ECE 4112: Internetwork Security
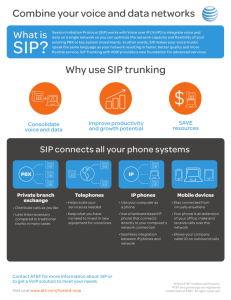
advertisement

ECE 4112: Internetwork Security Lab : SIP Security Group Number: _______________ Member Names: _________________________ _________________________ Date Assigned: Date Due: Last Edited: Authored by: Jennifer Stoll Please read the entire lab and any extra materials carefully before starting. Be sure to start early enough so that you will have time to complete the lab. Answer ALL questions and be sure you turn in ALL materials listed in the Turn-in Checklist ON or BEFORE the Date Due. Part 1: SIP Security Goal & Summary: The specific goal of this lab is to become more familiar with the SIP protocol and some of the security vulnerabilities related to this protocol. We will set-up a SIP server to mediate sessions between hosts. We will also set-up an attacker to compromise the SIP sessions being established to better understand some SIP security issues. In addition to attacks, we will become more familiar with countermeasures to make SIP sessions more secure. The general goal is to apply security theory to better understand SIP security. Background and Theory [1, 4]: SIP stands for Session Initiation Protocol, and it is an application-layer protocol used to set-up, maintain and tear-down interactive sessions between computers. It has been standardized by the IETF (Internet Engineering Task Force) as the multi-media signaling protocol. This protocol has been used inside networks for interconnecting and tracking in long distance calls. However, it is now being used to set up sessions for virtually any application where a session initiation is requirement, e.g., event subscription and notification, local & long distance telephony, instant messaging, rich media conferencing, push-to-talk, voice messaging, presence (showing status of users such as “busy”, “online”, or some other status) etc. In fact, the next generation of mobile phones will use SIP as the primary signaling technology. The popularity of SIP is partly due to the fact that it is the first protocol that enables multi-user sessions regardless of the media content of those sessions. 1 The advantage that the use of SIP has over current telephony is the extreme flexibility regardless of user location. For example, a user can attach a phone anywhere on the Internet and be immediately reachable. The phone used may have video, instant messaging or even file sharing because it is on an IP network. People will be able to find each other more easily on the Internet much in the same way that using a phone number helps us locate people. Current trends indicate that SIP will be the primary protocol for constructing P2P systems and resident telephony such that the current PBXs will be replaced to enable the rise of the next generation networks such as IMS (IP Multimedia Subsystem). In the development of SIP, the focus has bee on interoperability rather than security. Therefore, as a protocol, it is conveniently extensible, but vulnerable to not only general IP attacks but also to attacks unique to SIP. These attacks are unique to SIP because it is an evolving protocol that must incorporate more security measures to be built-in. The four potential threats we will look at include: Confidentiality: Is someone else listening on the user’s SIP call setup? Integrity: Is the SIP message received by the host the same one that was actually sent? Authentication: Can users steal the identity of other users? Privacy: What are the potential violations to privacy and why does protecting privacy matter? From the end-user’s perspective, any system or service should provide confidentiality, integrity, authentication and privacy. We will examine how SIP does or does not meet these security requirements. Some of these reasons are due the lack of maturity as a protocol; other reasons include design tradeoffs that were made which now have security implications. Prelab Questions: None. Lab Scenario: This lab requires two host machines and two virtual machines. The first host (Host1) which is a windows machine will have the RedHat7.2 (or Ubuntu) Virtual Machine. The second host (Host2) also a windows machine will have another linux virtual machine set up on it as well. This will be the SIP network that is used for the lab. There will be one SIP server running on the RedHat7.2 virtual machine (or Ubuntu) of Host1. 1: SIP Protocol, Functions & Features [4, 6] 1.1 SIP Protocol The following terms are for the major components in SIP [collier] : 2 Section User Agent (UA) – an endpoint in a SIP system, typically an IP phone, media gateway, or other media processing component such as voicemail. Identified using URIs (Universal Resource Identifiers) which incorporates a phone number or a name, e.g., owen@ece4112.edu. SIP Proxy – an application that enables UAs to locate and communicate with one another. The SIP Proxy we will use in this lab is Openser [open] which is an open source SIP server. SIP Registrar – an application which enables UAs to register themselves so they can receive calls SIP Redirect Server – an application that receives requests from a UA or proxy and returns a redirection response indicating where the request should be tried again. The SIP architecture is fairly simple and is usually composed of a SIP Proxy, Registrar and Redirect servers implemented on one system. Below is a description taken from RFC 3261 which describes the SIP protocol [RFC]: SIP makes use of elements called proxy servers to help route requests to the user's current location, authenticate and authorize users for services, implement provider call-routing policies, and provide features to users. SIP also provides a registration function that allows users to upload their current locations for use by proxy servers. SIP runs on top of several different transport protocols.” Interoperability has been the focus of the SIP protocol so that different components can be used to build the SIP network. Developed in the ‘90’s, this protocol relies heavily on existing protocols. As described in the RFC, this protocol works in conjunction with a number of other protocols and specialized servers to provide the capability of connecting multiple users over the Internet. Unfortunately, according to SecureLogix: “Interoperability can be an issue from a security point of view because all components must support the same security standard. If they don’t, you can use only a common capability (which may be weak).” For example, SIP is effectively designed as an IP protocol and its messages are text-based to enable easier and more flexible, e.g., similar to HTTP or SMTP, since such protocols can more easily work in conjunction with others. Once SIP establishes a session, other protocols are used to negotiate the type of media to be exchanged and how it is to be transported. Q1.1.1: The Universal Datagram Protocol (UDP) is one protocol which SIP uses to provide basic functionality. Use RFC 3261 or other information available on the web to list a few other transport protocols on which SIP runs on top of. Q1.1.2: What is a benefit of SIP being workable with many different protocols? Q1.1.3: Some implementations use UDP for transporting SIP messages. What security implication does this have and what protocol should be used instead? 3 Q1.1.4: Based on your answer to Q1.3 and the notes provided above, what would you say is a disadvantage of SIP’s interoperability? 1.2 SIP Functions and Features User location: A program uses SIP to register a user with a server by providing the user name and IP address of the computer being used. This allows other users to now locate that user on the Internet via this server and establish a session with the user. User availability: This function allows a user to control whether or not s/he can be contacted. This conveys the user’s presence status as “busy”, “away”, “online”, or as available only for particular types of information. If the user is available, then other users are allowed to invite that user to participate in a session. User capabilities: SIP can be used with different programs and different platforms; therefore the exact capabilities that the user has during a session largely depends on the features provided by the program and platform. It also depends on the capabilities of the other user being invited to the session, e.g. both ends must have a camera participate in a video-conference initiated using SIP. Session set-up & tear-down: This function sends request for session-initiation to the invited user and terminates the connection at the end of session. Session management: This function modifies the session while in use, e.g. if users decide to share other media during a session that was initially a voice call or if users decide to switch to video conferencing, etc. Q1.2.1: Based on the functions and features described above and using information available on the Internet, discuss what attacks could be executed. Section 2: SIP Server & Network Set-up In this portion of the lab we will set-up the SIP server and the two UAs who will be using the SIP Proxy to communicate. We will also set up an attacker who will attempt to compromise the session. 2.1 SIP Proxy set-up on the RedHat 7.2 VM on the Windows host 2.1.1 Server set-up instructions Openser is an opensource SIP server. Download openser-1.1.1-tls_src.tar.gz (SIP Server 1.1.1) from the NAS (http://www.openser.org/pub/openser/latest/src/openser-1.2.0tls_src.tar.gz) to your home/tools directory. This SIP server will be used to resolve 4 usernames to IP addresses so that requests from one user or UA to another can be properly directed. Each user agent must register with the server with a username and current IP address. We will be running a stateful server which remembers all the requests and responses it receives [[double-check this]]. Steps for set-up: Unpack the source files: tar xvzf openser-1.1.1-tls_src.tar.gz Build the executable: make Install the program: make install Run the server by entering openser 2.1.2 SIP signaling commands REGISTER – used by UA to register with a SIP server INVITE – used to invite another UA to communicate and establish a SIP session between two users ACK – used to accept a session and confirm reliable message exchanges OPTIONS – used to obtain information on the capabilities of another user SUSCRIBE – used to request updated presence information NOTIFY – used to send updated information on the UA’s current status CANCEL – used to cancel a pending request w/o terminating the session BYE – used to terminate the session 2.2 Softphone set-up on both of the two host machines X-Lite will be used as softphone. Throughout the document, the two Windows-based hosts will be referred to as Host-UA1, which runs SIP-VM, the virtual machine hosting the SIP server; and Windows Host-UA2, which runs Attack-VM, the virtual machine running the attacks. Steps for set-up on Windows Host 1: Download X-Lite_Win32_1006e_34025.exe from the NAS server (http://www.counterpath.com/index.php?menu=download_xlite&platform=win). Double-click the file to begin the setup process. Follow the instructions on the screen. Open X-Lite. The first time you run the program, it will prompt you to add a SIP account. Click the “Add...” button. Display Name: UserAgent1 User name: UA-1 Password: password Authorization user name: leave blank Domain: IP address of SIP-VM (see section 2.2.1 instructions on how to do this) Make sure “Register with domain and receive incoming calls” is checked. Select proxy under “Send outbound via:” and set the Address to the IP address SIPVM (see section 2.2.1 for instructions on how to do this) Click “OK”. Close the SIP Accounts window. 5 Repeat this process for the Windows Host 2, using UA-2 for the Display Name and UserAgent2 for the User name. Next, the default gateway for both hosts has to be cleared: Open Control Panel and open Network Connections. Double-click “Local Area Connection”. Click the “Properties” button. Under the “General” tab, select “Internet Protocol (TCP/IP)” from the list of items. Click “Properties”. Make sure “Use the following IP address:” is selected with the following values: IP address: 192.168.1.1 Subnet mask: 255.255.255.0 Default gateway should be cleared Repeat this process for the second host, using 192.168.1.4 for the IP address 2.2.1 Determining the IP address of the virtual machine In the Ubuntu Linux virtual machine (SIP-VM), enter the following command into a terminal: ifconfig. Find the eth0 entry and the inet addr field within that entry. This value is the IP address of the virtual machine. For example: # ifconfig eth0 Link encap:Ethernet HWaddr 00:AA:BB:CC:DD:EE inet addr:192.168.1.3 Bcast:192.168.1.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:2023 errors:0 dropped:2 overruns:0 frame:0 TX packets:1544 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:848679 (828.7 Kb) TX bytes:147853 (144.3 Kb) Interrupt:19 Base address:0x6000 Memory:b0107000-b0107fff In this example, the IP address is 192.168.1.3. 2.3 SIP Session Description 6 SIP Proxy Server Attacker Host 1 Host 2 The above diagram shows the SIP Proxy Server setting up a session between Host1 and Host2. Once the session is established, Host1 and Host2 communicate with each other without the help of the proxy. The attacker will execute attacks on both the server and the session between Host1 and Host2. Section 3: SIP Attacks [2, 3] 3.1 Common SIP attacks SIP security can be weak due to both vulnerabilities in the protocol and attacks. Most attacks are successful when vulnerabilities are exploited. Some exploits that can occur have to do with the fact that the SIP protocol either recommends weak defenses or the default is not to use any encryption. The majority of SIP attacks are similar to those executed on IP networks. Some well-know SIP vulnerabilities and attacks are as follows [porter]: Registration Hijacking: This is similar to a man-in-the-middle attacks where an attacker sniffs a REGISTER message from a legitimate user and modifies it with its own address at the contact address. The SIP server will receive this fake message and update the contact address belonging to the legitimate address with the fake address. All incoming calls for the legitimate contact will be redirected to the fake address. IP Spoofing/Call Fraud: This attack is executed by impersonating a legitimate user with a spoofed ID and sending an INVITE or REGISTER message. This attack is easy to do when SIP messages are sent in clear-text. An illegitimate REGISTER message from an attack can cause calls for the legitimate user to be redirected to a random IP address with no user at the other end. An attacker can use a legitimate IP address to make free calls. Weak Digest Authentication: The SIP protocol recommends using the MD5 digest algorithm for authentication. However, this particular hash algorithm is 7 considered to weak for use in systems requiring high security. Additionally, the SIP hash authentication algorithm has minimal header fields which can be forged. INVITE flooding: This is similar to a SYN flood attack in TCP connections where an attacker can execute a denial-of-service attack by flooding a SIP server with fake INVITE messages. BYE Denial-of-Service: When a SIP signaling packet is sent in clear text, it can be tampered with. For example, an attacker sniffing legitimate INVITE messages can forge a legitimate BYE message and send it to one of the UAs in a session and effectively tear-down the session prematurely. RTP Flooding: This attack is related to media transmission since most of these transmissions are based on RTP once the session has been created with SIP. An attacker forges RTP packets and bombards either UA in the session which results in degrading the quality of the session or a terminal reboot. SPIT (Spam over Internet Telephony): This attack sends unsolicited calls to legitimate users without their consent. At best, such an attack is an annoyance; at worst, it can flood the voicemail system, resulting in a form of denial-of-service. Q3.1.1: Identify two vulnerabilities of the SIP protocol and give an example of an attack that exploits each of the vulnerabilities. Q3.1.2: The negative effects of attacks on end-user systems are more than just on the system itself. Attacks can have potentially devastating consequences on the users themselves. Using three of the attacks listed above, give one example for each attack of the social disruption that could occur as a result of a successful attack. 3.2 Executing attacks on the SIP server 3.2.1 Setting up the attack environment For the attacks to build successfully, you will first need to install a special library. The instructions for obtaining the library and setting it up are below: Download hack_library.tar.gz from the NAS server (http://www.hackingvoip.com/tools/hack_library.tar.gz) and save it to the home/tools directory Unpack the source code: tar xvzf hack_library.tar.gz Change to the hack_library directory: cd hack_library Build the library: make The attack programs below will expect to find the files hack_library.h and hack_library.o in ../hack_library. 3.2.2 INVITE flood Attack The first attack on the SIP server will be an INVITE flood denial-of-service attack. This attack sends many SIP INVITE packets to the server, which the server then tries to process. The set-up instructions for Attack-VM are below: 8 Download inviteflood.tar.gz from the NAS server (http://www.hackingvoip.com/tools/inviteflood.tar.gz) and save it to the home/tools/ directory. Unpack the source files: tar xvzf inviteflood.tar.gz Switch to the inviteflood directory: cd inviteflood Build the executable: make Run the program: # inviteflood eth0 UA-1 192.168.1.3 192.168.1.3 <num_packets> where: eth0 is the network interface to use for the attack UA-1 is the username of the target user 192.168.1.3 is the IP address of the target domain (the SIP-VM's IP address) 192.168.1.3 is also the IP address of the flood target <num_packets> is the number of packets to flood the target with Replace any of these values with the ones you specified, if necessary To see the attack in action, open Ethereal on the victim host (Host-UA1) and select the network interface that the virtual machine is using. Begin capturing packets, and then mount the attack. Take a screenshot of the capture and turn in as Screenshot #1. An example is below: Screenshot of INVITE flood attack 9 3.2.3 Registration Hijack Attack The registration hijacking attack overwrites a specified user's registration information. It requires the attacker to know the target user's password. This attack is performed from the Attack-VM. The set-up instructions are: Download reghijacker.tar.gz from the NAS server (http://www.hackingvoip.com/tools/reghijacker.tar.gz) and save it to the home/tools directory. Unpack the source files: tar xvzf reghijacker.tar.gz Switch to the reghijacker directory: cd reghijacker Build the executable: make Run the program: # ./reghijacker eth0 192.168.1.3 192.168.1.3 hijack@localhost outfile.txt -u UA-1 -p password where: eth0 is the network interface to use for the attack UA-1 is the username of the target user 192.168.1.3 is the IP address of the target domain (the SIP-VM's IP address) 192.168.1.3 is the IP address of the domain's registrar (same as above) hijack@localhost is the replacement contact information for the target user outfile.txt is the file to write the results of the attack to UA-1 is the user name of the victim user agent password is the password of the victim user agent Replace any of these values with the ones you specified, if necessary To verify that the attack succeeded, in the SIP-VM, run the following command: # openserctl ul show and look for the new contact information (hijack@localhost in the above example). Additionally, if you try calling the victim using the softphone, you should get an error saying that the user does not exist. Take a screenshot of the output showing the hijacking and turn in as Screenshot #2. An example is below: 10 Sample screenshot showing output of the SIP server’s user list: UA1’s registration being high-jacked 3.3 Executing attacks on the UAs’ SIP clients 3.3.1 SIP phone disruption attack This attack repeatedly calls a user, even disrupting them after they answered a call. It uses the inviteflood program, so follow the instructions in section 2.3.1 for retrieving and building the program. Then, from the Attack-VM, run inviteflood as follows: # ./inviteflood eth0 UA-1 192.168.1.3 192.168.1.3 <num_calls> -s <interval> where: eth0 is the interface the virtual machine is using UA-1 is the user name of the user to attack 192.168.1.3 is the IP address of the SIP-VM 192.168.1.3 is the same as above <num_calls> is the number of calls to place <interval> is the number seconds to wait between calls To confirm that the attack is succeeding, check that the softphone on the target host (Host-UA1) is receiving multiple calls, even after it hangs up or answers. Take a screenshot of the UA-1s SIP phone showing the multiple calls and turn in as Screenshot #3. An example is below: 11 Screenshot showing UA-1’s phone receiving a flood of calls from UA-2 3.3.2 SIP phone BYE session tear-down attack This attack disrupts a call that is in session between two users. Instructions to run the attack are below: Download teardown.tar.gz from the NAS (http://www.hackingvoip.com/tools/teardown.tar.gz) server to the home/tools directory. Unpack the source files: tar xvzf teardown.tar.gz Change to the teardown directory: cd teardown Build the executable: make Run the program: # ./teardown eth0 UA-1 192.168.1.3 192.168.1.3 <Call-ID> <FromTag> <ToTag> where: eth0 is the network interface being used by the virtual machine doing the attack UA-1 is the user to attack 192.168.1.3 is the address SIP-VM 192.168.1.3 - same as above <Call-ID> is the ID number of the call <FromTag> is the tag appended to the “From” of the SIP header <ToTag> is the tag appended to the “To” of the SIP header 12 <Call-ID>, <FromTag>, and <ToTag> can be discovered by capturing the SIP packets transmitted during the initiation of the phone call using Ethereal. See the figure. Take screenshot of the capture showing the <Call-ID>, <FromTag>, and <ToTag> and turn in as Screenshot #4. An example is below: “To” tag “From” tag “Call-ID” Screenshot of Ethereal packet capture and where to find info needed to run attack Take a screenshot of the disrupted call on both ends and turn in as Screenshot #5 & 6. An example is below: UA-2 13 UA-1 Screenshot of UA-1 & UA-2 where call from UA-2 was disrupted with a BYE session tear-down attack. Section 4: SIP Countermeasures [2, 5, 6] 4.1 Countermeasures for attack on SIP server and session Despite the effectiveness of the attacks detailed in Section 3, there are several countermeasures that can be put in place to deter the attacks or reduce their damage. Use TCP/IP for SIP Connections: All four attacks could be prevented by using TCP rather than UDP as the transport protocol underlying the SIP session between a client and the proxy. TCP provides persistent connections, sequence numbers, and other features that add robustness to the connection, making it more difficult for to trick a phone into accepting packet floods (i.e., the INVITE flood attack in section 3.2.1 and the disruption attack in section 3.3.1); it also makes it more difficult to trick the SIP server into accepting unauthorized requests (i.e., the registration hijacking attack in section 3.2.2 and the teardown attack in section 3.3.2). Use TLS for TCP communication: Transport Layer Security (TLS) is a security protocol used in the transport layer. See section 4.2 for more information on how it is used to prevent SIP attacks. Session Border Controller: A session border controller (SBC) is a type of stateful firewall that is placed at a VoIP network's borders to manage the setting up and tearing down of phone calls. SBCs are stateful because they maintain information about each session they are monitoring. They can then use this information to reject packets that are invalid; this is useful in preventing the flooding and disruption attacks (sections 3.2.1 and 3.3.1, respectively) by leaving the proxy server and clients unaffected. 14 Message Authentication: By authenticating certain packets sent to it, the SIP server can prevent some attacks, like the session teardown attack presented in section 3.3.2. Message authentication is performed by verifying that the message is coming from a valid client using some shared secret between the participants. One way to do this is by having the sender produce a message digest of a special value called a “nonce” before processing any requests from it. A nonce is large, possibly random, nonrepeatable number. The server sends this value to the client, the client computes a cryptographic function on the nonce to produce a digest , and the client sends back the nonce, the digest, and the original request. The server then computes the same function on the nonce and ensures that what it received from the client matches; since the nonce is non-repeatable, the server is able authorize the sender and agrees to process the request. Message authentication can thus be used to prevent the session teardown attack because the SIP server can verify that the teardown request did indeed come from one of the participants in the VoIP call. Q4.1.1: Why is a TCP connection needed between every softphone and the SIP server if we want every phone to be more secure? Q4.1.2: Is it necessary for the challenge value used in message authentication to be non-repeatable? Does it need to be random? Why or why not? 4.2 Using an encrypted channel for SIP Transport Layer Security (TLS) is a protocol used to secure transport level communication. It provides confidentiality and authentication by encrypting data sent across a TCP connection (or any other transport layer protocol). Encryption of the data provides confidentiality by preventing eavesdropping on packets moving across the network; even if an attacker captures some packets, he will be unable to read them. This can prevent registration hijacking (section 3.2.2) and session teardown (section 3.3.2) attacks, which require the attacker to capture information about the server and the users. Similarly, TLS provides authentication because only an authorized agent can properly encrypt and decrypt the data. Thus, the INVITE flood (section 3.2.1) and SIP phone disruption (section 3.3.1) attacks can be deterred because the server can authorize the requests coming in before passing them along or trying to process the packets. 15 Source: http://www.networkworld.com/news/tech/2006/050106-secure-sip-voip.html[6] Use information available on the Internet and the diagram above to answer questions Q4.2.1, Q4.2.2, and Q4.2.3 below. Q4.2.1: Define confidentiality, integrity and authentication. Q4.2.2: Discuss what mechanism in the in the diagram above would protect confidentiality, integrity and authentication. Q4.2.3: What are some of the drawbacks of employing TLS in the communication between SIP clients and the proxy? References 1. Collier, Mark. “Basic Vulnerability Issues for SIP Security”. SecureLogix Corporation (2005). 2. Endler, David, Collier, Mark. Hacking Exposed: Voice Over IP Secrets & Solutions. The McGraw Hill Companies (2007). 16 3. www.openser.org 4. Porter, Thomas, et al. Practical VoIP Security. Syngress Publishing, Inc. Rockland, MA (2006). 5. RFC 3261. http://www.ietf.org/rfc/rfc3261.txt 6. Ward, Michael. “Secure SIP protects VoIP traffic”. NetworkWorld (2006). Available at: http://www.networkworld.com/news/tech/2006/050106-secure-sipvoip.html 17 ECE 4112: Internetwork Security Lab : SIP Security Group Number: _______________ Member Names: _________________________ _________________________ Q1.1.1: The Universal Datagram Protocol (UDP) is one protocol which SIP uses to provide basic functionality. Use RFC 3261 or other information available on the web to list a few other transport protocols on which SIP runs on top of. Q1.1.2: What is a benefit of SIP being workable with many different protocols? Q1.1.3: Some implementations use UDP for transporting SIP messages. What security implication does this have and what protocol should be used instead? Q1.1.4: Based on your answer to Q1.3 and the notes provided above, what would you say is a disadvantage of SIP’s interoperability? Q3.1.1: Identify two vulnerabilities of the SIP protocol and give an example of an attack that exploits each of the vulnerabilities. 18 Q3.1.2: The negative effects of attacks on end-user systems are more than just on the system itself. Attacks can have potentially devastating consequences on the users themselves. Using three of the attacks listed above, give one example for each attack of the social disruption that could occur as a result of a successful attack. Q3.2.2 Screenshot #1 Attach to answer sheet Q3.2.3 Screenshot #2 Attach to answer sheet Q3.3.1 Screenshot #3 Attach to answer sheet Q3.3.2 Screenshots #4, #5, #6 Attach to answer sheet Q4.1.1: Why is a TCP connection needed between every softphone and the SIP server if we want every phone to be more secure? Q4.1.2: Is it necessary for the challenge value used in message authentication to be non-repeatable? Does it need to be random? Why or why not? Q4.2.1: Define confidentiality, integrity and authentication. Q4.2.2: Discuss what mechanism in the in the diagram above would protect confidentiality, integrity and authentication. 19 Q4.2.3: What are some of the drawbacks of employing TLS in the communication between SIP clients and the proxy? Q5: How long did it take you to complete this lab? Was it an appropriate length lab? What corrections and/or improvements do you suggest for this lab? Please be very specific and if you add new material give the exact wording and instructions you would give to future students in the new lab handout. You may cross out and edit the text of the lab on previous pages to make minor corrections/suggestions. General suggestions like add tool xyz to do more capable scanning will not be awarded extras points even if the statement is totally true. Specific text that could be cut and pasted into this lab, completed exercises, and completed solutions may be awarded additional credit. Thus if tool xyz adds a capability or additional or better learning experience for future students here is what you need to do. You should add that tool to the lab by writing new detailed lab instructions on where to get the tool, how to install it, how to run it, what exactly to do with it in our lab, example outputs, etc. You must prove with what you turn in that you actually did the lab improvement yourself. Screen shots and output hardcopy are a good way to demonstrate that you actually completed your suggested enhancements. The lab addition section must start with the form “laboratory Additions Cover Sheet” which may be found on the class web page. 20 Appendix A: Answer Sheet Q1.1.1: The Universal Datagram Protocol (UDP) is one protocol which SIP uses to provide basic functionality. Use RFC 3261 or other information available on the web to list a few other transport protocols on which SIP runs on top of. Answer: any combination of SDP, TCP, RTP, RTCP, MGCP, RTSP Q1.1.2: What is a benefit of SIP being workable with many different protocols? Answer: It enables SIP to be highly flexible and extensible. Q1.1.3: Some implementations use UDP for transporting SIP messages. What security implication does this have and what protocol should be used instead? Answer: Because UDP does not use re-transmission or sequence numbers, it is easier for an attacker to spoof UDP packets. TCP would be more secure because Q1.1.4: Based on your answer to Q1.3 and the notes provided above, what would you say is a disadvantage of SIP’s interoperability? Answer: SIP is now also vulnerable to the same security issues with each of the different protocols it works with. Q3.1.1: Identify two vulnerabilities of the SIP protocol and give an example of an attack that exploits each of the vulnerabilities. Answer: #1: SIP sends messages in clear-text by default. The BYE DoS attack exploits this vulnerability. #2: SIP recommends using the MD5 hash for authenticating. Any flavor of impersonation attacks can exploit this vulnerability. Q3.1.2: The negative effects of attacks on end-user systems are more than just on the system itself. Attacks can have potentially devastating consequences on the users themselves. Using three of the attacks listed above, give one example for each attack of the social disruption that could occur as a result of a successful attack. Answer: Can be a variety of answers, e.g., any DoS attack such as the BYE attack can be extremely socially disruptive depending on the nature of the session being disrupted. If the session is time-sensitive, such as the conversation between a financial consultant and a client wishing to purchase shares of stock or between medical personnel collaborating on the emergency treatment of a heart patient. 21 Q3.2.2 Screenshot #1 Attach to answer sheet Q3.2.3 Screenshot #2 Attach to answer sheet Q3.3.1 Screenshot #3 Attach to answer sheet Q3.3.2 Screenshots #4, #5, #6 Attach to answer sheet Q4.1.1: Why is a TCP connection needed between every softphone and the SIP server if we want every phone to be more secure? Answer: Any phones that use UDP to talk to the server will still be vulnerable to attacks because they will not take advantage of the features of TCP that provide connection robustness, so the server will not be able to authenticate packets to or from that phone. Q4.1.2: Is it necessary for the challenge value used in message authentication to be non-repeatable? Does it need to be random? Why or why not? Answer: If an attacker were eavesdropping and recording all the values used as challenges and their respective digests, then if one of the challenges showed up again, the attacker could intercept it and send a valid digest, imitating the client Q4.2.1: Define confidentiality, integrity and authentication. Answer: Confidentiality is a security concept that implies safety from interception, viewing or copying, i.e. the information remains secret. Integrity is a concept that implies safety from illegally modifying data across endpoints. Authentication is a security concept that implies that the user of a system has provided the proper credentials to be allowed access. Q4.2.2: Discuss what mechanism in the in the diagram above would protect confidentiality, integrity and authentication. Answer: Using an encrypted channel such as TLS better ensures confidentiality, integrity and authentication for communication across each hop. Q4.2.3: What are some of the drawbacks of employing TLS in the communication between SIP clients and the proxy? Answer: Encrypting packets adds a speed overhead to the communication. Encryption key distribution might be complicated. 22 Appendix B: Set-up Instructions for the TA: The set-up required by the TA is to set up two windows machines with a linux (we used Ubuntu) virtual machine running on each. A cross-over cable should be used to connect the two windows machines. Both machines should have access to the NAS server. The student will be able to set-up the rest. Two Windows Machines Host 1 + VM Host 2 + VM 23