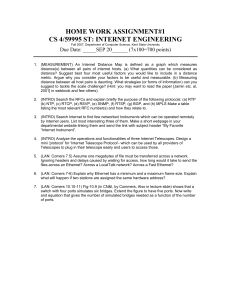
ES/EG 3567 The Ethernet Local Area Network
advertisement

Organisation
Data Communications 1
EG/ES 3567
lecturer:
Gorry Fairhurst
web site: http://www.erg.abdn.ac.uk/users/gorry/eg3567
Syllabus on web:
http://www.erg.abdn.ac.uk/users/gorry/eg3567
24 Lectures
- do take NOTES in lectures !!!
Course material on web
Tutorials (6 at end of each section)
Practical Exercises on web
Example Classes (4 during course, 2 at end)
Assessment:
Practical (6 afternoons) (10%+10%)
1 Three hour exam (80%)
Course Books
Data Communications,
Computer Networks
and Open Systems
Fred Halsall
Publisher: Addison Wesley
ES/EG 3567
The Ethernet
Local Area Network
Data and Computer Communications
William Stallings
Publisher: Addison Wesley
G. Fairhurst
See also:
http://www.erg.abdn.ac.uk/users/gorry/course/books.html
What is a LAN?
A Local Area Network is....
local (i.e. one building or group of buildings)
controlled by one administrative authority
What is Ethernet?
First LAN designed at Xerox "PARC" (1972)
! 2 Mbps 75 Ohm Coaxial cable
! To share expensive laser printers
File sharing followed later
Printer
PC
PC
PC
assumes other users of the LAN are trusted
usually high speed and is always shared
either planned (structured ) or unstructured
Ethernetv2 - Blue Book (1980)
Digital, Intel, Xerox (DIX)
! 10 Mbps 50 Ohm Coaxial cable
What is Ethernet?
10B5 (Thick Ethernet)
!Yellow PVC Outer Coating (0.5")
Copper
Conductor
First LAN designed at Xerox "PARC" in 1972
Ethernetv2 followed with Digital, Intel, Xerox (DIX) in 1980
Standardised by IEEE in 1985:
! IEEE 802.3
! Two variants: Thick Ethernet and Thin Ethernet
Dielectric Insulation
50 Ohm
Various speeds now available:
! 10 Mbps (original)
! 100 Mbps (Fast Ethernet LAN)
! 1000 Mbps (1 Gbps LAN)!
! 10000 Mbps (10 Gbps)
and higher (for WAN links)
Braided Outer Conductor
Segment length ≤ 500m
Cable run needs careful attention
Good noise immunity
N-Type connector used
Vampire or In-Line external transceiver
Used mainly for building backbones
Ethernet 10B5 Cabling
Ethernet Bus
Network medium (cable)
Terminator
Ethernet trunk cable
Wiring cabinet
Repeater
Bridge
or Router
Bus Topology
Transceiver
(Attachment Unit)
Network Interface
AUI drop cable to each room
Attachment Unit
Interface Cable
50 Ohm
terminator
(one end earthed)
Host Computer
(station)
10B5 (Thick Ethernet Transceiver)
N-type Connectors
Vampire Cable Tap
10B5 (Thick Ethernet Vampire Transceiver)
50 ohm
terminator
Bolt to Tighten Block
Transceiver Block
Vampire
Transceiver
In-Line
Transceiver
15 pin AUI
D-Connector
Attachment Unit Interface
(AUI) Drop Cable
0 - 50 m
Host AUI Port
Host AUI Port
2-Part Block
Holds Cable
Insulated
Spike Pierces
Centre Core
MAU
Thick Wire
(Yellow)
Ethernet Cable
Shorter Spikes
Cut into Outer
Conductor
Cable
Ethernet 10B2 Cabling
10B2 (Thin Ethernet)
!White, Grey or Black PVC Outer Coating
Wiring cabinet
Copper
Conductor
Repeater
Bridge
or Router
Dielectric
Insulation
50 Ohm
Braided Outer
Conductor
Segment length ≤ 185m
Cable flexible and cheap
BNC connector used
Integrated or external transceiver with 'T'
Used mainly for workgroups
Difficult to manage
Ethernet Success Story
10 Base Fibre
Fibre Optic Cable
Cost-Effective
Segment length ≤1 km (2km in later spec)
Simplicity - plug and play
High noise immunity
Familiarity to customers
No electrical path (e.g. protected from lightning)
External transceiver
Used for pt-to-pt links
(i.e. connecting a pair of repeaters)
Easy to upgrade by replacing transceivers at the ends
10 Base Fibre
AUI connector
on equipment
Reaching 2-3 km (5.1 km using fibre)
10B5 ”thick” cable segments may be joined to 500m
AUI cable up to 50m at each transceiver
10BF
transceiver
“Repeaters” needed to get further
3 Copper segments (“ACTIVE”) end-to-end
1 fibre segment (“INACTIVE”) 1km
Pair of fibres
(62.5/125 )
Larger “multimode” fibre usually used
Total = 0.5 x 3+1+.05 x8 = 2.9 km !!!
MAC
5-4-3 Repeater Rule
Most LANs assign one segment
as a "backbone"
Medium Access Control
LAN interconnection device
Frames
- Data is sent on an Ethernet Network in Frames
Inactive
segments
Addressing
- All End Systems have an Ethernet Address (In their “PROM”)
- Addresses can be used in three ways:
Broadcast,Unicast, and Multicast
Not more than 5 segments in series
Not more than 4 repeaters
Not more than 3 active segments
Shared Access
- Sharing the cost of the network
- Sharing the reachability
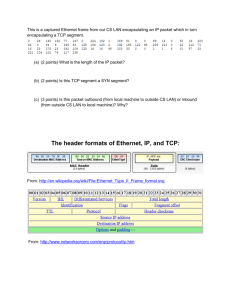
14 bytes
8 bytes
destination
address
preamble
source type
address
Ethernet MAC Address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
MAC Vendor Codes (OUIs)
08:00:20:00:00:01
08:00:20:00:00:01
The first 3B of address tells you the manufacturer
Each Network Interface Card has a MAC Address
Held in a manufacturer-configured PROM
Addresses are globally unique
A MAC Vendor Code (OUI) + Number
IEEE sells the blocks of addresses to manufacturers
Each block has 256 cubed addresses
That is 16 Million!!
080002
080003
080005
080008
080009
08000A
08000B
080011
080014
080017
08001A
08001B
08001E
080020
080022
080025
080026
3Com (Formerly Bridge)
ACC (Advanced Computer Communications)
Symbolics
Symbolics LISP machines
BBN
Hewlett-Packard
Nestar Systems
Unisys
Tektronix, Inc.
Excelan
BBN Butterfly, Masscomp, Silicon Graphics
NSC
Data General
Data General
Apollo
Sun
Sun machines
NBI
CDC
Norsk Data (Nord)
Shared Access to Ethernet Medium
Using the destination MAC address
All stations receive
the frame, but discard
the frame if the destination
address does not match
the local address
Source: A
Destination: B
Sender
Intended Recipient
C
A
D
B
Shared medium delivers all frames to all computers
A sends a frame to B
which is broadcast to
all stations
The destination station
receives the frame and
forwards it to host B
Each computer discards frames intended for other computers
This assume that a sender knows the value of the MAC address in the
destination’s PROM (we’ll find out how it does this later!)
Ethernet Frame Structure
! ! ! ! ! ! ! ! ! ! ! Unicast, Broadcast, Multicast
8 bytes
Broadcast
preamble
(1 copy to all)
14 bytes
destination
address
source type
address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
LAN address of intended recipient
Unicast
(1 copy to destination)
Multicast
(1 copy to some)
first bit = 0 indicates point to point
first bit = 1 indicates broadcast or multicast
48 bits, expressed as 12 hexadecimal digits
e.g., 12:34:56:78:9A:BC
A theoretical 200,000,000,000 addresses
! Actually 70,000,000,000... (2 bits are used)
20,000 MAC addresses for each person on the planet!
Group MAC Addresses
Special MAC Addresses
FF:FF:FF:FF:FF:FF
01:00:5E:00:00:FF
The all 1’s Address is used to send to all NICs
! Known as the broadcast destination address
! Only ever used as destination address
!
00:00:00:00:00:00
The all 0’s Address is special
! Known as the unknown address
! Only ever used as source address
Groups addresses
! Have the least significant bit of the first byte to 1
! The remainder forms the specific group address
!
Group addresses identify “channels” not Receivers
! Sender chooses a group address to use
! e.g. one channel may carry an Internet TV station
NICs need to “register” to receive a group
! A computer may “register” several group addresses
! The NIC passes all packets with addresses that match
!
Multicast on Ethernet
Why not just choose addresses randomly?
Server
So... you could decide to not have a central register of addresses
! Why not just choose a random address at power-on?
1 Receiver
Client
(destination
address matches)
Server
3 Multicast
Receivers
Client
(registered)
Client
Not
(registered) Registered
Client
(registered)
TV/Radio/etc Transmission (several receivers)
Answer
You’d need a very big address range to be unique!
!
The Birthday Paradox
What is the probability that two people in N have the same birthday?
N = number in a room; Let P = probability of NO collision
N=1, P=1
N=2, P=1 x (364/365)
N=3, P=1 x (364/365) x (363/365)
In general, P = 365 ! /((365-N)! x (365^N))
Probability of no collisions = (1-P)
N=23, gives P= 0.5!
Multicast
How many MAC addresses do I need?
Multicast
Unicast
In a small company 100’s to 1000’s
Broadcast
Why Multicast?
! Sending same data to multiple receivers
At home?
Why do they have to be globally unique?
What happens if they are not unique?
Advantages
! Network: less traffic than sending same data several times
! Server: Less Server Load
! Traffic/Load scales (1/N) for N receivers
! ! i.e. for 3 receivers 1/3 traffic
! ! i.e. for 1000 receivers 1/1000 of the utilisation!
!
Summary
All NICs have a MAC Address
! - Also provides an income stream to the IEEE :-)
Ethernet Transmit
All NICs receive:
Every frame with a broadcast MAC destination address of ff:ff:ff:ff:ff:ff
Sharing the Media
(shared bus)
(shared wireless channel)
Every frame with a destination address that matches its PROM
Every frame with a destination address that matches a registered
multicast group address (i.e. used by a program on a computer)
!
All filtering is performed within the NIC
Computer does not know about discarded frames.
A computer can override filtering, by placing NIC into
promiscuous mode - where all frames are received.
Sharing the media
Printer
PC
PC
PC
ALOHA Collision
A
B
B does not
notice that
A is already
sending
There is only one medium (cable)
All NICs should be able to use the cable
Clearly only one should send at a time
How does a NIC know if it may send?
Idle
A, B will both need to
send again at a later time
Maximum ALOHA Channel Throughput
Listen-Before-Talk
B
A
kmax= (2eLd)-1
L = average number of frames/sec
B hears A
and waits
Assumes a poisson arrival distribution
d = duration of each frame
Idle
B sends
Maximum throughput at 1/2e, i.e., 18.4%
Also called Carrier Sense Multiple Access
Collisions and Collision Detection
Slot Time
A starts transmission
t=0
A
B
t=∂t
t=2tp
A
B starts transmission
A
A detects collision
B
B
All senders need to know when a collision occurs.
t=tp
B detects collision
The sharing in a CSMA/CD system is controlled by the slot time.
A
B
The slot time In a IEEE 802.3 LAN is 51.2 µs (i.e. 64 B).
t=2tp
A detects collision
it limits the maximum distance across a LAN as 3km at 10 Mbps.
A
B
It defines the minimum Ethernet frame size (60 bytes+CRC32)
A minimum frame size is need to detect collision
Random Backoff
t=2tp
A detects collision
A
Retransmission
B
A
B
Senders need to back-off different periods.
Each sender waits for a random period of time
Senders choose a random number from a set of values [0...t]
Value is multiplied by the Ethernet Slot Time (51.2 microsecs)
Each attempt the sender exponentially increases t ([0..1], [0..3],[0..7]...)
Retransmit
[0,1]
Retransmit
[0,1]
A picks 0
from the
set of [0,1]
50% probability the two NICs choose different numbers
Exponential Back-Off
[0,1] First Retx
B
A
Random Backoff
[0,1,2,3] Second Retx
A
B
Result
0
0
Collision
0
1
A sends
0
2
B sends
0
3
A sends
1
0
B sends
1
1
Collision
1
2
A sends
1
3
A sends
2
0
B sends
2
1
B sends
2
2
Collision
2
3
A sends
3
0
B sends
3
1
B sends
3
2
B sends
3
3
Collision
Random Random
number at number at
A
B
Idle
Retransmit
[0,1]
Retransmit
[0,1]
Retransmit
[0,1,2,3]
Idle
Retransmit
[0,1,2,3]
Result
0
0
Collision
0
1
A sends
first
1
0
B sends
first
1
1
Collision
after 1
slot time
Binary Exponential Random Backoff
Ethernet Transmit Algorithm
Defer between
(0 and 2K)x 51.2 µS
where K=N, K≤10
Send Frame
(21
1st time K=1
– 2 values)
2nd time K=2 (22 – 4 values)
3rd time K=3 (23 – 8 values)
4th time K=4 (24 – 16 values)
5th time K=5 (25 – 32 values)
....
10th time K=10 (210 – 1024 values)
11th time K=10 (210 – 1024 values)
12th time K=10 (210 – 1024 values)
13th time K=10 (210 – 1024 values)
14th time K=10 (210 – 1024 values)
15th time K=10 (210 – 1024 values)
16th time – abort transmission!
N:= 0
Inter frame gap
allows receivers
time to settle
Carrier
Sense
Defer R x 51.2 µS
busy
Defer
K:= N
idle
wait 9.6 µS
N≤10
?
Transmit
Frame
yes
Transmit
4B Jam
N++
Test
Count
N=15
no
Increment Retry Count
Done
A
B
Congestion
collapse
Maximum
(Ethernet)
Offered Load
Performance degrades with increasing load
- when there are many NICs with data to send
Aborted
Capture by A
100%
0
N > 10
N < 15
Collision
Ethernet Utilisation
0
K:= 10
N ≤ 10
Maximum
(random retransmission)
Utilisation
Select Random Integer
R:
(0...2^(k-1)}
and 2K)
R =={0
Retransmit
[0,1]
Retransmit
[0,1]
Retransmit
[0,1]
Retransmit Idle
(A,B wait)
[0,1]
Retransmit
[0,1,2,3]
Retransmit
[0,1,2,3,
4,5,6,7]
Multiple Access - Summary
ALOHA
! Requires Checksum (CRC)
! Problem: Many collisions when many nodes
! Efficiency: 100% (1 node) 18% (many)
Listen-Before-Talk (CSMA)
! Requires Carrier Sense (CS)
! Problem: Collisions still possible
!
Collision Detection (CSMA/CD)
! Requires Collision Detect (CD) with Back-Off
! Problem: Capture possible
! Efficiency: 100% (1 node) higher (many)
Recap: Strengths v Weakness of CSMA/CD
Strengths
No controlling system needed
Easy to add new systems (NICs)
Performance “reasonably fair”
Weakness
Performance degrades with increasing load
One “busy” system can “capture” capacity
- more of a problem for “upstream”
(e.g. wifi base station, router)
On balance good design!
Ethernet Frame Structure
Ethernet Transmit
14 bytes
8 bytes
destination
address
preamble
Sending
the
Data
source type
address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
LAN address of intended recipient
first bit = 0 indicates point to point
first bit = 1 indicates broadcast or multicast
62 alternating 1's and 0's ( to lock receiver PLL)
followed by 11 (to indicate start of frame)
The Physical Layer
Synchronous Serial Communications
Synchronous Serial Communications
Tx Clock
Byte
76543210 76543210 76543210 76543210
Data in Frame consists of a series of bytes
One byte processed at a time
Each byte converted to 8 bits
One bit sent at a time as an electrical signal
serial bit stream
Byte
Rx Clock
Uses two shift registers (both clocks must be the same)
- Note that bytes are sent l.s.b. first!
Recall the Ethernet broadcast/unicast address bit?
T!
NE
R
HE
ET
IN 0 encoded:
SED
Traditional Synchronous Transmission
Non Return to Zero
Data
1 encoded:
TU
O
N
Clock
Data
Clock
2 signal levels used
The level indicates the value of each bit
- a low level indicates 0
- a high level indicates 1
The bandwidth of NRZ is approx 1 Hz / bit
!
SED
TU
NO
Data
Driver
Data
Clock
Clock
Clock signal transitions indicate centre of each bit
Requires two wires (clock & data)
Non Return to Zero
T
NE
R
E
IN
Driver
Manchester Encoding
H
ET
Data
0 encoded:
1 0
1 encoded:
0 1
NRZ
The receiver needs some way of determining the clock...
2 signal levels used
Transition in the centre of each bit
- down-wards transition indicates 0
- up-wards transition indicates 1
Double the bandwidth compared to NRZ
Encoded Data
Data
Encoded
Data
Decoder
Encoder
Clock
DPLL
Data
Manchester Encoded Signal
Data
Clock
NRZ
What no clock wire?
Digital Phase Locked Loop (DPLL) regenerates clock
Combined clock & data signal
cilloscope
Ethernet Waveform
Manchester Encoding - Bandwidth/Eye Diagram
Waveform on Oscilloscope
Bit #5
Bit #4
0.1
0V
-0.225 V
Bit #7
Bit #6
Bit #8
0.2
0.3
0.4
0.5
0.6
0.7 Time ( uS)
Bit #9
-1.825 V
0
Time ->
1
0
1
1
1
1
0
Can you decode this?
Eye Diagram on Oscilloscope
Transitions
at centre of bits
Bits 4 - 20
Power
Waveform as seen on an oscilloscope may be inverted!
20 MHz
<--- 1 Symbol ---->
Frequency
Manchester Encoding
Ethernet Reception
Three parts to decoding each bit of data
1) We need a clock signal at the receiver
2) We need to know the start of the data
(and polarity of a ‘1’)
2-signal levels used
3) We need to identify the end of frame
No DC component (even for long runs of 0‘s or 1’s)
Timing component at fundamental clock frequency (10 MHz)
Double bandwidth of NRZ (but Ethernet uses RF cable!)
Ethernet Clock Recovery
0.1
0V
-0.225 V
0.2
0.3
0.4
0.5
0.6
0.7 Time ( uS)
-1.825 V
Ethernet Clock Recovery by DPLL
0.1
0V
-0.225 V
0.2
0.3
0.4
0.5
0.6
0.7 Time ( uS)
-1.825 V
0
1
0
1
1
1
1
0
0
1
0
1
1
1
1
0
Encoded
Data
DPLL
Clock
DPLL contains a clock (oscillator)
Uses the phase transitions to lock oscillator frequency
If transition late, decreases period (increases frequency)
If early, increases period (decreases the frequency)
After many transitions frequency matches original clock
Carrier
Detected
Leading
Aligned
Lagging
Digital Phase-Locked Loop (DPLL)
Encoded
Data
Preamble Sequence
One bit sample
Centre of bit
Rx Data
Bit Sample
You do not
need to
reproduce
this!
x8 Clock
Correction Logic
14 bytes
8 bytes
source type
address
destination
address
preamble
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
÷ 8 Divider
Clock
Regenerated Clock
Ethernet Preamble Sequence
Loss of the start of the preamble
0.1
0V
-0.225 V
1 0
1
0
1
0
1
....
0.2
0.3
0.4
0.5
0.6
0.7 Time ( uS)
-1.825 V
0
1
0
1
1
1
1
0
“LOST”
Sequence of 62 alternating 1 and 0’s
Forms a square wave when encoded!
Start of frame delimiter (11 in l.s.b. position of last byte)
Strictly speaking the preamble is 7B and the SFD is (1B)
DPLL
Lock
NOTE:!
(1) Each sender will have a slightly different clock signal
(2) Not all bits of the preamble are “received”
More bits
in preamble
Ethernet Frame
More bits
in preamble
Ethernet Inter-Frame Gap / Spacing
More bits
in frame
A silent time between frames (no carrier on medium)
Allows electronics to recover after end of previous frame
20 byte periods (measured from end to next SFD)
10 Mbps: at least 9.6 microsecs between frames (at sender)
Carrier
Detected
Carrier
End
DPLL
Lock
Start of
Frame
Delimiter
(some descriptions say 10.4 microsecs)
Summary
IFG between each frame
Ethernet
Receiver
Operation
All Ethernet frames have a preamble
62 bits with 10
First bits used to detect carrier
Remainder allow DPLL to gain lock (takes time)
Not all preamble bits are “received”
Receive Frame
Start of MAC header detected by 2 bits, with 11
Carrier Detect
data =11?
Final bit in frame detected by absence of carrier
Start
of frame
CRC &
size
Error
Increment
Error Count
OK
Address matches
Local address
Broadcast address
Multicast address
CRC-32 used to verify the process
Wait for DPLL lock
no
yes
Length ≥ 64 B
Length ≤ 1518 B
Integral No Bytes
CRC = OK
addr
match
no
yes
Forward
Integrity Checks
Discard
Check Digits
Errors can and do occur
CSMA - Collisions
Interference, cable faults, equipment faults
Simplest form of check is a “sum” of digits/bytes
Limited usefulness in detecting errors
(e.g. can’t detect transpositions)
Size depends on length of data (PDU)
Simple check digit systems are easily understood
and implemented by humans:
Add odd digits
(not including the check digit)
Multiply by 3
Add even digits
Add results together
Take remainder of division by 10 modulo 10)
Subtract from 10
If remainder is 0, use 0 as the check digit.
Better algorithms trade probability of catching
errors against implementation cost
Universal Product Code (UPC)
UPC-A barcode is "02400000166x"
Add odd digits: 4+6+1 = 11
Multiply by 3:3 x 11= 33
Add even digits: 2+6 = 8
Add results together: 33 + 8 = 41
Take remainder of (41 / 10) = 1
and subtract from 10 i.e. (10 - 1 ) = 9.
The last digit is the check digit, "9".
Del Monte Pineapple Sliced In Its Own Juice
Size: 24/8 oz
Napolina Chopped Tomatoes
UPC-A is "501006100161x" what is the check digit?
Add odd digits: 5+1+0+1+0+6 = 13
Multiply by 3:13 x 3 = 39
Add even digits: 0+0+6+0+1+1 = 8
Add results together: 39 + 8 = 47
Take remainder of (47 / 10) = 7
and subtract from 10 i.e. (10 - 7 ) = 3.
Check digit is 3.
Many other uses of Check Digits
Cyclic Redundancy Check (CRC)
14 bytes
8 bytes
The UPC Check Digit detects:
single digit errors, such as 1 → 2
transposition errors, such as 12 → 21
human errors, such as 19 → 90
destination
address
preamble
source type
address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
CRC is a form of digital signature (32 bit hash)
Calculated at the sender & sent
Similar method used by ISBN-13
Odd digits multiplied by 3 instead of even digits
e.g.
Data and Computer Communications (9th Edition)
by William Stallings
ISBN-13: 978-0131392052
Re-calculated at the receiver
Two values compared at receiver
Able to verify the integrity of the frame
CRC detects:
Frames that have been corrupted
Frames where the DPLL failed
Division
Why Modulo 2 Division?
not used
Because the hardware solution is simple!!!!!
!
!
!
divisor
! !
! !
! !
generator
polynomial
!
!
!
!
!
!quotient
) dividend
Truth Table for Modulo-2 Division (XOR)
!___________
!
! !remainder
0⊕0=0
0⊕1=1
1⊕0=1
1⊕1=0
content of
frame
CRC calculations ignore the carry
fixed size (<divisor)
used for checksum
ts do
Studen
Modulo 2 Division
Modulo 2 division
replaces addition
in BCC calculation
First digit
must be '1'
Example simplified to generate a short (4 bit) CRC
n
lculatio
Modulo Division
10
11001 ) 1 1 1 0 0 1 0 1 0 0 0 0
⊕ 1 1 0 0 1 ¨
0|0 1 0 1 1
⊕ 0 0 0 0 0
0|1 0 1 1
1
11001 ) 1 1 1 0 0 1 0 1 0 0 0 0
⊕ 1 1 0 0 1
0|1 1 0 1
This digit must always be 0
CRC ca
You do not
need to
reproduce
this!
0's are appened
to the dividend
(flush bits)
Divisor
(Generator Polynomial)
d
not nee
e
duce th
to repro
1!
2!
3!
4!
5!
Bring next digit of dividend down
Copy msb of value to quotient
Insert 0 (if quotient 0) or divisor (if quotient 1)
Calculate XOR sum
Discard msb of value (always 0)
CRC Value
1011
11001 ) 1 1 1 0 0 1 0 1
⊕ 1 1 0 0 1
0|0 1 0 1 1
⊕ 0 0 0 0 0
0|1 0 1 1 0
⊕ 1 1 0 0 1
0|1 1 1 1 1
⊕ 1 1 0 0 1
0|0 1 1 0
⊕ 0 0 0 0
0|1 1 0
You do not
⊕ 1 1 0
need to
0|0 0
⊕ 0 0
reproduce
0|0
this!
⊕ 0
0|
0100
0000
0
0
00
01
010
000
0100
0000
0100
CRC value = Remainder
CRC Value after an Error
1011
11001 ) 1 1 1 0 0 1 1 1
⊕ 1 1 0 0 1
0|0 1 0 1 1
⊕ 0 0 0 0 0
0|1 0 1 1 1
Bit error in frame
⊕ 1 1 0 0 1
0|1 1 1 0 1
⊕ 1 1 0 0 1
0|0 1 0 0
⊕ 0 0 0 0
0|1 0 0
You do not
⊕ 1 1 0
need to
0|1 0
⊕ 1 1
reproduce
0|1
this!
⊕ 1
0|
Hardware Example: CRC-32
0111
0000
Received CRC
replace by 0's
0100
0
0
00
01
010
001
0110
1001
1111
≠
CRC value = Remainder
Ethernet Receiver
Receive Frame
Sum = x32 + x26 + x23 + x22
Received CRC
Calculated CRC
⇒ ERROR !!!!!
Carrier Detect
+ x16 + x12 + x11 + x10
Start
no
of frame
?
yes
+ x8 + x7 + x5 + x4 + x2 + x + 1
+
Receive Frame
+
+
Wait for DPLL lock
Length ≥ 64 B
Length ≤ 1518 B
Integral No Bytes
size
OK?
CRC received
= CRC calculated?
CRC
OK?
Address matches
Local address
Broadcast address
Multicast address
addr
match
Error
Increment
Error Count
OK
+
Data In
+
+
+
+
+
+
+
+
+
+
Error
Increment
Error Count
OK
no
yes
Forward
Discard
32 1-bit shift register elements
AUI Interface
MAC Functions
Gain access to medium by listening for activity (e.g. CSMA/CD)
Co-ordinate sharing of the medium between users
Attachment Unit
Interface (AUI)
Ethernet
Controller
AUI drop cable
(0 -50m)
5 shielded pairs
Power &
Ground
Medium Attachment
Unit (MAU)
or Transceiver
Rx
CS
Jabber
Control
Tx
MAU
Control
Media Interface
* Jabber is transmission of a frame longer than the maximum allowed.
Address single and groups of stations
! (i) Static address of each computer (copied from PROM)
! (ii) 1 or more dynamic group addresses (e.g. multicast)
! (iii) Broadcast address to send to every computer
Diagnose failures
! (i) transmission errors (detected by CRC-32)
! (i) protocol errors (e.g. jabber (too long) , runt (too short))
! (ii) cabling (e.g. loss of carrier, reflection from a cable break)
Why connect LANs?
Repeater
Identical physical interfaces
LAN A
Connecting
Device
Similar or different media (cabling)
Ethernet frames
received here
... are retransmitted here
Physical
Physical
LAN B
Isolation of cabling faults (partitioning)
Part 1 Regeneration of Clock and Data
Repeater
Repeaters
Repeater regenerate signal to all output ports
Receive “poor” signal
Lock to clock (using DPLL)
Uses:
! Extends media length and number of NICs
! Allows conversion between media types
! Allows for more flexible cable routing
Decode bits using Manchester Decoder
Reconstruct 0’s and 1’s of frame
MUST also regenerate full preamble
Function:
! Connect segments and regenerate signal
N.B. All interfaces must operate at same speed!
Re-encode bits using Manchester Encoder
Send “good” signal
Clock Regeneration
Minimum Frame Size - LAN slot-time
Sender
Minimum Frame size needed
Signal must reach all nodes before sender finishes
Ethernet defines a minimum payload of 46B
(64B including MAC header and CRC)
Part 2 : Repeaters must participate in CSMA/CD
Regeneration to all parts of the LAN
Ethernet LANs
Repeaters
Sender
Systems using a repeater need to to use CSMA/CD
All need to see each other signals
Assume one NIC sends
Sender
Participation in CSMA/CD
Repeater Network (1)
1.
Ethernet LANs
Sender
Sender
Repeaters
Sender
Sender
2.
Jam
Jam
Assume both senders transmit at same time
Repeater Network (2)
CSMA/CD determines maximum number of repeaters
3.
4.
Back-Off
Back-Off
1 collision domain
• Repeaters need to:
• Detect Collisions
• “regenerate” collisions on all output ports
• This takes time...
• Limits maximum number of repeaters in series
5-4-3 Repeater Rule
Most LANs assign one segment
as a "backbone"
LAN interconnection device
Inactive
segments
Not more than 5 segments in series
Not more than 4 repeaters
Not more than 3 active segments
Ethernet Cabling
Repeater Network
1
3
d
d
c
f
c
5
e
d
b
b
a
2
e
4
c
f
10B5 (Thick Ethernet)
c
10B2 (Thin Ethernet)
e
f
c
e
a
10BT (Unshielded Twisted Pair)
f
b
e
Ethernet
Cabling
d
b
a
b
a
d
a
f
g
10BF (Fibre Optic Pair)
10B5 (Thick Ethernet)
Copper
Conductor
Dielectric Insulation
50 Ohm
!Yellow PVC Outer Coating (0.5")
Braided Outer Conductor
Segment length ≤ 500m
Cable run needs careful attention
Good noise immunity
N-Type connector used
Vampire or In-Line external transceiver
Used mainly for building backbones
10B2 (Thin Ethernet)
!White, Grey or Black PVC Outer Coating
Copper
Conductor
Dielectric
Insulation
50 Ohm
Braided Outer
Conductor
Segment length ≤ 185m
Cable flexible and cheap
BNC connector used
Integrated or external transceiver with 'T'
Used mainly for workgroups
Difficult to manage
Ethernet 10B2 Cabling
10 Base Fibre
Wiring cabinet
Repeater
Bridge
or Router
Fibre Optic Cable
Segment length ≤1 km
High noise immunity
No electrical path
(protected from lightning)
External transceiver
Used for pt-to-pt links
(i.e. connecting a pair of repeaters)
Easy to upgrade
Reaching 2-3 km (5.1 km using fibre)
10 Base Fibre
AUI connector
on equipment
10B5 ”thick” cable segments may be joined to 500m
AUI cable up to 50m at each transceiver
10BF
transceiver
“Repeaters” needed to get further
3 Copper segments (“ACTIVE”) end-to-end
1 fibre segment (“INACTIVE”) 1km (2km in later spec)
Pair of fibres
(62.5/125 )
Total = 0.5 x 3+1+.05 x8 = 2.9 km !!!
10BT or UTP (Unshielded Twisted Pair)
First Stage of
Evolution
10BT or UTP (Connectors)
10BT Port
Alternative
AUI Port
Segment length 0.6m – 100m
Cable flexible and very cheap
RJ-45 connector used
Easy to manage / install
Integrated or external transceiver
8-pin RJ-45 Connector
Unshielded Twisted
Pair cable to hub
(2 Pairs)
Cable has 4 twisted pairs
2 are used in 10 BT:
Pins 1,2 (white+orange/orange)
and
Pins 3,6 (white+green/green)
EIA/TIA TS 568 wiring
Pin
T568A T568B
Signal
Pair
Pair
+
T568A Colour
OLD
T568B/C Colour
NEW
1
3
2
2
3
2
3
2
3
+
white/green
white/orange
green
orange
green
solid
orange
solid
white/orange white/green
4
1
1
-
white/green
white/orange
blue
blue
5
1
1
+
6
2
3
-
7
4
4
+
solid
blue
solid blue
white/blue
white/blue
white/blue
white/blue
orange
green
ring
green
solid
orange
solid
white/brown
white/brown
8
4
4
-
white/brown
white/brown
brown
brown
-
ring
white/green white/orange
Ethernet 10BT Cabling
Wiring cabinet
2 or more
UTP pairs
to each room
Wiring centre
& 10BT Hub
brown solid
brown solid
10BT Equipment
10BT Hub
Power Supply AUI port
20 MHz Crystal
Differential Transmission
10B2 Port
VLSI repeater
8 10BT Ports using RJ-45 Connectors
Indicator lights for each segment
10 BT uses two pairs.
100 Ohm termination
Uses 2 wires TWISTED to form a PAIR
0 Signal sent +ve on one wire, -ve on other
1 Signal sent -ve on one wire, +ve on other
One pair for transmission
One pair for reception
Basic CSMA/CD algorithm means use one direction at a time
LAN Summary
Bridges
Next Stage
of Evolution
You should know...
What a LAN is!
- Ethernet is the important example
- Medium Access Control protocols
- There are different types of Ethernet Media
LAN 1
LAN 2
Control
Next: Repeaters
- How to join Ethernet cable segments
- How CSMA/CD works across the LAN
When Do We Need A Bridge?
Bridges
Bridges are needed to:
! Connect > 1024 nodes
! Extend total network diameter
! Connect more than 5 segments in series
Bridges also:
! Increase maximum capacity of network
! Deny unauthorised use of the network
§
Use of the Ethernet Destination Address
Bridge
Different subnetwork hardware addresses
14 bytes
8 bytes
preamble
Address Table
destination
address
source type
address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
Address Table
Filter Table
NIC inserts a destination address in each frame
Data Link
Switches can now “see” where to send the frame
Physical
Physical
- i.e. using the “topology” information in the address table
- switches do this for each frame
Similar or different subnetworks
Address Table
1
00:11:00:02:03:04
Bridge 1
Forwarding (I)
Unicast frames sent only if destination is on another port
1I
Address
Table
(reads frame destination address & uses address table)
Sent only to specific port
00:EF:15:13:03:41
Unknown destinations flooded
(reads frame destination address, but not in address table)
One entry for each MAC Address, indicating port used
MAC Address
Static
Port
00:11:00:02:03:04
Yes
I
00:EF:15:13:03:41
Yes
II
Sent to all ports except the receiving port
Broadcast “flooded”
Multicast also “flooded” (unless configured group addresses)
Forwarding (II)
Static
Port
00:11:00:02:03:04
MAC Address
Yes
I
00:EF:15:13:03:41
Yes
II
Example Network
Ethernet LANs
Bridges
Sender
Is frame destination address in table?
NO - forward to all ports EXCEPT incoming port (flood)
YES - Look-up address and find table port
Is table port == incoming port?
NO - forward only to table port
YES - discard the frame
Receiver
Sender and Receiver on the same LAN segment
Bridged Network (1)
Example Network
Ethernet LANs
Sender
Sender
Bridges
Sender
Sender
Buffered
Assume both senders transmit at same time
red sends to green
green sends to red
How many bytes need to be read?
Bridged Network (2)
8 bytes
preamble
14 bytes
destination
address
source type
address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
The first 6 bytes identify the destination!
However, it is important to read at least first 64B
- collisions, etc result in packets less than 64B
No frames sent here
- “runt” frames MUST NOT be forwarded
Separate collision domains
Cut-Through Forwarding
Simple bridges receive a frame in full before forwarding
This lets the bridge check the frame is valid
Frame Header contains all addresses
Could start to forward as soon as 64 bytes are received
This eliminates some of the delay in storing data
1.2 ms lower transit delay!
Disadvantages
Could start to forward an oversize frame :-(
Could start to forward a frame with a bad CRC :-(
These frames are forwarded by CRC invalidated.
Known as “cut-through”
Summary of Bridge Forwarding
NIC operates in promiscuous mode
! (receives all frames ignoring destination address)
Bridge checks frame
! Check length and CRC
Stores in internal memory
Cut-Through can forward before receiving CRC !
Examine address table for destination address
Forward if matches different port to output port
Discard if matches same port as output port
Otherwise, flood to all ports (except input)
Examine filter table for an address match
Discard if matches filter table
May also send “traps” to alert network manager
Bridges are “smart”
Static Entries in tables
Part II - Dynamic Learning of Addresses
Static Tables are fine....
Can also fix the MAC address to a specific port
(useful in “public areas” to prevent hacking)
LAN 1
LAN 2
BUT!
Control
Someone needs to keep address tables correct
Address Table usually generated automatically
Makes bridges “Plug & Play
Static entries
Difficult to track 100’s, 1000’s of addresses
Prevent frames reaching wrong part of LAN
An automated method is required...
Address Table
Ethernet Collision Domains
Use of the Ethernet Source Address
8 bytes
preamble
14 bytes
destination
address
source type
address
46 -1500 bytes
4 bytes
packet of data to be sent
CRC
Bridges
II
00:EF:15:13:03:41
I
NIC inserts its own address in each frame!
Address
Table
00:5E:45:23:12:01
Switches can now “see” where a source is
- i.e. dynamically assign port & MAC in address table
MAC address
Static
Port
00:5E:45:23:12:01:03
00:EF:15:13:03:41:55
YES
YES
I
II
“Learning” entries in the Address Table
1
00:11:00:02:03:04
Address
Table
00:EF:15:13:03:41
00:02:00:02:03:FE
Entries made for each new (unicast) MAC Address
MAC Address
Dynamic Learning of Addresses in the Table
00:01:00:02:03:FF
Bridge 1
1I
- actually switches do this for every frame
00:11:00:02:03:04
Static
Yes
Port
I
00:EF:15:13:03:41
Yes
II
00:01:00:02:03:FF
No
I
00:02:00:02:03:FE
No
II
MAC Address
00:11:00:02:03:04
00:EF:15:13:03:41
Static
Yes
Port
I
Expires
never
Yes
II
never
00:01:00:02:03:FF
No
I
2 secs
00:02:00:02:03:FE
No
II
3 mins
Each entry is ”aged”
! old entries are deleted.
!
Age updated as packets arrive from a src address
Each second, all ages reduce
Zero entries are deleted
Idiot-proof plug&play?
Bridge 1
Loops
Bridge 1
Bridge 2
Connecting two networks needs a bridge
Connecting two bridges in parallel may cause looping
First deployed bridge did not work :-(
Bridges MUST NOT forward in loops!
You need to connect a port to each network :-)
The Spanning Tree Algorithm (STA) provides
an automatic way to ensure this (not in current course!).
The Spanning Tree Algorithm
Loops between bridges/switches?
Bridge 1
Bridge 2
Bridge 3
End System C
Bridge 1
Bridge 2
X
End System A
A sends to C
Connecting two bridges in parallel may cause looping
Bridges 1,2,3 receive the frame
Therefore need Spanning Tree Algorithm (STA)
Bridges 1 forwards the frame, Bridges 2,3 receive the frame
! Each bridge is either: Blocked, Learning or Forwarding
! There is only one active forwarding path to each LAN
! One bridge (the root) co-ordinates the other bridges
Bridges 2,3 also forward a copy of the frame
There are now three packets that have been forwarded
Each will also be forwarded be each bridge
Exponential proliferation of packets in the network
The Spanning Tree
A
11
X
3
2,3,3
Filter
6
7
2,1,7
9
2,2,4
2,0,2
2
10
Filter
5
Filter
2,0,2
4
2,2,4
Each port is a seperate LAN
2,1,6
2,2,11
The switch (a multi-port bridge)
14
Switch
Filter
2,1,5
2,1,14
Bridges form a tree that links all segments
Frames not necessarily forwarded along an optimal path
X->A is rather longer than necessary
(Note: IP Routers do more optimal forwarding)
Bother with spanning tree?
Ports
33
“Flooded” packets sent to all ports
except that on which received
Address Table (II)
Using a CAM for the Address Table
Bridge 1
MAC
Address
Address
Table
Two types of table entry:
! Static addresses to forward (set by administrator)
! Learned address to forward (dynamic entries)
Table COULD be implemented as an array !
! - may be a software “Tree” structure
- usually a Contents-Addressable Memory (CAM)
A CAM will be needed for high-speed switches!
Port
Address add:
CAM stores this in next available cell
Cell stores address, port, timestamp (and other info)
Entries checked by matching address (and other fields):
CAM automatically updates timestamp
Returns the cell information if there is a match
Can automatically handle purging of old addresses
Each read/write access performed in one cycle (e.g 50 ns)
CAM Design
The Filter Table
Good to set policies
Prevent frames from being forwarded to specific ports
Different subnetwork hardware addresses
Log/track users as they use the network
Address Table
Filter Table
Address Table
Data Link
Physical
Cost much higher than a RAM chip
Each cell has its own comparison logic
Physical
Bridges also check filter table BEFORE forwarding
Discard
if matches
filter
table
Similar
or different
subnetworks
May also send “traps” to alert network manager
Summary of Bridge Learning
Thinking about the Address Table
Things to think about:
! An end system that only listens (never sends)
! ! - Frames are broadcast to all ports
! ! - Could configure a static entry
An end system is turned off
! ! - Address entry will age and be deleted
!
!
!
!
An end system moves to another collision domain
! - Bridge will have learned the wrong port
! - End system will not receive unicast packets
! - Entry updated when end system sends
Bridges Learns form Source Address of Frames
Need to send to “create” entry in the Address Table
Address associated with a port
Address aged (old entries deleted)
Unknown destination addresses flooded
Simple Plug and Play
Must not form loops!
Examine filter table for an address match
Discard if matches filter table
May also send “traps” to alert network manager
Can also send the “frame contents!”
Bridges are “smart”
Q2.2
Fast Ethernet
Bridge Tutorial Question
100 Mbps
W
X
R
A
Y
B
B
Z
C
Four computers (W,X,Y,Z) are connected by 3 Ethernet segments (A,B,C)
using a Repeater (R) and a Bridge (B).
(a) Which computers receive (at the network level) the following
frames (show also which LAN segments carry each frame)
W -> Broadcast
X -> Z
Y -> Z
Y -> Broadcast
(b) W, X are members of the multicast group 0x23.
W = 0x00102030 and X = 0x00102040.
Sketch the MAC header for a multicast frame sent from X.
Which segments carry this frame?
Fast (100 Mbps) Ethernet
System
UTP cable
System
Fibre
System
System
Two Media:
Collision Domains
Broadcast Domains
Faster Transmission Speeds
Full Duplex [& Half Duplex]
100B-FX
Physical Layer for Fast (100 Mbps) Ethernet - 10BT
Copper (Unshielded Twisted Pair)
Uses 2 of the 4 twisted pairs in in CAT5 UTP
Pins 1 & 2 for Transmit; Pins 3,6 for Receive
CAT 5 UTP has a bandwidth of 100 MHz
100 Mbps Copper (UTP)
Manchester Encoding
100 Mbps Fibre
~ 20 MHz bandwidth (Carrier 10 MHz)
Two Modes:
Half Duplex (CSMA/CD) - Little used
~200 MHz bandwidth (Carrier 100 MHz)
Full Duplex (to switch ports)
100Mbps Manchester Encoded waveform
Frequency response for Cat5 UTP
5 bits
Power
Does not work
over CAT-5 UTP!
Frequency
20 MHz 125 MHz
4b/5b Encoding
4 bits
200 MHz
100 MHz UTP cable bandwidth
~ 200 MHz for Manchester Encoding :-(
4b/5b
4b/5b Encoding
4 bits have 2^4 (16) values
5 bits have 2^5 (32) values
Chooses an encoding rule that has:
2 changes/bit (ensures sufficient timing for DPLL)
≤3 bits changed in 5 bits
4b/5b Encoding
Decimal
0
1
2
3
4
5
6
7
8
9
A
B
C
D
E
F
Binary
00000
00001
00010
00011
00100
00101
00110
00111
01000
01001
01010
01011
01100
01101
01110
01111
Signaling Codes
Encoded
11110
01001
10100
10101
01010
01011
01110
01111
10010
10011
10110
10111
11010
11011
11100
11101
There are 16 unused encoded values
Some of these are used for signaling special events:
Quiet (00000) Idle (11111) Halt (00100)
Starting delimiters J (11000) K (10001)
Ending Delimiter T (01101)
Control Reset (00111) Set (11001)
The remaining should never be sent
Reception of these indicates an error
4b5b Encoded waveform
MLT-3 Encoding
125 Mbps
31.2 MHz
Sent least significant 4b first
MLT-3
Then sends most significant 4b
Contains transitions needed for receiver DPLL
Contains start, end and other control signals
However, spectral bandwidth is > 100 MHz!
Power
Frequency response for Cat5 UTP
MLT-3 Encoding
Levels -1, 0 +1
0 data sent as no change
1 data sent as next value in a sequence:
(0) -> (1) -> (0) -> (-1) -> (0) ...
NRZ 0 0 0 1 0 0 1 0 1 1 1 0 1 0
MLT-3 0 0 0 + + + 0 0 - 0 + + 0 0
Frequency
20 MHz
31.25-62.5 MHz bandwidth for 4b/5b+MLT-3 :-)
250 MHz
Example encoding
How does MLT-3 Encoding compress the frequency?
Fastest change results when sending 1,1,1,1 etc
Manchester
Clock
baud x 2
MLT-3
MLT-3
signal
Data
baud / 4
1
1
0
1
0
1
2ns/Division
Data
1
1
1
1
1
2ns/Division
Max fundamental frequency = 100*5/4*1/4 = 31.25 MHz
Waveform on Oscilloscope
Manchester Encoding - Bandwidth/Eye Diagram
How does MLT-3 Encoding compress the frequency?
Waveform on Oscilloscope
Bit #5
Bit #4
Bit #7
Bit #6
Bit #8
Bit #9
Time ->
Fastest change results when sending 1,1,1,1 etc (125 Mbps)
Eye Diagram on Oscilloscope
MLT-3
Bits 4 - 20
Power
baud / 4
20 MHz
Data
1
1
1
<--- 1 Symbol ---->
1
1
2ns/Division
Max fundamental frequency = 100*5/4*1/4 = 31.25 MHz
Frequency
AMD
Data to be Transmitted (After 4B/5B Encoding and Scrambling)
1
1
1
1
1
0
0
1
1
1
0
1
0
0
1
0
1
7
8
9
10
11
12
13
14
15
16
17
1
2
3
4
5
6
0
0
1
1
1
1
0
MLT-3 Encoding
Line Bit Clock at the Baud Rate
18
19
20
21
22
MLT transmission - Data patterns
23 24
AMD
A problem occurs when same set of bytes are repeated over the cable
Data to be Transmitted (After 4B/5B Encoding and Scrambling)
NRZI Waveform
1
1
1
1
1
0
0
1
1
1
0
1
0
0
1
0
1
0
0
1
1
1
1
Results in a repetitive waveform with distinct frequency components
(resulting in interference)
0
AMD
Line to
Bitbe
Clock
at the Baud
Rate
Data
Transmitted
(After
4B/5B Encoding and Scrambling)
MLT-3 Waveform
11
12
13
4
1
5
1
6
0
70
81
91
10
1
11
0
12
1
13
0
140
AMD
151
160
171
180
190
Figures 7 and 8 show the typical eye patterns of the NRZI
signal recovered by the receiver (at RD+/–) after 10 and
NRZI
Waveform
sends scrambled NRZILine
data
to theat the Baud Rate
Bit Clock
100 meters Figure
of UTP-5,
respectively.of
InNRZI
both cases,
the jit-Line Signals
3. Waveforms
and MLT-3
levels. The ML6671 converts the
ter is held below 3.0 ns. Figure 9 shows the jitter at the
vel, MLT-3 code. In MLT-3
coding,
1
2
3
4
5
6
7
8
9
10 11 12 13 14 15 16 17 18 19
PHY/PMD interface plotted as a function of cable length.
d by transitions and zeros are repreMLT-3
Waveform
ansitions. The transitions
areWaveform
always 10.0 dBm
NRZI
nt levels.
50 mV/Div
201
211
221
111111 = results in power concentrated at 31.25 MHz, 52.5 MHz, etc
231 240
18258A-3
20
21
22
23
24
... clearly the spectrum is a function of the payload data!
Power
0 dBm
set to 2 V peak-to-peak by placing a
18258A-3
-10 dBm
n pins 17 and 18 of the ML6671. The
MLT-3 Waveform
Figure 3. Waveforms of NRZI and MLT-3 Line Signals
acent levels (10% to 90%)
out of the
-20 dBm
n 1.0 ns. A low pass filter on the
-30 dBm
he rise time to 3.0 ns, prior to launche cable. A fast rise time maintains a 10.0 dBm
18258A-3
-40 dBm
ut it also creates unnecessary overFigure 3. Waveforms of NRZI and MLT-3 Line Signals
0 dBm
an develop when the signal encoun-50 dBm
cks in the wiring closet and cable -10 dBm
-60 dBm
ns rise time has been found empiri10.0 dBm
ns/Div
18258A-6
m value for the application. The Fil- 2-20
-70
dBm
le also provides AC Coupling, -300 Figure
Eye
the Transmitter
25
40 Pattern
55 of 70
85
100
115
130
145
160
dBm 106. MLT-3
reduces radiated emissions by proFrequency – MHz
150
mV/Div
-40 dBm
-10
e Filtering. In the transmit channel, it
18258A-4
t the transformer center tap be AC -20
-50 dBm Figure 4. Typical MLT-3 Spectrum at the Transmitter Output
or added Common Mode Filtering.
-60 dBm
MLT-3 eye pattern at the transmitter -30
esistive load. The output jitter of the -40
-70 dBm
Adaptive Equalization
TP-PMD Circuit
y less than 2.5 ns.
10
25
40
55
70
85
100
115
130
145
160
Adaptive equalization
is necessary to compensate forFrequency
the The
copper solution described in this application note has
-50 dBm
– MHz
cable attenuation and phase distortion that is encoun- been based on three functional
blocks: AMD’s
18258A-4
-60 dBm
®
2 PHYOutput
(Am79C864A PLC-S, Am79865
tered
at various lengths
of
STP and
UTP cable.
STP
ca- SUPERNET
onsists of a differential
Equalization
Figure
4. Typical
MLT-3
Spectrum
at the Transmitter
PDT and Am79866A PDR), Micro Linear’s MLT-3 Transble hastoaNRZI
characteristic
-70 dBmimpedance of 150 Ω. 100 meters
ect Circuitry and an MLT-3
25
40
55 12 dB
70(a
85
100
115 and 130
145
160
ceiver
(ML6671)
Pulse Engineering’s
Filter/Magnetic
of this
cable
will attenuate10
a transmitted
signal by
signal is AC coupled from
the
media
Module
(PE68502). An application circuit of the TP-PMD
factorTwo
of 4)50atΩ62.52MHz.
Frequency
– MHz
ns/Div100 meters of UTP-5 cable, such
18258A-7
r in the PE68502 module.
Adaptive
Equalization
TP-PMD
Circuit
is Receiver,
shown in Figure 5. This is a UTP-5
implementation utilasCMREF
AT&T 1061
(ZO =Figure
100 Ω),7.attenuates
signalOut
by 18
18258A-4
NRZI Eye the
Pattern
of the
and 3 of the PE68502 to
(pin
Adaptive
equalization
is necessary
to compensate
for
the
copper
solution
described
in this
application
note
izing
an RJ-45
connector
at the
media
interface.
A has
13-pin
dB at 62.5
MHz. Should
the
channel
be equalized
for
the The
Meters
UTP-5
Cable
Figure
4.10Typical
MLT-3
Spectrum
at the
Transmitter
Output
re part of the cable termination
and
cable
attenuation
and
phase
distortion
that
encoun- been
basedis on
three
connection
shown
at thefunctional
PHY-PMDblocks:
interfaceAMD’s
which is
maximum
length
of
either
cable,
it would
be isover-equalthe receive amplifier tered
input.atPin
4
of lengths
®
2 PHY
(Am79C864A
PLC-S,
Am79865
various
of STP
and UTP cable.
STPOverca- SUPERNET
150 mV/Div
pin
compatible
with
the
footprint
of
the
Sumitomo
ODL.
A
ized
for
the
shorter
and
intermediate
lengths.
so be connected to CMREF.
with
and
Am79866A
PDR),
Transble
has As
a characteristic
impedance
of 150
Ω. 100
meters
9- or
22-pin
footprint
couldMicro
also Linear’s
be used MLT-3
for compatibility
equalization
results in
excessive
signal
jitter.
With PDT
Adaptive
Equalization
TP-PMD
Circuit
AC coupling the center
tap
4)will
of attenuate a transmitted signal by 12 dB (a ceiver
and Pulse
Engineering’s
Filter/Magnetic
of
this (pin
cable
other common
ODL
configurations
from AT&T,
adaptive
equalization,
the receiver frequency response is with (ML6671)
module to ground improves
common
(PE68502).
application
circuit
of the TP-PMD
factor
of 4)
at
metersto
of
UTP-5
such
Adaptive
equalization
is 100
necessary
for
theto Module
The
copper
solution
described
in this
application
note has
Siemens
and
HP. An
optimized
for62.5
anyMHz.
given
segment
ofcompensate
cable.cable,
In order
the channel and reduces
noise
shownbased
in Figure
is a functional
UTP-5 implementation
utilas
AT&T
1061the
(ZO and
= 100
Ω), attenuates
the
signal
byby
18 a isbeen
cable
attenuation
phase
that
is encounon5. This
three
blocks: AMD’s
achieve
this,
equalizer
isdistortion
constantly
adjusted
dB at at
62.5
MHz. Should the channel be equalized for the izing an RJ-45® connector at the media interface. A 13-pin
tered
various
feedback
loop. lengths of STP and UTP cable. STP ca- SUPERNET 2 PHY (Am79C864A PLC-S, Am79865
is shown atPDR),
the PHY-PMD
interface
which
is
maximum
length of either
cable, it would
PDT and Am79866A
Micro Linear’s
MLT-3
Transble
has a characteristic
impedance
of 150be
Ω.over-equal100 meters connection
y implementations ofized
MLT-3
overshorter waveform
A for
repetitive
causes
distinct
frequency
components
compatible
with
thePulse
footprint
of the Sumitomo
ODL. A
thewill
anda transmitted
intermediate
lengths.
ceiver
(ML6671)
and
Engineering’s
Filter/Magnetic
of this
cable
attenuate
signal
by 12OverdB (a pin
alization cannot be optimized
for allresults in excessive signal jitter. With 9- or 22-pin footprint could also be used for compatibility
equalization
factor
of 4) at 62.5
MHz. 100 meters of UTP-5 cable, such Module (PE68502). An application circuit of the TP-PMD
stances and cable adaptive
performance.
other
ODL
from AT&T,
theΩ),
receiver
frequency
response
is with
Implementing
FDDI
Over
The
ANSI
X3T9.5
Standard
is shown
in common
Figure
5. This
isconfigurations
a UTP-5 implementation
as AT&T equalization,
1061 (ZO = 100
attenuates
the
signal
byCopper;
18
The
exceed
the
permitted
density
allowed
for the cable util-3
n changes the receiver
gain
andpeaks
fre-any given
Siemens
and HP.
optimized
for
segment
of be
cable.
In order
topower
izing an RJ-45
connector at the media interface. A 13-pin
dB
at 62.5 MHz.
Should the
channel
equalized
for the
a function of the received
signal.
Thethe of
achieve
this,
equalizer
is constantly
adjusted
by a connection is shown at the PHY-PMD interface which is
maximum
length
either cable,
it would be
over-equalas a dynamic range ized
of 20:1,
fromshorter
2 ns/Div
18258A-8 with the footprint of the Sumitomo ODL. A
feedback
loop.
compatible
for the
and intermediate
lengths.cables
Over- pin
Causes
interference
to other
and
equipment!
The equalizer boosts
the
high fre-results
Figure
8. NRZI Eye
Pattern
of the
Receiver,
9- or
22-pin footprint could also be used for compatibility
equalization
in excessive
signal
jitter. Out
With
Metersresponse
UTP-5 Cable
e signal in order to compensate
for
adaptive equalization,
the receiver100
frequency
is with other common ODL configurations from AT&T,
distortion. Equalization
is
adaptive
The spectrum
must of
not
be Ina
function
of ANSI
the
payload
data!
andX3T9.5
HP. Standard
optimized
for any given Implementing
segment
cable.
order
to Siemens
3
FDDI
Over
Copper;
The
compensate for lengths
of UTP-5
achieve
this, the equalizer is constantly adjusted by a
meters.
feedback loop.
+1
0
-1
10101 = results in power concentrated at 16.13 MHz, 31.25 MHz, etc
Power
IDEAL
Eye Diagram
Max Power
11111 encoded
MLT-3
2ns/Division
63 MHz
Frequency
Frequency
< 1 bit >
MLT transmission - Interference
Power
Effect of repetition
Power
IDEAL
without scrambler
Implementing
Over Copper; The ANSI X3T9.5 Standard
Max FDDI
Power
MLT-3
Implementing FDDI Over Copper; The ANSI X3T9.5 Standard
63 MHz
Frequency
5
3
MLT transmission - Scrambler
Scrambling is needed to ensure a smooth spectral response
A scrambler changes the output in some determistic way, that may be
restored at the receiver prior to decoding.
Data appears random to the MLT-3 encoded, and power is ideally
spread rather than focussed at particular frequencies.
The data is restored at the received by inverting scrambling function.
Power
Effect of repetition Power
without scrambler
with scrambler
MLT-3
63 MHz
Frequency
MLT-3
MLT-3
63 MHz
Frequency
63 MHz
Frequency
NRZI Waveform
MLT-3 Waveform
100BT Transmission
100BT Transmission Power Spectrum
18258A-
Figure 3. Waveforms of NRZI and MLT-3 Line Signals
byte
10.0 dBm
125 Mbps
4b/5b
125 Mbps
Scrambler
31.2 MHz
MLT-3
4 bits (1/2 byte) processed at a time
4 bits encoded to 5 bits
≤3 bits changed in 5 bits
Scrambled
Bits randomised to disperse energy
0 dBm
-10 dBm
1/100th power
of 10 MHz signal
-20 dBm
-30 dBm
-40 dBm
-50 dBm
-60 dBm
-70 dBm
10
25
40
55
70
85
100
115
130
145
160
Frequency – MHz
18258A-4
Log
power
plot Spectrum
v frequency
using
scrambler
Figure 4.
Typical
MLT-3
at the
Transmitter
Output
MLT-3 encoded (3 signal levels)
100B-FX Transmission
byte
125 Mbps
4b/5b
125 MHz
NRZ
Adaptive Equalization
TP-PMD Circuit
Adaptive equalization is necessary to compensate for the
cable attenuation and phase distortion that is encountered at various lengths of STP and UTP cable. STP cable has a characteristic impedance of 150 Ω. 100 meters
of this cable will attenuate a transmitted signal by 12 dB (a
factor of 4) at 62.5 MHz. 100 meters of UTP-5 cable, such
as AT&T 1061 (ZO = 100 Ω), attenuates the signal by 18
dB at 62.5 MHz. Should the channel be equalized for the
maximum length of either cable, it would be over-equalized for the shorter and intermediate lengths. Overequalization results in excessive signal jitter. With
adaptive equalization, the receiver frequency response is
optimized for any given10
segment
Mbps of cable. In order to
achieve this, the equalizer is constantly adjusted by a
100 Mbps
feedback loop.
The copper solution described in this application note h
been based on three functional blocks: AMD
SUPERNET® 2 PHY (Am79C864A PLC-S, Am7986
PDT and Am79866A PDR), Micro Linear’s MLT-3 Tran
ceiver (ML6671) and Pulse Engineering’s Filter/Magne
Module (PE68502). An application circuit of the TP-PM
is shown in Figure 5. This is a UTP-5 implementation u
izing an RJ-45 connector at the media interface. A 13-p
connection is shown at the PHY-PMD interface which
pin compatible with the footprint of the Sumitomo ODL.
9- or 22-pin footprint could also be used for compatibil
with otherCollision
common ODL
configurations from AT&
Domains
Siemens and HP.
10/100
10/100
Switch
Implementing FDDI
Over Copper; The ANSI
X3T9.5 Standard
10/100
Switch
10/100 ES
Switch
10
Hub
4 bits (1/2 byte) processed at a time
10 ES
4 bits encoded to 5 bits
10 Printer
NRZ encoded (2 signal levels)
Broadcast Domain
10/100 ES
Collision Domain
Bandwidth of the fibre is not a limiting function
GBE Transmission
Faster Ethernet
byte
1 Gigabit Ethernet
10 Gigabit Ethernet
8b/10b
Scrambler
PHY
8 bits (1 byte) processed at a time
8 bits encoded to 10 bits (constant disparity)
Each value contains 5 ones or 5 zeros
Scrambled
Bits randomised to disperse energy
Transmitted using the PHY (e.g. over Fibre)
Bit
1000BT PAM-5 Transmission
Gigabit Ethernet
Standardised by IEEE 802 Committee
2 streams at ~250 M pulse/sec
Line signal
Physical layer changed
0
125 MHz
2 streams at ~500 Mbps
+2
PAM-5
Copper
! 1 Gbps Fibre & UTP (100m CAT-5e)
! 8b/10b+Scrambler+PAM-5+2 channels
-1
125 MHz
Scrambler
+1
-2
PAM-5
Link layer allows sending bursts of frames with upto 8192 B
Bit time 0.001 µS
Small frames VERY inefficient
64B frame => (64)/(512+12) = 12% efficiency
Groups of 3 bits mapped to the PAM-5 signal
Mapping of data to levels is complex,
designed to optimise immunity to noise
Uses all four pairs to reach 125 MHz limit of CAT-5e
1 Gigabit over Fibre
10 Gbps over Fibre
Two sets of versions
! LAN & WAN versions share a common “transceiver” slot
Various fibre physical “sublayers” have been defined
One standard interface
! LAN & WAN versions share a common “transceiver” slot
64b/66b encoding (10GBASE-X uses 8b/10b)
0
1 Gbps Fibre - GBICs
!Multimode Fibre (LAN)
5km! !
(short haul) SX
10GBASE-E
! SInglemode Fibre (WAN)
70km! ! (long haul) LX
! 300 km ! (with optical repeaters) LH
10GBASE-L4
20000
30000
40000
10GBASE-L
- performance increases, as does price!!
10 Gbps over copper
10 GBASE-CX4
802.3ak specifies 10 Gbps over copper
4 Pairs of twin-axial copper cable - upto 15 m
IBX4 Connector
10000
10GBASE-S
Single Mode
Multimode
OM3 Multimode
Category 6/6a Cabling
Thicker wires that are much more tightly twisted
Better cable insulation
CAT-6
250 MHz bandwidth
Maximum length: 100m (Max 90m solid wire)
10BASE-GT limits length to 55m
CAT-6a
500 MHz bandwidth
Maximum length 100m (Max 90m solid wire)
10BASE-GT limits length to 100m
Results in a much thicker cable
Current cost x10 for CAT-5e
UTP Cable
CAT-7 STP
(1 GHz)
500 MHz
CAT-6a
• 10BASE-GT
Cat 6e
400 MHz
300 MHz
CAT-6
200 MHz
100 MHz
CAT-5e
GBE
FE
CAT-5
CAT-4
Telephony/ADSL/10BT
30 MHz
Evolution of the Ethernet Specification
Time
10Mbps
100Mbps
1000 Mbps
Cable
Fibre
UTP
Coax
Encoding
Manc
(4b/5b)
(8b/10b)
(64b/66b)
Format
2 level
(20 MHz)
3 levels
(31 MHz)
5 level
(125 MHz)
16 levels
(250/500
MHz)
Mode
HDX
HDX/FDX
FDX
FDX
Hubs on
longest path
4
0
0
0
Fibre
Fibre
Fibre
UTP (CAT-5) UTP (CAT5e) CAT6/special
(1 or 2 in std !!)
Wireless Ethernet
Summary of GBE
Gorry Fairhurst (c) 2003
New Physical Layer technology
Challenges: Bandwidth, Interference
Fast Ethernet : 4b/5b+MLT-3 (over CAT-5/CAT-5e/Fibre)
GBE: 8b/10b+PAM-5 (over CAT-5 /CAT-5e/Fibre)
10GBE: 64/66b (over CAT-6/Fibre/CX-4)
1 GHz CAT-7 Screened cable
Switches & Hubs
Packet rate becomes major challenge
New rules for fast Ethernet Hubs, but rarely used
Hubs rarely supported in FE and GB Ethernet
Next steps...
40 Gbps... was standardised 2010 (over Fibre)
First 100 Gbps Philadelphia, 2008.
100 Gbps... variant of above (over Fibre)
Many variants being designed/built
1 Tb/s in research labs
Ethernet continues to evolve
802.11 Success
WiFi deployment
!
~500,000 Hotspots in 144 countries!
!
1,000,000,000 chipsets since 2000
Wire-less physical layer
No cable
Standardised by IEEE 802.11 Committee
Wireless LAN - Infrastructure Mode
Infrastructuture mode
! ! Users connect to an access point
! ! Roaming between access points
! ! Access points connected via cable
Speeds
!
Initial 11 Mbps
!
Grew to 300 Mbps in a decade
Since 2011, looking at 1 Gbps at short distances ~ 10m
(rate reduces with distance at 100m or so, only 11 Mbps)
Variety of uses
! Trains, airplanes, parking meters, lamp posts, garden sprinklers.
Consumer electronics, smartphones, tablets, game consoles,
TVs, ipads, etc.
10 000 Mbps
Access point
Access point
Access point
Frequency Channel Re-use
Radio Link
2.4-2.485 GHz Industrial Science & Medicine (ISM) Band
!
14 channels available worldwide
!
(fewer channels available in some countries)
Only 3 non-overlapping 20 MHz channels
Uses spread spectrum channels
! First used by military ~ 50 years ago
! Very high immunity to noise
RF Power
! 802.11b! ! ! !
! Mobile Phone ! !
! CB Radio !! !
! Microwave Radio
The ISM frequency band allows several WiFi channels
! All systems using an access point use the same channel
This forms a logical network
Y
X
A
B
100m
100mW
600 mW
5W
!2W
!!!
P
Y
X
5.15-5.825 GHz Band also used for 802.11n (3 channels)
B
A
Base Stations and Beacon Frame
Can be interference
from adjacent
networks!
Wireless (802.11)
How do you know which network you are using?
! The WiFi access point sends periodic beacon frames
! ! can also identify the network (ssid)
A
A
AP
Each wireless node has a range
A is an end system; AP is a an access point
AP
WiFi basestation
! A needs to be able to receive signal from AP
(and AP from A)
!
The WiFi access point forms the logical centre of the network
When A sends to AP it can first sense the medium
(i.e. check if any system is sending)
Wireless (802.11)
A
Hidden Node Problem
AP
A and AP can no longer communicate (interference)
A
AP
C
Some nodes may not be able to “see” other transmissions
! e.g.C does not know if A is sending
C may try to send to AP (causing a collision)
A
AP
A and AP can no longer communicate (signal strength)
Note 1: Wireless propagation can be very variable!
Note 2: By definition AP sees signal from all nodes using AP
Virtual Carrier Detect
CSMA/CA
WiFi uses CSMA with Collision Avoidance
Three important changes:
A
AP
1. A sender attempts to avoid causing a collision
C
! C first sends a Clear To Send frame to ask if it can transmit
! ! - received by all nodes in range (i.e. Pink)
2. A sender cannot monitor the wireless medium
Receivers acknowledge (after a short delay) if they receive a frame.
If no ACK is received within a timeout, the sender backs-off (as in
CSMA/CD). Backoff increases for 5-7 attempts
! AP responds with an Ready To Send frame
! ! - received by all nodes in range (i.e. Pink & Yellow)
! ! both now know the “channel is in use”
3. A procedure known as CTS/RTS is used to detect hidden nodes.
! When Ready To Send is not received
! ! sender must defer (“back-off”) before repeating Clear To Send
Hidden Node Problem and CTS/RTS
AP
C
CTS
A
RTS
media
busy
RTS
Data from C
transmission
starts
Roaming
Several access points (APs) may be part of a LAN
! APs connected via cabled LAN
! Can also use built-in modem (some cases)
Roaming between access points
! Each AP sends a “beacon” signal to all nodes (SSID)
! Nodes can select the AP with best “beacon” signal
! Wireless nodes keep the same MAC address
! ! - users do not need to know the AP has changed
time
Access Point
Access Point
Note: If C needs to talk to A, it would rely on AP to relay (or repeat)
the signal so that A can receive it.
More details ... in case you wish to do it for real...
802.11n Radio Link
5 GHz Band
!
Band
Power Europe
50 mW
200 mW
5.25-5.35 GHz
250 mW
200 mW
5.75-5.85 GHz
1W
4W
5.47-5.725 GHz
I’m not going to ask this in the exam...
but will be doing projects over the summer involving this:-)
Power US
5.15- 5.25 GHz
1W
WiFi Antenna
Directional WiFi Antenna`
5 dBi
H
2m
1m
1
Signal
3m
1/4
Signal
V
5 dBi
32 deg
1/9
Signal
7 dBi
24 deg
Counting in dB
! 3 dB = x2
! 6 dB = x4
! 10 dB = x10
! 20 dB = x100
+2dB (x1.5)
Point-to-Point Wireless Bridge
“Patch” WiFi Antenna
H
V
14 dBi
30 deg
Connects two LANs
+9dB (x8)
Typically <100m
24 dBi
3 deg
km (or more) with directional antennae
Reaches the parts of networks
! wires can’t reach
+19dB (x80)
Summary
“Grid” WiFi Antenna
30 dBi
5 deg
Wireless uses half-duplex
+26dB
(x400)
Beacon frame used to “form” a network
5m
antenna
CSMA/CD
doesn’t work when sender don’t see all the systems!
+52dB
(x160000)
160 km!
Actually it’s a bit more complicatd
AND, regulations on allowed power and antenna position!!
Needs to be updated slightly - CSMA/CA
Various modes ... lots of things we could talk about
802.11 Frame Format
Wireless LAN - Ad Hoc
4 addresses*:
! Ad Hoc mode (peer-to-peer)
! ! Maximum of 8 users
! ! No access point
Addr 1 Wireless Receiver
Addr 2 Wireless Transmitter
Addr 3 Dst Mac
Addr 4 Src Mac
Pre Frame Frame Addr Addr Addr Seq Addr
Payload CRC
amble Control Duration 1
2
3 Cont 4
* Address usage depends on frame control header
Network Evolution
Security
Threats
! Evesdropping (easy to listen in)
! Intentional theft of data
! Hacking
! Encryption helps! ....
4 Stages of Evolution:
!
!
!
!
Top security mistakes
! Access point setup inside firewall
! Default encryption keys used
! No encryption used
!
Solutions
! Use encryption
! Control access by MAC address (filter table)
! Control access by user (login,802.1x)
1. Shared LAN (1 Collision Domain)
2. Separate LANs (>1 Collision Domain)
3. Switched LANs
4. Managed/Virtual Switched LANs
Enterprise Stage 1
Enterprise Stage 2
Stage 2
Server
Server
Hub /
Repeater
Hub /
Repeater
Each workgroup has own server
All connected via backbone
to form one network
(10B5 or 10BF with repeaters)
Server
Bridge
Each workgroup has own server
Most traffic only local
Server
Bridge
Server
Bridge
LANs connected via backbone
(typically 10B5 or 10BF)
Repeaters / Hubs isolate faults
Server
Hub /
Repeater
Auto-negotiation
10BT
use 10
100BT
use 100
10BT
use 10
No auto-negotiation for 100 FX!
10BT
10BF
100BT
100BFX
100BT
10BF
Most 100BT NICs also include an embedded 10BT NIC
Auto- negotiation allows systems to find the lowest interoperable physical layer (including whether to use CSMA/CD)
10BF
Fibre
100BFX
Fibre
Fibre
X
100BFX
No inter-operability of 100 BT and 100B-FX.
Enterprise Stage 3
Stage 3
Enterprise Stage 4
Hub /
Repeater
Hubs confined to work groups (L1)
Centralised server location
Hub /
Repeater
High-speed switches 10/100/1000 (L2)
Mixture of switched and shared
networks
Managed switches at “core” 1000 (L2)
High speed backbones
(e.g. 100TX, 100FX, 1000BF)
“Virtual” LANs
Switch
Server
Server
Wireless Access Points (L2)
Routers to Internet (L3)
Server
Router connections at 10/100/1000/10000
Switch
+ 2-Port Gigabit Switch with Webview and Power over Ethernet
N, enter the VLAN ID and VLAN name, up to 32 characters long. Mark the Enable checkbox to
N, and click Create VLAN.
Tagged Ethernet Frames
select a VLAN ID and click the Edit icon (which resembles a pen). Modify the VLAN name and
Ethernet
d. Select the Tagged
membership
typeFrames
by marking the appropriate radio button in the list of ports or lags.
VLANs
Each port is in one of 3 modes:
IEEE 802.1pQ Tag comprises:
Priority Field (3-bit)
None
VLAN cannot use this port
ype. Select VLAN membership for each interface by marking the appropriate radio button for a
CR
VLAN-ID
Tagged
All packets sent tagged
Interface is a member of the VLAN. All packets transmitted by the port will be tagged,
that is,
Untagged
ag and therefore carry VLAN or CoS information.
Packets sent untagged
d. Interface is a member of the VLAN. All packets transmitted by the port will be untagged, that is,
y a tag and therefore not carry VLAN or CoS information. Note that an interface must be assigned
st one group as an untagged port.
terface is not a member of the VLAN. Packets associated with this VLAN will not be transmitted by
face.
!
Figure 5-16: Adding/Editing VLAN
Repeaters, Bridges and Routers
Checking your understanding...
Application Programs
Layer 7 !(Application)
To other
LAN & WAN
networks
Layer 6 !(Presentation)
Layer 5 !(Session)
To other
LAN segments
Layer 4 !(Transport)
Layer 3 !(Network)
Layer 2 !(Link)
TCP
Layer 1 !(Physical)
IP
Layer 0 !(Cabling)
MAC
To other
LAN segments
MAU
Router
Bridge
MAC
Two key performance measures:
MAU
MAU
Throughput
Repeater
Utilisation
Example 1
Example 1
Calculate the maximum frame rate of a node on a 10 Mbps Ethernet
LAN.
Frame Part
Calculate the maximum frame rate of a node on an Ethernet LAN.
Frame Part
Minimum Size Frame
Minimum Size Frame
Inter Frame Gap (9.6µs)
Inter Frame Gap (9.6µs)
MAC Preamble (+ SFD)
MAC Preamble (+ SFD)
MAC Destination Address
MAC Destination Address
MAC Source Address
MAC Source Address
MAC Type (or Length)
MAC Type (or Length)
Payload (Network PDU)
Payload (Network PDU)
Check Sequence (CRC)
Check Sequence (CRC)
Total Frame Physical Size
Total Frame Physical Size
Example 2
Throughput
Calculate maximum throughput of link service provided by 10 Mbps Ethernet
Frame Part
Inter Frame Gap (9.6µs)
MAC Preamble (+ SFD)
MAC Destination Address
Defined as “the number of bits transferred per second
from a given layer to the upper layer as a result of a
conversation between two users of the layer”
Considers only data forwarded (i.e. not overhead)
Expressed in bits per second
MAC Source Address
MAC Type (or Length)
Payload (Network PDU)
Check Sequence (CRC)
Total Frame Physical Size
Maximum Size Frame
Transmission rate (e.g. 10, 100, ... Mbps)
Example 3
Utilisation
One node transmits 100 B frames at 10 frames per second,
another transmits 1000 B frames at 2 frames per second,
calculate the utilisation of a 10 Mbps Ethernet LAN.
Unused capacity
Frame Part
Utilised capacity
Inter Frame Gap (9.6µs)
Defined as “the total number of bits transferred at the
physical layer to communicate a certain amount of data
divided by the time taken to communicate the data.”
MAC Preamble (+ SFD)
MAC Destination Address
MAC Source Address
Includes all bits in all types of frame irrespective of whether
they are corrupted or correctly received.
MAC Type (or Length)
Expressed as a percentage of transmission rate.
Check Sequence (CRC)
Measures link capacity used
Total Frame Physical Size
Over to you....
• Spend one session reviewing material on web.
• Answers to examples are at:
• ./lan-pages/enet-calc.html
• Finally, do the revision questions....
• ./questions/intro/index.html
Payload (Network PDU)
Minimum Size Frame