Study guide for Final exam
advertisement
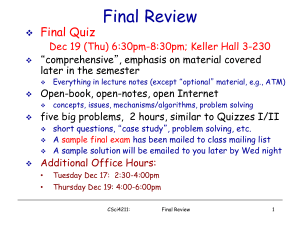
CMSC506 study guide for final exam Question format: Term explanations: e.g., what is CSMA/CD? Short question: e.g., what is the hidden node problem and what causes this problem. Simple math and terminology: e.g., calculating effective data rate for Ethernet. Protocol tracing: Explain binary countdown algorithm and its motivation. o What is binary exponential backoff algorithm? Where is it being used? Scope: Mostly after midterm. Network Layer, Chapter 5, Mainly on 5.2 and 5.6 o Routing Related Topics o The fundamental routing scheme is store-and-forward o 5.2.2 Should be able to step-by-step construct Shortest Path Routing path for a given graph. You should be very familiar with Figure 5-7. o 5.2.3 The pros and cons of flooding. How to improve it? o 5.2.4 Distance Vector Routing: focus on updating process. The main drawback of DVR: count-to-infinity problem o 5.2.5 Link state Routing: each node will calculate routing table when received enough information. Notice how link stage packet is defined and passed around. o 5.2.6 Hierarchical routing: able to determine the size of routing table when the hierarchical structure is given. o 5.2.7 Broadcasting routing: spanning tree and reverse path forwarding o Internet Related Topics o 5.5.6-7 Internetwork routing, Fragmentation o 5.6.1 understand various fields in IPv4 header, such as TTL and MF. The IP routing options (strict and loose source) and their functionality. When studying these, always ask yourself why a particular IP feature is their. o 5.6.2 Subnet and netmask. o 5.6.3 ICMP types. ARP and RARP. Keep in mind that these are IP level protocols. But the functionalities of ARP and RARP is to translate IP and MAC address. o 5.6.8 IPv6. Difference when compared to IPv4. Media Access Layer: mainly at 4.1 4.2 4.3 4.4 4.5 and some subsection in 4.6 and 4.7. Understand three types of access methods: o Fixed channel allocation: FDMA, TDMA. Often centralized. o Dynamic allocation with collision: ALOHA, CSMA/CD, CSMA/CA o Dynamic allocation and collision-free: bit-map, binary countdown… 4.1.1 and 4.1.2 basic concepts and terms. 4.2.1 the difference between pure aloha and slotted aloha. The vulnerable period. 4.2.2 CSMA and several variations. Persistent or not. Augmented by collision detection (Figure 4.5). 4.2.3 collision free protocols. pros and cons. Efficiency calculation. 4.2.6 wireless properties: range, hidden node and exposed node. MACA, collision avoidance. 4.3 Ethernet related topics 4.3.1 4.3.2 Basic specifications: physical dimension, physical media, speeds. Signal forms. 4.3.2 Frame format, collision detection in Ethernet. Propagation delay, minimum packet size. 4.3.4 Binary Exponential Backoff algorithm: what is its purpose? 4.3.7 and 4.3.8 switched Ethernet and gigabit Ethernet 4.4 WLAN related topics: basic protocol is also at 4.2.6 4.4.1-4.4.2 physical layer specification and Different versions in 802.11 family 4.4.3 RTS/CTS handshake, and Network Allocation Vector. Figure 4.27. Fragmentation transmission. DCF and PCF operation mode in 802.11. Base station (AP), beacon frame and channels in 802.11 4.4.4 802.11 framing. 4.5.1 Compare 802.11 and 802.16 4.6.1 bluetooth