Carl Marandola CCAI-CCNA
Objectives
• Define and describe the purpose and operation of ACLs
• Explain the processes involved in testing packets with
ACLs
• Describe ACL configuration commands, global statements,
and interface commands
• Define and explain the function and operation of wildcard
masks bits and the wildcards any and host
• Describe standard ACLs
• Describe extended ACLs
• Describe named ACLs
• Monitor and verify selected ACL operations on the router
ACL Overview
•
•
•
•
Reasons to Create ACLs
Creating an ACL in the Correct Order
Using ACLs
How ACLs Work
What Are ACLs?
• Lists of instructions you apply to a router's interface.
– Tell the router what kinds of packets to accept and what kinds to
deny based on criteria defined in the ACL.
• Cisco ACLs support all routed network protocols (IP, IPX).
– Each protocol must have its own ACLs.
Reasons to Create ACLs
•
•
•
•
Limit network traffic and increase network performance
Provide traffic flow control
Provide a basic level of security for network access
Decide which types of traffic are forwarded or blocked at the
router interfaces
ACL Configuration Tasks
• Grouping (Applying) ACLs to Interfaces
• Assigning a Unique Number to Each ACL
• Using Wildcard Mask Bits
Basic ACL Creation Steps
Router#config t
Router(config)#access-list 50 permit 192.168.1.10
Router(config)#access-list 50 deny 192.168.1.0 0.0.0.255
Router(config)#access-list 50 permit any
Router(config)#interface Ethernet0
Router(config-if)#ip address 192.168.5.1 255.255.255.0
Router(config-if)#ip access-group 50 out
(applying the ACL)
•
Create a List of Permit or Deny Statements.
– Created in global configuration mode.
– Created in sequential order.
• Each new item is added to the bottom of the ACL.
– ACLs are processed in sequential order (top down).
•
Apply the ACL to a Task.
– Although ACLs can be used in many ways, the CCNA exam
covers only filtering interfaces.
Applying ACLs to Interfaces
Router#config t
Router(config)#access-list 50 permit 192.168.1.10
Router(config)#access-list 50 deny 192.168.1.0 0.0.0.255
Router(config)#access-list 50 permit any
Router(config)#interface Ethernet0
Router(config-if)#ip address 192.168.5.1 255.255.255.0
Router(config-if)#ip access-group 50 out
•
•
Keyword ip access-group applies ACL to an interface.
In the above example, the ACL is applied “outbound” meaning:
–
Only outbound traffic is checked by the ACL.
• Out or in is always viewed from the center of the router.
•
•
The default direction is out (that is, if no designation is mad).
Each interface can have an in and out ACL for each protocol
configured on the interface.
ACLs Command-Line Basics
Router#config t
Router(config)#access-list 50 permit 192.168.1.10
Router(config)#access-list 50 deny 192.168.1.0 0.0.0.255
Router(config)#access-list 50 permit any
Router(config)#interface Ethernet0
Router(config-if)#ip address 192.168.5.1 255.255.255.0
Router(config-if)#ip access-group 50 out
•
•
•
Keyword access-list required; identifies an ACL item.
ACL number (50 above) is the identifier for this particular list.
Things to know about ACL numbers:
–
–
–
–
–
•
•
Standard IP ACLs use numbers 1–99.
Extended IP ACLs use numbers 100–199.
Each item in the list will have the same number.
No two ACLs on a router can use the same number.
ACLs and ACL numbers are router-specific.
Keywords permit / deny allow or prevent passage, respectively.
Balance of the ACL is the criteria (rules for filtering).
How an Outbound ACL Works
Flowchart of the ACL Test
Matching Process
ACL lines are processed
sequentially (top-down).
When a criteria is matched, the
packet is permitted or denied
and no other testing occurs on
that packet.
If no ACL test matches, the
packet it is denied by default.
Wildcard Mask Bits #1
Router#config t
Router(config)#access-list 50 deny 192.168.1.0 0.0.0.255
Router(config)#access-list 50 permit any
Router(config)#interface Ethernet0
Router(config-if)#ip address 192.168.5.1 255.255.255.0
Router(config-if)#ip access-group 50 out
Although maybe not a perfect explanation, it is often easiest to see
wildcard masks as being just the opposite of subnet masks. The subnet
mask 255.255.255.0 identifies the network, the wildcard mask 0.0.0.255
identifies the hosts.
A subnet mask is a 32-bit value made up of contiguous 1s and then 0s.
A wildcard is a 32-bit value made up of contiguous 0s indicating a “must
match” and then 1s.
In the above example, the 0s mean the first 3 octets must match exactly.
The 255 means any value from 0 to 255 can be here.
Both actually occur in binary and can often be understood only in binary.
Wildcard Mask Bits #2
Wildcard Mask Bits #3
It is possible to identify a
range of subnets.
172.30.16.0 0.0.15.255
The 255 means the last
octet can be 0 to 255.
3rd Octet
= 16
This means any value
that can be made using 4
bits (0 to 15), so the
range is 16+0 to 16+15.
Keywords Any and Host
• Any
– Same as 0.0.0.0 255.255.255.255
– Example: access-list 12 permit any
• Host
–
–
–
–
Same as IP-address 0.0.0.0
Example: 192.168.1.10 0.0.0.0
Example: access-list 12 deny host 192.168.1.10
Can be omitted in standard IP ACLs
Router(config)#access-list 75 deny host 192.168.1.10
Router(config)#access-list 75 deny 192.168.17.123
Router(config)#access-list 75 permit any
Implicit Deny Any Statement
• By default, an interface will allow all traffic
in both directions.
• Once an ACL is applied, the default state
switches to deny all traffic in the direction
of the ACL (in or out).
– Many ACLs end with access-list # permit any to
avoid the implied deny any.
Router(config)#access-list 75 deny host 192.168.1.10
Router(config)#access-list 75 deny 192.168.17.123
Router(config)#access-list 75 permit any
Permit and Deny Statements
• Except in special circumstances, every ACL must
have at least one permit statement.
– An ACL made up of only deny statements combined
with the implicit deny any statement will block all traffic
in the direction of the ACL.
• No similar requirement for deny statements.
Standard ACLs
• Criteria is limited to source network address
only.
– Can identify a host, subnet, or network
– Denies or permits all traffic from the target address for
the protocol
– Necessary to place close to the destination
Standard ACLs
Example #1
This one-line ACL
will allow into each
LAN only packets
from the other
LAN, not from the
cloud.
The implicit deny
any blocks any
other traffic.
Standard ACLs
Example #2
This two-line ACL will
deny traffic from a
single host A from
getting to the X network.
A
Network X
The second line could
and should have been
access-list 1 permit any.
The implicit deny any is
negated by the previous
line, which allowed
every thing through.
Standard ACLs
Example #3
This two-line ACL will
deny traffic from the
entire 172.16.4.0 network.
The second line allows
any traffic from the cloud.
The implicit deny any is
negated by the permit any
line, which allowed
everything else through.
Extended ACLs Can Filter on
One or Many Data Fields
Extended ACLs – Creating an
Extended Access List
As with standard lists, the access-list command is used to create each condition
of the list – using one condition per line. The syntax for each line in the list is:
access-list access-list-number {permit | deny} {protocol | protocol
keyword} {source | any} [source-wildcard] [source port] {destination |
any} [destination-wildcard] [destination port] [options]
Example:
Lab-X#config t
Lab-X(config)#Access-list 101 deny tcp 192.168.1.0 0.0.0.255 any eq www
Lab-X(config)#Access-list 101 deny tcp any eq ftp 192.168.1.25
Lab-X(config)#Access-list 101 permit ip any any
Lab-X(config)#interface Fastethernet 0/0
Lab-X(config-if)#ip access-group 101 out
The access list-number range for IP extended access lists is 100 to 199.
The protocol entry defines the protocol to be filtered, such as IP, TCP, UDP, or
ICMP for example. Because IP headers transport TCP, UDP, and ICMP, it is
important to specify the protocol or you could end up inadvertently filtering
more than you want to.
Extended ACLs – TCP
Relational Operators
The access list TCP protocol option supports both source and
destination ports. You can access each by using either the port
number or a mnemonic or acronym. Keyword relational operators
such as those shown in the following code output precede these:
Lab-X(config)#access-list 101 deny tcp any ?
A.B.C.D Destination address.
any
Any destination host.
eq
Match only packets on a given port number.
gt
Match only packets with a greater port number.
host
A single destination host.
lt
Match only packets with a lower port number.
neq
Match only packets not on a given port number.
range
Match only packets in the range of port numbers.
Extended ACLs – Protocol
Identifiers
After choosing a relational operator, specify a mnemonic (or acronym) or
port number, such as the following code output for the TCP port names:
Lab-X(config)#access-list 101 deny tcp any eq ?
<0-65535>
Port number
bgp
Border Gateway Protocol (179)
chargen
Character generator (19)
cmd
Remote commands (rcmd, 514)
daytime
Daytime (13)
discard
Discard (9)
domain
Domain Name Service (53)
echo
Echo (7)
exec
Exec (rsh, 512)
finger
Finger (79)
ftp
File Transfer Protocol (21)
--Some output omitted—
uucp
Unix-to-Unix Copy Program (540)
whois
Nicname (43)
www
World Wide Web (HTTP, 80)
UDP and TCP Port Numbers
Extended ACLs – TCP
Example
The first statement could have used the mnemonic “telnet” in place of 23
with exactly the same result. The one advantage to using the mnemonic
is that it is more intuitive to anyone having to support the device.
Lab-X#config t
Lab-X(config)#access-list 101 deny tcp 192.168.5.0 0.0.0.255 any eq 23
Lab-X(config)#access-list 101 permit ip any any
Lab-X(config)#interface fastethernet 0/1
Lab-X(config-if)#ip access-group 101 in
If you want to block network 192.168.5.0 from being able to surf the Web
while still allowing other services such as FTP, use this code:
Lab-X#config t
Lab-X(config)#access-list 106 deny tcp 192.168.5.0 0.0.0.255 any eq www
Lab-X(config)#access-list 106 permit ip any any
Lab-X(config)#interface ethernet 0
Lab-X(config-if)#ip access-group 106 in
Extended ACLs – Blocking RIP
Routing Updates
One example of using ACLs with UDP packets would be to block RIP
routing updates from passing out a particular interface using an ACL
such as the following:
Lab-X#config t
Lab-X(config)#access-list 150 deny udp any any eq rip
Lab-X(config)#access-list 150 permit ip any any
Lab-X(config)#int e0
Lab-X(config-if)#ip access-group 150 out
Important Concept for
Extended ACLs
Both ACLs below implicitly deny all other IP traffic, not just all other TCP
traffic. A common mistake many people make is assuming that because
they specified only TCP in the main statement(s), they need only to refer
to TCP in the final permit any statement (102 below).
The unplanned result would be that all ICMP and UDP traffic matching
the address/protocol criteria would be blocked (102 below).
ACL 101’s permit IP any any statement will allow all other traffic.
Lab-X#config t
Lab-X(config)#Access-list 101 deny tcp any 192.168.1.25 eq ftp
Lab-X(config)#Access-list 101 permit IP any any
Lab-X(config)#Access-list 102 deny tcp 10.0.0.0 0.255.255.255
192.168.1.1 eq ftp
Lab-X(config)#Access-list 102 permit TCP any any
Lab-X(config)#interface Fastethernet 0/0
Lab-X(config-if)#ip access-group 101 out
Lab-X(config-if)#ip access-group 102 in
Extended Access List
Processing
Named ACLs – Basics
The Cisco IOS release supports using named access lists rather than
the traditional number designations. This ability to name a list makes
them easier to recognize and can make them easier to debug.
Another advantage is that it is possible to delete individual entries
from a specific ACL instead of erasing the entire list.
A couple things to consider when implementing named ACLs:
1. Names, like numbers, must be unique on each router.
2. Named ACLs do not work with IOS releases prior to 11.2.
The first step is to create the ACL using the following syntax:
Router(config)#ip access-list {standard | extended} name
Example:
Lab-X(config)#ip access-list extended BlockInternet
Named ACLs – Example
Lab-X#conf t
Lab-X(config)#ip access-list ?
(to see the options)
extended
Extended Access List
log-update Control access list log updates
logging
Control access list logging
standard
Standard Access List
Lab-X(config)#ip access-list standard ProtectLAN
Lab-X(config-std-nacl)#deny 192.168.20.0 0.0.0.255
Lab-X(config-std-nacl)#deny 192.168.30.0 0.0.0.255
Lab-X(config-std-nacl)#permit any
Lab-X(config-std-nacl)#exit
Lab-X(config)#ip access-list extended FilterOutside
Lab-X(config-ext-nacl)#permit tcp any 192.168.5.0 0.0.0.255 established
Lab-X(config-ext-nacl)#deny icmp any 192.168.5.0 0.0.0.255
Lab-X(config-ext-nacl)#permit ip any any
Lab-X(config-ext-nacl)#^Z
Lab-X#
Named ACLs are applied to interfaces the same as other ACLs.
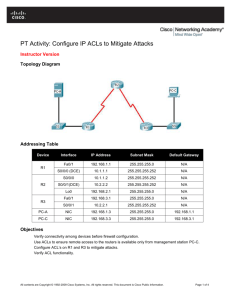
ACL Placement
Standard ACLs must be placed close to the destination.
Extended ACLs should be placed close to the source.
ACLs and Firewall Routers
Border routers are charged with providing network security from
potential attacks from outside the network. The figure shows the
simplest situation where the border router becomes the clear
demarcation between the network and the rest of the world.
Typically intruders come from the global Internet and the
thousands of networks connected to it.
ACLs and Firewall Routers
Another type of firewall implementation uses two or more routers
to provide the security. The border router, A, is ultimately
responsible for securing the LAN(s).
The firewall router, F, is responsible for protecting both the shared
servers and the internal networks from attack from outside. In an
optimal solution, this would be a specialty device like Cisco’s PIX
box, which combines hardware and software to secure the
connection. Whether a specialty device or a router with the firewall
feature set, ACLs will be a part of the solution.
Verifying ACLs
Lab-X#show ip interface
Ethernet0 is up, line protocol is up
Internet address is 192.168.5.1/24
Broadcast address is 255.255.255.255
Address determined by non-volatile memory
MTU is 1500 bytes
Helper address is not set
Directed broadcast forwarding is disabled
Multicast reserved groups joined: 224.0.0.9
Outgoing access list is 50
Inbound access list is 70
Proxy ARP is enabled
The show ip interface command will tell whether an inbound or
outbound access list has been applied to an interface. Rows 9 and 10
above contain the information. The rest of the lines do not pertain to
ACLs, so they have been omitted.
The show access-lists
Command
Lab-X#show access-lists
Standard IP access list 50
deny
192.168.1.10 log
permit any
Standard IP access list 75
deny
192.168.17.123
deny
192.168.1.10
permit any
Lab-X#
The show access-lists command will display all access lists on the
router but does not show whether or where they are applied.
Another command, show ip access-lists, would include only IP access
lists. Both commands enable you to specify an ACL number or name
after the command to display just that ACL.
The show run Command
Lab-X#show run
hostname Lab-X
!
! (output abbreviated)
!
access-list 50 deny
192.168.1.10 log
access-list 50 permit any
access-list 75 deny
192.168.17.123
access-list 75 deny
192.168.1.10
access-list 75 permit any
!
One way to see your access lists and how they are applied is to use the
show run command to see the active configuration. The above lines
show the output of a show run command with some of the unrelated
lines removed.
Verifying Named ACLs
Lab-X#show run
!
(output edited and omitted)
ip access-list standard ProtectLAN
deny
192.168.20.0 0.0.0.255
deny
192.168.30.0 0.0.0.255
permit any
!
ip access-list extended FilterOutside
permit tcp any 192.168.5.0 0.0.0.255 established
deny
icmp any 192.168.5.0 0.0.0.255
permit ip any any
!
Lab-X#show access-list
Standard IP access list ProtectLAN
deny
192.168.20.0, wildcard bits 0.0.0.255
deny
192.168.30.0, wildcard bits 0.0.0.255
permit any
Extended IP access list FilterOutside
permit tcp any 192.168.5.0 0.0.0.255 established
deny icmp any 192.168.5.0 0.0.0.255
permit ip any any
Lab-X#
ACL Labs and exercises
•
•
•
•
•
•
Complete the e-labs below: (6/09 and 6/11)
6.3.2
6.3.3
6.3.6.1
6.3.6.2 6.4.2.1
6.4.2.2
6.4.2.3 6.5.1
6.8.1.1
6.8.1.2
Regular lab—Handouts