Joint Channel Coding and Cryptography for SMS
advertisement

> REPLACE THIS LINE WITH YOUR PAPER IDENTIFICATION NUMBER (DOUBLE-CLICK HERE TO EDIT) <
1
Joint Channel Coding and Cryptography for
SMS
Ashok Kumar Nanda, Lalit Kumar Awasthi
Abstract—SMS has a variety of advantages and disadvantages
for M-Commerce purpose. The advantages are easy to use,
common messaging tool among consumers, works across all
wireless operators, affordable for mobile users, no specific
software required for installation, allows banks and financial
institutions to provide real-time information to consumers &
employees, stored messages can be accessed without a network
connection. Most important disadvantage of SMS so it does not
offer a secure environment for confidential data during
transmission and there is no standard procedure to certify the
SMS sender. There is a need for an end to end SMS Encryption
with errorless message transmission in order to provide a secure
with error free data transmission for communication. These two
factors are important for SMS. Till now there is no such scheme
that provides complete solutions. The transmission of an SMS in
GSM network is not secure at all. Therefore it is desirable to fully
secure with errorless SMS for business purposes. Both these two
issues are researched and dealt separately with sufficient
literature available. However these solutions were dealt
separately till now. In this paper, we have analyzed about Joint
Channel Coding and Cryptography (JCCC), Soft Input
Decryption (SID). We theoretically proposed a novel scheme
XTR – NR Signature algorithm in this paper. We are expecting
that it will improve the current security level, fastest speed and
provide reliable message recovery at receiver end with respect to
key generation, encryption decryption, signing and verification
and small key size for SMS application in any kind of mobile
device.
Index Terms— Joint Channel Coding and Cryptography
(JCCC), SMS, Soft Input Decryption (SID), XTR – NR Signature
I. INTRODUCTION
W
ireless networks offers mobility and easy if use to many
applications. Most popular applications are cellular
telephony, Short message Service (SMS), multimedia
messaging service (MMS), web browsing and Internet access,
file transfer, sensing streaming audio & video and video
conferencing. Scope, coverage and deployment infrastructure
of the wireless communication vary depending on the desired
application. Wireless communication is more prone
transmission errors. The tolerable data error rate depends upon
Ashok Kumar Nanda is a full time research scholar in Computer Science
and Engineering Department, National Institute of Technology, Hamirpur,
Himachal Pradesh India – 177005. His office Phone: 091 – 1972 – 254413,
Mobile: 091 – 9418143520, e-mail: ashokkumarnanda@yahoo.com and
nanda@nitham.ac.in.
Prof. Lalit Kumar Awasthi is professor & Head of Computer Centre,
National Institute of Technology, Hamirpur, Himachal Pradesh India –
177005. His office Phone: 091 – 1972 – 254404, e-mail: lalit@nitham.ac.in.
the application. For more transmission error is allowed in
voice communication as compared to file transfer application.
Similarly SMS is also a kind of file transmission. Here data
transmission error should be absolutely negligible. In wireless
environment, the transmission errors are due to its broadcast
nature. Presently many business organizations are using SMS
as an application in business. Cryptography is a time tested
technique to provide security. A new concept has been
proposed as called as Joint Channel Coding and Cryptography
(JCCC) to provide both security & error control. It combines
the cryptographic methods for data security with the
techniques for error correction.
Nataša ŽIVIĆ has stated interesting property of the
cryptographic algorithms in [1] that a good cryptographic
algorithm should be such that a one bit error in the input to the
encryption should result in about 50% of the decrypted bits to
be wrong. Thus, if we make use of such algorithm for
verification of data at the receiver and there was an error of at
least one bit introduced during the transmission, then the
verification of cryptographic check value should fail. This
means, that all bits of the message and the cryptographic
check value have to be correct at the input of encryption for
successful verification of data. SID corrects bits at the input of
decryptor. If the decoder is not able to reconstruct the original
message and cryptographic check value because of a noisy
channel or inefficiency of the channel decoding algorithm, it is
possible to correct the message with the cryptographic check
value using side information of the channel decoder in form of
so called L-values. Channel decoding improvement depends
on using a message with its cryptographic check value which
has been corrected by Soft Input Decryption. It is a
combination of Soft Input Soft Output (SISO) convolution
channel coding and decrypting. Corrected L-values are used as
feedback information to the channel decoder for improving
decoding process of bits in error.
Rest of paper is organized as follows. Section II provides an
overview of Joint Channel Coding and Cryptography. Section
III analyses overview of the Soft Input Decryption (SID)
scheme and its algorithm. Section IV presents briefly about
XTR - Nyberg Rueppel (XTR – NR) message recovery
signature scheme. Section V discusses the anticipated result of
application of novel scheme and followed by conclusion.
> REPLACE THIS LINE WITH YOUR PAPER IDENTIFICATION NUMBER (DOUBLE-CLICK HERE TO EDIT) <
II. JOINT CHANNEL CODING AND CRYPTOGRAPHY (JCCC) [2]
Soft Input Decryption (with feedback) is used for Joint
Channel Coding and Cryptography. The data block is the input
of the encryptor. This data block is equally divided two parts - message ma and message mb (each of length of m). To each
message, its digital signature is appended i.e. na and nb, each
of length n, using a cryptographic check function (CCF) as
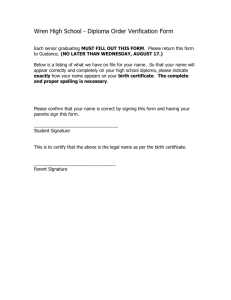
shown in Fig 1.
In general, the lengths of message parts ma and mb and the
lengths of cryptographic check values na and nb do not have
to be the same. The different lengths of ma, mb, na and nb
have only minor influence on the bit error rate (BER).
Therefore equal lengths of message parts as well as
cryptographic check values are used to obtain the simulation
results in this work.
Block ‘a’ consists of the message part ma and the appended
XTR – NR Signature message na:
Block ‘b’ consists of the message part mb and the appended
XTR – NR Signature message nb:
Interleaving of the blocks a and b forms the assembled
message u:
u is encoded by a convolutional code, modulated and
transferred over the noisy channel.
After demodulation of the received message, Joint Channel
Coding and Cryptography is applied in 3 steps (Fig. 2).
The first step consists of the following sub tasks,
a. channel decoding
b. segmentation and de-interleaving of the output u’ of
the decoder into block ‘a and block b’, and
c. parallel SID with feedback of blocks a’ and b’.
The second step is the feedback from block a’ corrected by
SID to block b’, or vice versa, from block b’ corrected by SID
to block a’. L-values of bits of the corrected block (for
example, block a’) are set to ±∞, because bits are known and
correspondingly their L-values are known. L-values of bits of
another – not corrected block (for example, block b’) are set to
0, which represent unknown bits. These L-values are fed back
to channel decoder, enabling improved bit error correction of
block which has to be corrected.
The third step is additional SID of block, which has been
improved corrected by feedback in the second step (for
example, block b’).
Fig. 2 shows the joint channel coding and cryptography
process for a received message using the serial SID with
feedback. BER after each of the process components is
recorded as,
• BERcd1 is the BER after the first decoding
• BER1.SID is the BER after the first step
• BERcd2 is the BER after the second step
• BER2.SID is the BER after the third step
The second and third step dependent on one of the
following cases:
• If the results of SID of block a’ and SID of block b’ are
correct, then the decoding succeeds. In this case BER2.SID
=0
• If the result of SID of block a’ is correct, but block b’
could not be corrected then the following step the
•
•
2
corrected block a’ is used for the correction of block b’
by feedback to the second channel decoding, resulting in
BER feedback. Block b´ is tried to be corrected by SID
(BER2.SID).
If the result of SID of block b’ is correct, but block a’
could not corrected then the second step the corrected
block b’ is used for the correction of block a’ by feedback
to the second channel decoding, resulting in BER
feedback. In the third step, block a´ is tried to be corrected
by SID (BER2.SID).
If neither the result of SID of block a’ nor the result of
SID of block b’ is correct then BER is equal to BER of
the convolutional decoder (BER of the inner code).
III. SOFT INPUT DECRYPTION (SID) ALGORITHM [3]
SID is a method for the correction of SID blocks which
contain cryptographic check values (digital signatures, MACs,
H-MACs) by using L-values as the output of the SISO channel
decoder. Cryptographic check values provide data integrity,
data origin authentication and non repudiation. It works in
block oriented fashion. The input for SID contains data which
are secured by cryptographic check values. The block which
has to be corrected by SID after channel decoding is called
ma
mb
……….
Message
Vector
CCF
Key
CCF
XTR-NR Signature
ma
Key
XTR-NR
Signature
na
mb
nb
Block a
Block b
Interleaving
a
b
a
b
a
…….
a
b
Interleaved message (u)
Figure 1. Interleaving of blocks a and b into message u [4].
SID block (SID block). It may contain data and cryptographic
check values, or just cryptographic check values, depending
on the used scenario. The standard verification process
without SID is presented in fig. 3.
The algorithm of Soft Input Decryption (fig. 4) is as
follows: If the verification of the cryptographic check value is
successful, i.e. the output is “true”, then SID is successfully
completed. If the verification is false, then soft output of the
channel decoder is analyzed and the bits with the lowest |L|values are flipped (XOR 1). Then the decryptor performs the
verification process and proves the result of the verification
> REPLACE THIS LINE WITH YOUR PAPER IDENTIFICATION NUMBER (DOUBLE-CLICK HERE TO EDIT) <
again. If the verification is false, then the bits with another
combination of the lowest |L|-values are changed. This
iterative process will stop when the verification is successful
or the needed resources are consumed.
3
a very long SID block or an attack, so that the resources are
not sufficient to find the correct content of a SID block.
Channel
SISO CHANNEL DECODER
Channel
SOFT INPUT DECRYPTION
SID Block
L - Values
Demodulation
BERcd1
DECRYPTOR
(VERIFICATION)
SISO Channel Decoding
Changing of bits
of SID Block NO
No
Step 1
Segmentation of u’
Step 1
(into blocks a’ & b’)
Block a’
Block b’
SID of Block a’
SID of Block a’
BER 1, SID
BER 1, SID
SISO Channel Decoding
SISO Channel Decoding
Step 2
BER feedback
BER feedback
SID of Block b’
SID of Block a’
Step 3
Figure Algorithm of Joint Channel Coding Cryptography
BER 2, SID
BER 2, SID
Figure 2. Algorithm of Joint Channel Coding and Cryptography [4].
Channel
SISO CHANNEL DECODER
SID BLOCK
L – Values of bits of SID block
DECRYPTOR (VERIFICATION)
No
VERIFICATION
TRUE
Successfully
Verified data Yes
No
Not Verified data
SOURCE DECODER
Figure 3. Verification of SID block without soft Input Decryption [3].
In the case that the attempts for correction fail, the number
of modified bits is too large as a result of a very noisy channel,
VERIFICATION
TRUE
Successfully
verified data
Yes
Successfully
Verified SOURCE
data
YES
DECODER
YES
Number
of trials
exceede
Unsuccessfullyd
verified data
yes
No
unsuccessfully verified data
Figure 4. Algorithm of the Soft Input Decryption [3].
It may happen that the attempts for the correction of a SID
block succeed, but the content of a SID block is not equal to
the original one: a collision happened. This case has a
negligible probability if the length of the cryptographic check
values is chosen under security aspects.
IV. XTR-NYBERG-RUEPPEL (XTR – NR) MESSAGE
RECOVERY SIGNATURE SCHEME
XTR is an algorithm for public-key encryption. XTR stands
for ‘ECSTR’. It stands for Efficient and Compact Subgroup
Trace Representation. From a security point of view, XTR is a
traditional discrete logarithm system: For its security it relies
on the difficulty of solving discrete logarithm related problems
in the multiplicative group of a finite field. Some advantages
of XTR are its fast key generation (much faster than RSA),
small key sizes (much smaller than RSA, comparable with
ECC for current security settings), and speed (overall
comparable with ECC for current security settings) [5]. In
1996, the Nyberg-Rueppel signature scheme was improved as
ElGamal version. In 2000, the XTR-Nyberg-Rueppel version
was presented. Then, the XTR – Blind – Nyberg – Rueppel
version and the verifiable encryption of XTR-Nyberg-Rueppel
version were presented in 2003 and 2007, respectively. It is
XTR version of the Nyberg-Rueppel (NR) message recovery
signature scheme. XTR can in a similar way be used in other
‘ElGamal-like’ signature schemes.
A. XTR-NR signature generation [6]
It is stated in [6] that to sign a message M containing an
agreed upon type of redundancy using the XTR version of the
NR protocol, Alice does the following:
Let P, q & Tr(g) be shared XTR public key data.
1. Alice selects a random integer u ∈ [2, q − 3], and n = u
and c = Tr(g) in
> REPLACE THIS LINE WITH YOUR PAPER IDENTIFICATION NUMBER (DOUBLE-CLICK HERE TO EDIT) <
2.
3.
4.
5.
6.
Sn(c) = (cn-1, cn, cn+1) ∈ GF (P2)3 so
Su(Tr(g)) = (Tr(gu−1), Tr(gu), Tr(gu+1)) ∈ GF(p2)3 where q
is prime number,
Alice determines a symmetric encryption key K based on
Tr(gu) ∈ GF(p2).
Alice uses an agreed upon symmetric encryption method
with key K to encrypt M, resulting in the encryption E.
Alice computes the (integer valued) hash h of E.
Alice computes s = (k·h + u) mod q ∈ {0, 1… q − 1}.
Alice’s resulting signature on M is (E, s).
B. XTR-NR signature verification [6]
It is assumed that Alice’s XTR public key data for digital
signatures consist of p, q, Tr(g), and Tr(gk) for a secret integer
k that is known only to Alice. However, in addition it is
assumed that not only Tr(gk) but also Tr(gk−1) and Tr(gk+1)
(and thus Sk(Tr(g))) are available to the verifier. These
additional GF(p2) elements are either part of the public key or
they are reconstructed by the verifier. Tr(gk−1) (or Tr(gk+1)) can
be reconstructed from p, q, Tr(g), Tr(gk), and Tr(gk+1) (or
Tr(gk−1)) using an explicit and easily computed formula.
Reconstruction of Tr(gk+1) (or Tr(gk−1)) given just (p, q, Tr(g),
Tr(gk)) requires additional assumptions and a slightly more
involved computation. To verify Alice’s signature (E, s) and to
recover the signed message M, verifier Bob does the
following.
1. Bob checks that 0 ≤ s < q; if not failure.
2. Bob computes the hash h of E.
3. Bob replaces h by −h mod q ∈ {0, 1 . . . q − 1}.
4. Bob applies Algorithm 5.27 stated in [6] to Tr(g),
Sk(Tr(g)) (with k unknown to Bob), a = s, and b = h to
compute Tr(gs · ghk) (which equals Tr(gu)).
5. Bob determines a symmetric encryption key K based on
Tr(gs · ghk) ∈ GF(p2).
6. Bob uses the agreed upon symmetric encryption method
with key K to decrypt E resulting in M.
7. The signature is accepted if and only if M contains the
agreed upon redundancy.
V. ANTICIPATED RESULT
There are so many cryptosystems are available in market to
implement. Here we have considered more popular ECC and
RSA algorithms with XTR algorithm. We have shown the
comparison among them in Table 1. W. r. t. key length, key
selection, encryption time, decryption time, signature time,
verification time and operation speed. Out of these, XTR is
the best among all others (stated in [8], [9]).
XTR – NR Signature generation and verification are both
considerably faster than traditional implementations of the NR
scheme that are based on subgroups of multiplicative groups
of finite fields of the same security level: XTR-NR Signature
generation is about three times faster than traditional NR
signature generation, and XTR-NR signature verification is
about 1.75 faster than the traditional method [6]. The length of
the signature is identical to other variants of the hybrid version
of the NR scheme: an overhead part of length depending on
4
the desired security (i.e., the subgroup size) and a message
part of length depending on the message itself and the agreed
upon redundancy and symmetric encryption. The XTR
signatures scheme with Message Recovery is secure enough
against attacks, especially forgery attacks [7].
TABLE: 1 COMPARISON AMONG XTR, ECC & RSA [8], [9]
XTR
ECC
RSA
Short 170-bit
Short 170-bit
Long 1020-bit
Key Length
Simplest
Hard
Simple
Key Selection
23 ms
28 ms
05 ms for 32 – bit
Encrypt
11 ms
16 ms
40ms CRT
Decrypt
11 ms
14 ms
123 ms
Sign
23 ms
≤ 21ms
05 ms for 32 – bit
Verify
Operation
Fastest
Fast
slow
Speed
Implementation on Pentium III 450 MHz and 96 MB of Ram
VI. CONCLUSION AND FUTURE WORK
Now-a-days SMS is more popular for different applications
in our daily real life. Errorless data transmission with secured
is important in wireless environment. In this paper we have
discussed about joint channel coding and cryptography, SID
algorithm and XTR – NR message recovery signature scheme.
From the above, we have concluded that XTR – NR message
recovery signature algorithm is best among other popular and
traditional algorithms. As a result, secured data will transfer
from sender to receiver end(s) with errorless. It will efficient
scheme and provide better result. It is our future work to
implement, prove and compare. We ensure that it will improve
the current security level, fastest speed and provide reliable
message recovery at receiver end with respect to key
generation, encryption, decryption, signing and verification
with small key length for SMS in any kind of mobile devices.
REFERENCES
[1]
[2]
[3]
[4]
[5]
[6]
[7]
[8]
[9]
Nataša ŽIVIĆ: “Iterative Method for Improvement Of Coding And
Decryption”, International Journal of Network Security & Its
Applications (IJNSA), Vol 1, No 2, July 2009, PP. 1 – 15.
Nataša ŽIVIĆ and Obaid Ur REHMAN: “On using the message digest
for error correction in wireless communication networks”, in 21 st
International Symposium on Personal, Indoor and Mobile Radio
Communications Workshops 2010, Page(s): 491 – 495.
NATASA ZIVIC: “Strategies and Performances of Soft Input
Decryption”, International Journal of Computer Science and Information
Security, Issue 1, Volume 1, May 2009, PP 1 – 12.
Nataša ŽIVIĆ, Christoph RULAND and Obaid Ur REHMAN: “Error
Correction over wireless Channels using Symmetric Cryptography”, in
1st International Conference Wireless Communication, Vehicular
Technology, Information Theory and Aerospace & Electronic Systems
Technology, 2009. Wireless VITAE 2009, Page(s): 752 – 756.
http://en.wikipedia.org/wiki/XTR
Arjen K Lenstra, Eric R Veheul: “An Overview of the XTR Public Key
System”, www.win.tue.nl/~klenstra/xtrsurvey.ps
Li Yong; Zhang Xiang-li; He Long; Xie Zhi-heng; Zhu Chong:
“Research of Trace Equivalence Relation on XTR”, in WRI CMC '09,
International Conference Communications and Mobile Computing,
2009.. Volume: 3, Page(s): 380 – 384
www.ietf.org/proceedings/67/slides/msec-2/msec-2.ppt
www.ecc-brainpool.org/workshop2/XTR.ppt
ACKNOWLEDGMENT
This research work is supported by Ministry of Human
Resource Development (MHRD), Government of India.