Chapter 9: Subnetting
IP Networks
Introduction to Networking
9.0
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
1
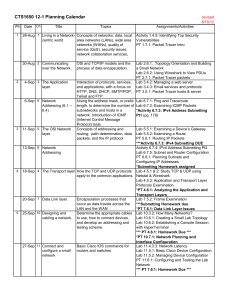
Chapter 9
9.1 Subnetting an IPv4 Network
9.2 Addressing Schemes
9.3 Design Considerations for IPv6
9.4 Summary
9.0
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
2
Chapter 9: Objectives
Explain why routing is necessary for hosts on different
networks to communicate.
Describe IP as a communication protocol used to identify a
single device on a network.
Given a network and a subnet mask, calculate the number of
host addresses available.
Calculate the necessary subnet mask in order to
accommodate the requirements of a network.
Describe the benefits of variable length subnet masking
(VLSM)
Explain how IPv6 address assignments are implemented in a
business network.
9.0.1.1
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
3
Introduction
Subletting IP Networks
Consider doing class activity
9.0.1.2 Activity - Call Me
9.0.1.2
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
4
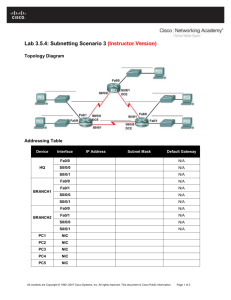
Network Segmentation
Reasons for Subnetting
Large networks need to be segmented into smaller sub-networks,
creating smaller groups of devices and services in order to:
Control traffic by containing broadcast traffic within subnetwork
Reduce overall network traffic and improve network performance
Subnetting - process of segmenting a network into multiple smaller
network spaces called subnetworks or Subnets.
Communication Between Subnets
A router is necessary for devices on different networks and subnets
to communicate.
Each router interface must have an IPv4 host address that belongs to
the network or subnet that the router interface is connected to.
Devices on a network and subnet use the router interface attached to
their LAN as their default gateway.
9.1.1.1
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
5
Why Subnet Networks
Communication Between Subnets
To determine if
traffic is local or
remote, the router
uses the subnet
mask.
Each subnet is
treated as a
separate network
space.
Devices on the same subnet
must use an address, subnet
mask, and default gateway
9.1.1.2
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
6
Subnetting an IPv4 Network
IP Subnetting is FUNdamental
9.1.2.1
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
7
Subnetting an IPv4 Network
The Plan – Address Assignment
255.0.0.0
8 network bit, 24 host bits
• 2^24 = 16,777,216 possible hosts
255.255.0.0
16 network bit, 16 host bits
• 2^24 = 65,536 possible hosts
255.255.255.0
24 network bit, 8 host bits
• 2^8 = 256 possible hosts
Problem: Our Public IP address is 165.15.0.0/16
We have one network that can hold 65,535 hosts!
We need many networks, not one huge one!
9.1.2.2
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
8
Subnetting an IPv4 Network
Basic Subnetting
Borrowing Bits to Create Subnets
Borrowing 1 bit 21 = 2 subnets
Do the buttons on 9.1.3.1
Borrowing 1 Bit from the host portion creates 2 subnets with the same subnet mask
Subnet 0
Subnet 1
Network 192.168.1.0-127/25
Network 192.168.1.128-255/25
Mask: 255.255.255.128
Mask: 255.255.255.128
9.1.3.1
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
9
Subnetting an IPv4 Network
Subnets in Use
Subnet 0
Network 192.168.1.0-127/25
Subnet 1
Network 192.168.1.128-255/25
Do the buttons on 9.1.3.2
9.1.3.2
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
10
Subnetting an IPv4 Network
Subnetting Formulas
Calculate Number of Subnets
Calculate Number of Hosts
Do the buttons on 9.1.3.3
9.1.3.3
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
11
Subnetting an IPv4 Network
Creating 4 Subnets
Borrowing 2 bits to create 4 subnets. 22 = 4 subnets
9.1.3.4
Presentation_ID
Do the buttons on 9.1.3.4
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
12
Subnetting an IPv4 Network
Creating 8 Subnets
Borrowing 3 bits to Create 8 Subnets. 23 = 8 subnets
9.1.3.5
Presentation_ID
Do the buttons on 9.1.3.5
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
13
Subnetting an IPv4 Network
Creating 8 Subnets(continued)
9.1.3.5
Presentation_ID
Do the buttons on 9.1.3.5
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
14
Subnetting an IPv4 Network
Creating 8 Subnets(continued)
9.1.3.5
Presentation_ID
Do the buttons on 9.1.3.5
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
15
Subnetting an IPv4 Network
Creating 8 Subnets(continued)
Do the buttons on
9.1.3.5
9.1.3.5
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
16
Subnetting an IPv4 Network
9.1.3.6 Activity - Determining the Network Address – Basic
9.1.3.7 Activity - Calculate the Number of Hosts – Basic
9.1.3.8 Activity - Determining the Valid Addresses for Hosts – Basics
9.1.3.9 Activity - Calculate the Subnet Mask
9.1.3.6
Presentation_ID
Do Activities 9.1.3.6, 9.1.3.7, 9.1.3.8 and 9.1.3.9 in class
Students should practice this until mastery.
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
17
Subnetting an IPv4 Network
Creating 100 Subnets with a /16 prefix
• In situations where
more hosts are
required, You must
borrow bits from the
3rd octet instead of
the 4th.
• In this example we
have 9 host bits for
510 hosts (2^9 -2)
9.1.3.10
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
18
Subnetting an IPv4 Network
9.1.3.11 Calculating the Hosts
9.1.3.11
Presentation_ID
Do the buttons on 9.1.3.11
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
19
Subnetting an IPv4 Network
9.1.3.12 Calculating the Hosts
9.1.3.12
Presentation_ID
Do the buttons on 9.1.3.12
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
20
Subnetting an IPv4 Network
9.1.3.13 Activity - Determining the Network Address – Advanced
9.1.3.14 Activity - Calculating the Number of Hosts – Advanced
9.1.3.15 Activity - Determining the Valid Addresses for Hosts - Advanced
9.1.3.13 – 9.1.3.15
Presentation_ID
Do activities 9.1.3.13, 14, 15 in class
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
21
Determining the Subnet Mask
Subnetting Based on Host Requirements
There are two considerations when planning subnets:
Number of Subnets required
Number of Host addresses required
Formula to determine number of useable hosts
2^n-2
2^n (where n is the number the number of host bits remaining) is
used to calculate the number of hosts
-2 Subnetwork ID and broadcast address cannot be used on each
subnet
9.1.4.1
Presentation_ID
Do animation on 9.1.4.1
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
22
Determining the Subnet Mask
Subnetting Network-Based Requirements
Calculate number of subnets
Formula 2^n (where n is the number of bits borrowed)
Subnet needed for
each department in
graphic
9.1.4.2
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
23
Determining the Subnet Mask
Subnetting To Meet Network Requirements
It is important to balance the number of subnets needed
and the number of hosts required for the largest subnet.
Design the addressing scheme to accommodate the
maximum number of hosts for each subnet.
Allow for growth in
each subnet.
Do the buttons on 9.1.4.3
9.1.4.3
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
24
Determining the Subnet Mask
Subnetting To Meet Network Requirements (cont)
9.1.4.4
Presentation_ID
Do the buttons on 9.1.4.4
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
25
Benefits of Variable Length Subnet Masking
Traditional Subnetting Wastes Addresses
Traditional subnetting - same number of addresses is
allocated for each subnet.
Subnets that require fewer addresses have unused
(wasted) addresses. For example, WAN links only need 2
addresses.
Variable Length Subnet Mask (VLSM) or subnetting a
subnet provides more efficient use of addresses.
9.1.4.4
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
26
Subnetting an IPv4 Network
9.1.4.5 Activity - Determining the Number of Bits to Borrow
9.1.4.5
Presentation_ID
Do activities 9.1.4.5
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
27
Benefits of Variable Length Subnet Masking
Variable Length Subnet Masks (VLSM)
VLSM allows a network space to be divided in unequal
parts.
Subnet mask will vary depending on how many bits have
been borrowed for a particular subnet.
Network is first subnetted, and then the subnets are
subnetted again.
Process repeated as necessary to create subnets of
various sizes.
9.1.5.1
Presentation_ID
Do buttons on 9.1.5.1
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
28
Benefits of Variable Length Subnet Masking
Basic VLSM
9.1.5.2
Presentation_ID
Do buttons on 9.1.5.2
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
29
Benefits of Variable Length Subnet Masking
Basic VLSM
9.1.5.3
Presentation_ID
Do buttons on 9.1.5.3
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
30
Benefits of Variable Length Subnet Masking
VLSM in Practice
Using VLSM subnets, the LAN and WAN segments in
example below can be addressed with minimum waste.
Each LANs will be assigned a subnet with /27 mask.
Each WAN link will be assigned a subnet with /30 mask.
9.1.5.4
Presentation_ID
Do buttons on 9.1.5.4
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
31
Benefits of Variable Length Subnet Masking
VLSM Chart
9.1.5.5
Presentation_ID
Do buttons on 9.1.5.5
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
32
Subnetting an IPv4 Network
9.1.5.6 Activity - Practicing VLSM
9.1.4.6
Presentation_ID
Do activities 9.1.4.6 in class
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
33
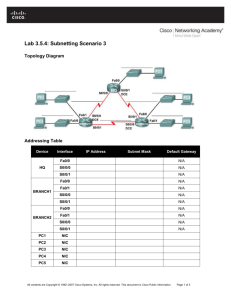
Structured Design
Planning to Address the Network
Allocation of network addresses should be planned and
documented for the purposes of:
Preventing duplication of addresses
Providing and controlling access
Monitoring security and performance
Addresses for Clients - usually dynamically assigned using
Dynamic Host Configuration Protocol (DHCP)
Sample Network
Addressing Plan
9.2.1.1
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
34
Subnetting an IPv6 Network
Subnetting Using the Subnet ID
An IPv6 Network Space is subnetted to support
hierarchical, logical design of the network
9.3.1.1
Presentation_ID
Do buttons on 9.3.1.1
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
35
Subnetting an IPv6 Network
IPV6 Subnet Allocation
9.3.1.2
Presentation_ID
Do buttons on 9.3.1.2
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
36
Subnetting an IPv6 Network
Subnetting into the Interface ID
IPv6 bits can be borrowed from the interface ID to create
additional IPv6 subnets
9.3.1.3
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
37
Chapter 9: Summary
Process of segmenting a network, by dividing it into to
multiple smaller network spaces, is called subnetting.
Subnetting a subnet, or using Variable Length Subnet
Mask (VLSM) was designed to avoid wasting addresses.
IPv6 address space is a huge address space so it is
subnetted to support the hierarchical, logical design of
the network not to conserve addresses.
Size, location, use, and access requirements are all
considerations in the address planning process.
IP networks need to be tested to verify connectivity and
operational performance.
9.4.1.1
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
38
Ta Da!
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
39