Overview of Anonymous Communications
advertisement

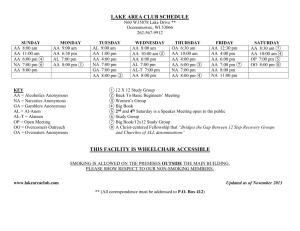
Anonymous Communications Adam C. Champion and Dong Xuan CSE 4471: Information Security Autumn 2012 Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications • Final Remarks Overview: Anonymous Communications • Network communications among parties concealing parties’ identity, existence of communications – Applications: whistleblowing, privacy-preserving free expression, voting in elections, etc. – Systems: Tor [1], I2P [2], Anonymizer [3], etc. – Practice: Users’ communications cloaked by partitioning into application-layer chunks, relayed among users in system [4] Case Study: How Tor Works Source: [1] Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications – Motivation – Flow marking traceback technique – Prototyping – Implementation and Evaluation – Related Work • Final Remarks Motivation: Invisible Traceback (1) • Traceback in the real world Animal traceback Mail traceback Family traceback [5] Motivation: Invisible Traceback (2) • Internet is breeding ground for many crimes: Credit Card Fraud Sharing © Files (without permission) Cyber-Terrorism Malware Distribution • Criminal enterprises like anonymous communications… • For such cases, law enforcement investigators need to determine parties responsible for crimes Motivation: Invisible Traceback (3) • Traceback aims to determine “whodunit”: – Origin of a packet/message – Unauthorized distributors, downloaders of © files – Evil cybercriminals communicating with each other Investigator Evil Evil Motivation: Invisible Traceback (4) • Critical point: investigator’s traceback activity needs to be invisible to suspects (e.g., illegal file sharers, cybercriminals) • Without invisibility: – Suspects would cease criminal activity, do it elsewhere, develop countermeasures to fool investigators, etc. – Investigator would have no evidence of wrongdoing • Traceback helps hold cybercriminals responsible for their actions Challenges to Invisible Traceback (1) • The nature of the Internet: – Large scale, loose control – Destination oriented routing and forwarding ⟹ easy to spoof source IP addresses – Intermediate nodes record very little information Challenges to Invisible Traceback (2) • Availability of anonymous communication systems Receiver Sender B to R B S to A A Human Spy Network A to B Anonymous Communication Our Focus Anonymous Channel Sender Receiver • Suppose a sender sends traffic through an encrypted anonymous channel. How can the investigator trace and confirm the receiver’s identity? • Papers [4] and [6] (S&P 2007, ToN 2012) Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications – Motivation – Flow marking traceback technique – Prototyping – Implementation and Evaluation – Related Work • Final Remarks An Intuitive Solution • Packet marking: mark certain packets Sender Receiver Anonymous Network • However, packets are encrypted in anonymous communication systems – Carelessly marked packets fail decryption ⟹ visible to the attacker! Our Solution • Flow marking – Change traffic flow rates – Traffic rate changes represent a “mark,” i.e., special secret code Sender Anonymous Network Anonymous Channel Interferer Investigator Receiver Sniffer Investigator knows that Sender communicates with Receiver! Key Differences Between Flow and Packet Marking • Packet marking – Mark embedded in packets – Packet content is changed – It is very difficult, if impossible, to hide such changes when packets are encrypted • Flow marking – Mark is embedded in flow rate changes – No packet content is changed – It is feasible to hide flow rate changes in the Internet, typically with dynamic traffic Questions About Flow Marking • A “detail” question: – How is a mark embedded into flow rate changes? • Two “big picture” questions: – How do we make the traffic rate changes invisible to cybercriminals? – How do we make the traffic changes robust to burst traffic interference in the Internet? Embedding Mark Into Flow Rate Changes Flow Mark 1 1 1 -1 1 -1 -1 • Mark decides flow rate changes – Key to flow rate changes’ invisibility and robustness: choose an appropriate mark – Direct Sequence Spread Spectrum (DSSS) Basic Direct Sequence Spread Spectrum (DSSS) • A pseudo-noise (PN) code is used for spreading a signal and despreading a spread signal Interferer Original Signal dt Sniffer rb tb ct PN Code Spreading noisy channel dr cr PN Code Despreading Recovered Signal Example: Spreading and Despreading • Signal • PN code (i.e. DSSS code) • – One symbol is “represented” by 7 chips – PN code is random; not visible in time or frequency domains • tb is the mark! • Despreading is the reverse process of spreading +1 dt t –1 tb Tc (chip) t +1 ct t –1 Mark NcTc Invisibility of Flow Marking • Marks show a white noise-like pattern in both time, frequency domains • Mark amplitude can be very small • As suspects don’t know the code, it’s very hard for them to recognize marks Accuracy of Flow Marking Recognition • Spreading/despreading processes make the mark immune to burst interference introduced by Internet background traffic +1 dt t –1 tb Tc (chip) +1 ct –1 t Mark Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications – Motivation – Flow marking traceback technique – Prototyping – Implementation and Evaluation – Related Work • Final Remarks A Prototype System Sender Receiver Anonymous Network Flow Modulator Flow Demodulator Signal Modulator Signal Modulator Recovered Signal Interferer Sniffer Embedding Signal into Traffic at Interferer Signal 1. 2. Choose a random signal of length n: (1 -1) Signal modulator: obtain the spread signal Signal Modulator PN Code Flow Modulator 3. Flow modulator: modulate a target traffic flow by appropriate interference • Bit 1: without interference • Bit –1: with interference Internet spread signal + noise Recovering Signal at Sniffer 1. Flow demodulator: • Sniff target traffic • Sample target traffic to derive traffic rate time series • Use high-pass filter to remove direct component by Fast Fourier Transform (FFT) spread signal + noise Flow Demodulator High-pass Filter PN Code 2. Signal demodulator: • Despreading by the PN code • Use low-pass filter to remove highfrequency noise 3. Decision rule: • Recovered signal == Original signal? Low-pass Filter Signal Demodulator Decision Rule Analytical Results • 1 bit signal detection rate: probability that we recognize 1 signal bit if we know when the signal appears where erfc(⋅) is complementary error function, A Signal to Noise Ratio (SNR) Nc is PN code length • n-bit signal detection rate • SNR influences accuracy as well as invisibility Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications – Motivation – Flow marking traceback technique – Prototyping – Implementation and Evaluation – Related Work • Final Remarks Real World Experimental Setup • The flow modulator at the interferer uses denial of service attack in wired networks Evaluation Setup Sender Receiver Traceback Invisibility • Overlapping traffic rate curves for traffic without marks in time and frequency domains Traceback Accuracy Transformation into a Real-World Tool • Remaining issues – Not totally invisible – Not accurate to low rate traffic – Robustness • Applied to different scenarios – One-to-one ⟹ group • Orthogonal codes ⟹ parallel flow marking – Wireless/wired networks Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications – Motivation – Flow marking traceback technique – Prototyping – Implementation and Evaluation – Related Work • Final Remarks Related Work • IP packet marking based traceback (UC Berkeley, Purdue U.) [7, 8] – Each router on path adds its IP address to packet; victim reads path from packet – Con: requires extra space in packet; requires network infrastructure involvement • Packet inter-arrival time based traceback (NCSU, George Mason U.) [9, 10] – Adjusts packet inter-arrival time conveying information – Pro: fewer packets – Con: sensitive to interference; needs more controlled network segments • Correlation based traceback (UT Arlington, U. of Cambridge) [11, 12] – Correlates traffic at different locations (passively or actively) – Pro: passive, no target traffic interference (good secrecy) – Con: needs threshold to determine whether traffic at different locations is related Outline • Overview of Anonymous Communications • Invisible Traceback over Anonymous Communications • Final Remarks Final Remarks • Anonymous communication systems useful, but can be abused by cybercriminals • Invisible traceback: important, hard problem • We proposed novel traceback technique based on flow marking with spread spectrum • We prototyped a system based on this technique • Technique has strong potential for development as a real-world tool References (1) 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Tor Project, “Tor: Anonymity Online,” http://torproject.org/about/overview.html.en “I2P Anonymous Network,” http://www.i2p2.de/ Anonymizer, Inc., http://www.anonymizer.com Z. Ling, J. Luo, W. Yu, X. Fu, D. Xuan, and W. Jia, “A New Cell-Counting-Based Attack Against Tor,” ACM/IEEE Trans. on Networking (ToN), vol. 20, no. 4, Aug. 2012, pp. 1245– 1261. http://www.englishexercises.org/makeagame/viewgame.asp?id=453 W. Yu, X. Fu, S. Graham, D. Xuan, and W. Zhao, “DSSS-Based Flow Marking Technique for Invisible Traceback,” Proc. IEEE Symp. on Security and Privacy (S&P), 2007, pp. 18– 31. D. X. Song and A. Perrig, “Advanced and authenticated marking schemes for IP traceback”, in Proc. IEEE INFOCOM, 2001 K. Park and H. Lee, “On the Effectiveness of Probabilistic Packet Marking for IP Traceback under Denial of Service Attack”, in Proc. IEEE INFOCOM, 2001. X. Wang, S. Chen, and S. Jajodia, “Tracking anonymous peer-to-peer voip calls on the internet,” in Proc. ACM Conf. on Computer Communications Security (CCS), 2005. P. Peng, P. Ning, and D. S. Reeves, “On the secrecy of timing-based active watermarking trace-back techniques,” in Proc. IEEE Symp. on Security and Privacy (S&P), 2006. References (2) 11. 12. Y. Zhu, X. Fu, B. Graham, R. Bettati, and W. Zhao, “On flow correlation attacks and countermeasures in mix networks,” in Proc. Workshop on Privacy Enhancing Technologies (PET), 2004. B. N. Levine, M. Reiter, C. Wang, and M. Wright, “Timing analysis in low-latency mix systems,” in Proc. Int’l. Conf. on Financial Cryptography, 2004.
![[#MOO-6147] Character weight-height range rolls are too extreme](http://s3.studylib.net/store/data/007783478_2-b98e047926bddb86e885153b90e16bf1-300x300.png)