1 Refer to the exhibit. After configuring QoS, a network administrator
advertisement

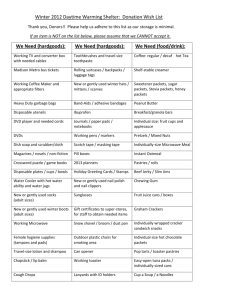
1 Refer to the exhibit. After configuring QoS, a network administrator issues the command show queueing interface s0/1. What two pieces of information can an administrator learn from the output of this command? (Choose two.) queue traffic definitions priority list protocol assignments type of queuing being implemented number of packets placed in each queue queuing defaults that have been changed queuing has not been applied to this interface 2 What design strategy should be followed when designing a network that uses video on demand? implement the appropriate routing protocol to ensure that data segments arrive in order implement different QoS queues based on the type of video traffic being distributed install servers to store the data in a centrally located server farm configure queuing in the core routers to ensure high availability 3 A company that has a traditional telephone system wants to convert to IP telephony. Which two factors should be considered for the design? (Choose two.) Digital communications systems have greater noise than analog systems when processing voice traffic. Voice-enabled routers or a server must be used for call control and signaling. Voice to IP conversions can cause router overhead. Power to the phones can be supplied through properly equipped patch panels or switches. The cost to combine voice and data VLANs can be a considerable amount. 4 Which two network applications are most affected by network congestion and delays? (Choose two.) IP telephony live video webcasts audio file downloads online banking services file archival and retrieval 5 two.) What two Cisco tools can be used to analyze network application traffic? (Choose NBAR NetFlow AutoQoS Wireshark Custom Queuing 6 A company is considering adding voice and video to the data networks. Which two statements are true if voice and video are added? (Choose two.) PoE switches must be purchased. More UDP-based traffic flows will be evident. Response times will be increased even if QoS is implemented. QoS will most likely be implemented to prioritize traffic flows. VPNs will most likely be implemented to protect the voice traffic. 7 A database server is configured to purge all data that is 60 days old. Ten data items that are 60 days old are to be purged. However, there is a failure halfway through the transaction, and the entire transaction is voided. What type of transaction action occurred? atomic consistent durable isolated 8 An analysis of network protocols reveals that RTP and RTCP are being used. What uses these protocols? IDS VPN WLAN firewall real-time video 9 In addition to the technical considerations, what other major factor is used to evaluate the success of a network installation? final project costs maintenance costs user satisfaction statistics describing the performance of network devices 10 two.) Which two statements are characteristics of file transfer traffic flows? (Choose RTP should be used. Traffic is predictable. Packets are small in size. Transfers are throughput intensive. Response-time requirements are low. 11 What are two characteristics of voice over IP traffic? (Choose two.) Voice packets tend to be small. Voice packets must be processed in real time. Voice packets can effectively use TCP reliability features. Voice traffic can survive packet drops and retransmission delays. Voice packets must be converted to analog before being sent across the IP network. Voice packets automatically receive a higher priority value than other types of packets. 12 Refer to the exhibit. Which option correctly matches the terms on top with its definition on the bottom? A=1, B=3, C=2, D=4 A=2, B=1, C=4, D=3 A=2, B=4, C=1, D=3 A=3, B=2, C=4, D=1 A=4, B=3, C=1, D=2 A=4, B=2, C=3, D=1 13 The design of an IP telephony system needs to meet the technical requirements to provide a connection to the PSTN as well as provide high-quality voice transmissions using the campus network. Which two elements directly affect the ability of the design to meet these requirements? (Choose two.) voice-enabled firewall PoE switches and patch panels redundant backbone connectivity voice-enabled router at the enterprise edge separate voice and data VLANs with QoS implemented 14 Several web and email servers have recently been installed as part of an enterprise network. The security administrator has been asked to provide a summary of security features that can be implemented to help prevent unauthorized traffic from being sent into or out of sensitive internal networks. Which three features should the security administrator recommend? (Choose three.) firewalls priority queuing access control lists intrusion detection systems DHCP 128-bit WEP 15 Which two items can be determined by diagramming internal traffic flow? (Choose two.) the type of ISP services needed the capabilities of end-user devices the areas where network congestion may occur the location of VPN servers used to connect teleworkers locations where high-bandwidth connections are required 16 What are two things that a network designer can do to determine current and anticipated network traffic flows? (Choose two.) Survey end users to obtain customer input. Upgrade the Cisco IOS software in all networking devices to optimize traffic flow. Limit the analysis to host-to-server traffic because host-to-host traffic is unimportant. Run a network traffic analysis to determine which applications are in use and by whom. Conduct an inventory of all networking devices that includes model numbers and memory configurations. 17 When implementing VoIP services, which two design considerations should be followed? (Choose two.) Confirm that network jitter is minimal. Use TCP to reduce delays and dropped packets. Establish priority queuing to ensure that large data packets are sent uninterrupted. Disable real-time protocols to reduce queuing strategy demands. Ensure that packet delays do not exceed 150 ms. 18 Which service can be provided by the NetFlow Cisco utility? network planning and mapping IDS and IPS capabilities peak usage times and traffic routing network billing and accounting application security and user account restrictions source and destination UDP port mapping 19 In network design, which technology can be implemented to prioritize traffic based on its importance and technical requirements? STP QoS RTP TCP VPN 20 When implementing QoS in traffic queues, what is the first step the designer should take to ensure that traffic is properly prioritized? define QoS policies define traffic classes determine traffic patterns identify traffic requirements identify networking equipment 21 Refer to the exhibit. If ACL 150 identifies only voice traffic from network 192.168.10.0/24 and no other traffic, which queue will voice traffic from other networks use? high normal medium default 22 switch. Which two traffic types are examples of external traffic flows? (Choose two.) A user in the IT department telnets to the core layer router. A user in marketing connects to the web server of a competitor. A user in the IT department telnets into the access layer switch. A user in the services department logs in to a web-based email program. A user in accounting connects to an FTP server that is connected to the access layer