CA 304 - Networks Project 2008/2009 Implement Diffie
advertisement
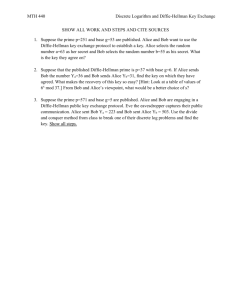
CA 304 - Networks Project 2008/2009 Implement Diffie-Hellman Key Exchange Bis FORBEN David DUPEYRON CA 304 – Network Project Diffie-Hellman Key Exchange Bis Forben David Dupeyron Introduction : The aim of this project is to write a program able to make communicate two computers with secure conversation using a key exchange. First of all, we have to write a single source code, divided in two principal files: a server and a client. Then, we need to implement the “Diffie-Hellman Key Exchange” in order to have a secure communication with different keys generated on each different execution of the code. Network part: To communicate between a client and a server, we must create a socket, which is the constant connection between two programs or computers. A socket is essentially an end point in a communications session, a program can send and receive TCP/IP messages by opening a socket and reading and writing data to and from the socket. This simplifies program development because the programmer needs to worry only about manipulating the socket and can rely on the operating system to actually transport messages across the network correctly. Actually a socket address on a device is the TCP/UDP port number plus the IP network. So we have to launch the server at first, which is listening on the port which writes as an argument (allows you to change it in an easy way) until the client is launched. We did not encounter a lot of problems in this part, besides that the server closed the connection after having received the first message, which solved the trouble with a boucle. Page 2/3 CA 304 – Network Project Diffie-Hellman Key Exchange Bis Forben David Dupeyron Cryptographic part: The Diffie-Hellman key exchange is a cryptographic protocol which permits to create a secure connection between a client and a server, using a secret calculated key. The calculation and the exchange of the key between “Alice” and “Bob” are made as follows: http://fr.wikipedia.org/wiki/Diffie-Helman Alice and Bob use a secret and different integer (a and b), and use a same prime number (p) and a same base (g). And with this system, they will get the same Key (K) and a third person called Eve has no way to find out this key. This symmetric key cipher is an easy way to encrypt a communication. Page 3/3