Internet Security
advertisement
COSC1078 Introduction to
Information Technology
Lecture 22
Internet Security
James Harland
james.harland@rmit.edu.au
Lecture 22: Internet Security
Intro to IT
Introduction to IT
1-4 Introduction, Images, Audio, Video
5-6 Computer Fundamentals
Assignment 1, WebLearn Test 1
7 Review
8 Operating Systems
WebLearn Test 2
9 Operating Systems
Assignment 2
10 Internet
11 Internet Security
12 Future of IT
Lecture 22: Internet Security
WebLearn Test 3
Assignment 3, Peer and Self Assessment
Intro to IT
Overview
Questions?
Assignment 3
Internet Security
Questions?
Lecture 22: Internet Security
Intro to IT
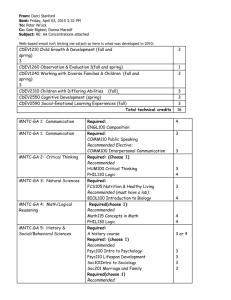
Intro to IT Schedule
Week
Lecture 1
Lecture 2
11
Internet Protocols
Internet Security
12
Future of IT
Review by request or
more Future of IT
13
Mock Exam
Wednesday 2nd June
Lecture 21: Internet Security
Intro to IT
Mock Exam
10.30-1.00 on Wednesday 2rd June in 12.08.02
Bring your own paper, pens, etc.
Calculators allowed
Answers will be available from me when you leave
Schedule:
10.30 Access to room
10.45 Reading time commences
11.00 Writing time commences
1.00 Exam concludes
Lecture 21: Internet Security
Intro to IT
Assignment 3
Review
(re-) answer What is IT? questions from Tutorial 1
Identify difficult parts of the course
Suggest new questions
Include favourites from Assignments 1 and 2
Reflect
Answer reflection questions from tutorials
Research
Write about a particular IT topic of your choice
(5-6 paragraphs)
Lecture 21: Internet Security
Intro to IT
Internet Security
pass
virus
proxy
word
patch
war
worm
Lecture 21: Internet Security
spam
fire
wall
key
logger
driving
phishing
Intro to IT
Trojan
horse
Security vs access
It is always a trade-off (a balance between two
competing forces)
More security means less access
More access means less security
Redundancy can be either fatal or vital
Nothing is perfect!
Freedom vs security
`Everything which is not forbidden is allowed’
-- Principle of English Law
`Everything which is not allowed is forbidden’
-- Common security principle
`Anything not mandatory is forbidden’
-- “military policy”
`Anything not forbidden is compulsory’ (??)
— T.H. White (The Once and Future King)
Passwords
Should be:
Long (8 characters or more)
Not obvious or from a dictionary
Contain capitals, numerals and nonalphanumeric characters (!&^*$@.,’[]{}? …)
Recorded securely somewhere
Transmitted in encrypted form only
Older programs such as FTP, Telnet transmit
this in plaintext …
Lecture 7: Internet Security
Intro to IT
Firewalls
Device which limits internet connections
Limit network uses to only approved ones
Prevent malicious software reporting information
Prevent outside attacks
May need to have ports opened to allow
applications to work
Only work on applications, not on content
Lecture 7: Internet Security
Intro to IT
Proxy servers
All internet traffic routed via proxy server
Acts as an internet gateway
Once proxy is secure, so is network
Can filter content
Can cache content
Often used with a firewall in a corporate
environment
Lecture 7: Internet Security
Intro to IT
Wardriving
Driving around to find a vulnerable wireless signal
Find a wireless connection that doesn’t require a
password (so add one to yours if you haven’t!)
Attack systems that use a default admin login name
and password (change yours!)
Snoop on transmissions which are not encrypted
(encrypt yours!)
Using a MAC address whitelist means only specified
devices can connect to your router
Lecture 7: Internet Security
Intro to IT
Viruses,Worms,Trojans
Virus: self-replicating program that attaches
itself to files and is spread when they are
transferred
Worm: self-replicating program that proactively spreads itself
Trojan horse: a program that appears
legitimate but is in fact malicious
Lecture 7: Internet Security
Intro to IT
Malware and Spyware
Malicious software:
Hidden mail server
Key logging (to capture passwords)
Enable machine takeover
Direct traffic to particular web sites
Analyse behaviour
Act as a proxy
…
Lecture 7: Internet Security
Intro to IT
Denial of service
Prevent network from working normally
Flood a server with ‘invalid’ inputs
Use a network of compromised machines to
generate an overwhelming number of requests
(Conficker?)
Such zombie machines can form a botnet,
which then attack a particular server
Lecture 7: Internet Security
Intro to IT
Tricking the user
Users are often the weakest link in security
Email attachments containing trojan horses
‘Phishing’
Malicious web pages
Malicious documents (macros in spreadsheets)
Account stealing (via key logging)
Scams (‘I have $10 million to import’, ‘You have
just won the lottery’, …)
Lecture 7: Internet Security
Intro to IT
Protecting your system
Keep up to date with patches (Windows
update, Software update)
Use a firewall
Use anti-virus software and keep it up to date
Use anti-spyware tools
Filter email for spam and suspicious messages
Be aware of ‘fake alerts’
Lecture 7: Internet Security
Intro to IT
Conclusion
Work on Assignment 3
Check your software defenses!
Lecture 21: Internet Security
Intro to IT