Laboratory 9
advertisement

Student Name
Date
DT021/4
COMMUNICATIONS NETWORKS 2
Laboratory 9
Objective
Objective:
To apply the RSA Public-Key Encryption Algorithm in simple examples.
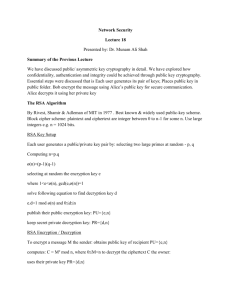
Description: One of the first public-key schemes was developed in 1977 by Rivest, Shamir
and Adleman at MIT. The RSA scheme, known by the initials of its three discoverers, has
survived all attempts to break it since then, and is considered very strong. Its major
disadvantage is that it requires keys of at least 1024 bits (about 300 decimal digits) for good
security, which makes it quite slow.
RSA is a block cipher in which the plaintext and ciphertext are processed as integers between
0 and n – 1 for some n. Encryption and decryption are of the following form, for some plaintext
block M and ciphertext block C:
C = Me (mod n)
M = Cd (mod n)
•
A public/private key pair {e,n} {d,n} is generated as follows:
•
select two large primes at random: p, q
•
compute the product n = p.q
•
note t(n) = (p-1)(q-1)
•
select the encryption key e, where 1 < e < t(n), gcd(e,t(n)) = 1
(gcd: Greatest Common Divisor)
•
solve following equation to find decryption key d
•
•
•
publish pUblic key: KU={e,n}
•
keep secret pRivate key: KR={d,n}
to encrypt a message M, (Message M binary sequence interpreted as integer number, M
< n), using KU, the sender computes:
•
•
e.d=1 mod t(n) d < t(n),
C = Me mod n,
to decrypt the ciphertext C, the owner of private key KR computes:
•
Procedure:
M = Cd mod n
Use Matlab to perform this laboratory. Include your code and your results in
the report.
Reminder: you get the syntax of a particular MATLAB function by typing help
function.
116102316
Page 1/3
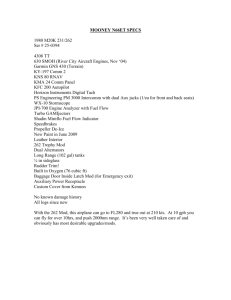
1. Perform encryption and decryption using the RSA algorithm for the following set of prime
numbers:
p = 3; q = 11.
The equation that e must verify, where 1 < e < t(n), is: gcd(e,t(n)) = 1
<> Use the MATLAB function “gcd” to calculate the candidate values for e, given p, q.
(1a) > Select the lowest value for e:
The equation that d must verify is: (d e) MOD(t(n)) = 1
<> Use the MATLAB function “mod” to find the possible value for d.
> Report the 2 keys as KU={e,n}, KR={d,n}.
You will use these keys to encrypt a message represented by the integer value: 5
<> Use the MATLAB function “mod” to find the encrypted value C for M=5
using KU. Report the value.
<> Use the MATLAB function “mod” to verify the decryption of encrypted
message C using KR. Report the result.
(1b) > Select the highest value for e:
The equation that d must verify is: (d e) MOD(t(n)) = 1
<> Use the MATLAB function “mod” to find the possible value for d.
> Report the 2 keys as KU={e,n}, KR={d,n}.
You will use these keys to encrypt a message represented by the integer value: 5
<> Use the MATLAB function “mod” to find the encrypted value C for M=5
using KU. Report the value.
<> Use the MATLAB function “mod” to verify the decryption of encrypted
message C using KR. Report and interpret the result.
2. These calculations involving very large numbers can be affected negatively by insufficient
precision: loss of significant digits due to lack of precision after an exponentiation producing a
very large number, does not allow the successful application of the modulo operation. In order
to successfully perform these operations using limited precision, an alternative method to
perform encryption or decryption using a public/private pair of keys uses the property that:
For any x, y, (x*y) mod(n) = (x*(y mod(n))) mod(n)
This allows to write that xk mod(n) = (x*(xk-1 mod(n))) mod(n); therefore, xk mod(n) can be
calculated iteratively, multiplying at each iteration 2 numbers smaller than n.
<> Use MATLAB to implement this method for the calculation of encryption
and decryption, and apply it to the last example (1b).
116102316
Page 2/3
3. Using the previous example as a guide, calculate the keys for the following samples
1.
p = 7; q = 11, e = 17; encrypt 28, and then decrypt
2.
p = 229; q = 541, e = 17; encrypt 28, and then decrypt.
4. (a) In an RSA system, find the private key of the user whose public key is: KU = {31, 3599}.
This requires to find the values of p and q so that n (= 3599) = pq.
<> Use the MATLAB function “primes” that produces prime numbers to find p and q.
Divide n by all prime numbers between 1 and sqrt(n)+1, until the result is integer.
<> Find the private key KR = {d, 3599}.
(b) A Method proposed by the mathematician Fermat can be used to factor more rapidly n:
Let k be the smallest positive integer so that k2 > n.
If there is h so that k2 – n = h2, then we have factored n as (k + h)*(k – h).
If not, try again with (k + 1)2 –n, then (k + 2)2 - n,… and consider
Eventually, we find m so that m 2 – n = h2. In the worst case, the process stops with
[(n+1)/2]2 – n = [(n-1)/2]2.
We get p = m – h, q = m + h.
<> Use Matlab to implement Fermat’s method to factor n = 62096119. Use method in
4(a) to compare the efficiency of the 2 methods.
5. Propose a public-private key combination to encrypt any message of 8 bits.
116102316
Page 3/3