Chapter 7:
Transport Layer
Introduction to Networking
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
1
Cisco Confidential
2
Dermot Clarke DIT Sept’ 2013
Role of the Transport Layer
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
1
Dermot Clarke DIT Sept’ 2013
Purpose of the Transport Layer:
The Transport layer is the link between the Application layer
and the lower layer that are responsible for network
transmission.
This layer accepts data from different conversations and
passes it down to the lower layers as manageable pieces
that can be eventually multiplexed over the media.
Applications do not need to know the operational details of
the network in use.
Additionally, the lower layers are not aware that there are
multiple applications sending data on the network.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
3
Dermot Clarke DIT Sept’ 2013
Transportation of Data
Role of the Transport Layer
The Transport Layer is responsible for establishing a temporary
communication session between two applications and delivering data
between them. TCP/IP uses two protocols to achieve this:
Transmission Control Protocol (TCP)
User Datagram Protocol (UDP)
Primary Responsibilities of Transport layer Protocols
1. Tracking the individual communication between applications on
the source and destination hosts
2. Segmenting data for manageability and reassembling segmented
data into streams of application data at the destination
3. Identifying the proper application for each communication stream
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
4
2
Dermot Clarke DIT Sept’ 2013
Transportation of Data
Conversation Multiplexing
Segmenting the data
Enables many different
communications, from many
different users, to be
interleaved (multiplexed) on
the same network, at the
same time.
Provides the means to both
send and receive data when
running multiple applications.
Header added to each
segment to identify it.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
5
Dermot Clarke DIT Sept’ 2013
Transportation of Data
Transport Layer Reliability
Different applications have different transport reliability requirements
TCP/IP provides two transport layer protocols, TCP and UDP
Transmission Control Protocol (TCP)
Provides reliable delivery ensuring that all of the data arrives at the
destination.
Uses acknowledged delivery and other processes to ensure delivery
Makes larger demands on the network – more overhead (slower)
User Datagram Protocol (UDP)
Provides just the basic functions for delivery – no reliability
Less overhead
TCP or UDP
There is a trade-off between the value of reliability and the burden it
places on the network.
Application developers choose the transport protocol based on the
requirements of their applications.
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
6
3
Dermot Clarke DIT Sept’ 2013
Introducing TCP and UDP
Introducing TCP
Transmission Control Protocol (TCP)
In addition to the basic functions of data segmentation and reassembly,
some protocols at the Transport layer provide:
•
•
•
•
•
Connection-oriented – creating a session between source and destination
Reliable delivery – retransmitting lost or corrupt data
Ordered data reconstruction – numbering and sequencing of segments
Flow control - regulating the amount of data transmitted
Stateful protocol – keeping track of the session
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
7
Dermot Clarke DIT Sept’ 2013
TCP Header Summary
Source Port – used to identify the
sending application.
TCP
Header
Destination Port – used to identify the
receiving application.
The sequence number – Used to
identify the segments position in the
broken up large file.
The ACK number – Send back by the
receiver to acknowledge that the
segment was received correctly.
Header length – Length of header
Flags: Used to indicate the purpose of
the segment.
Window size –Sliding window size.
TCP checksum – covers the TCP
segment, i.e. TCP header and TCP
data, used for bit error checking.
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
Flags: Used to manage the TCP
processes.
SYN: Synchronise
ACK: Acknowledge
FIN: Finish
(1 = Set 0 = Unset)
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
8
4
Dermot Clarke DIT Sept’ 2013
Introducing TCP and UDP
Introducing UDP
User Datagram Protocol (UDP)
Connectionless
Unreliable delivery
No ordered data reconstruction
No flow control
Stateless protocol
Applications that use UDP:
Domain Name System (DNS)
Video Streaming
Voice over IP (VoIP)
If these applications used TCP, they may experience large delays while TCP
detects data loss and retransmits data. These delays would be more
detrimental to the application than small data losses.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
9
Dermot Clarke DIT Sept’ 2013
Introducing TCP and UDP
Separating Multiple Communications
Port Numbers are used by TCP and UDP to
differentiate between different applications.
.
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
10
5
Dermot Clarke DIT Sept’ 2013
Introducing TCP and UDP
TCP and UDP Port Addressing
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
11
Cisco Confidential
12
Dermot Clarke DIT Sept’ 2013
Introducing TCP and UDP
TCP and UDP Port Addressing
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
6
Dermot Clarke DIT Sept’ 2013
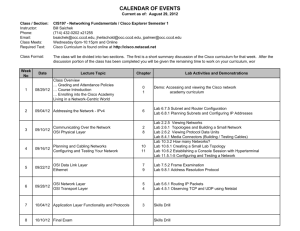
Introducing TCP and UDP
TCP and UDP Port Addressing
Netstat
Used to examine TCP connections that are open and
running on a networked host
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
13
Cisco Confidential
14
Dermot Clarke DIT Sept’ 2013
TCP Communication
TCP Server Processes
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
7
Dermot Clarke DIT Sept’ 2013
TCP Communication
TCP Connection, Establishment and Termination
Three-Way Handshake
Establishes that the destination
device is present on the network.
(SYN)
Verifies that the destination device
has an active service and is
accepting requests on the
destination port number that the
initiating client intends to use for
the session. (SYN ACK)
Informs the destination device that
the source client intends to
establish a communication session
on that port number. (ACK)
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
15
Dermot Clarke DIT Sept’ 2013
TCP Communication NEED New Graphic for this and next two slides
TCP Three-Way Handshake – Step 1
Step 1: The initiating client requests a client-toserver communication session with the server.
Establishes that the
destination device is
present on the
network.
(“Will you accept my
connection”)
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
16
8
Dermot Clarke DIT Sept’ 2013
TCP Communication
TCP Three-Way Handshake – Step 2
Step 2: The server acknowledges the client-toserver communication session and requests a
server-to-client communication session.
Verifies that the destination
device has an active service
and is accepting requests.
(“Yes I will accept your
connection”)
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
17
Dermot Clarke DIT Sept’ 2013
TCP Communication
TCP Three-Way Handshake – Step 3
Step 3: The initiating client acknowledges the
server-to-client communication session.
Informs the
destination device that
the source client
intends to establish a
communication
session. (“great, data
is on its way”)
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
18
9
Dermot Clarke DIT Sept’ 2013
TCP Communication
TCP Session Termination
To end TCP session, a
two-way handshake is
used, consisting of a
FIN and an ACK flags.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
19
Dermot Clarke DIT Sept’ 2013
TCP Reliability Positive Acknowledgement & Retransmission
Normal Operation
Lost Packet
So retransmitted.
ACK lost
So retransmitted.
Packet delayed
So retransmitted.
Note: Last 2 scenarios will
result in 2 versions of the
same packet at the receiver.
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
20
10
Dermot Clarke DIT Sept’ 2013
Reliability and Flow Control
TCP Reliability – Ordered Delivery
Sequence numbers used to reassemble segments into
original order
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
21
Cisco Confidential
Dermot Clarke DIT Sept’ 2013
Sequence & Acknowledgement Numbers
The segment sequence number and
acknowledgement number are used to
confirm receipt of the bytes of data in the
segments.
Server
Client
–The sequence number is the relative number
of bytes that have been transmitted in this
session plus 1.
–The sending host is expected to send a
segment that uses a sequence number that is
equal to the acknowledgement number.
•The source is informed that the destination has
received all bytes in this data up to, but not
including, the byte indicated by the
acknowledgement number.
•This is called expectational acknowledgement.
So the ACK number is the next
sequence number that the sender
of the ACK expects to receive
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
22
11
Dermot Clarke DIT Sept’ 2013
Sequence & Acknowledgement Numbers
Consider the example opposite :
The Client sends a segment containing 28 bytes of
data. The Seq. Number used by the client is 21495118.
This data is acknowledged by the Receiver by sending
an ACK segment with the acknowledge number set to
the client sequence number plus the number of bytes
received. i.e 21495118 + 28 bytes giving
Ack=21495146. The ACK flag is set.
TCP allows multiple packets to be acknowledged by a
single ACK. See example opposite.
This will reduce the overhead of these acknowledgements,
multiple segments of data can be sent before and
acknowledged with a single TCP message.
This acknowledgement contains an acknowledgement
number based on the total number of bytes received
This is known as “windowing”
Window Size - The amount of data that a source can
transmit before an acknowledgement must be received.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
23
Dermot Clarke DIT Sept’ 2013
Reliability and Flow Control
TCP Flow Control – Congestion Avoidance
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
24
12
Dermot Clarke DIT Sept’ 2013
TCP Congestion Control – Reducing Window Size
Another way to control the data flow is to use dynamic window sizes.
When network resources are constrained, TCP can reduce the window size to require
that received segments be acknowledged more frequently.
This effectively slows down the rate of transmission because the source waits for data
to be acknowledged more frequently.
If the destination needs to slow down the rate of communication because
of limited buffer memory, it can send a smaller window size value to the
source as part of an acknowledgement.
After periods of transmission with no data losses or constrained
resources, the receiver will begin to increase the window field again.
This dynamic increasing and decreasing of window size is a continuous
process in TCP, which determines the optimum window size for each
TCP session.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
25
Dermot Clarke DIT Sept’ 2013
Reliability and Flow Control
TCP Reliability - Acknowledgements
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
26
13
Dermot Clarke DIT Sept’ 2013
UDP Communication
UDP Low Overhead vs. Reliability
UDP
Simple protocol that provides the basic transport layer functions
Used by applications that can tolerate small loss of data
Used by applications that cannot tolerate delay
Used by
Domain Name System (DNS)
Simple Network Management Protocol (SNMP)
Dynamic Host Configuration Protocol (DHCP)
Trivial File Transfer Protocol (TFTP)
IP telephony or Voice over IP (VoIP)
Online games
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
27
Cisco Confidential
28
Dermot Clarke DIT Sept’ 2013
UDP Communication
Datagram Reassembly
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
14
Dermot Clarke DIT Sept’ 2013
UDP Communication
UDP Server and Client Processes
UDP-based server applications are assigned wellknown or registered port numbers.
UDP client process randomly selects port number from
range of dynamic port numbers as the source port.
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
29
Cisco Confidential
30
Dermot Clarke DIT Sept’ 2013
TCP or UDP
Applications that use TCP
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
© 2008 Cisco Systems, Inc. All rights reserved.
15
Dermot Clarke DIT Sept’ 2013
TCP or UDP
Applications that use UDP
Presentation_ID
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
31
© 2008 Cisco Systems, Inc. All rights reserved.
Cisco Confidential
32
Dermot Clarke DIT Sept’ 2013
Presentation_ID
© 2006, Cisco Systems, Inc. All rights reserved.
Presentation_ID.scr
16