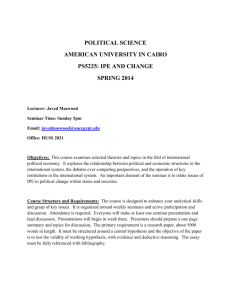
Critical Security Studies
advertisement

Critical Security Studies Paul Roe Course Description and Aims This course is concerned with how the so-called ‘critical turn’ in International Relations has been reflected specifically in thinking about Strategy and Security. ‘Critical Security Studies’ is, in its broadest sense, a collection of approaches all united by a profound dissatisfaction with so-called ‘traditional’ security studies. Critical Security Studies seeks to question, though not always completely do away with, the foundations upon which the dominant state-centrism and military-centrism is built. This course deals with a number of these approaches: from the ‘conventional’ constructivists, through the ‘Copenhagen’ and ‘Aberystwyth’, or ‘Welsh’, Schools, to more ‘critical’ constructivist positions. In doing so, not only does it seek to illuminate the main theoretical assumptions underpinning each of the various approaches, but also to explore just how they are ‘critical’; that is, in what ways they challenge traditional security studies, and in what ways they compare and contrast with each other. While the course is mainly theoretical in its orientation, much emphasis is also placed on empirical application; how, and to what kind of cases, each of the approaches can be profitably applied. Learning Outcomes This course is designed to produce the following main learning outcomes: The ability to recognize various ways in which the ‘critical turn’ in IR has impacted Security studies; The ability to reveal those assumptions that distinguish some critical positions from others; The ability to both recognize and formulate questions that structure and contribute to existing debates; The ability to evaluate the strengths and weaknesses of the application of (critical) theory to practice. Teaching Method For this course, there are no lectures. Instead, students will participate in seminars where they are expected to form their own opinions through ‘critical’ evaluation of the readings. Seminar discussion will be structured around a short presentation of the topic, in which students will (briefly) summarise and then critique the readings. For each seminar, there will be one key text (in the course reader). For the topics discussed there is not necessarily a right answer. What is important is to focus on the way in which people think. Method of Assessment Each student will be assessed through a combination of seminar contribution and written work. In terms of written work, two research papers (approximately 4,000 words) are required; one midterm and one end-term. The topics for the papers are of the students own choosing. For each of the two research papers 35% of the overall grade is allocated (total 70%). The remaining 30% is devoted to seminar attendance and contribution. Guidelines for Assessment The research paper is the most important element as part of the overall assessment. In terms of grading the term paper, the categories below provide some guidance as to what qualities assessors are looking for, and what kinds of weakness may incline assessors towards giving a lower mark. A Work of exceptional quality that authoritatively demonstrates knowledge and understanding of the topic. Well argued, organised, and structured. Critical awareness of the theoretical and/or empirical material, and shows originality of thought. A- Work of high quality that is well above the average for a postgraduate paper. Not necessarily faultless in terms of the above, but still shows some originality of thought. B+ A very competent piece of work displaying substantial knowledge and understanding. There may well be room for improvement in terms of organisation and structure, although in general terms the work is solid. B Again a piece of some competence. More improvement than the above will be required organisationally and structurally. Work at this level may also display some oversimplification and irrelevance. B- An adequate piece of work, but where significant improvements must be made. Too much oversimplification and irrelevance. Required points are missing. Work may also contain serious grammatical errors. C+ Inadequate. A work displaying far too many of the above weaknesses. F A totally unacceptable piece of work. Fail. Week 1/Seminar 1. Introduction This first seminar will act as a brief introductory class where the nature of the course is discussed, together with the expectations of both the professor and students. Here, initial oral presentations will be assigned. Week 1/Seminar 2. No Class While the class will not meet, this seminar serves as an opportunity for preparatory reading. For those students who attended ‘International Security Studies’ in the Fall Semester, this will mainly involve some re-engagement in the second part of that course. For those students who did not attend, some familiarization with the ‘critical turn’ in Security Studies can be made through a general engagement with the relevant literature. The following are just a brief, recommended selection: Suggested Reading: Terry Terriff, Stuart Croft, Lucy Jones, & Patrick M. Morgan, Security Studies Today (Cambridge: Polity Press, 1999). Alan Collins (ed.), Contemporary Security Studies (Oxford: OUP, 2007). Ken Booth & Nicholas J. Wheeler, The Security Dilemma: Fear, Cooperation, and Trust in World Politics (Basingstoke: Palgrave MacMillan, 2008). Keith Krause & Michael C. Williams (eds.), Critical Security Studies: Concepts and Cases (London: UCL Press, 1997). Barry Buzan & Lene Hansen, The Evolution of International Security Studies (Cambridge: CUP, 2009). Week 2/Seminar 3. Third Generation Strategic Culture: Institutional Culture Key Text: Jeffrey Legro, ‘Military Culture and Inadvertent Escalation in World War II’, International Security, vol.18, no.4, 1994. Week 2/Seminar 4. Third Generation Strategic Culture: Global Norms Key Text: Nina Tannenwald, ‘Stigmatizing the Bomb: Origins of the Nuclear Taboo’, International Security, vol.29, no.4, 2005. Further Reading for 2/3 & 2/4: Tannenwald, The Nuclear Taboo: The U.S. and the Non-Use of Weapons Since 1945 (Cambridge: CUP, 2007). Peter Katzenstein (ed.), The Culture of National Security (New York: Columbia University Press, 1996), Chapter 4: Richard Price & Tannenwald, ‘Norms and Deterrence: The Nuclear and Chemical Weapons Taboos’; Chapter 6: Elizabeth Kier, ‘Culture and French Military Doctrine Before World War II’; Chapter 7: Alistair Iain Johnston, ‘Cultural Realism and Strategy in Maoist China’. Theo Farrell & Helene Lambert, ‘Courting Controversy: International Law, National Norms and American Nuclear Use’, Review of International Studies, vol.27, no.3, 2001. Farrell, ‘Transnational Norms and Military Development: Constructing Ireland’s Professional Army’, European Journal of International Relations, vol.7, no.1, 2001. Farrell, ‘World Culture and Military Power’, Security Studies, vol.14, no.3, 2005. Emily Goldman, ‘Cultural Foundations of Military Diffusion’, Review of International Studies, vol.32, no.1, 2006. Edward Lock, ‘Refining Strategic Culture: Return of the Second Generation’, Review of International Studies, vol.36, no.3, 2010 Week 3/Seminar 5. Ontological Security: Culture and Identity as Self-Help Key Text: Brent Steele, ‘‘Ideals That Were Never Really in Our Possession: Torture, Honor and US Identity’, International Relations, vol.22, no.2, 2008. Further Reading: Steele, ‘Making Words Matter: The Asian Tsunami, Darfur, and “Reflexive Discourse” in International Politics’, International Studies Quarterly, vol.51, no.4 2007 Alexander Wendt, ‘The State as Person in International Theory’, Review of International Studies, vol.30, no.2, 2004. Jacob Schiff, ‘‘Real’? As if! Critical Reflections on State Personhood’, Review of International Studies, vol.34, no.3, 2008. Steele, Ontological Security in International Relations: Self-Identity and the IR State (London: Routledge, 2008), Chapter 2, ‘Identity, Morality, and Social Action’; Chapter 3, ‘The Possibilities as Self’. Ayse Zarakol, ‘Ontological (In)security and State Denial of Historical Crimes: Turkey and Japan’, International Relations, vol.24, no.1, 2010. Week 3/Seminar 6. Security and Contestation: Identity and Symbolic Power Key Text: Ronald Krebs & Jennifer Lobasz, ‘Fixing the Meaning of 9/11: Hegemony, Coercion and the Road to War in Iraq, Security Studies, vol.16, no.3, 2007. Further Reading: Krebs & Patrick Jackson, ‘Twisting Tongues and Twisting Arms: The Power of Political Rhetoric’, European Journal of International Relations, vol.13, no.1, 2007. Janice Bially Mattern, ‘The Power Politics of Identity’, European Journal of International Relations, vol.7, no.3, 2001. Jane Cramer, ‘Militarized Patriotisms: Why the U.S. Place of Ideas Failed Before the Iraq War’, Security Studies, vol.16, no.3, 2007. A. Trevor Thrall, ‘A Bear in the Woods? Threat Framing and the Market Place of Ideas’, Security Studies, vol.16, no.3, 2007. Jack Holland, ‘‘When You Think of the Taliban, Think of the Nazis’: Teaching Americans ‘9/11’ in NBC’s The West Wing’, Millennium, vol.40, no.1, 2011. Richard Jackson, Writing the War on Terrorism (Manchester: MUP, 2005). Michael Williams, Culture and Security: Symbolic Power and the Politics of International Security (London: Routledge, 2007). Week 4/Seminar 7. Second Generation Securitization Key Text: Thierry Balzacq, ‘The Three Faces of Securitization: Political Agency, Audience and Context’, European Journal of International Relations, vol.11, no.2, 2005. Further Reading: Balzacq, Securitization Theory: How Security Problems Emerge and Dissolve (London: Routledge, 2011). Matt McDonald, ‘Securitization and the Construction of Security’, European Journal of International Relations, vol.14, no.4, 2008. Holger Stritzel, ‘Towards a Theory of Securitization: Copenhagen and Beyond’, European Journal of International Relations, vol.13, no.3, 2007. Stritzel, ‘Security, the Translation’, Security Dialogue, vol.42, no.4-5, 2011. Paul Roe, ‘Actor, Audience(s) and Emergency Measures: Securitization and the UK’s Decision to Invade Iraq’, Security Dialogue, vol.39, no.6, 2008. Week 4/Seminar 8. Contextualising Securitization Key Text: Claire Wilkinson, ‘The Copenhagen School on Tour in Kyrgyzstan: Is Securitization Theory Useable Outside of Europe?’, Security Dialogue, vol.38, no.1, 2007. Further Reading: Juha Vuori, ‘Illocutionary Logic and Strands of Securitization: Applying the Theory of Securitization to the Study of Non-Democratic Political Orders’, European Journal of International Relations, vol.14, no.1, 2008. Monika Barthwal-Datta, ‘Securitising Threats Without the State: A Case Study of Misgovernance as a Security Threat in Bangladesh’, Review of International Studies, vol.35, no.2, 2009. Nicole Jackson, ‘International Organizations, Security Dichotomies and the Trafficking of Persons and Narcotics in Post-Soviet Central Asia: A Critique of the Securitization Framework’, Security Dialogue, vol.37, no.3, 2006. Pinar Bilgin, ‘Politics of Studying Securitization? Copenhagen School in Turkey’, Security Dialogue, vol.42, no.4-5, 2011. Maria Julia Trombetta, ‘Environmental Security and Climate Change: Analysing the Discourse’, Cambridge Review of International Affairs, vol.21, no.4, 2008. Shirley Scott, ‘Securitizing Climate Change: International Legal Implications and Obstacles’, Cambridge Review of International Affairs, vol.21, no.4, 2008. Hakan Seckinelgin, Joseph Bigirumwami, & Jill Morris, ‘Securitization of HIV/AIDS in Context: Gendered Vulnerability in Burundi’, Security Dialogue, vol.41, no.5, 2010. Felix Ciuta, ‘Security and the Problem: A Hermeneutical Critique of Securitisation Theory’, Review of International Studies, vol.35, no.2, 2009. Week 5.Seminar 9. The Ethics of Securitization Key Text: Stefan Elbe, ‘Should HIV/AIDS Be Securitized? The Ethical Dilemmas of Linking HIV/AIDS and Security’, International Studies Quarterly, vol.50, no.1, 2006. Further Reading: Floyd, ‘Towards a Consequentialist Evaluation of Security: Bringing Together the Copenhagen and Welsh Schools of Security Studies’, Review of International Studies, vol.37, no.2, 2007. Floyd, Security and the Environment: Securitisation Theory and US Environmental Security Policy (Cambridge: CUP, 2010). Floyd, ‘Can Securitization Theory be Used in Normative Analysis: Towards a ‘Just Securitization Theory’, Security Dialogue, vol.42, no.4-5, 2011. Huysmans, ‘Minding Exceptions: The Politics of Insecurity and Liberal Democracy’, Contemporary Political Theory, vol.3, no.3, 2004. Week 5/Seminar 10. The Security of Silence: Marginalisations, Nothings, Images Key Text: Lene Hansen, ‘The Little Mermaid’s Silent Security Dilemma and the Absence of Gender in the Copenhagen School’, Millennium, vol.29, no.2, 2000. Further Reading: Hansen, ‘Theorizing the Image for Security Studies: Visual Securitization and the Muhammad Cartoon Crisis’, European Journal of International Relations, vol.17, no.1, 2011. Huysmans, ‘What is in an Act? On Security Speech Acts and Little Security Nothings’, Security Dialogue, vol.42, no.4-4, 2011. Vibeke Schou Tjalve, ‘Designing (de)Security: European Exceptionalism, Atlantic Republicanism and the ‘Public Sphere’, Security Dialogue, vol.42, no.4-5, 2011. Campbell, ‘Cultural Governance and Pictorial Resistance: Reflections on the Imaging of War, Review of International Studies, vol.29, no.2, 2003. Stuart Croft, ‘Images and Imaginings of Security’; James Gow, ‘Strategic Pedagogy and Pedagogic Strategy’; Andrew Hoskins, ‘Temporality, Proximity, and Security: Terror in a MediaDrenched Age’; Brandon Hamber, Paddy Hillyard, Amy Maguire, Monika McWilliams, Gillian Robinson, David Russell, & Margaret Ward, ‘Discourses in Transition: Re-imagining Women’s Insecurity’, International Relations, vol.20, no.4, 2006. Williams, ‘Words, Images, Enemies: Securitization and International Politics’, International Studies Quarterly, vol.47, no.4, 2003. Week 6/Seminar 11. Security and the Politics of Human Trafficking Key Text: Claudia Aradau, ‘The Perverse Politics of Four-Letter Words: Risk and Pity in the Securitisation of Human Trafficking’, Millennium, vol.33, no.2, 2004. Further Reading: Jacqueline Berman, ‘(Un)Popular Strangers and Crises (Un)Bounded: Discourses of Sex Trafficking, the European Political Community and the Panicked State of the Modern State’, European Journal of International Relations, vol.9, no.1, 2003. Karen Lund Petersen, ‘Trafficking in Women: The Danish Construction of Baltic Prostitution’, Cooperation and Conflict, vol.36, no.2, 2001. Andrew Nichols Pratt, ‘Human Trafficking: The Nadir of an Unholy Trinity’, European Security, vol.13, no.1, 2004. Barbara Sullivan, ‘Trafficking in Women: Feminism and New International Law’, International Feminist Journal of Politics, vol.5, no.1, 2003. Jo Goodey, ‘Migration, Crime and Victimhood: Responses to Sex Trafficking in the EU’, Punishment and Society, vol.5, no.4, 2003. Week 6/Seminar 12. Desecuritization Key Text: Hansen, ‘Reconstructing Desecuritisation: The Normative-Political in the Copenhagen School and Directions for How to Apply it’, Review of International Studies, vol.38, no.3, 2012. Further Reading: Robert Miles & Dietrich Thranhardt (eds.), Migration and European Integration: The Dynamics of Inclusion and Exclusion (London: Pinter, 1995), Chapter 3: Jef Huysmans, ‘Migrants as a Security Problem: Dangers of “Securitizing” Societal Issues’. Huysmans, ‘The Question of the Limit: Desecuritization and the Aesthetics of Horror in Political Realism’, Millennium, vol.27, no.3, 1998. Mark Salter, ‘Securitization and Desecuritization: A Dramaturgical Analysis of the Canadian Air Transport Security Authority’, Journal of International Relations and Development, Vol.11, no.4, 2008. Week 7. Seminar 13. Desecuritization: Transformation versus Management Key Text: Roe, ‘Securitization and Minority Rights: Conditions of Desecuritization’, Security Dialogue, vol.35, no.3, 2004. Further Reading: Matti Jutila, ‘Desecuritizing Minority Rights: Against Determinism’, Security Dialogue, vol.37, no.2, 2006. Roe, ‘Reconstructing Identities or Managing Minorities? Desecuritizing Minority Rights: A Response to Jutila’, Security Dialogue, vol.37, no.3, 2006. Kristian Atland, ‘Mikhail Gorbachev, the Murmansk Initiative, and the Desecuritization of Interstate Relations in the Arctic’, Cooperation and Conflict, vol.43, no.3, 2008. Week 7/Seminar 14. Desecuritization, Emancipation, and the Ethics of Security Key Text: Aradau, ‘Security and the Democratic Scene: Desecuritization and Emancipation’, Journal of International Relations and Development, vol.7, no.4, 2004. Further Reading: Rita Taureck (later Floyd), ‘Securitization Theory and Securitization Studies’; Andreas Behnke, ‘No Way Out: Desecuritization, Emancipation and the Eternal Return of the Political – A Reply to Aradau; Hayward Alker, ‘On Securitization Politics as Contexted Texts and Talks’; Aradau, ‘Limits of Security, Limits of Politics? A Response’, Journal of International Relations and Development, vol.9, no.1, 2006. Aradau, Rethinking Trafficking in Women: Politics out of Security (Basingstoke: Palgrave Macmillan, 2008). Ole Waever, ‘Politics, Security, Theory’, Security Dialogue, vol.42, no.4-5, 2011. Roe, ‘Is Securitization a Negative Concept? Revisiting the Normative Debate over Normal versus Emergency Politics’, Security Dialogue, vol.43, no.3, June 2012. David Chandler & Nik Hynek (eds.), Human Security: Rethinking Emacipation and Power in International Relations (London: Routledge, 2011), Chapter 14: Mark Neocleous, ‘Inhuman Security’. Neocleous, ‘The Problem with Normality: Taking Exception to Permanent Emergency’, Alternatives, vol.31, no.2, 2006. Chandler, ‘The Revival of Carl Schmitt in International Relations: The Last Refuge of Critical Theorists?’, Millennium, vol.37, no.1, 2008. Weeks 8/Seminar 15, Week 8/Seminar 16, & Week 9/Seminar 17. The Politics of Fear For these three seminar sessions, a three-part film will be shown; Adam Curtis’ The Power of Nightmares: The Rise of the Politics of Fear. The film explores the parallel development of two political movements: in the U.S., the Neo-Conservatives, and in North Africa the Islamic Brotherhood/Islamic Jihad. The film shows how not only certain constructions of threat are made possible, but the political function of these constructions; that is, the ordering of societies along particular lines. The aim of these seminars is to reveal not so much what security is, but, perhaps more pertinently, what security does. Week 9/Seminar 18. Human Security, Emancipation, and ‘C’ritical Security Studies Key Text: Edward Newman, ‘Critical Human Security Studies’, Review of International Studies, vol.36, no.1, 2010. Further Reading: Ken Booth, Theory of World Security (Cambridge: CUP, 2007). Booth (ed.), Critical Security Studies and World Politics (Boulder: Lynne Rienner, 2005). Heidi Hudson, ‘‘Doing’ Security as Though Humans Matter: Feminist Perspective on Gender and the Politics of Human Security’, Security Dialogue, vol.36, no.2, 2005. Ryerson Christie, ‘Critical Voices and Human Security: To Engage or To Critique?’, Security Dialogue, vol.41, no.2, 2010. Rita Floyd, ‘Human Security and the Copenhagen School’s Securitization Approach: Conceptualizing Human Security as a Security Move’, Human Security Journal, vol.5, no.4, 2007. Andrew Linklater, ‘Towards a Sociology of Global Morals with an ‘Emancipatory Intent’, Review of International Studies, vol.33, Supplement 1, 2007. Chandler and Hynek (eds.), Human Security, Chapter 8: Tara McCormack, ‘The Limits to Emancipation in the Human Security Framework’ Week 10/Seminar 19. The Politics of Emancipation Mike Bourne & Dan Bulley, ‘Securing the Human in Critical Security Studies: The Insecurity of a Secure Ethics’, European Security, vol.20, no.3, 2011. Further Reading: Booth, ‘Anchored in Tahrir Square’, European Security, vol.20, no.3, 2011. Christopher Browning & Matt McDonald, ‘The Future of Critical Security Studies: Ethics and the Politics of Security’, European Journal of International Relations, vol.?, no.?, 2012. Benjamin Shepherd, ‘Thinking Critically about Food Security’, Security Dialogue, vol.43, no.3, 2012. Joao Nunes, ‘Reclaiming the Political: Emancipation and Critique in Security Studies’, Security Dialogue, vol.43, no.4, 2012. Week 10/Seminar 20. Critical (Emancipatory) Approaches to Terrorism Key Text: Harmonie Toros, ‘‘We Don’t Negotiate with Terrorists!’: Legitimacy and Complexity in Terrorist Conflicts’, Security Dialogue, vol.39, no.4, 2008. Further Reading: Booth, ‘The Human Faces of Terror: Reflections in a Cracked Looking Glass’, Critical Studies on Terrorism, vol.1, no.1, 2008. Richard Jackson, Marie Breen Smyth, & Jeroen Gunning (eds.), Critical Terrorism Studies: A New Research Agenda (London: Routledge, 2009). Angharad Closs Stephens & Nich Vaughan-Williams (eds.), Terrorism and the Politics of Response (London: Routledge, 2010), Chapter 8: James Brassett, ‘Cosmopolitanism versus Terrorism: Discourses of Ethical Possibility Before and After 7/7’. Eric Herring, ‘Critical Terrorism Studies: An Activist Scholar Perspective’, Critical Studies on Terrorism, vol.1, no.2, 2008. Toros, ‘Terrorists, Scholars and Ordinary People: Confronting Terrorism Studies with Field Experience’, Critical Studies on Terrorism, vol.1, no.2, 2008. Michael Stohl, ‘Don’t Confuse me with the Facts: Knowledge Claims and Terrorism’, Critical Studies on Terrorism, vol.5, no.1, 2012. Week 11/Seminar 21. ‘Risk’, 9/11, and the ‘War on Terror’ Key Text: Aradau & Rens van Munster, ‘Governing Terrorism Through Risk: Taking Precautions, (un)Knowing the Future’, European Journal of International Relations, vol.13, no.1, 2007. Further Reading: Louise Amoore & Marieke de Goede 9 (eds.), Risk and the War on Terror (London, Routledge, 2008). Gabe Mythen & Sandra Walklate, ‘Terrorism, Risk and International Security: The Perils of Asking ‘What If?’, Security Dialogue, vol.39, no.2-3, 2008. de Goede, ‘Beyond Risk: Premeditation and the Post 9/11 Security Imagination’, Security Dialogue, vol.39, no.2-3, 2008. William Clapton, ‘Risk in International Relations’, International Relations, vol.25, no.3, 2011. Craig McLean, Alan Patterson & John Williams, ‘Risk Assessment, Policy-Making and the Limits of Knowledge: The Precautionary Principle and International Relations’, International Relations, vol.23, no.4, 2010. Oliver Kessler & Christophe Daase, ‘Knowns and Unknowns in the ‘War on Terror’: Uncertainty and the Political Construction of Danger’, Security Dialogue, vol.38, no.4, 2008. Week 11/Seminar 22. The Privatisation of Security Key Text: Anna Leander, ‘The Power to Construct International Security: On the Significance of Private Military Companies’, Millennium, vol.33, no.3, 2005. Further Reading: Singer, ‘Corporate Warriors: The Rise of the Privatized Military Industry and its Ramifications for International Security’, International Security, vol.26, no.3, 2001/2. Rita Abrahamsen & Williams, ‘Security Beyond the State: Global Security Assemblages in International Politics’, International Political Sociology, vol.3, no.1, 2009. Elke Krahmann, ‘Security: Collective Good or Commodity?’, European Journal of International Relations, vol.14, no.3, 2008. Leander & van Munster, ‘Private Security Contractors in the Debate about Darfur: Reflecting and Reinforcing Neo-Liberal Governmentality’, International Relations, vol.21, no.2, 2007. Leander, ‘The Paradoxical Impunity of Private Military Companies: Authority and the Limits to Legal Accountability’, Security Dialogue, vol.41, no.5, 2010. Week 12/Seminar 23. No Class Week 12/Seminar 24. No Class