Communication Frequency Spectrum Wireless Networks
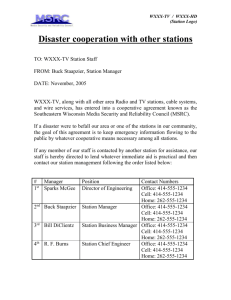
advertisement

Communication Frequency Spectrum • Electromagnetic spectrum and applications (Tanenbaum 2003) Wireless Networks Background • – – – • – – – – Aspects of Wireless Networks mobility and convenient deployment scarce frequency spectrum wireless implications such as transmission problems (e.g. interference, path loss, fading), security, battery, installation, health Wireless networks Cellular: GSM, PCS, IMT 2000 Satellite: IRIDIUM, Globalstar WLAN: IEEE 802.11, HiperLAN Ad-Hoc, PAN, HAN Wireless Local Area Networks (WLAN) • General considerations: – limited utilization till last decade but extensive development lately – usually in spaces where wired networks were difficult or not appropriate to deploy – may increase reliability – cost effective – different standards – different transmission medium used WLAN Applications [1] • LAN Extension: – wireless extensions to fixed LANs – stations in large open areas – single or multiple cells • Cross-Building Interconnect: – connect nearby building – usually point-to-point communication – connected devices: usually routers and bridges • Some WLAN implications: – transmission problems: connection, multipath propagation, path loss and radio signal interference – network security – system interoperability – installation issues and health risks WLAN Applications [2] • Nomadic Access: – connect mobile terminals with a LAN hub • Ad-hoc Networking: – spontaneous established temporary networks WLAN Requirements [1] • Throughput: efficient use of the transmission medium • Number of nodes: large number of nodes may be needed • Connection to backbone LAN: usually a connection with a wired networks is needed • Service area: typical 100 to 300 m • Battery life time: efficient management of mobile station battery • Transmission robustness and security: WLAN may be interference prone and may be eavesdropped 1 WLAN Requirements [2] WLAN Technologies [1] Î Categorized according with the used transmission technology: • Infrared (IR) LAN : • Collocated network operations: more than one WLAN in the – IR does not penetrate walls same area – limited to a single room • License free operation: user oriented approach • Spread Spectrum LAN: • Handoff and roaming: moving between cells and even – use spread spectrum networks may be needed – usually operate in ISM band • Dynamic configuration: addition, deletion and reallocation of • Narrowband microwave LAN: end systems without affecting the network functionality – operate at microwave frequency (e.g. above 1 GHz) – can use ISM or licentiate frequency spectrum – do not use spread spectrum Infrared (IR) WLAN WLAN Technologies [2] • Directed Beam IR (a) (a) – point-to-point links – range depend on power and wave focus • Omnidirectional IR (b) – single base station in LOS of all stations (b) – the base station acts as a repeater • Diffused (c) – all transmitter focus at a point on ceiling – IR radiation is retransmitted (reradiate) (c) – reradiated IR waves are received by all stations in the area Infrared (IR) WLAN vs. Microwave WLAN • Strengths Spread Spectrum and Narrowband WLAN • Spread Spectrum WLAN – usually multi-cell with different frequencies – virtual unlimited spectrum – hub or peer-to-peer topology in a cell – unregulated spectrum – hub topology: the hub may provide access control and repeater operations and is – simple equipment needed -> inexpensive usually connected to a backbone network – reflected by light-colored objects – peer-to-peer topology: use ad-hoc connectivity without any hub – does not penetrate walls: more secure against eavesdropping and does not – usually unlicensed spectrum introduce interference – interference prone • Drawbacks: – sunlight, indoor lighting and other ambient radiation perceived as noise • Narrowband WLAN – high-power transmitter required -> may introduce health problem (i.e. eye – usually use narrow microwave band for transmission safety) and power consumption problems – unlicensed as well as licensed frequency spectrum – limited range – does not use spread spectrum – licensed -> interference-free 2 Other Wireless Networks - Cordless Systems Other Wireless Networks - Wireless Local Loops (WLL) • Characteristics – Residential: single base station with support for voice and data • Broadband WLL - high-speed voice and data services – Office: single base station for small offices, multiple base stations deployed using a cellular configuration for larger offices – Telepoint: a base station set up in a public place (e.g. an airport) – Small range for hand set -> low power – Inexpensive base station and hand set -> simple technical approaches – Limited frequency flexibility -> must work in different places • Usually use milimetric waves (e.g. above 10 GHz) • Advantages: cost, installation time, selective installation • Propagation problems: free space loss, rainfall attenuation, atmospheric and gaseous absorption, mutipath losses, vegetation effects • Multichannel Multipoint Distribution Service: MMDS (ex. 2.67-2.68 GHz) • Local Multipoint Distribution Service: LMDS, standardized as IEEE 802.16 • Cordless Systems Example: DECT • Narrowband WLL - replacement for telephony services (ex. 27.5-28.3 GHz) – Band: 1.88 - 1.9 GHz; Bandwidth: 20 MHz; Number of channels 120 – Access Method : TDMA/FDMA – Data rate: 1.152 Mbps; Speech rate: 32 kbps – Mean power: 10 mW – Maximum cell radius: 30 to 100 m – Provide handoff Other Wireless Networks - Personal Area Networks (PAN) and Home Area Networks (HAN) Î PAN • Network serving a single person or a small group • Usually accommodate diverse mobile devices • Provide support for virtual docking station, peripheral sharing • Examples: Bluetooth, Infrared Data Association (IrDA), HomeRF Frågor? ÎHAN • Broadband smart house with intelligent appliances • HANs over phone lines, powerline and wireless HANs: diverse combination possible • Examples: HomeRF, Home Audio Video interoperability HAVi • Control Networks: low-speed powerline networks – specify protocols that are used via the power line – examples: LonWorks, X10, CEBus Contents Ad-Hoc Networks Ad-hoc Networks overview WLAN - IEEE 802.11 Wireless Local Area Networks - IEEE 802.11 WPAN - Bluetooth Wireless Personal Area Networks – Bluetooth Glomosim lab 3 Challenges in Ad-Hoc Networks [1] Ad-Hoc Networks Spectrum allocation - regulated by authorities • Spontaneous established networks • Self-organizing and adaptive • Accommodate communication between diverse devices - use of free portion of the spectrum (e.g. ISM) Medium access control - need for distributed protocols - mobility of nodes • Devices can communicate directly with neighbor devices - transmission problems (e.g. collisions) • Single-hop or multi-hop communication can be employed Routing - dynamically changing topology - random joining and existing of the network - highly dynamic management of the communication links Challenges in Ad-Hoc Networks [2] Ad-Hoc Networks – Media Access Control Multicasting - non-static routers • MAC protocols or schemes Energy efficiency - shared communication channel - diverse mobile devices - per-link (i.e. one-hop) communication - battery lifetime Service location, provision and access - heterogeneous devices with different capabilities - mobility of nodes - synchronous protocols –> nodes synchronized via a central entity - asynchronous protocols –> contention-based Security and privacy Media Access Control Schemes for Ad-Hoc Networks Ad-Hoc Networks – Routing Protocols [1] Example of MAC protocols • Table-Driven Protocols CSMA - Carrier Sense Multiple Access - proactive approach MACA – Multiple Access with Collision Avoidance - consistent view of the network - use RTS-CTS-Data - use of routing tables - no carrier sense - power control features - react to changing in the network by generating route updates IEEE 802.11 - usually differ by the number and type of routing tables and - based on CSMA/CA the methods for updating the network view - can use RTS-CTS-Data-ACK • Example: -specify both distributed and an optional centralized access - Destination Sequenced Distance Vector (DSDV) control - Wireless Routing Protocol (WRP) - complex algorithm with high performance 4 Ad-Hoc Networks – Routing Protocols [2] • On-Demand-Driven Protocols - reactive approach - create route at the source node request - different route discovery mechanisms - different route maintenance mechanisms • Examples Frågor - Ad Hoc On-Demand Distance Vector (AODV) - Dynamic Source Routing (DSR) - Location-Aided Routing (LAR) 26 Hidden Terminal Problem [1] • Hidden terminal problem - ad-hoc and WLAN - medium free near the transmitter - medium not free near the receiver => Packet collision • Possible solution: - MAC scheme using RTS-CTS scheme Hidden Terminal Problem [2] • • - RTS – CTS solution: RTS -> Requests To Send CTS -> Clear To Send Example: Node1 want to send data to Node 2 (figure below) Problems with RTS-CTS solution: possible collisions between CTS and RTS collisions between data packets due to multiple CTS granted to different neighboring nodes RTS (1) CTS (2) CTS (2) Data (3) ACK(4) ACK(4) Node 2 Node 1 Exposed Terminal Problems • Exposed terminal problem - ad-hoc and WLAN - medium free near the receiver - medium busy near the transmitter => Waist of bandwidth • Possible solutions: - directional antennas - separate channels for control and data Node 3 WLAN Applications [1] • LAN Extension: – wireless extensions to fixed LANs – stations in large open areas – single or multiple cells • Cross-Building Interconnect: – connect nearby building – usually point-to-point communication – connected devices: usually routers and bridges 30 5 WLAN Applications [2] WLAN Requirements [1] • Nomadic Access: – connect mobile terminals with a LAN hub • Ad-hoc Networking: – spontaneous established temporary networks • Throughput: efficient use of the transmission medium • Number of nodes: large number of nodes may be needed • Connection to backbone LAN: usually a connection with a wired networks is needed • Service area: typical 100 to 300 m • Battery life time: efficient management of mobile station battery • Transmission robustness and security: WLAN may be interference prone and may be eavesdropped 31 32 WLAN Technologies [1] WLAN Requirements [2] Î Categorized according to the used transmission technology: • Collocated network operations: more than one WLAN in the same area • Infrared (IR) LAN : • License free operation: user oriented approach – limited to a single room • Handoff and roaming: moving between cells and even networks may be needed • Spread Spectrum LAN: • Dynamic configuration: addition, deletion and – usually operate in ISM band reallocation of end systems without affecting the network functionality • Narrowband microwave LAN: – IR does not penetrate walls – use spread spectrum – operate at microwave frequency (e.g. above 1 GHz) – can use ISM or licentiate frequency spectrum 33 – do not use spread spectrum 34 Infrared (IR) WLAN WLAN Technologies [2] • Directed Beam IR (a) (a) – point-to-point links – range depend on power and wave focus • Omnidirectional IR (b) – single base station in LOS of all stations (b) – the base station acts as a repeater • Diffused (c) – all transmitter focus at a point on ceiling – IR radiation is retransmitted (reradiate) (c) – reradiated IR waves are received by all stations in the area 35 36 6 Spread Spectrum and Narrowband WLAN Infrared (IR) WLAN vs. Microwave WLAN • Spread Spectrum WLAN • Strengths – usually multi-cell with different frequencies – virtual unlimited spectrum – hub or peer-to-peer topology in a cell – unregulated spectrum – simple equipment needed -> inexpensive – hub topology: the hub may provide access control and repeater operations and is usually connected to a backbone network – reflected by light-colored objects – peer-to-peer topology: use ad-hoc connectivity without any hub – does not penetrate walls: more secure against eavesdropping and does not introduce interference – usually unlicensed spectrum – interference prone • Drawbacks: – sunlight, indoor lighting and other ambient radiation perceived as noise – high-power transmitter required -> may introduce health problem (i.e. eye safety) and power consumption problems • Narrowband WLAN – usually use narrow microwave band for transmission – unlicensed as well as licensed frequency spectrum – does not use spread spectrum – limited range – licensed -> interference-free 37 38 Wireless Local Area Networks (WLAN) • Most known standard for WLAN - IEEE 802.11 • Use a layering architecture similar to OSI called IEEE 802 reference model Frågor 39 IEEE 802 Protocols Architecture • Physical Layer: – – – – encoding/decoding signals generation/removal of synchronization data transmission and reception of bits include specifications of the transmission medium and topology • Medium Access Control (MAC) – transmission Î create data frames containing the original data and error correction and address information – reception Î extract original data from the received message, perform address recognition and error detection – control access to the LAN transmission medium • Logical Link Control (LLC) – provide interface to higher layers – perform flow and error control IEEE 802.11 Architecture • Station: a device containing 802.11 equipment • Basic Service Set (BSS): set of stations controlled by a coordination function • Coordination function: logical function determining when a station can receive and send data in a BSS • Distribution System (DS): a system connecting a set of BSS and integrated LANs to create an extended service set (ESS) • Extended Service Set: a set of BSS and LANs appearing as a single unit to the LLC layer of the component stations • Access point (AP) : entity providing access to the distribution system 7 IEEE 802.11 Services • IEEE 802.11 define 9 services: – 6 services for supporting delivery of MAC service data units (MSDU) between stations – 3 services for LAN access and confidentiality • Service provider type: – station: services implemented in stations and access point stations (APs) – distribution system (DS): services between BSSs implemented in access point stations or dedicated devices Message distribution within the Distribution System (DS) ÎIEEE 802.11 define 2 services for message distribution in DS: • Distribution Service – use to exchange MAC frames from stations in one BSS to stations in another BSS – if transmitting and receiving stations are within the same BSS-> the distribution service logically goes through the AP of the BSS • Integration Service – transfer data between stations on an IEEE 802.11 network and stations on an integrated 802.X network (i.e. wired LAN physically connected with the DS) – deal with address translation and media conversion between the two networks Association-Related Services [1] • Provide information about stations within an extended service set (ESS) • The distribution service can deliver or accept data only from associated stations -> DS need to know the location of the stations, i.e. the AP to which a message should be delivered for reaching further the destination • Stations maintain association with the AP from their current BSS • Three types of mobility are defined: – No transition: stationary stations or stations move only within the same BSS Association-Related Services [2] ÎIEEE 802.11 define 3 associated-related services: • Association Service – establish initial association between a station and an AP • Reassociation Service – enable an established association to be transferred from one AP to another when a station move from a BSS to another one • Disassociation Service – association termination notice from station or from the AP associated with the station – BSS transition: stations may move from a BSS to another BSS within the same ESS – ESS transition: stations move from a BSS in one ESS to a BSS in another ESS Access and Privacy Services IEEE 802.11 Medium Access Control (MAC) ÎIEEE 802.11 define 3 access and privacy services: ÎIEEE 802.11 MAC cover 3 areas: • Authentication Service • Reliable Data Delivery – establish identity of stations to each other – require due to the error-prone wireless transmission characteristics – can employ different schemes (e.g open system, shared key) – noise, interference, other propagation effects • Deauthentication Service • Access Control – invoked when existing authentication is terminated – distributed access -> ad-hoc networks and networks implying bursty traffic • Privacy Service – prevent message content from being read by non-intended recipients – optional encryption – use Wired Equivalent Privacy (WEP) algorithm – centralized access -> networks containing base stations connected with a backbone wired network • Security – required due to easy capture of transmission 14 8 IEEE 802.11 MAC - Reliable Data Delivery 802.11 MAC - Distribution Coordination Function [1] • MAC level: • Make use of CSMA (carrier sense multiple access) • Use set of delays generic called Interframe Space (IFS) – more efficient to deal with errors at MAC than at higher layers • IEEE 802.11 include a frame protocol Algorithm Logic: – usually a two-frames protocol: data transmitted by the source station must be acknowledged (ACK) by the destination station – the exchange of Data+ACK is atomic -> not to be interrupted by other transmission – if the source does not receive ACK it retransmits the data 1. Station sense the medium 2. If medium idle, wait IFS, then if still idle transmit frame 3. If medium busy or become busy, defer and monitor the medium until idle 4. Then, delay IFS and sense medium 5. If medium idle, exponential backoff and if then if station transmit • Binary exponential backoff -> handle heavy load • IEEE 802.11 define a four-frame protocol for enhance reliability – source sends Request To Send (RTS) frame – destination responds with Clear To Send (CTS) frame – after receiving CTS, the source send data that must be acknowledged (ACK) by destination – RTS alert stations within source range about the current data exchange – CTS alert station within destination range about the current data exchange 15 802.11 MAC - Distribution Coordination Function [2] • Priority-based scheme - use 3 values for IFS: – SIFS (short IFS): shortest IFS used for immediate responses such as ACK, CTS, poll response – PIFS (point coordination function IFS): middle length IFS used for issuing polls by a centralized controller – DIFS (distributed coordination function IFS): longest IFS used for regular asynchronous frames 802.11 MAC - Frames Types • Six types of control frames – Power save - poll (PS-poll) – Request to send (RTS) – Clear to send (CTS) – Acknowledgment (ACK) – Contention-free (CF)-end – CF-end + CF-Ack 802.11 MAC - Point Coordination Function • • • • Alternative access method on top of DCF Polling operation by a centralized master Use PIFS when issuing polls For avoiding locking out the asynchronous traffic the superframe is used IEEE 802.11 MAC - Security • Eight types of data fram ÎCarry user data – Data – Data + CF-Ack – Data + CF-poll – Data + CF-Ack + CF-poll Î Do not carry user data – Null Function •Management frames – CF-Ack – association request and association response – CF-Poll – reassociation request and reassociation response – CF-Ack + CF-Poll – probe request and probe response – beacon – announcement traffic indication message – disassociation – authentication and deauthentication • Provide both privacy and authentication mechanisms • Wired Equivalent Privacy (WEP) Algorithm: – modest protection – use encryption algorithm based on RC4 • Authentication: – open system authentication: identities exchange – shared key authentication: two parties share a key not shared by others 9 IEEE 802.11 security • War-driving: drive around Bay area, see what 802.11 networks available? – More than 9000 accessible from public roadways – 85% use no encryption/authentication – packet-sniffing and various attacks easy! • Securing 802.11 – encryption, authentication – first attempt at 802.11 security: Wired Equivalent Privacy (WEP): a failure – current attempt: 802.11i WEP data encryption • Host/AP share 40 bit symmetric key (semipermanent) • Host appends 24-bit initialization vector (IV) to create 64-bit key • 64 bit key used to generate stream of keys, kiIV • kiIV used to encrypt ith byte, di, in frame: ci = di XOR kiIV • IV and encrypted bytes, ci sent in frame 802.11 Security Wired Equivalent Privacy (WEP): • authentication as in protocol ap4.0 – host requests authentication from access point – access point sends 128 bit nonce – host encrypts nonce using shared symmetric key – access point decrypts nonce, authenticates host • no key distribution mechanism • authentication: knowing the shared key is enough 802.11 WEP encryption Sender-side WEP encryption Breaking 802.11 WEP encryption Security hole: • 24-bit IV, one IV per frame, -> IV’s eventually reused • IV transmitted in plaintext -> IV reuse detected • Attack: – Trudy causes Alice to encrypt known plaintext d1 d2 d3 d4 … – Trudy sees: ci = di XOR kiIV – Trudy knows ci di, so can compute kiIV – Trudy knows encrypting key sequence k1IV k2IV k3IV … – Next time IV is used, Trudy can decrypt! Packet encryption using WEP. 10 802.11i: improved security • numerous (stronger) forms of encryption possible • provides key distribution • uses authentication server separate from access point 802.11i: four phases of operation STA: client station AP: access point AS: Authentication server wired network 1 Discovery of security capabilities 2 STA and AS mutually authenticate, together generate Master Key (MK). AP servers as “pass through” 3 STA derives Pairwise Master Key (PMK) 3 AS derives same PMK, sends to AP 4 STA, AP use PMK to derive Temporal Key (TK) used for message encryption, integrity IEEE 802.11 issues • Different IEEE 802.11 physical media – direct sequence spread spectrum (DS-SS) – frequency hopping spread spectrum (FH-SS) – infrared • Currently well-known IEEE 802.11 versions – IEEE 802.11b: operating in ISM band, around 2.4 GHz, with data Frågor rates of 5.5 to 11 Mbps – IEEE 802.11a: operates in 5 GHz band with data rates of 6, 9, 12, .. 54 Mbps 64 Wireless Personal Area Network - Bluetooth Bluetooth: Applications Areas and Specifications Ö Application Areas • Universal short-range wireless communication standard • Up to 10 m indoor and 100 m outdoors • Uses the ISM 2.4-GHz unlicensed band • Data rate up to 720 kbps (asymmetric) • Supports different applications: data transfer , audio, graphics, video, ... • Data and voice access points: real-time voice and data transmissions to mobile and stationary devices • Cable replacement: eliminates need for cable attachments for connections • Ad hoc networking: a Bluetooth device can establish spontaneous connection with another Bluetooth devices in the transmission range Ö Specifications: • Core specifications -> details of various Bluetooth layers • Profiles specifications -> address the use of core specifications for different applications such as: file transfer, LAN access, fax, headset, hand-free, dial-up network, synchronization 11 Bluetooth Architecture [1] • Core protocols • Cable replacement and telephony protocols • Adopted protocols Bluetooth Core Protocols • Radio: – specifies details related with the air interface utilization – include frequency hopping, modulation, encoding and transmission power • Baseband: – connection establishment, addressing and packet format – power control and timing • Link Manager Protocol (LMP): – link setup between devices and ongoing link management – include security, control and negotiation of baseband packets • Logical Link Control and Adaptation Protocol (L2CAP): – adapts upper-layer protocols to baseband layer – provide connection-less and connection oriented services • Service Discovery Protocol (SDP): – manage the query mechanisms for obtaining information about device services and characteristics of the services – connection may be established based on the collected data Bluetooth Networking A typical Bluetooth data frame Bluetooth Physical Links • Piconets and Scatternets: – Bluetooth devices are organized in local networks called piconets – up to eight devices can be part of a piconet – devices are divided in master and slaves – the master controls the utilization of the radio channel (e.g. frequencyhopping sequence and timing) use in the communication with the slaves – a slave may communicate only with the master and when allowed by the master – a device may belong to different piconets and may be both a master and a slave in two different piconets – a network formed by several connected piconets is called a scatternet ACL Links Data Rates • Synchronous Connection Oriented (SCO) links: – – – – – – • – – – – – – point-to-point connection between master and a single slave allocates fixed bandwidth the master maintains link using reserved slots (basic two slots, one per direction) the master may support up to 3 SCO simultaneous links, a slave 2-3 SCO links SCO packets are never retransmitted used primarily for time-bounded data -> e.g. audio with built-in loss tolerance Asynchronous Connectionless (ACL) links: point-to-multipoint link between master and all slaves only single ACL link can exist the master exchange data with slaves on an per-slot basis usually packet retransmission is applied packet-switched style of connection 1, 3 and 5 slot packets are defined 12 Bluetooth - Channel control in a piconet [1] • Two major states of a Bluetooth – Standby: low-power state – Connection: the device is connected Bluetooth - Channel control in a piconet [2] device: • Seven states for adding new slaves to a piconet: – Page – device issued a page (used by master) – Page scan – device is listening for a page – Master response – master receives a page response from slave – Slave response – slave responds to a page from master – Inquiry – device has issued an inquiry for identity of devices within range – Inquiry scan – device is listening for an inquiry – Inquiry response – device receives an inquiry response Bluetooth - Inquiry and Page Procedure [1] Bluetooth - Inquiry and Page Procedure [2] ÎPage Procedure ÎInquiry Procedure: • Potential master identifies devices in range that wish to participate – transmits an identification ID packet with inquiry access code (IAC) – occurs in Inquiry state • Devices receives inquiry – enter Inquiry Response state – return data with address and timing information (in an FHS packet) – slave moves to Page Scan state or returns to Inquiry Scan • Master uses device address to calculate a page frequency-hopping sequence • Master pages with ID packet and device access code (DAC) of specific slave • Slave responds with ID DAC packet • Master responds with a special FHS packet containing its address and real-time Bluetooth clock value • Slave confirms master’s FHS packet reception with a ID DAC packet • Slaves moves to Connection state ÎConnection state control for slaves • Master send a Poll packet to verify that a slave has switched on master timing and channel frequency • Slave responds with any packet Bluetooth - Slave Connection State Modes Lecture Summary • Active – slave participates in piconet – listens, transmits and receives packets – master sent regularly synchronization data • Sniff – slave listens only on specified slots •Ad-hoc networks – master indicate a reduced number of slots – slave can operate in reduced power mode when not listening •Brief description of IEEE 802.11: standard, layering, • Hold – slave may participate partially in the piconet – slave in reduced power status – slave does not support ACL packets – slave may participate in SCO exchanges architecture, services, MAC, LLC, security • Brief description of Bluetooth: standard, applications, architecture, networking, channel control in piconets, LMP, L2CAP • Park – slave does not participate currently in the piconet – slave still retained as part of the piconet – device receive a parking address and loses its active member address – piconet may then have more than 7 slaves, but only 7 are active 13