Additional Resources
advertisement

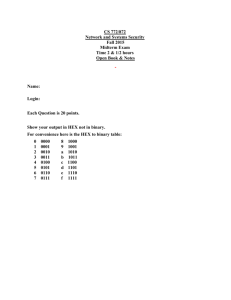
Additional Resources 1. Advanced Encryption Standard http://en.wikipedia.org/wiki/Advanced_Encryption_Standard 2. Symmetric cryptography http://www.ibm.com/developerworks/library/s-crypt02.html 3. Asymmetric cryptography http://www.ibm.com/developerworks/library/s-crypt03.html 4. PGP Corporation http://www.pgp.com/ 5. Trusted Platform Module http://en.wikipedia.org/wiki/Trusted_Platform_Module Key Terms Advanced Encryption Standard (AES) A symmetric cipher that has been approved as a replacement for DES. algorithm Procedures based on a mathematical formula; used to encrypt the data. asymmetric cryptographic algorithm Encryption that uses two mathematically related keys. BitLocker A Microsoft Windows Vista hardware-enabled data encryption feature. block cipher A cipher that manipulates an entire block of plaintext at one time. Blowfish A block cipher that operates on 64-bit blocks and can have a key length from 32 to 448 bits. ciphertext Data that has been encrypted. cleartext Unencrypted data. collision In cryptography, two different sets of data that produce the same hash. cryptography The science of transforming information into an unintelligible form while it is being transmitted or stored so that unauthorized users cannot access it. Data Encryption Standard (DES) A symmetric block cipher that encrypts data in 64bit blocks. decryption The process of changing ciphertext into plaintext. Diffie-Hellman A cryptographic algorithm that allows two users to share a secret key securely over a public network. digest The unique signature created by a hashing algorithm. digital signature An electronic verification of the sender. elliptic curve cryptography An algorithm that uses elliptic curves instead of prime numbers to compute keys. Encrypting File System (EFS) An encryption scheme for Windows operating systems. encryption The process of changing plaintext into ciphertext. file system A method used by operating systems to store, retrieve, and organize files. GNU Privacy Guard (GPG) Free, open-source software that is commonly used to encrypt and decrypt e-mail messages. hash The unique signature created by a hashing algorithm. hashing The process for creating a unique signature for a set of data. homoalphabetic substitution cipher A cipher that maps a single plaintext character to multiple ciphertext characters. International Data Encryption Algorithm (IDEA) A symmetric algorithm that dates back to the early 1990s and is used mainly in Europe. key A mathematical value entered into the algorithm to produce the ciphertext. Message Digest (MD) A common hash algorithm of several different versions. Message Digest 2 (MD2) A hash algorithm that takes plaintext of any length and creates a hash that is 128 bits in length after the message is divided into 128 bit sections. Message Digest 4 (MD4) A hash that was developed in 1990 for computers that processed 32 bits at a time. Message Digest 5 (MD5) A revision of MD4 that is designed to address its weaknesses. metadata Data that is used to describe the content or structure of the actual data. monoalphabetic substitution cipher A cipher that simply substitutes one letter or character for another. non-repudiation The process of proving that a user performed an action. one-time pad (OTP) Combining a truly random key with plaintext. one-way hash The process for creating a unique signature for a set of data. pad In cryptography, a truly random key. padding Additional data that is added to a hash to make it the correct number of bytes. plaintext Data input into an encryption algorithm. Pretty Good Privacy (PGP) A commercial product that is commonly used to encrypt e-mail messages. private key An asymmetric encryption key that does have to be protected. private key cryptography Cryptographic algorithms that use a single key to encrypt and decrypt a message. public key An asymmetric encryption key that does not have to be protected. public key cryptography Encryption that uses two mathematically related keys. RC2 A block cipher that processes blocks of 64 bits. RC4 A stream cipher that will accept keys up to 128 bits in length. RC5 A block cipher that can accept different length keys and blocks. RC6 A cipher that has three key sizes (128, 192, and 256 bit) and performs 20 rounds on each block. Rivest Cipher (RC) A family of cipher algorithms designed by Ron Rivest. RSA An asymmetric algorithm published in 1977 and patented by MIT in 1983. Secure Hash Algorithm (SHA) A secure hash algorithm that creates hash values of longer lengths. SHA-1 The first versions of Secure Hash Algorithm. SHA-2 A family of Secure Hash Algorithms that has four variations, known as SHA224, SHA-256, SHA-384, and SHA-512. steganography Hiding the existence of data within a text, audio, image, or video file. stream cipher An algorithm that takes one character and replaces it with one character. substitution cipher A cipher that simply substitutes one letter or character for another. symmetric cryptographic algorithm Encryption that uses a single key to encrypt and decrypt a message. transposition cipher A cipher that rearranges letters without changing them. Triple Data Encryption Standard (3DES) A symmetric cipher that was designed to replace DES. Trusted Platform Module (TPM) A chip on the motherboard of the computer that provides cryptographic services. Twofish A later derivation of the Blowfish algorithm that is considered to be strong. Whirlpool A new cryptographic hash function that has received international recognition and adoption by standards organizations. whole disk encryption Cryptography that can be applied to entire disks.